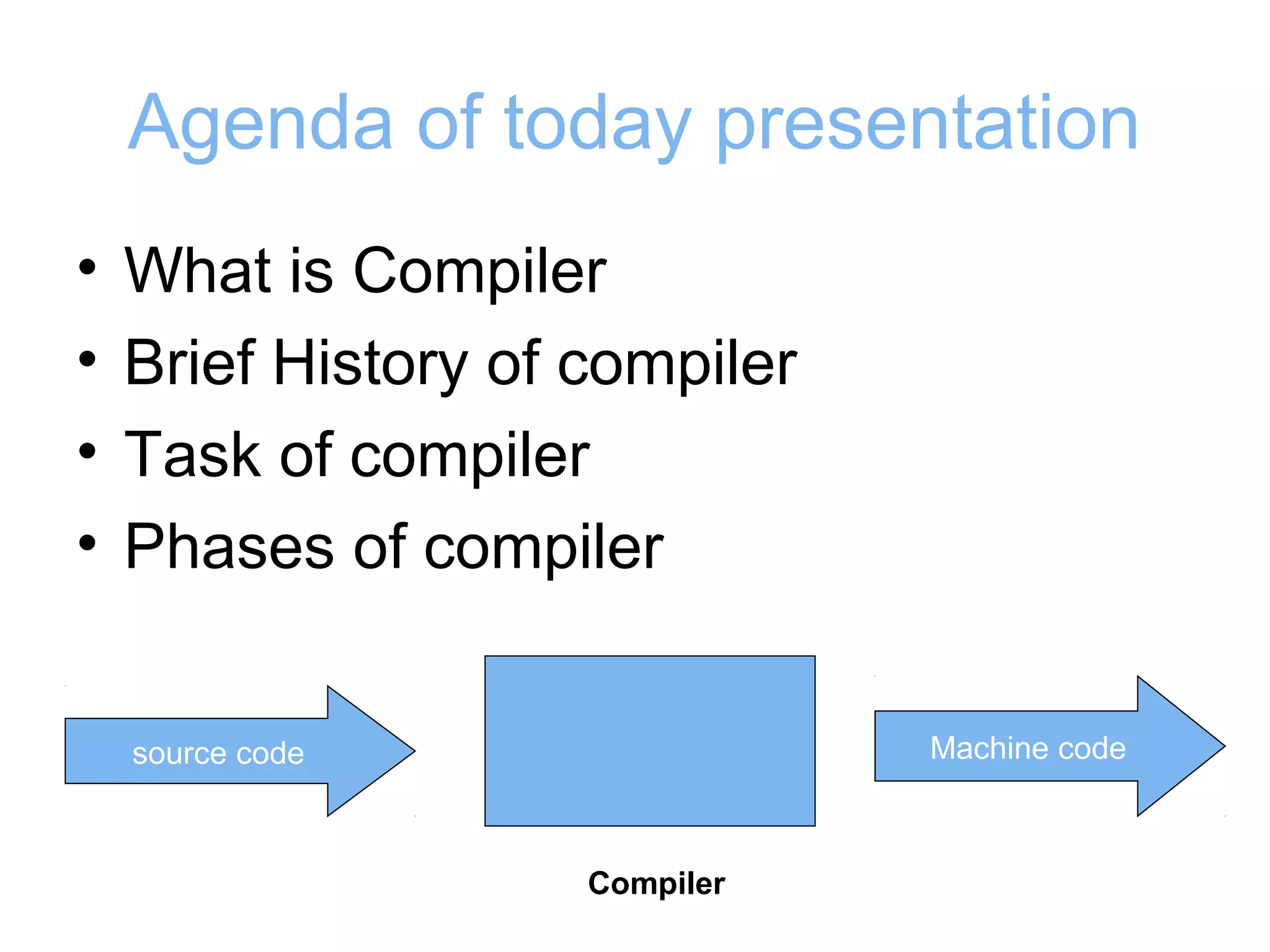
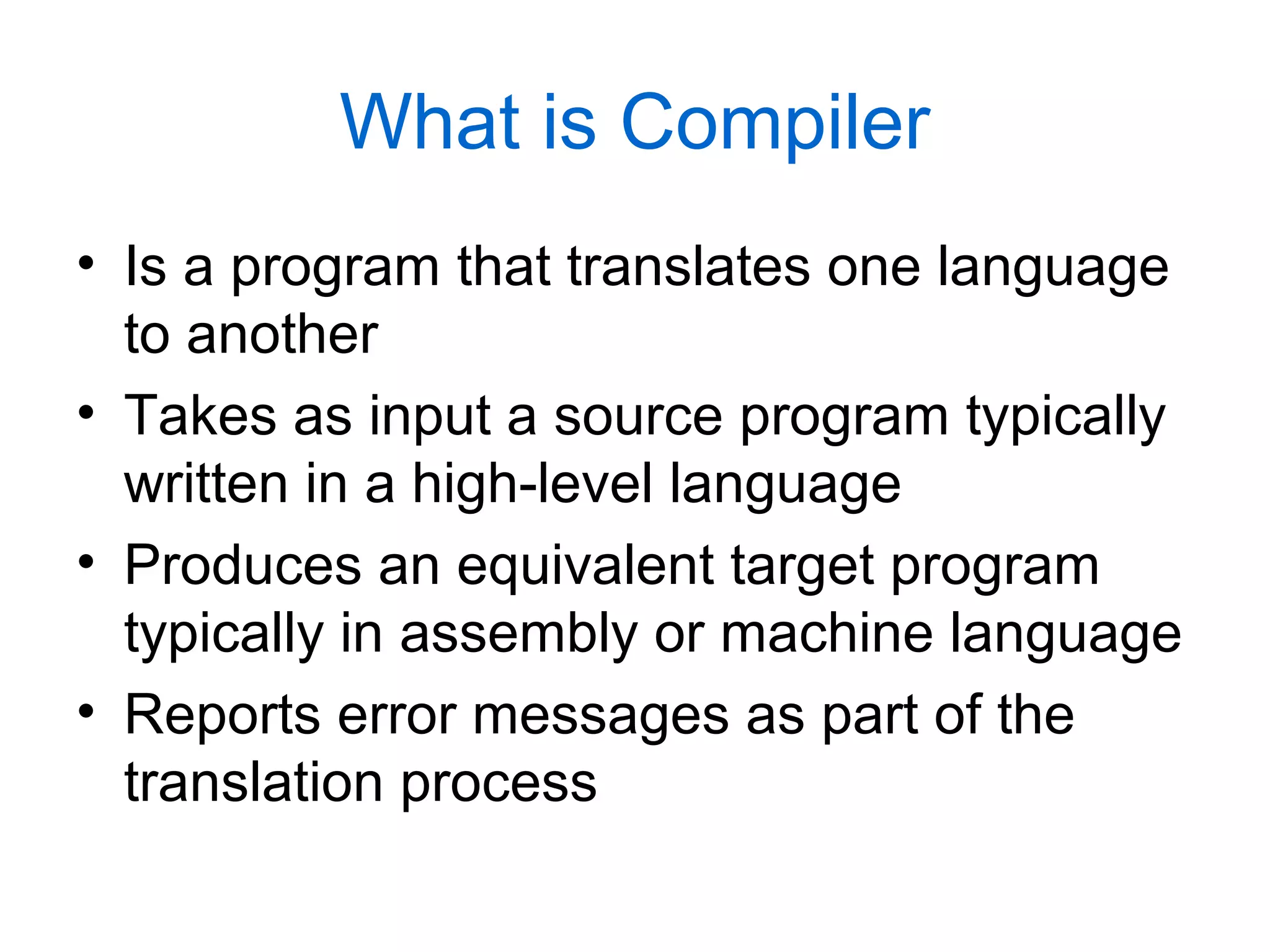
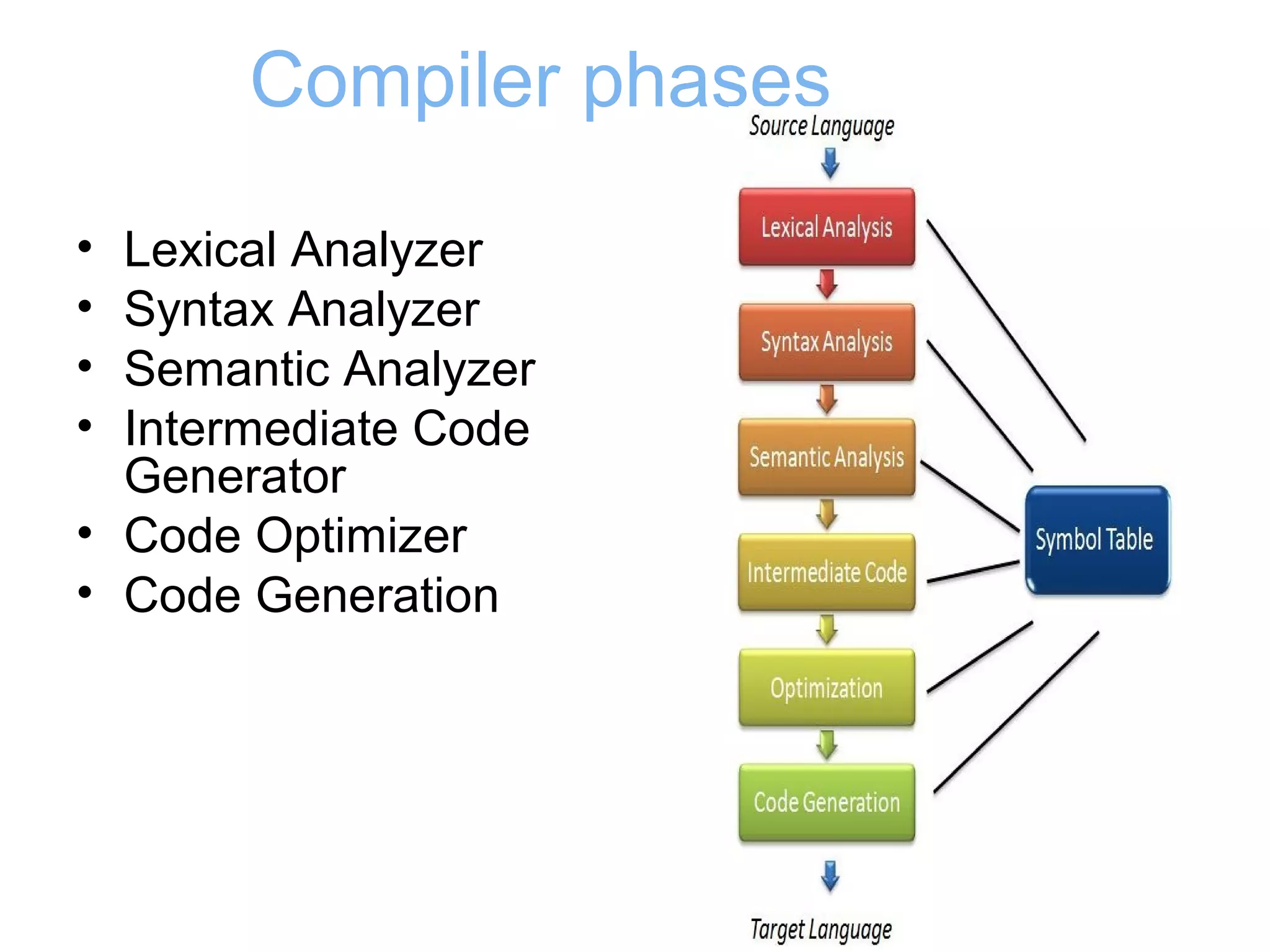
