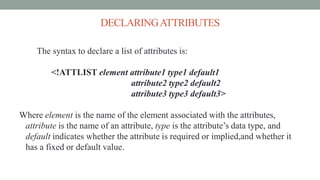
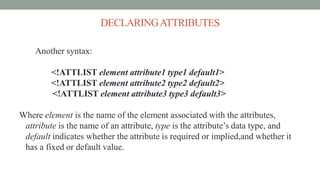
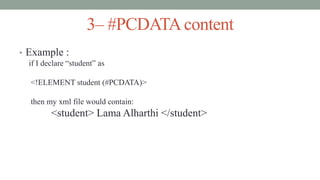
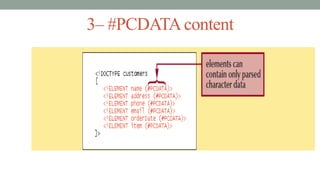
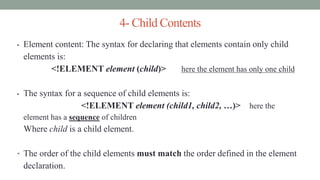
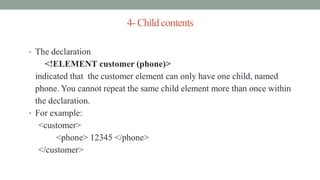
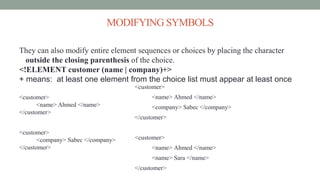
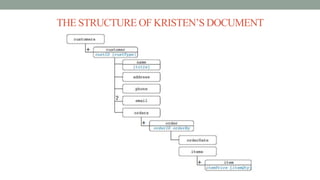
This document discusses validating XML documents using DTDs. It explains that DTDs define the structure and elements of an XML document. Elements, attributes, and their content must be declared in the DTD. Elements can have text, child elements, or mixed content. Attributes have types like ID, enumerated, and default values like required or implied. The document provides examples of declaring elements, attributes, and their types in a DTD to validate an XML file.
![DECLARINGADTD
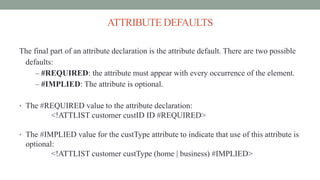
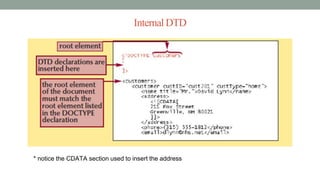
An internal DTD is declarations placed in the same file as the document
content. The DOCTYPE declaration for an internal subset is:
<!DOCTYPE root
[
declarations
]>
Where root is the name of the document’s root element, declarations are the
