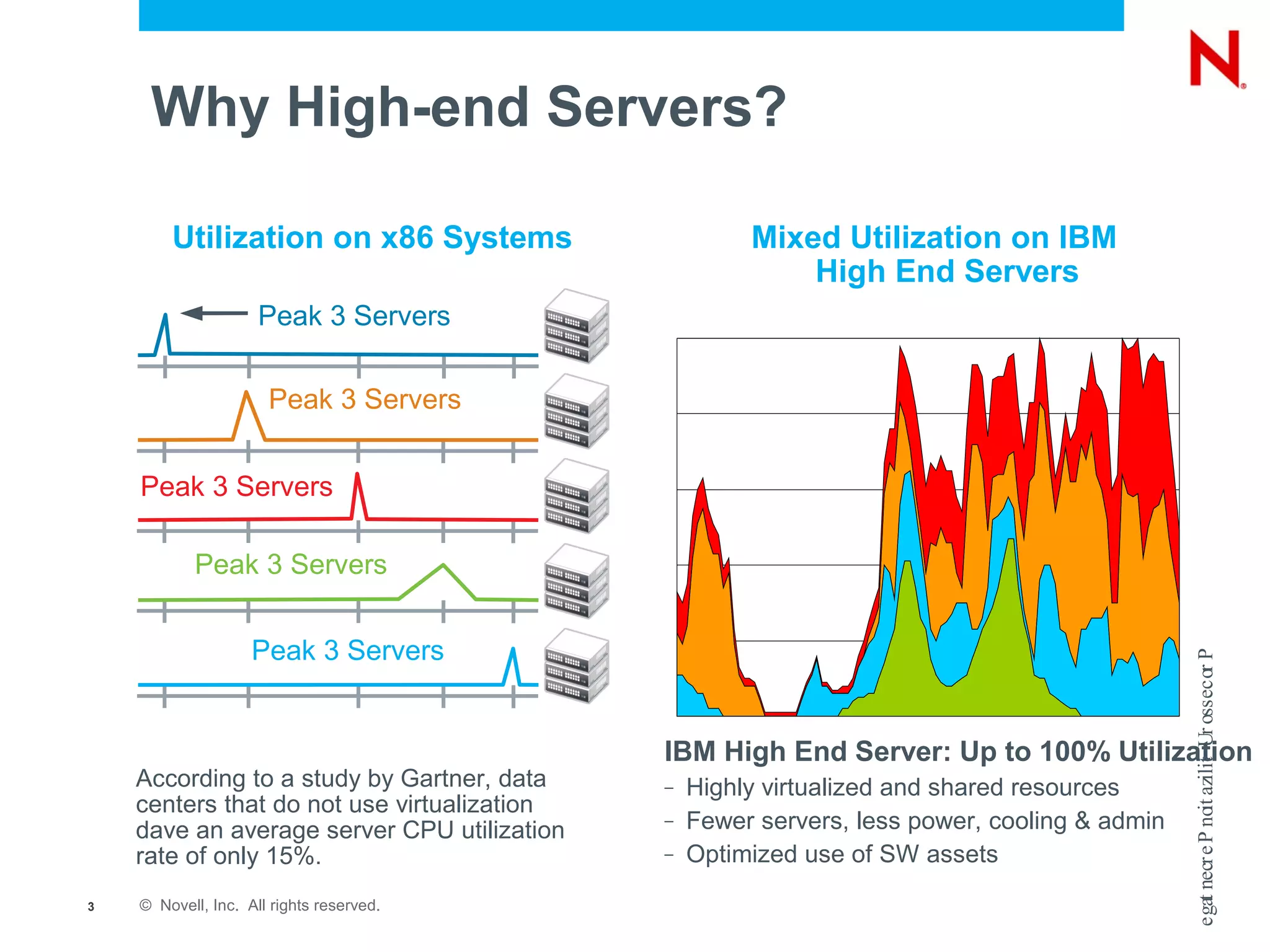
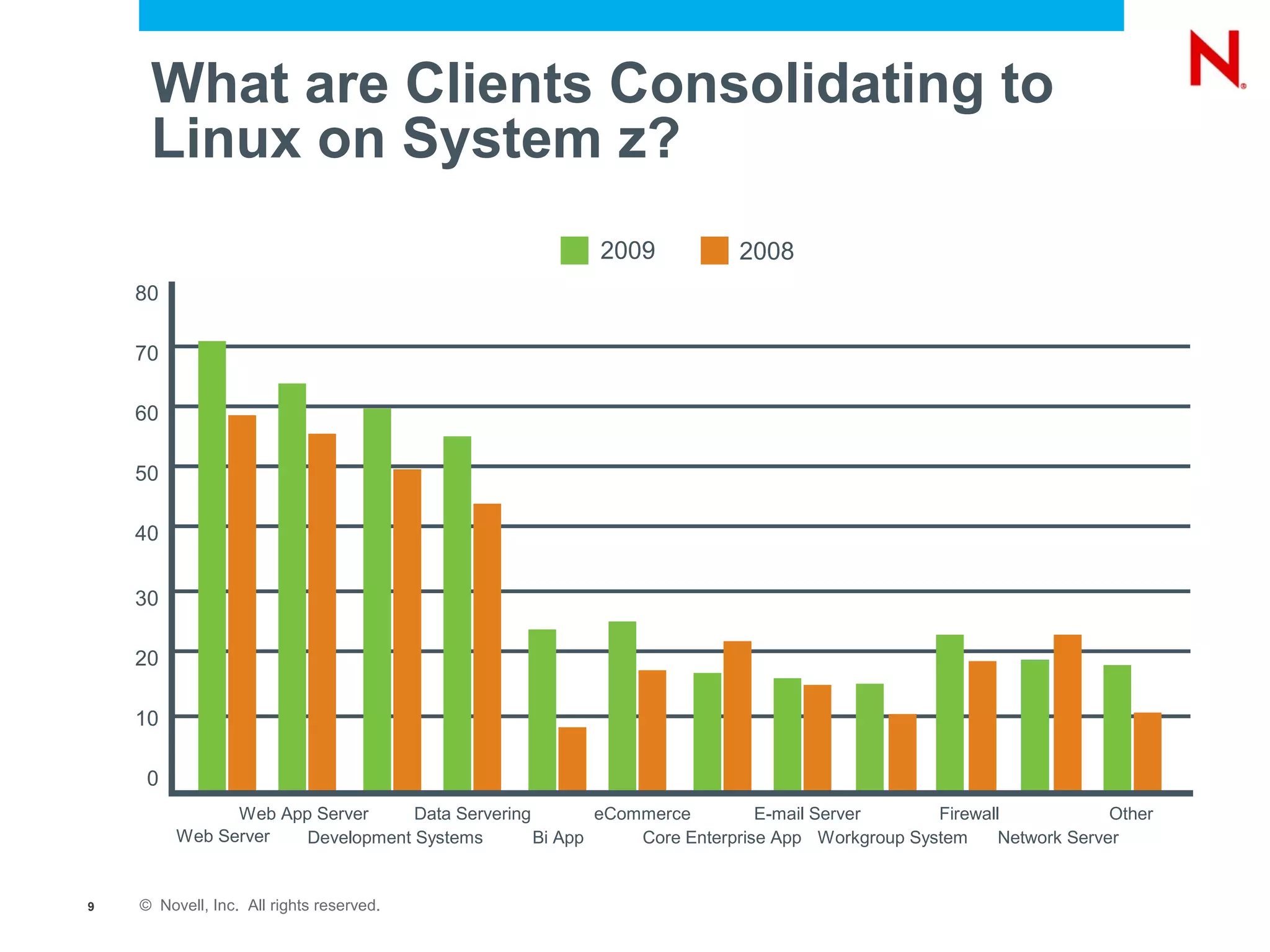
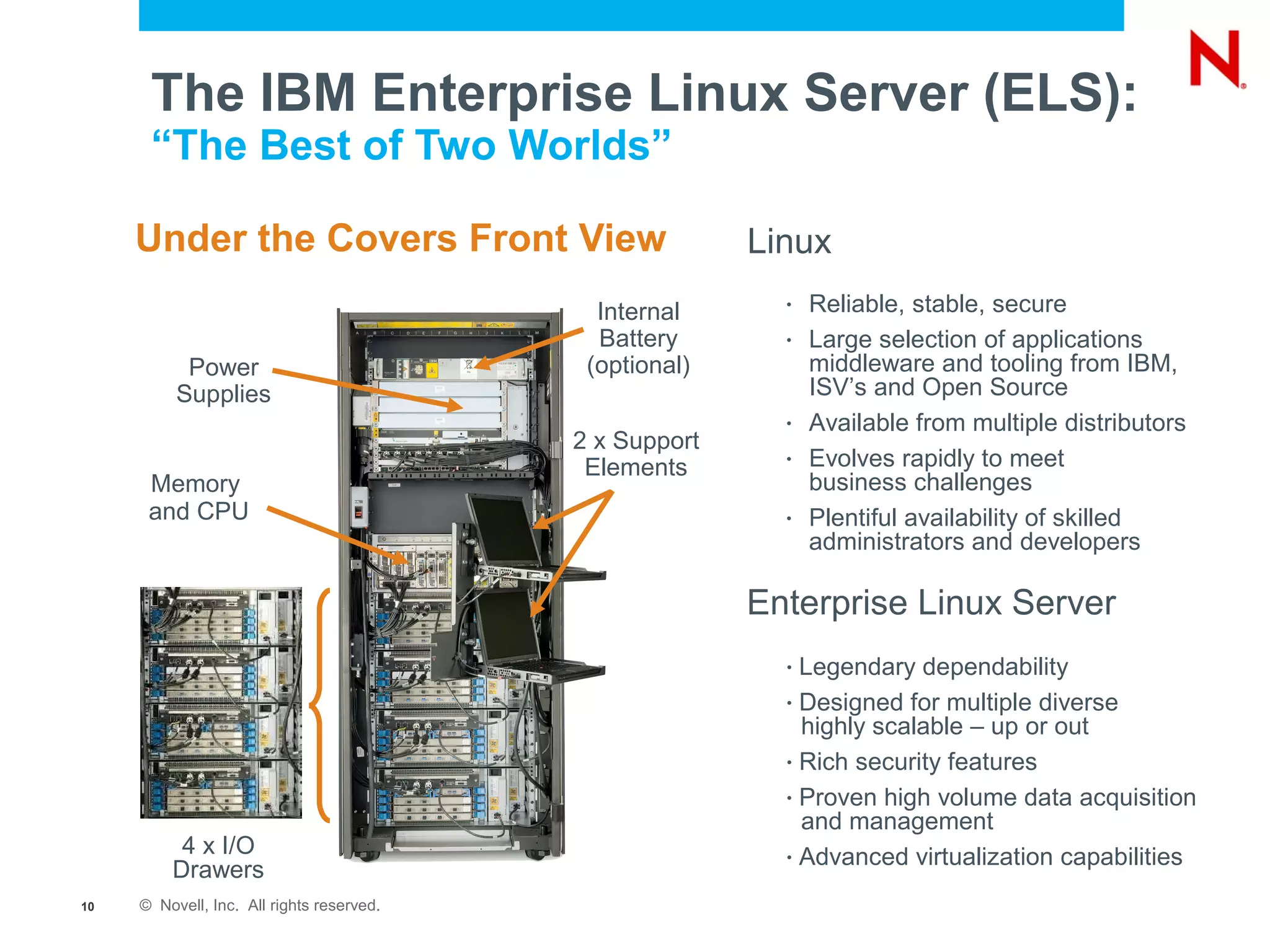
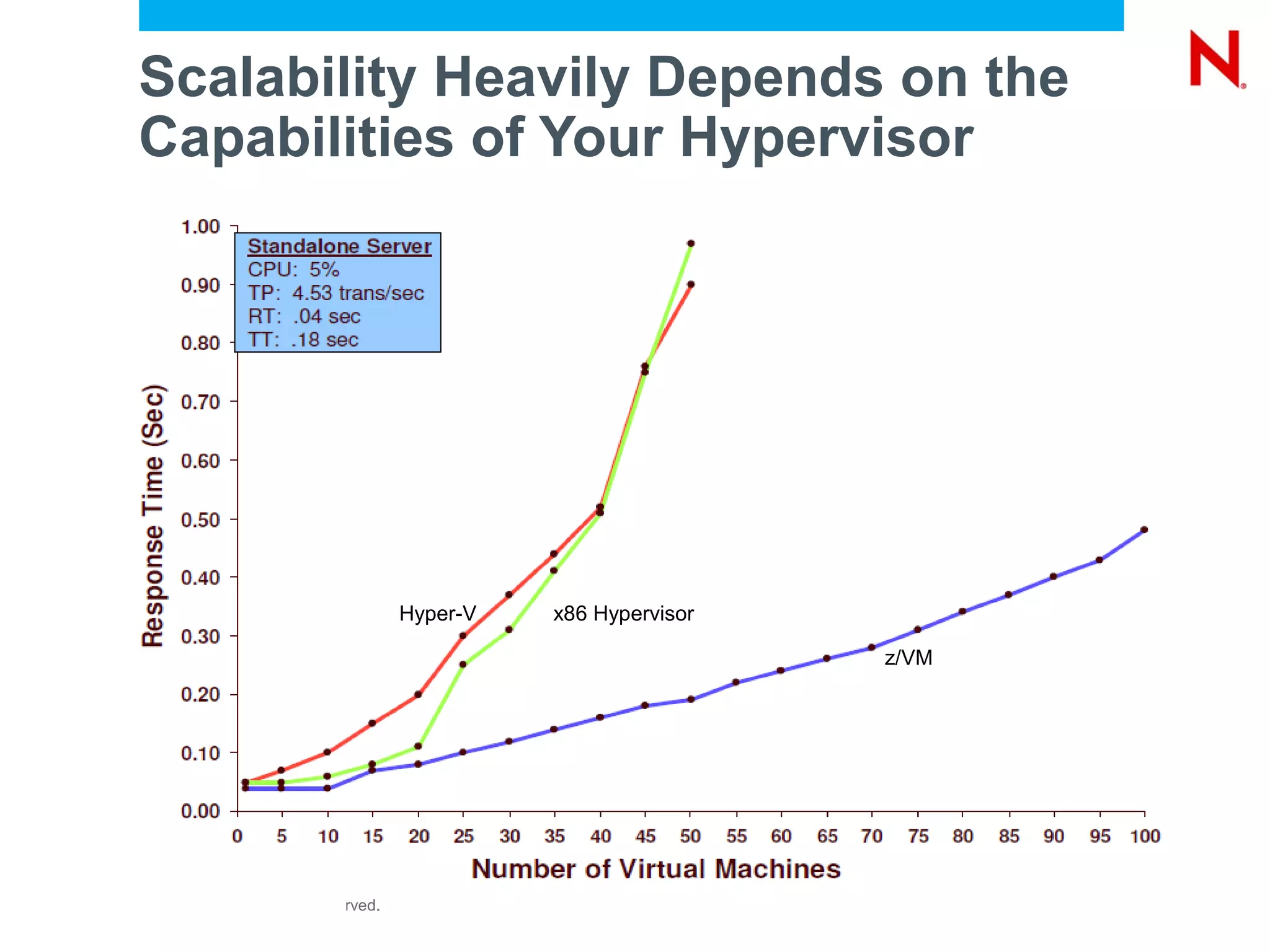