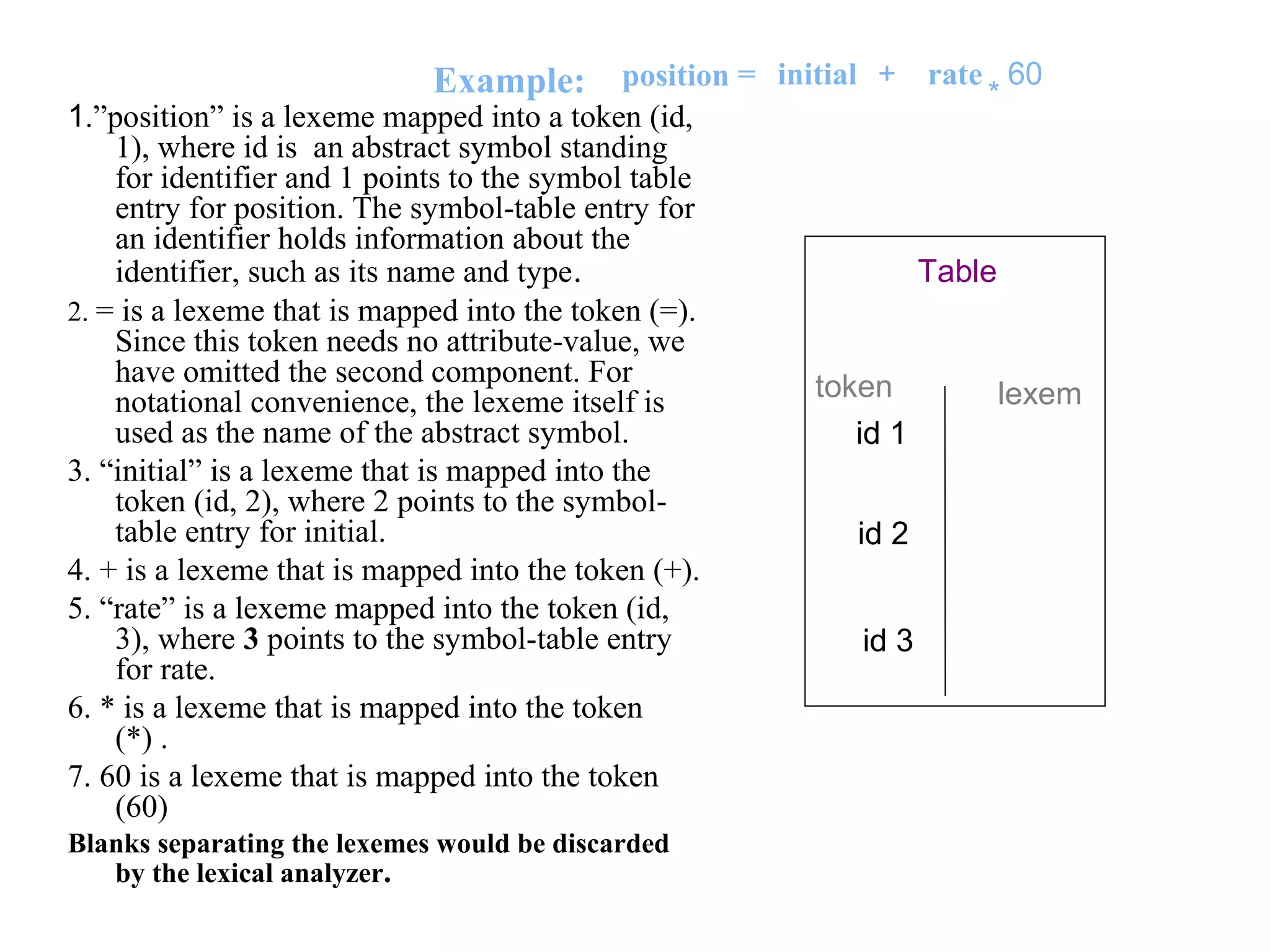
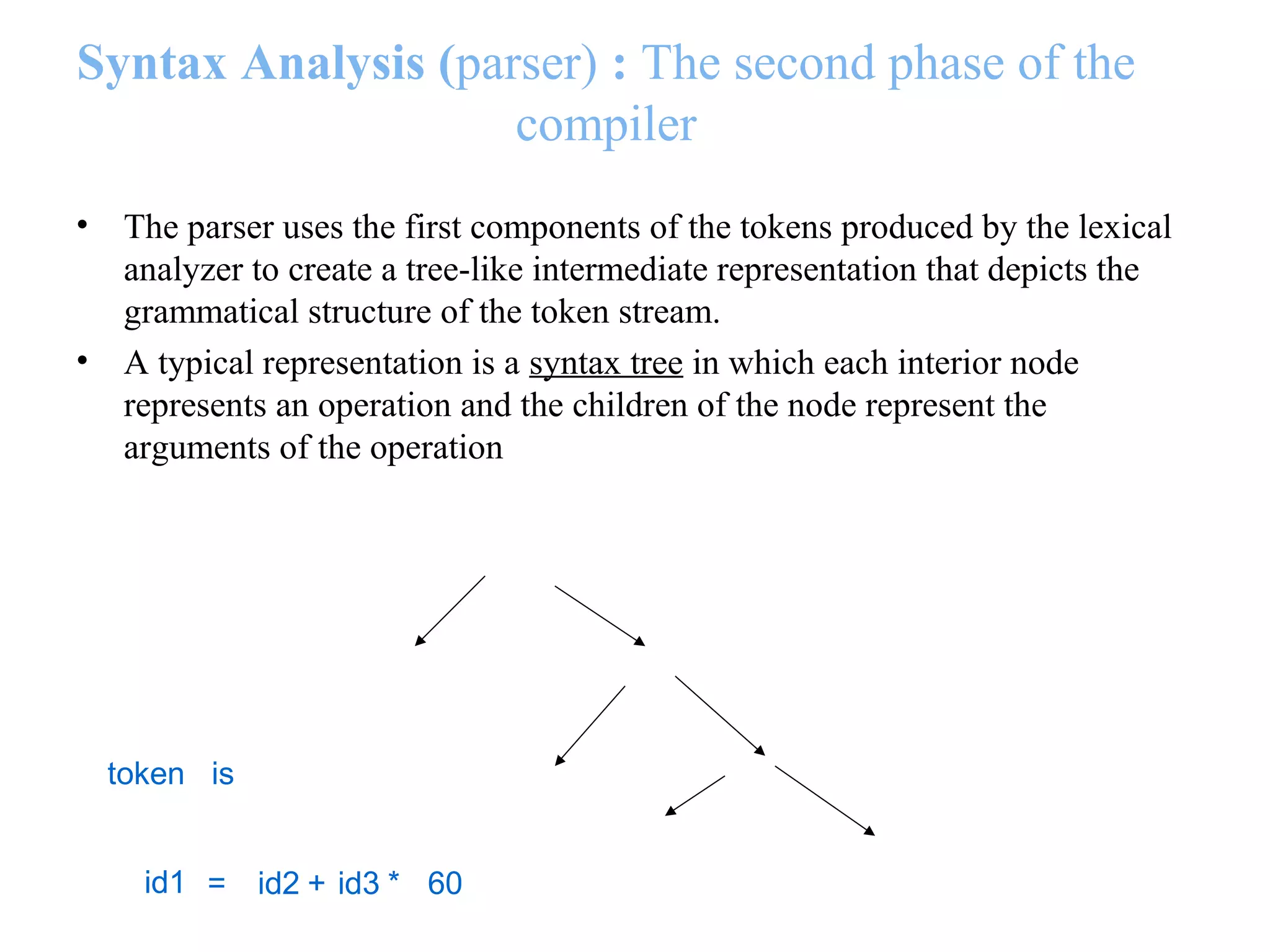
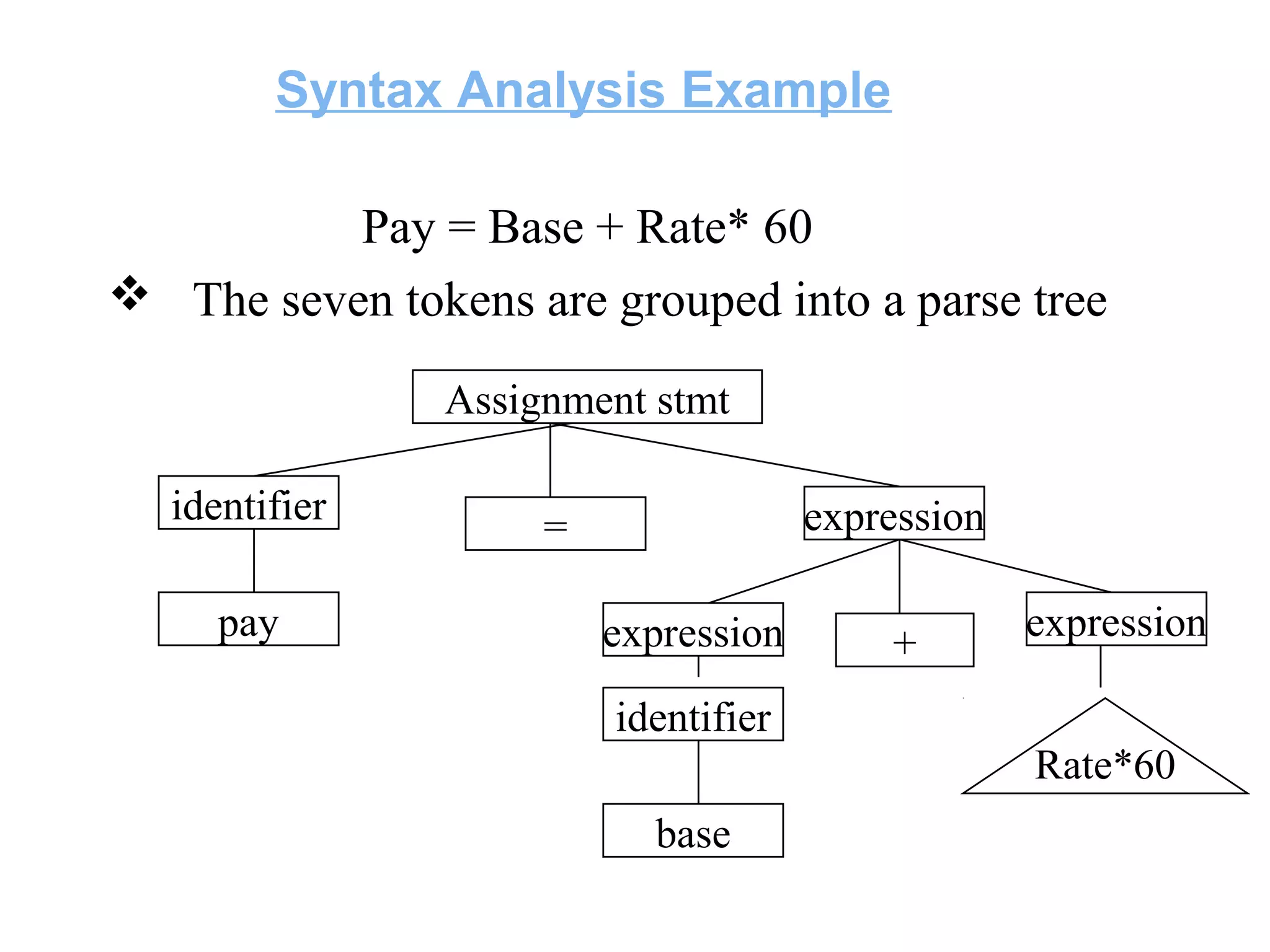