statements that comprise the DTD.](https://image.slidesharecdn.com/xmlpart21-161210091739/85/Xml-part2-7-320.jpg)
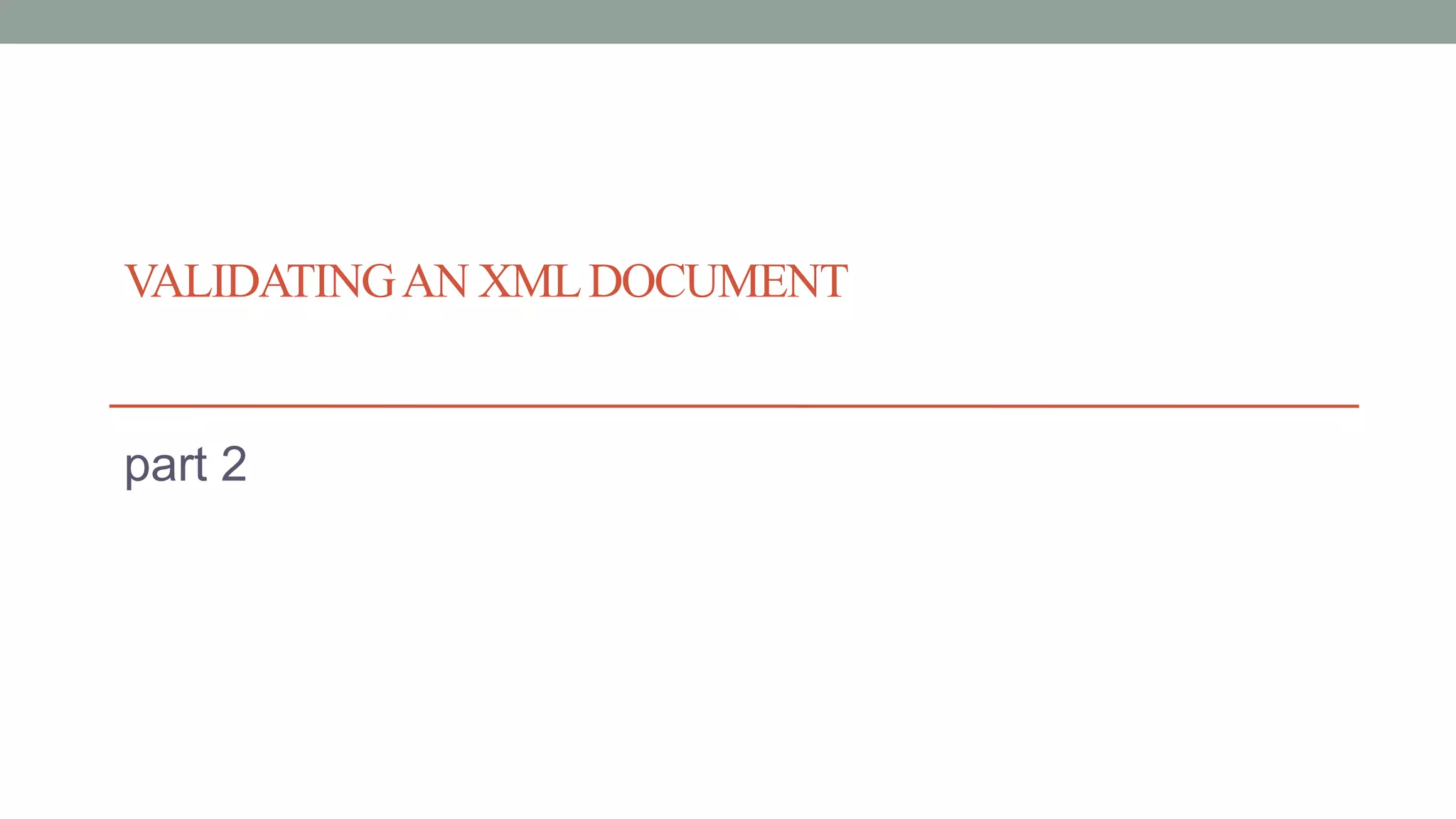
![DECLARING A DTD
Example for internal DTD:
<!DOCTYPE customers
[
declarations
]>](https://image.slidesharecdn.com/xmlpart21-161210091739/85/Xml-part2-8-320.jpg)
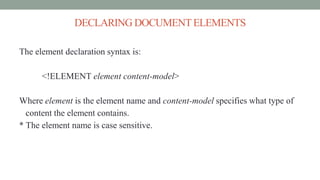
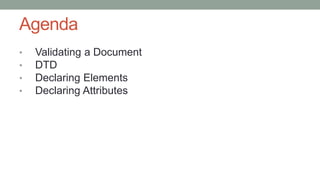
![<!DOCTYPE customers
[ <!ELEMENT customers (customer+)>
<!ELEMENT customer ( name, address, phone,
email?, orders)>
<!ELEMENT name (#PCDATA)>
<!ELEMENT address (#PCDATA)>
<!ELEMENT phone (#PCDATA)>
<!ELEMENT email (#PCDATA)>
<!ELEMENT orders (order+)>
<!ELEMENT order ( orderDate, items)>
<!ELEMENT orderDate (#PCDATA)>
<!ELEMENT items (item+)>
<!ELEMENT item (#PCDATA)>
]>
<customers>
<customer>
<name>Ahmed</name>
<address>14 Bronson st.</address>
<phone>12345</phone>
<orders>
<order>
<orderDate>12/12/09</orderDate>
<items>
<item>>bread </item>
</items>
</order>
<order>
<orderDate> 22/01/10</orderDate>
<items>
<item> eggs </item>
<item> milk </item>
</items>
</order>
</orders>
</customer>
<customer>
…………….
</customer>
</customers>](https://image.slidesharecdn.com/xmlpart21-161210091739/85/Xml-part2-35-320.jpg)