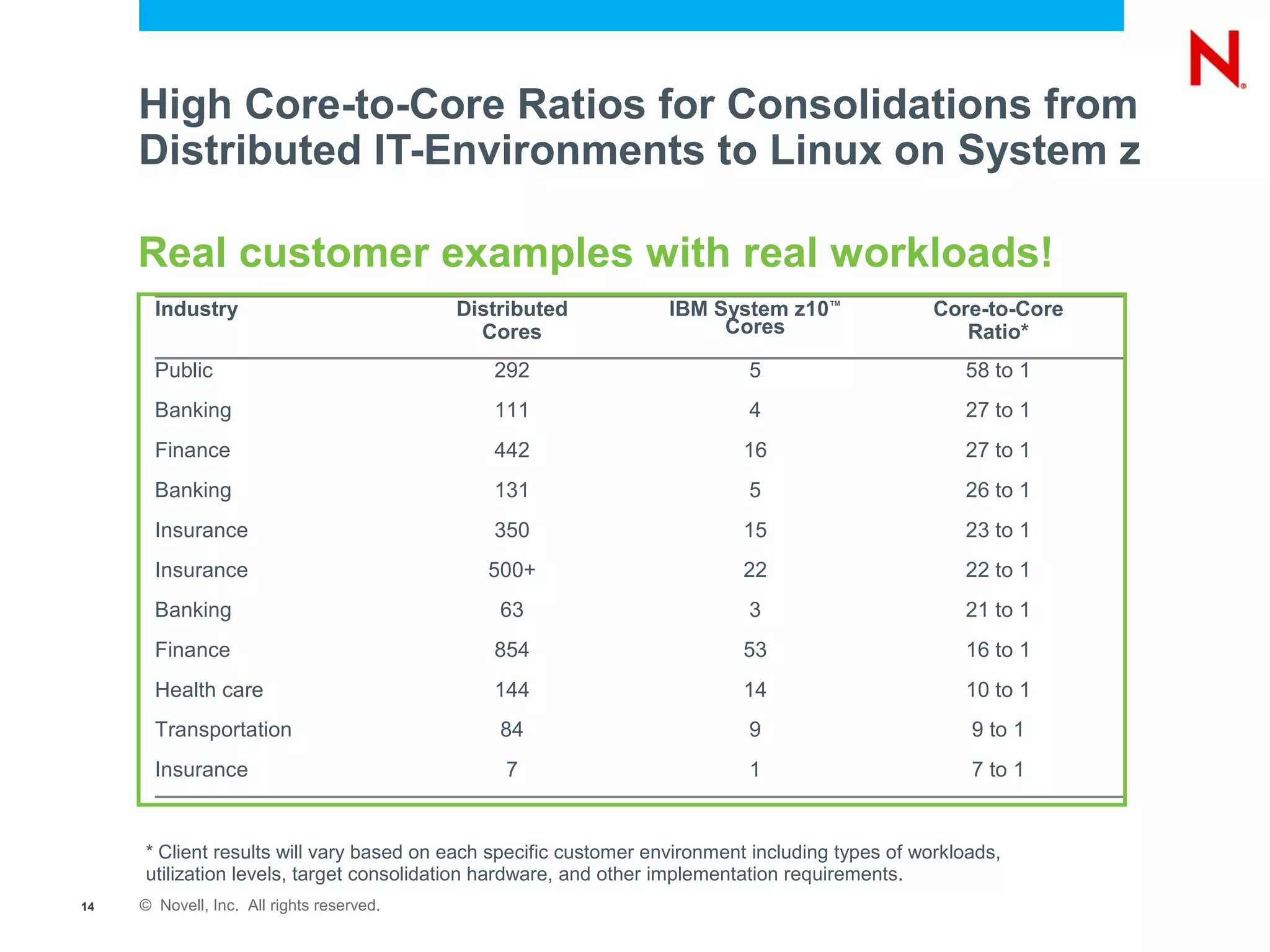
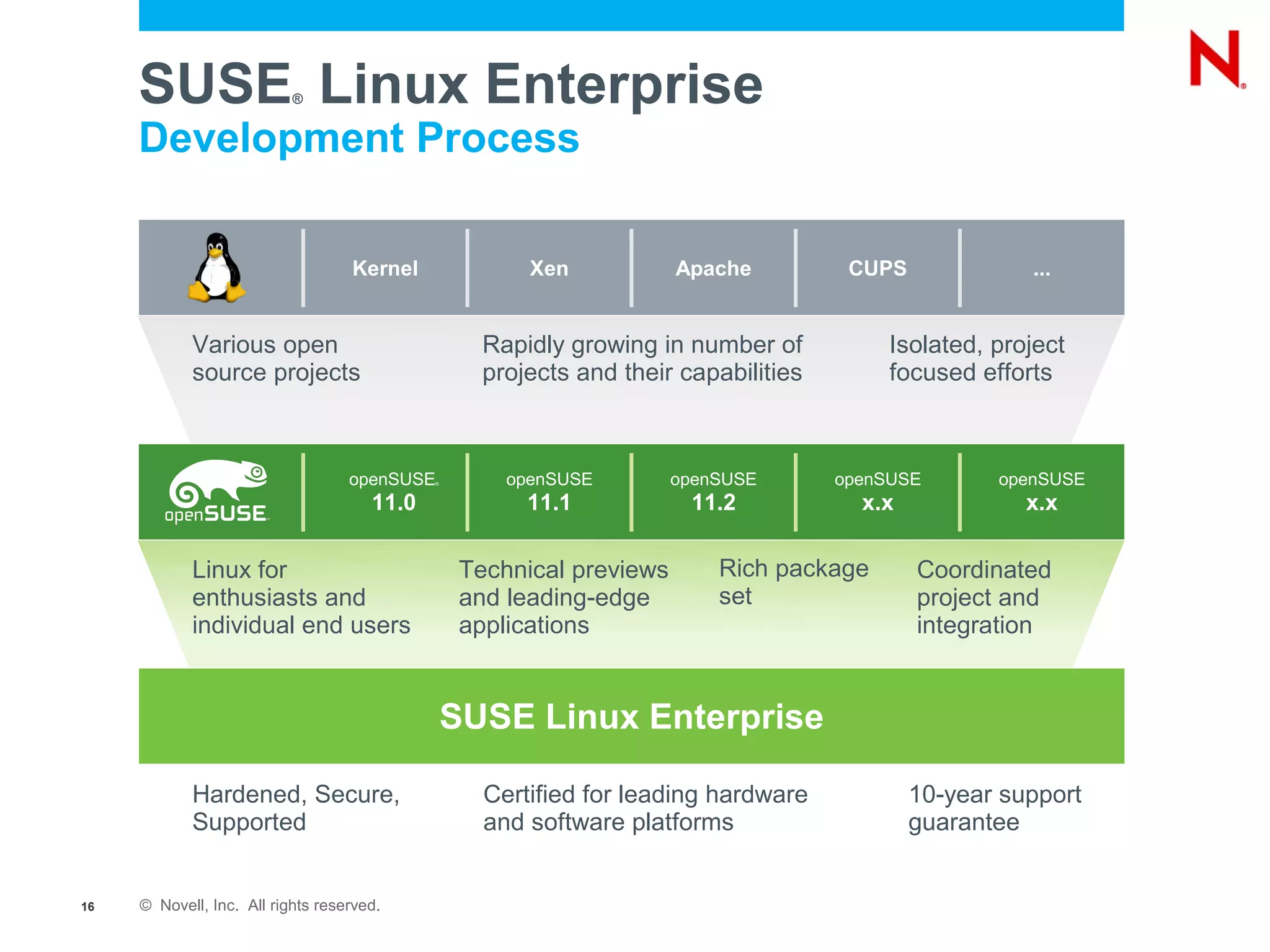
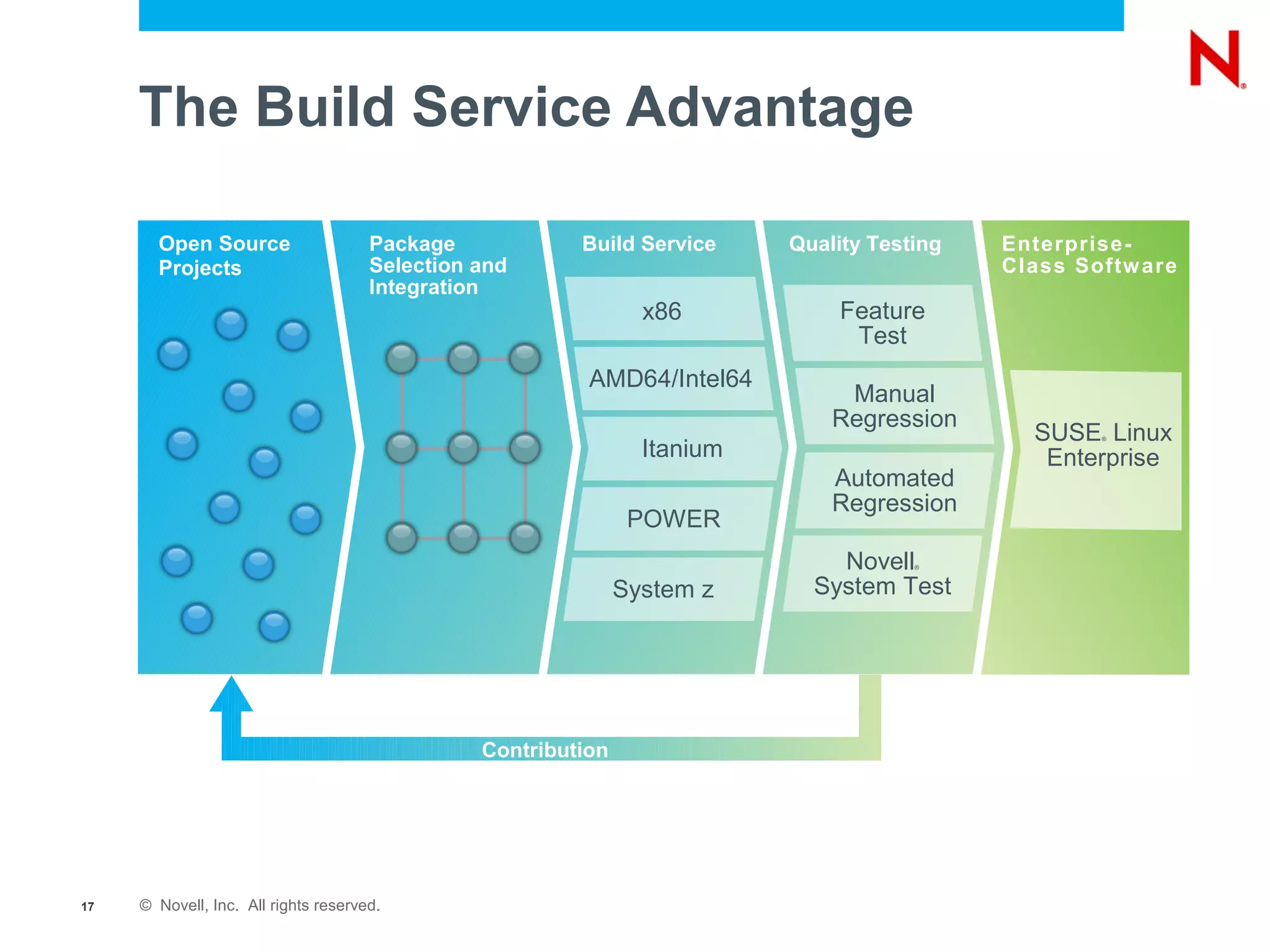
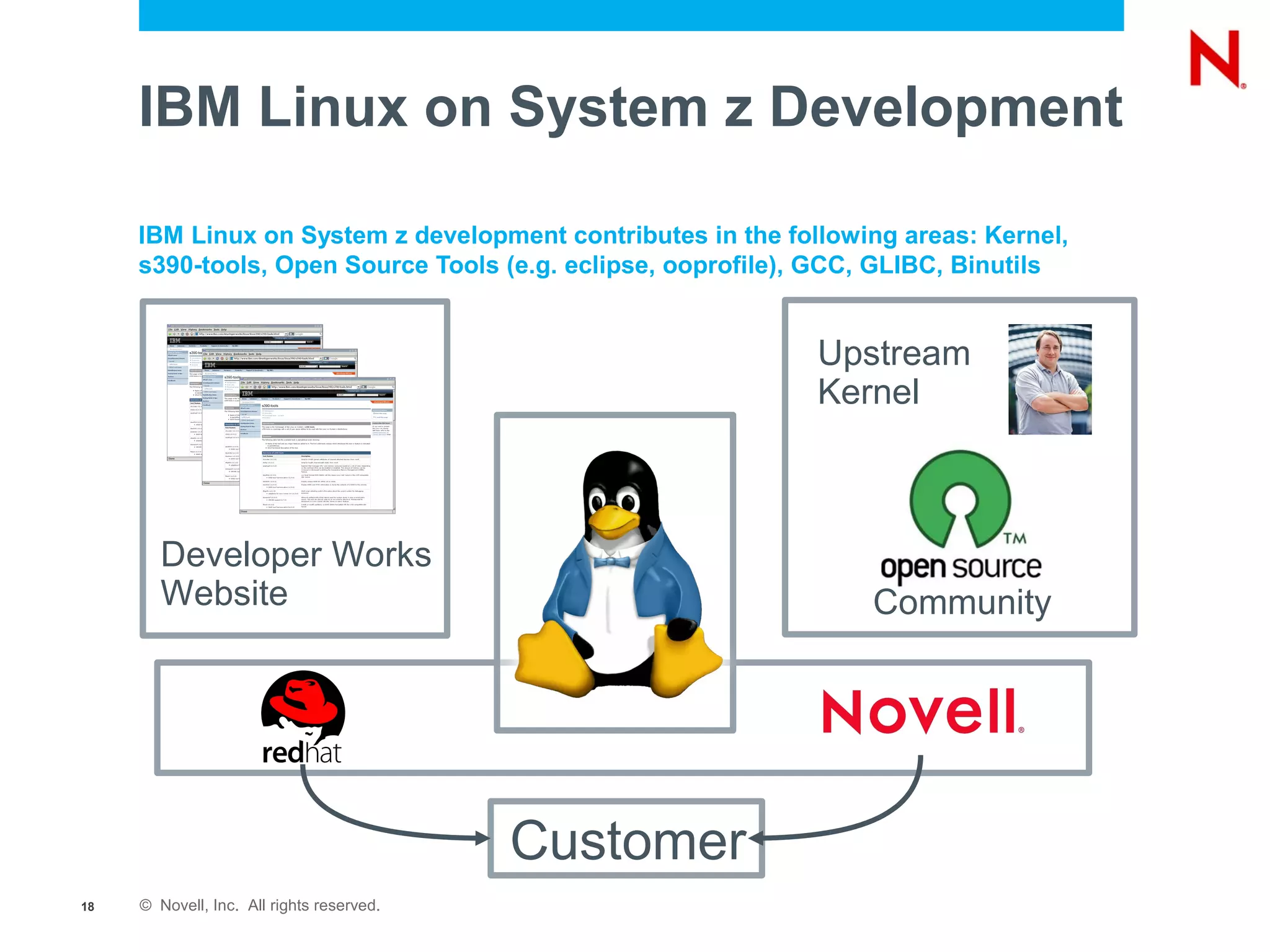