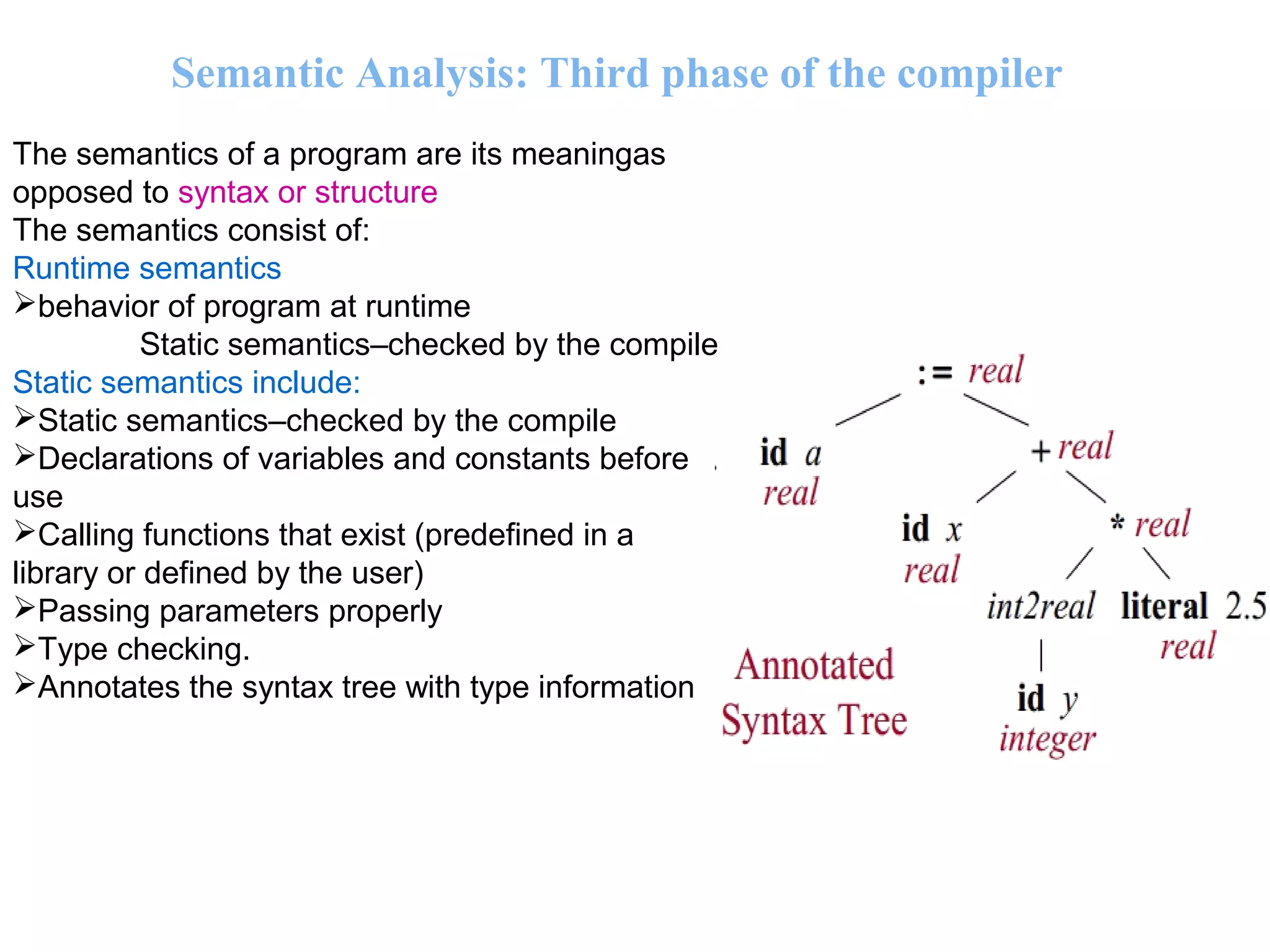
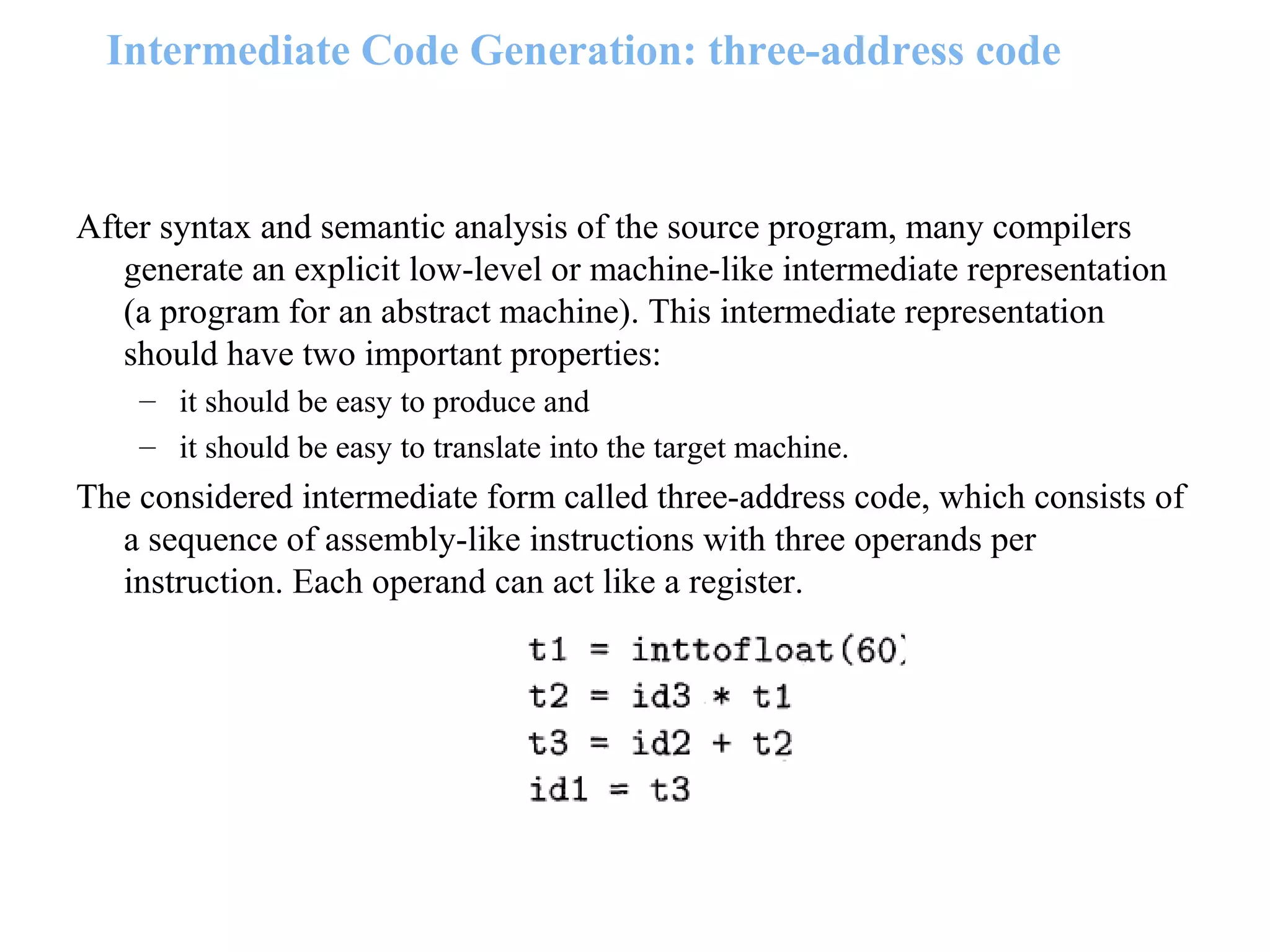
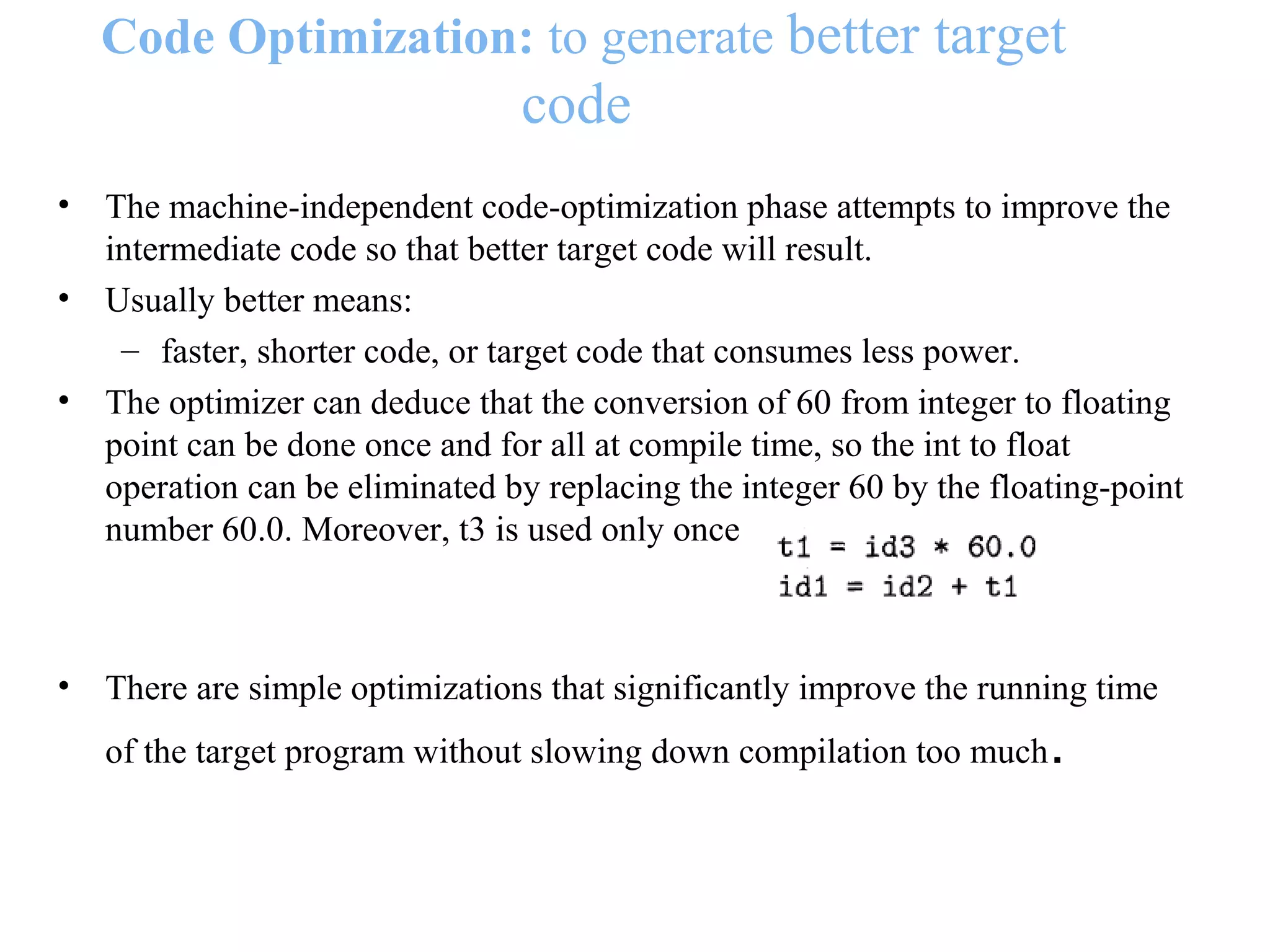
