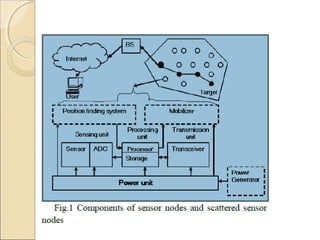
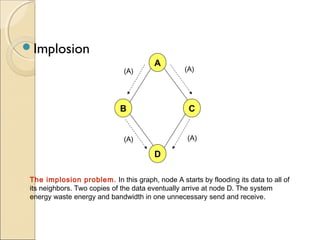
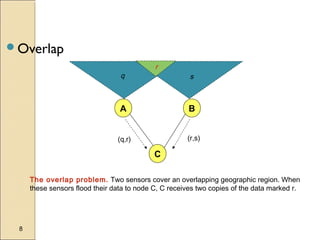
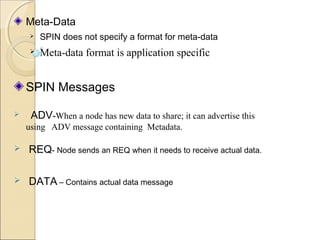
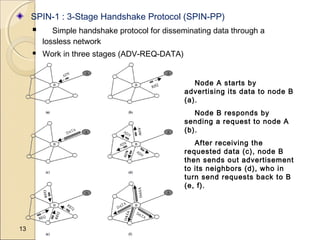
Wireless sensor networks consist of large numbers of sensor nodes that monitor parameters and communicate wirelessly. The SPIN protocol family was developed to address the limitations of sensor nodes, particularly their limited energy, computation, and communication capabilities. SPIN uses meta-data negotiation and resource awareness to disseminate data between nodes more efficiently than flooding protocols. SPIN-1 is a simple three-stage handshake protocol that reduces energy costs. SPIN-2 builds upon SPIN-1 with an additional energy conservation heuristic to further prolong network lifetime. Evaluation shows SPIN consumes significantly less energy than flooding for data dissemination in wireless sensor networks.