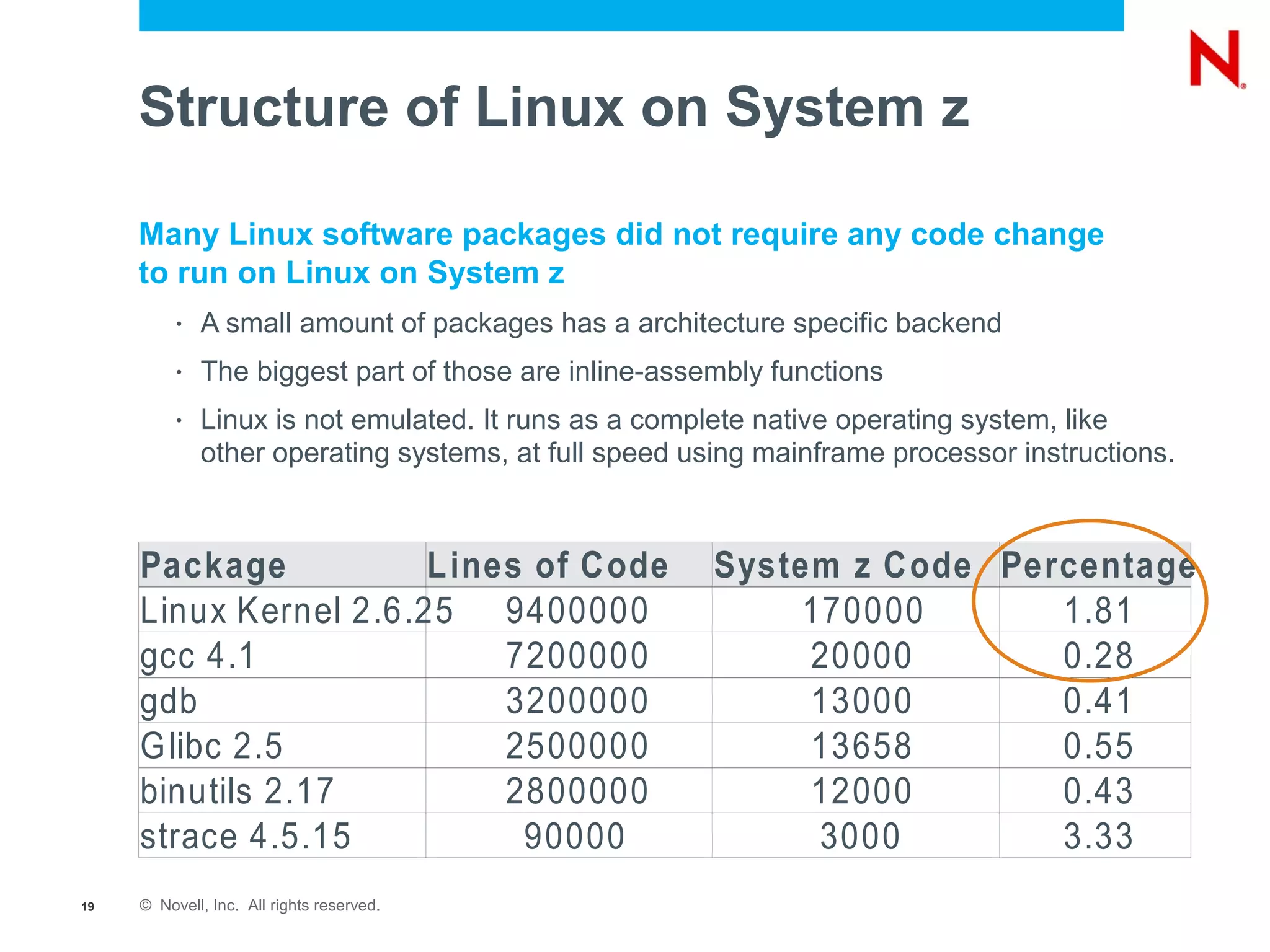
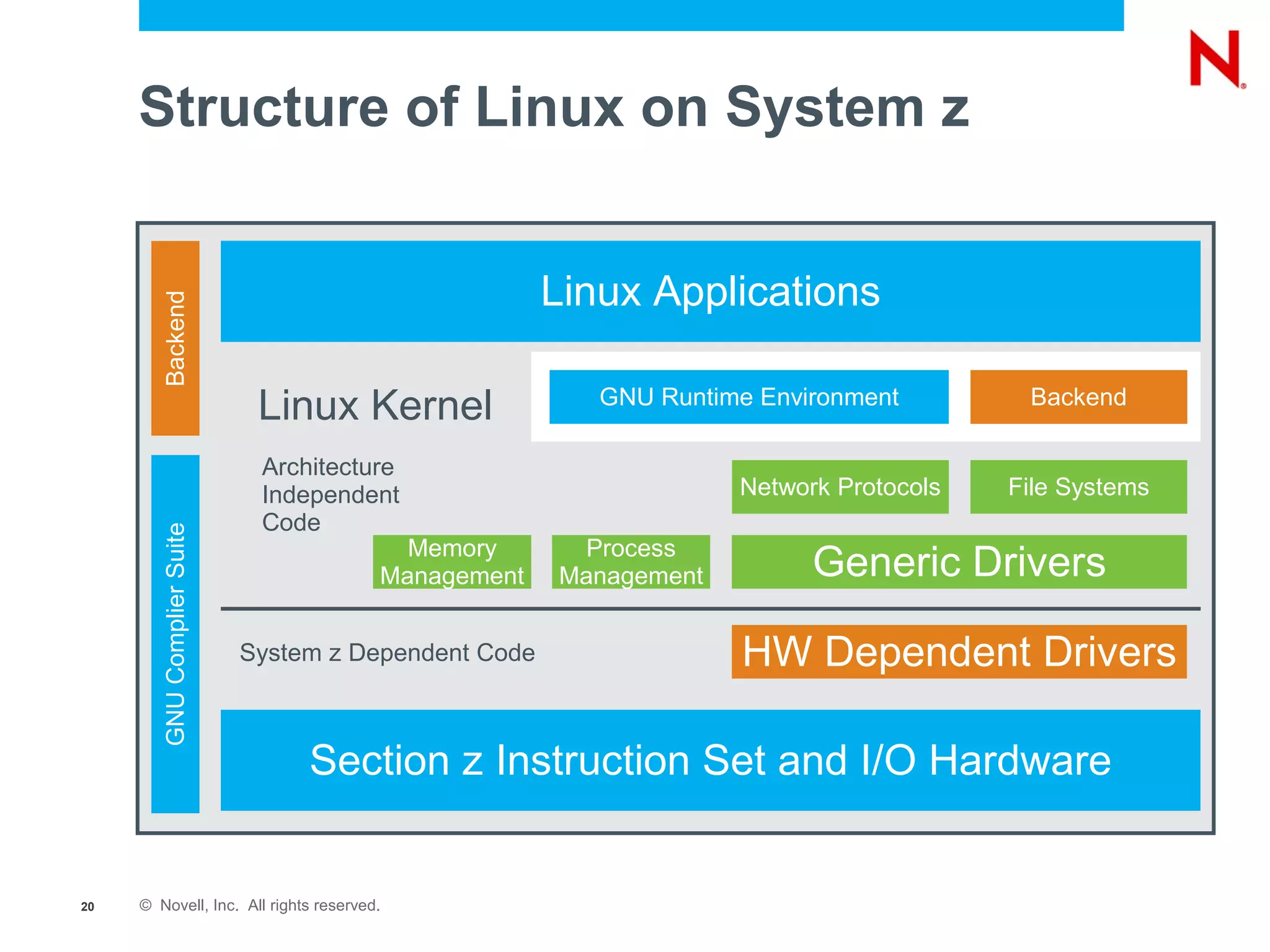
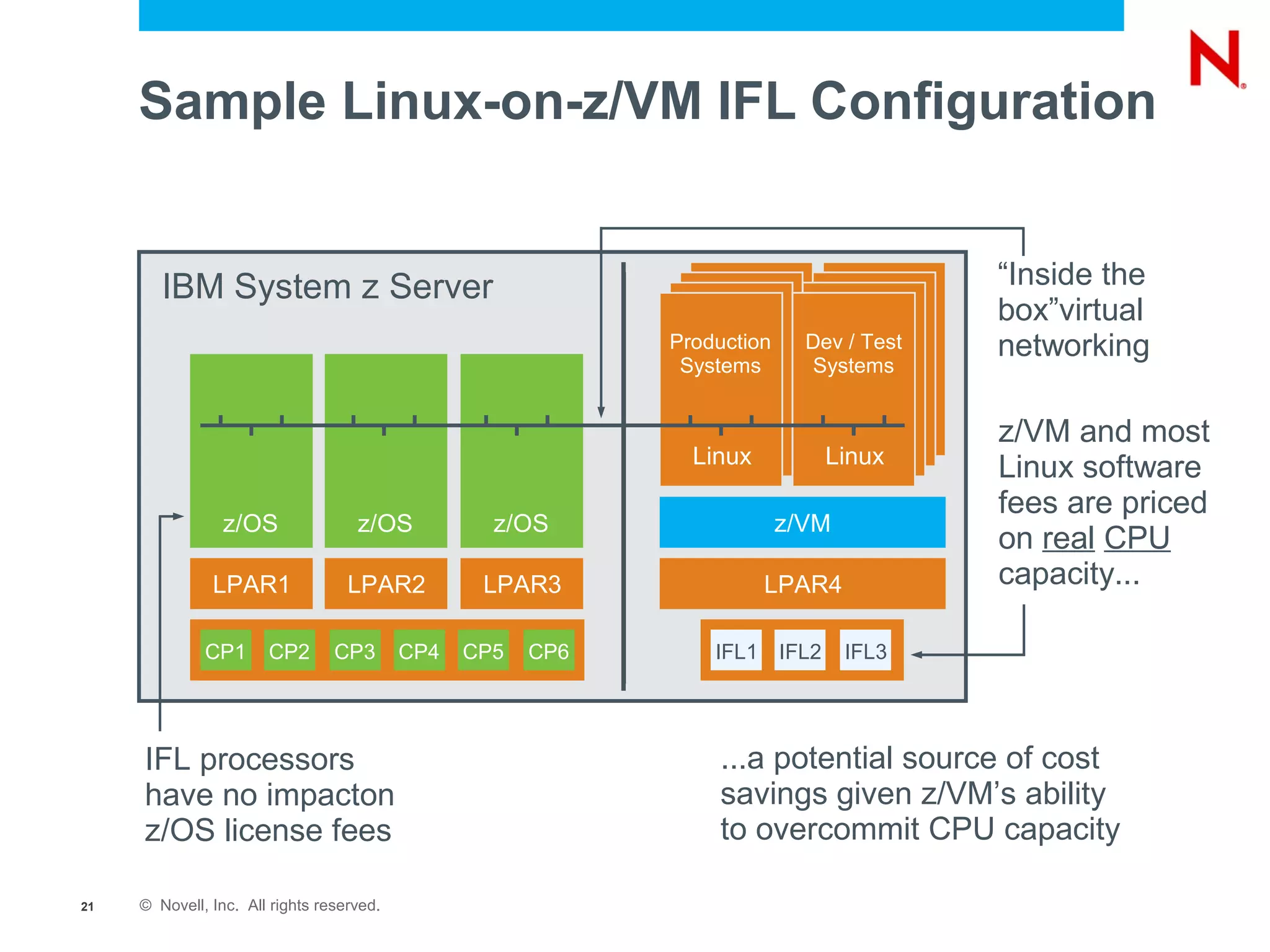
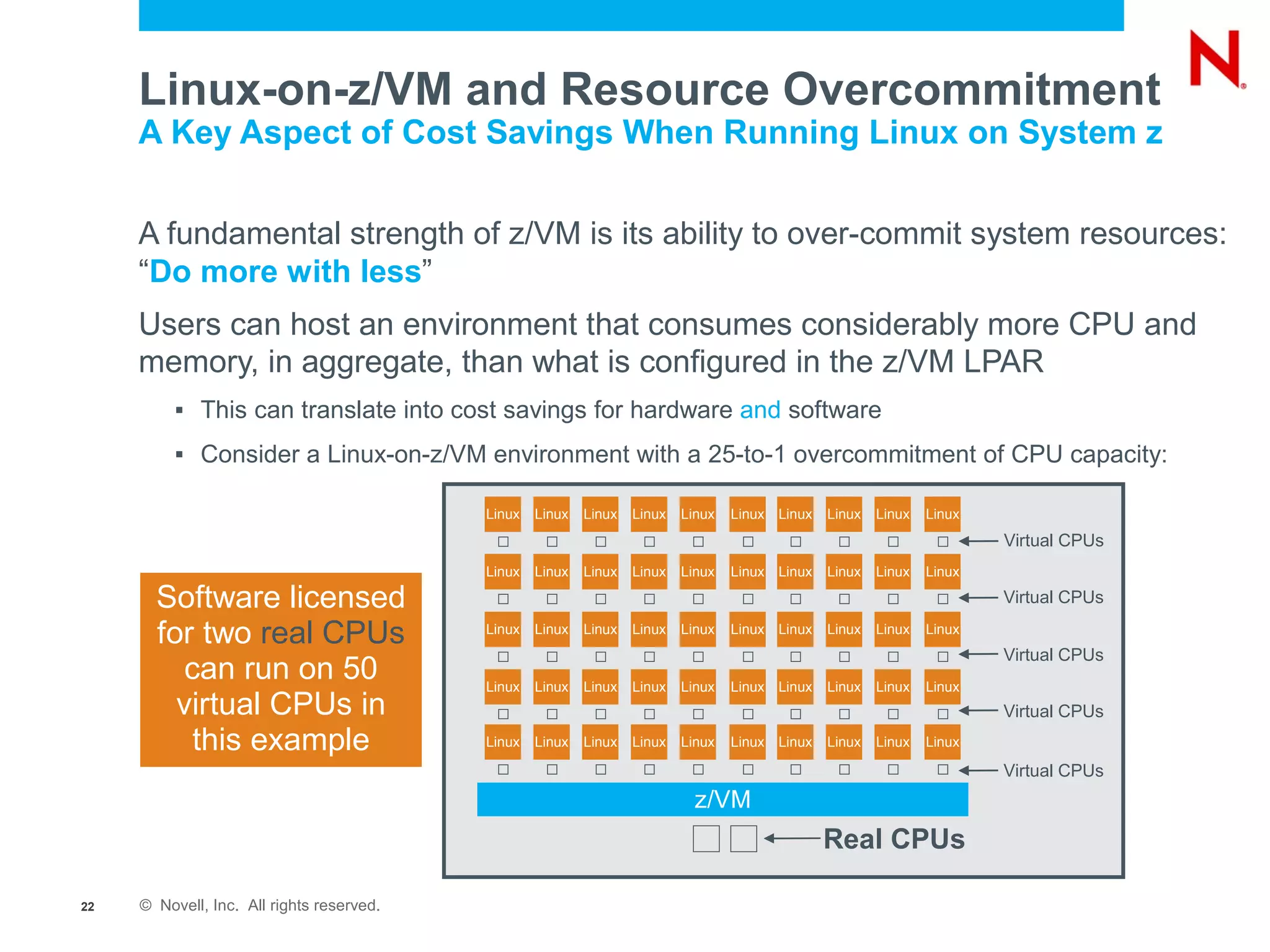
