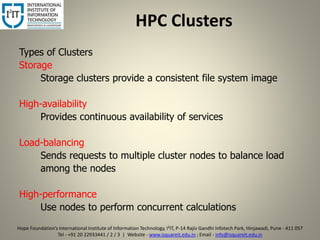
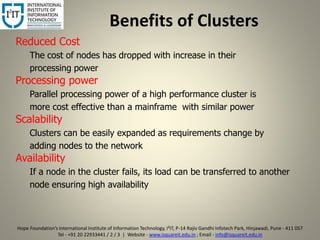
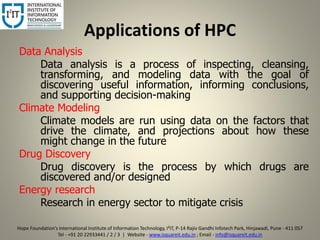
The document provides an overview of the Hope Foundation's International Institute of Information Technology (i2it) and its focus on high-performance computing (HPC) systems for scientific research and various applications. It highlights the benefits of HPC clusters, including cost effectiveness, scalability, and high availability, as well as their applications in data analysis, climate modeling, drug discovery, and energy research. The document concludes that HPC clusters offer efficient and flexible computing environments to solve demanding problems.