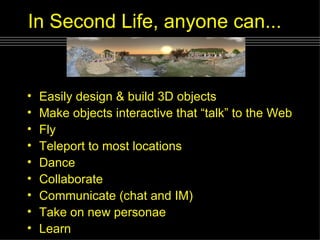
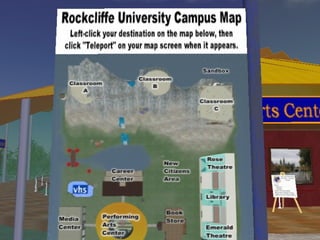
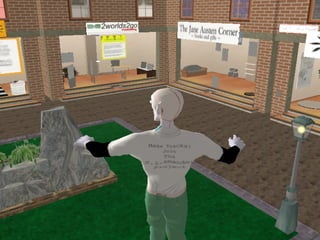
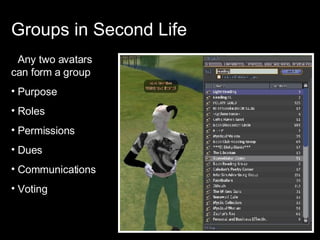
The document discusses the use of a 3D virtual world, Second Life, as an educational tool for collaboration, construction, and learner engagement. It highlights various learning activities and benefits, such as immersion, community building, and multimodal learning environments, while also providing insights from educators using the platform for teaching. Furthermore, it emphasizes how these virtual experiences can enhance academic learning by lowering failure threats and fostering engagement.