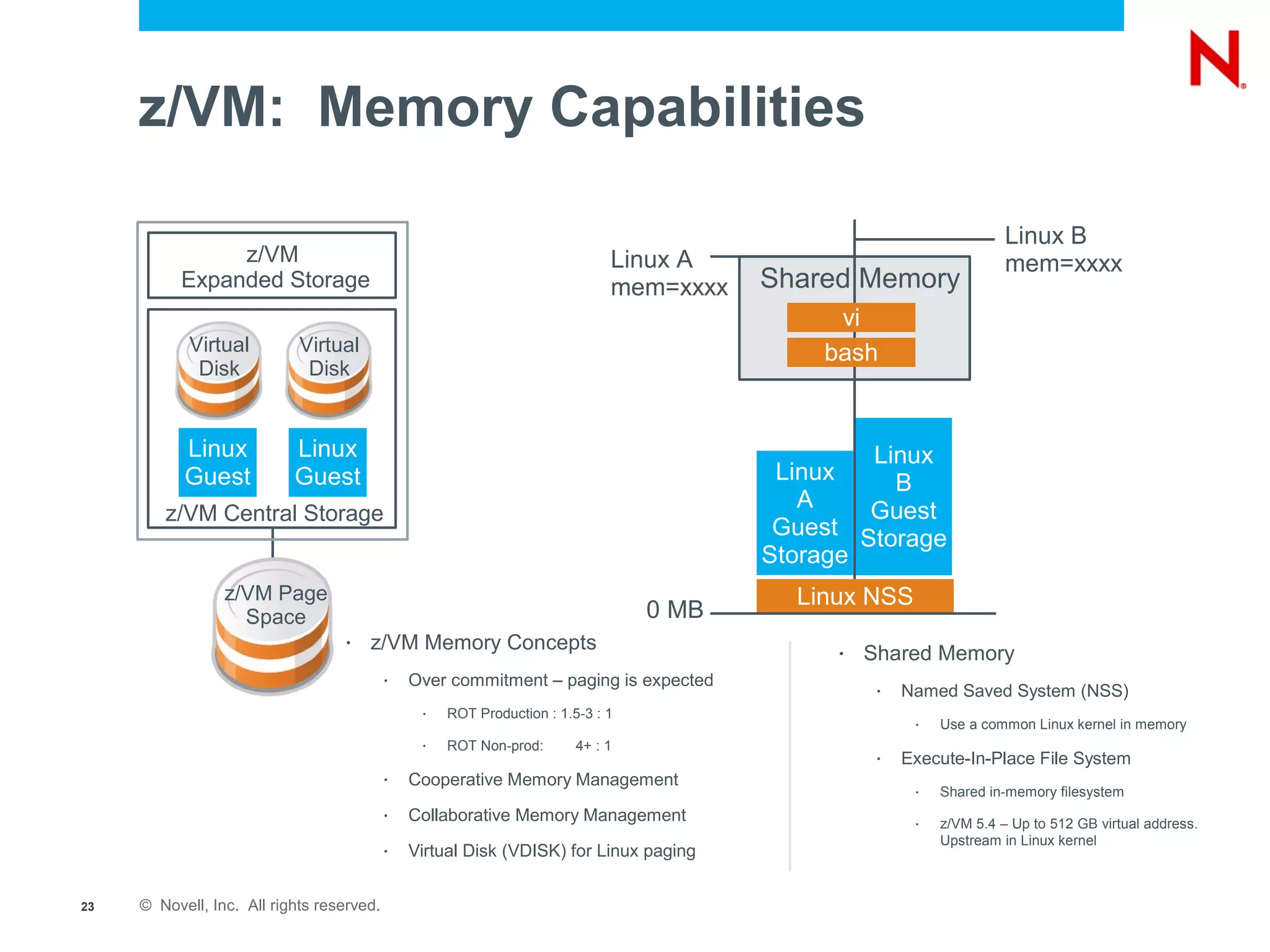
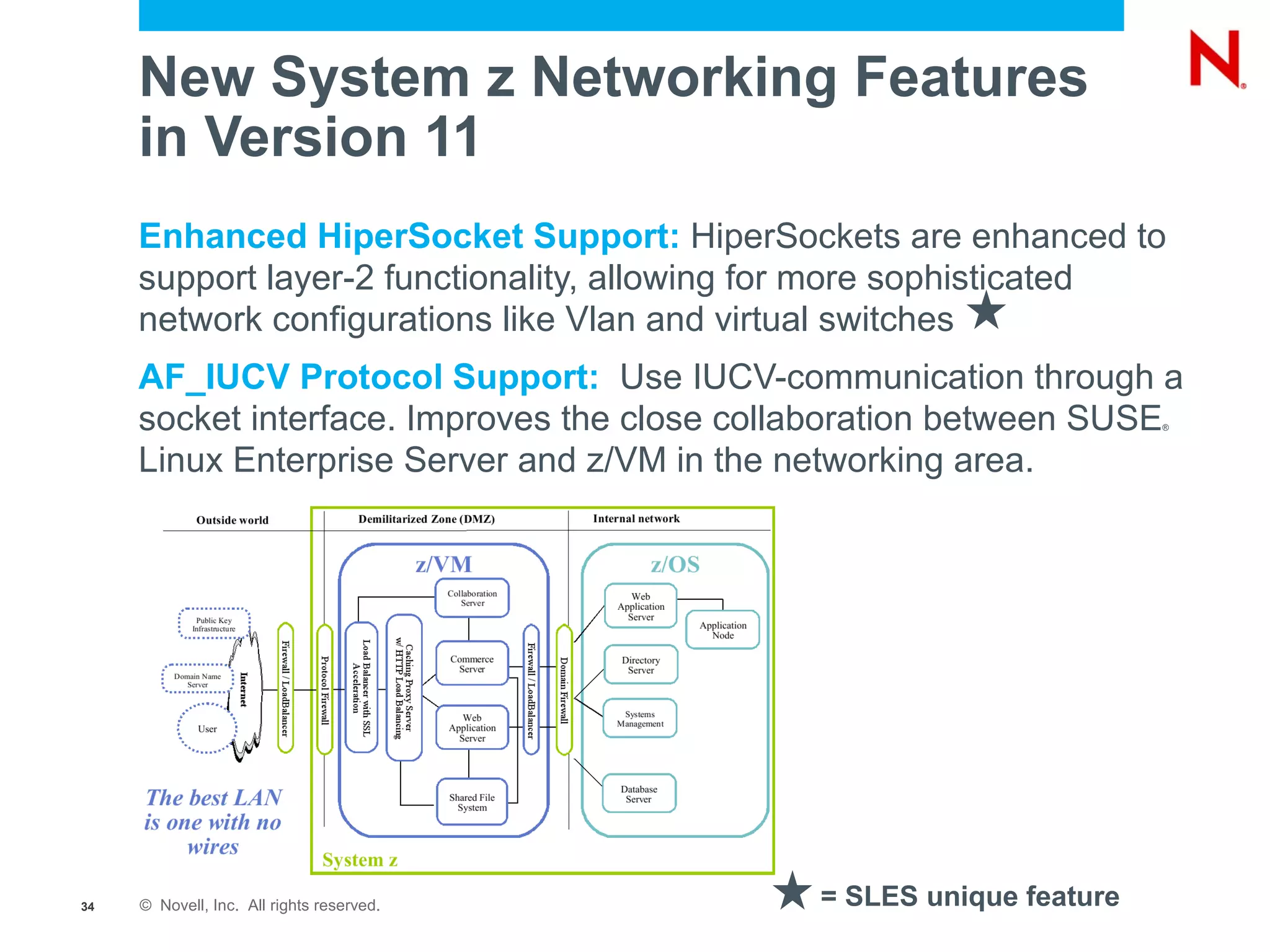
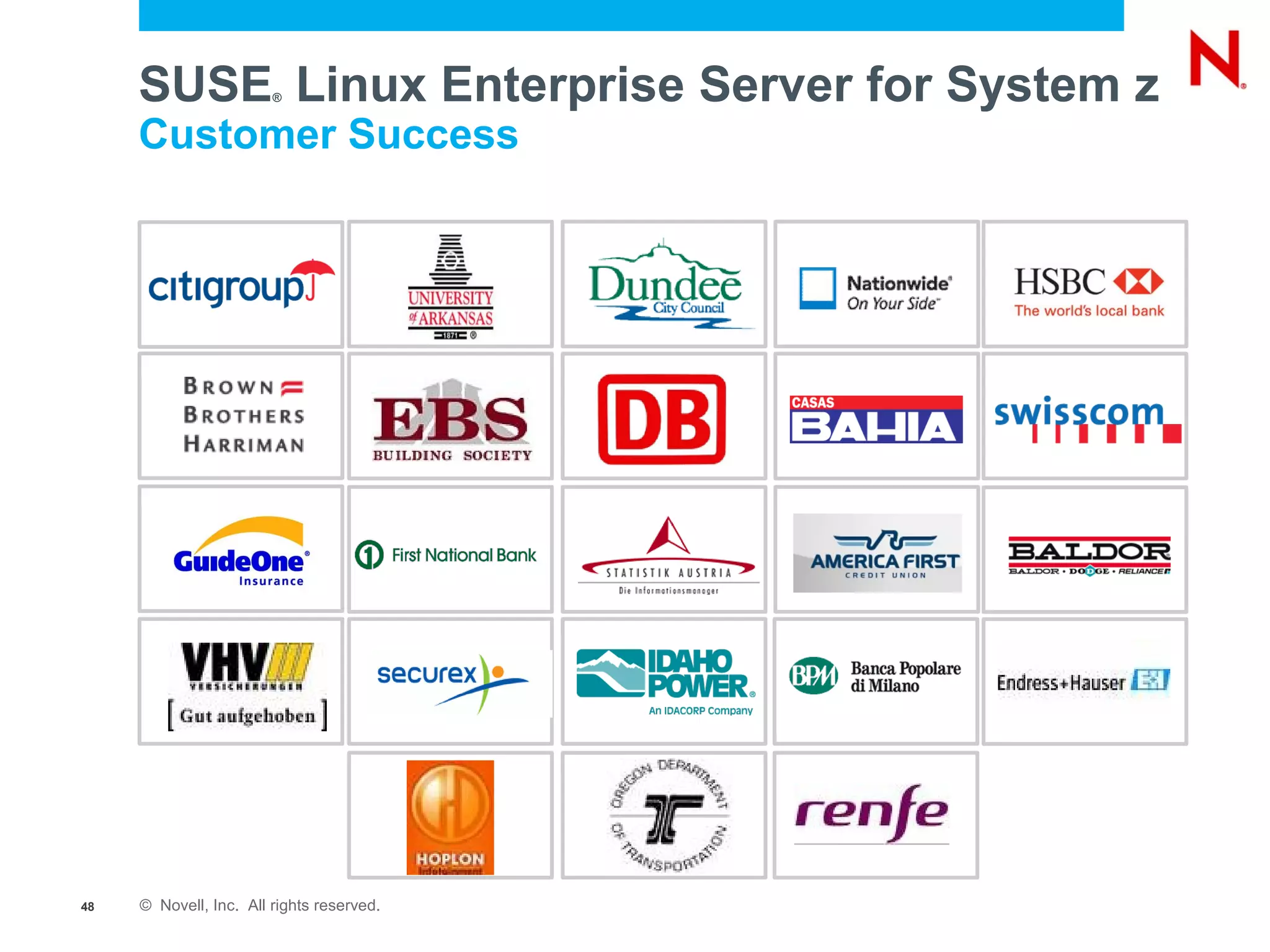
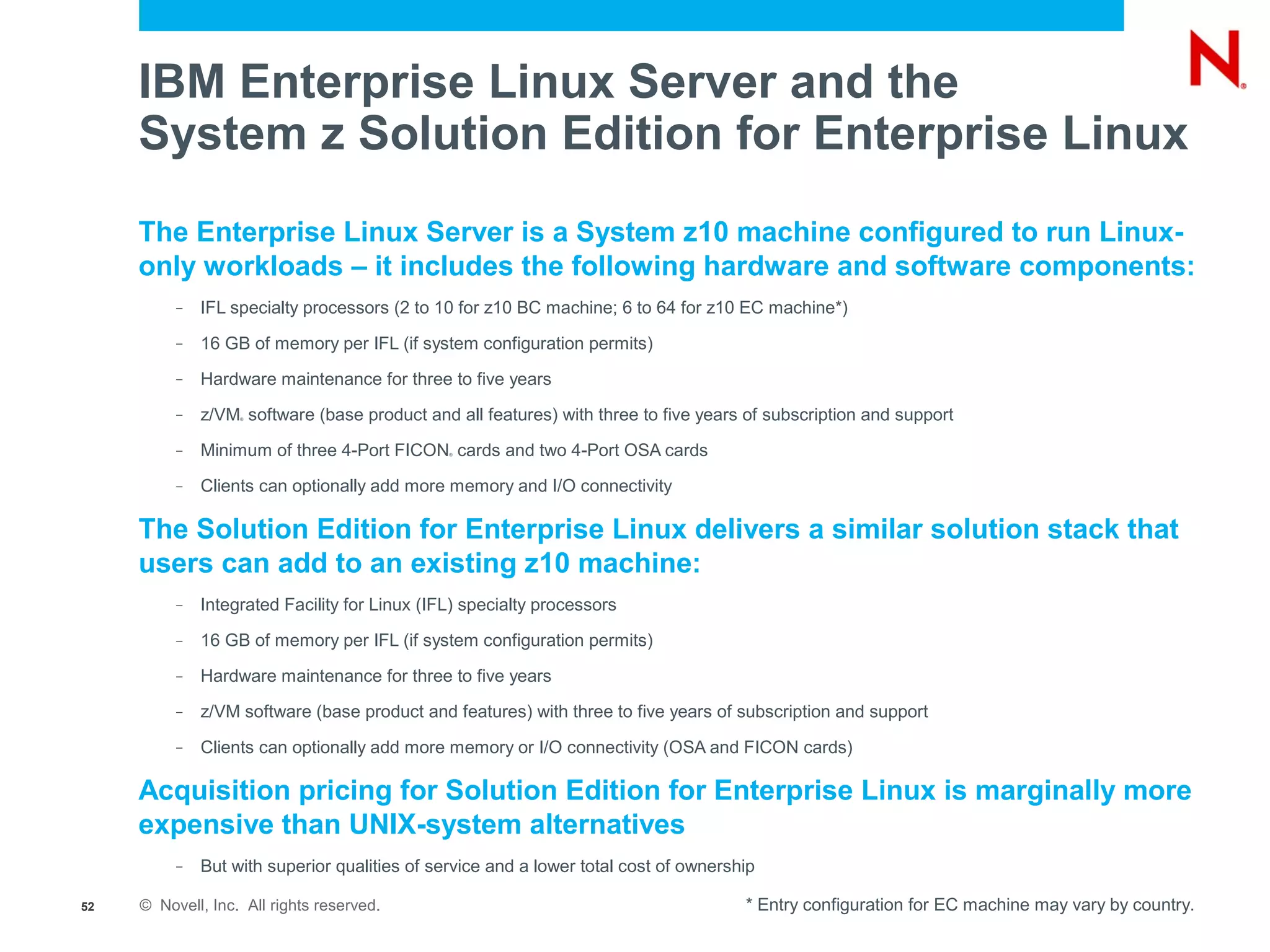