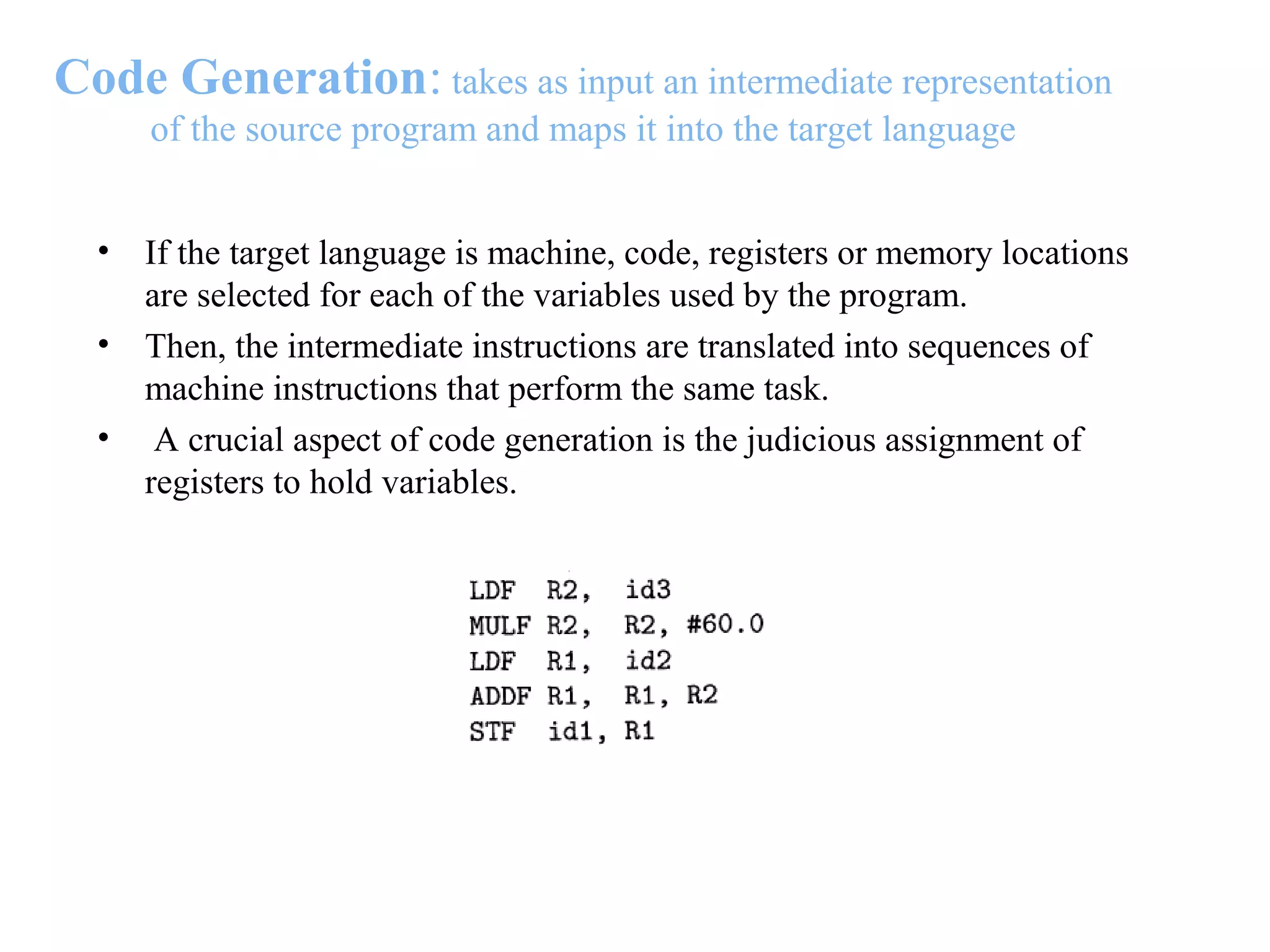
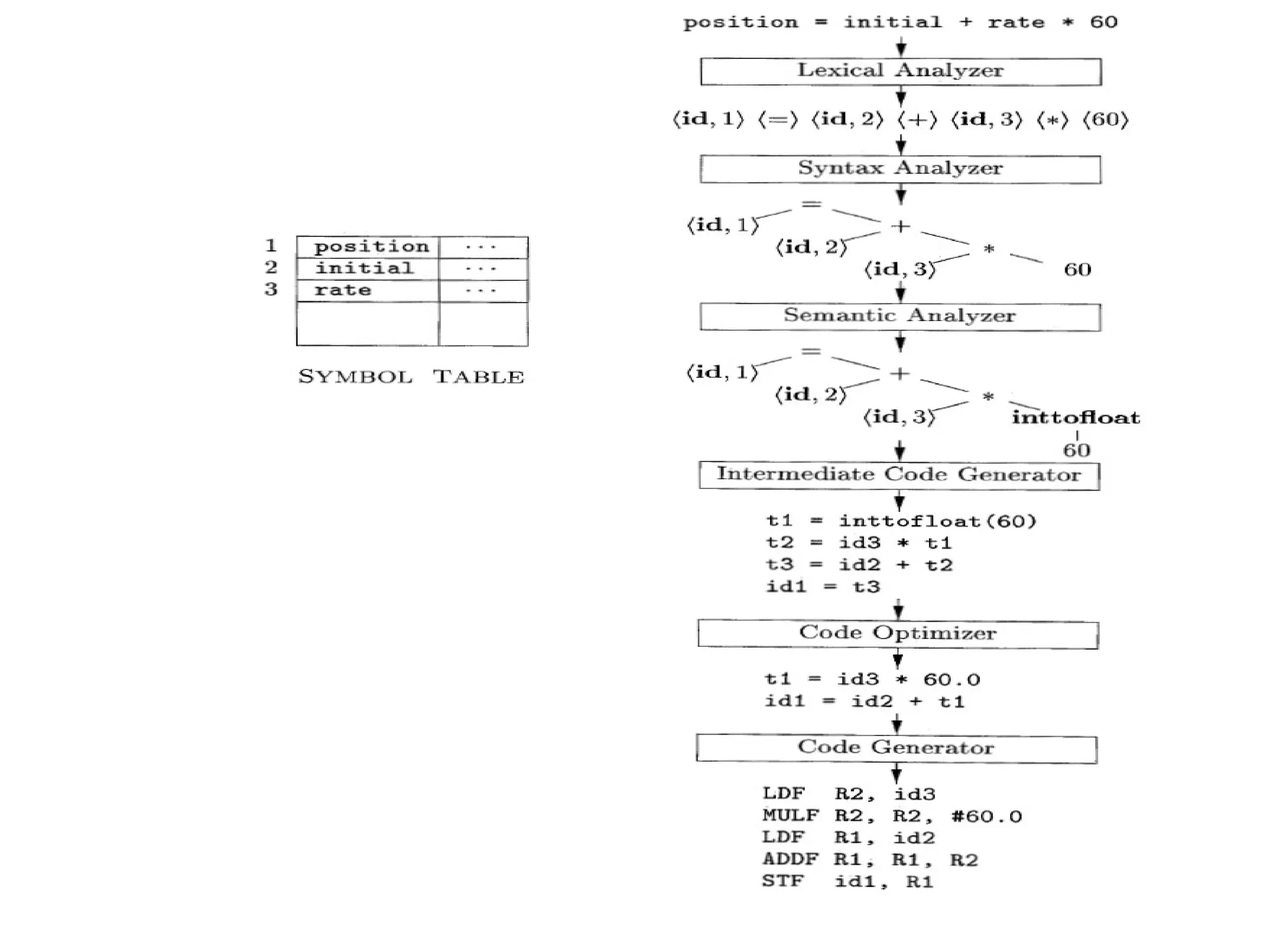
The document provides an overview of compilers, detailing their definition, history, tasks, and phases. It explains that a compiler translates high-level source code into machine code and outlines the main phases of compilation: lexical analysis, syntax analysis, semantic analysis, intermediate code generation, code optimization, and code generation. Each phase is described with its specific functions and examples, illustrating how compilers work to ensure proper program translation and execution.