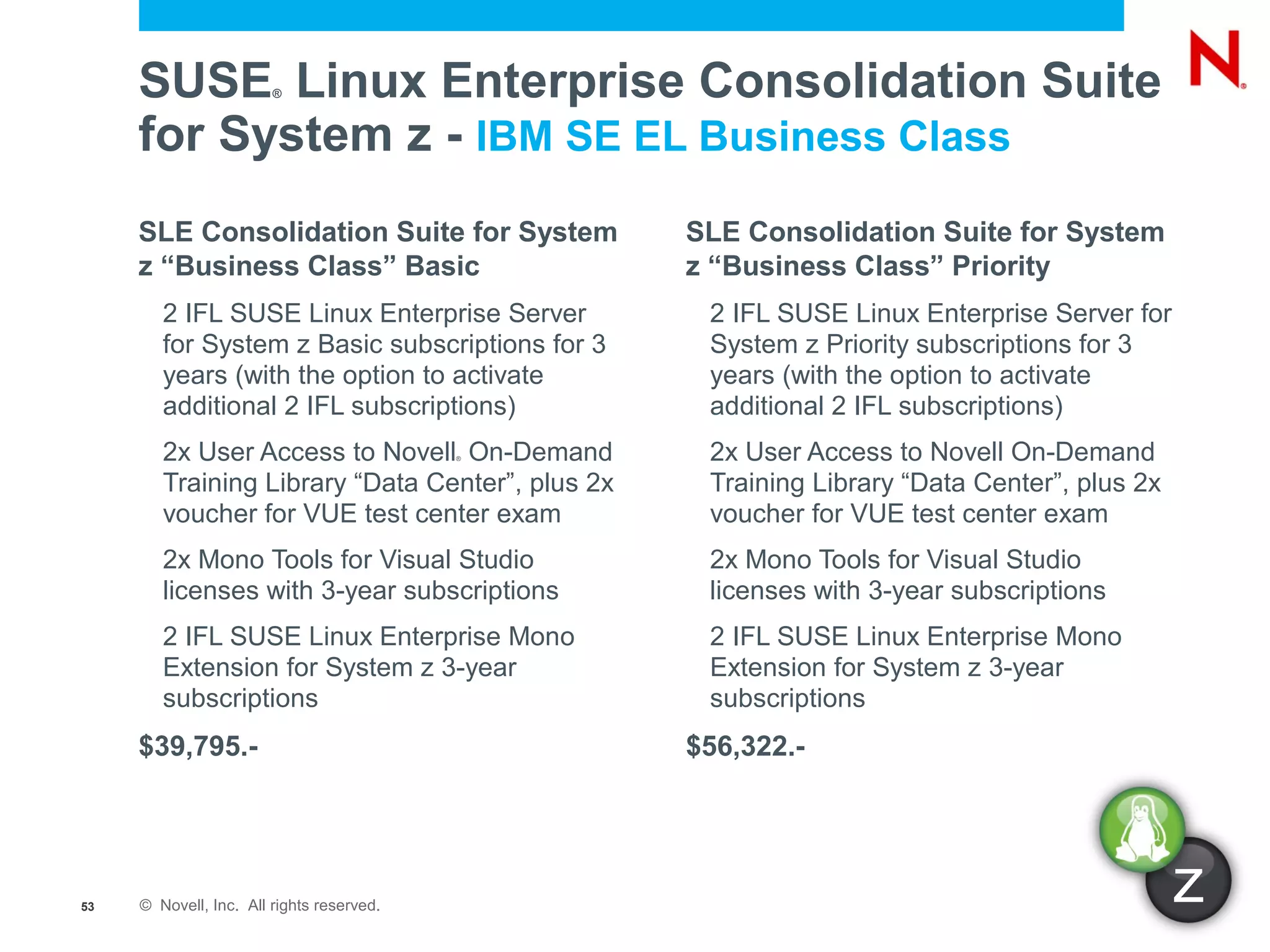
The document discusses the advancements and benefits of running Linux on IBM's System Z mainframe servers, highlighting their high efficiency, reliability, and cost-effectiveness compared to x86 systems. It details the long-standing partnership between IBM and Novell in supporting enterprise Linux, the historical milestones, and customer success stories in using SUSE Linux Enterprise Server for mission-critical applications. Future technologies and enhancements in Linux on System Z, including advanced virtualization and memory management capabilities, are also addressed.