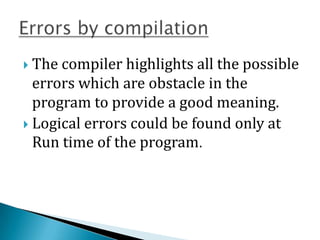
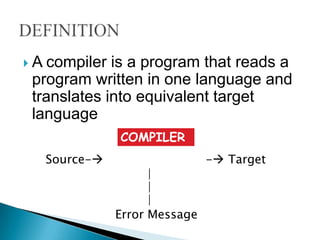
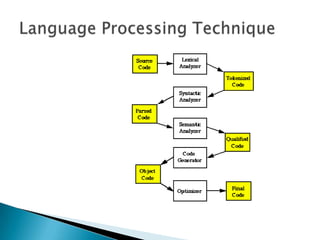
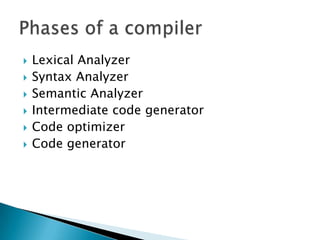
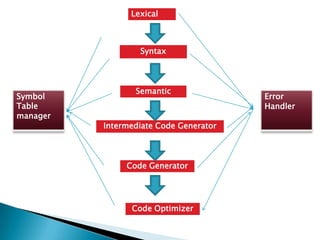
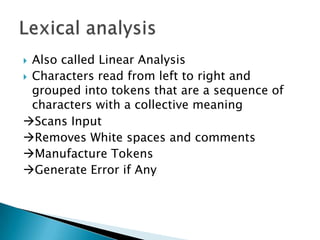
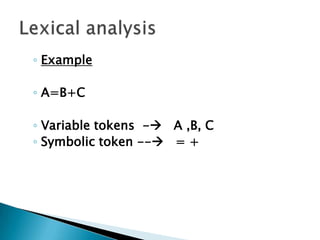
A compiler is a program that translates a program written in one language into an equivalent target language. The front end checks syntax and semantics, while the back end translates the source code into assembly code. The compiler performs lexical analysis, syntax analysis, semantic analysis, code generation, optimization, and error handling. It identifies errors at compile time to help produce efficient, error-free code.

![ Also called as Hierarchial Analysis
A syntax tree[also called as parse tree] is generated
where
◦ Operators Interior nodes
◦ Operands Children of node for operators.
=
A + Interior
B C Children](https://image.slidesharecdn.com/compilers-111229101725-phpapp02/85/Compilers-11-320.jpg)
![ Input : Concrete Syntax Tree[Parse Tree] or
Abstract Syntax Tree
The tree is converted into a linear sequence
of instructions, usually in an intermediate
language such as three address code.
This is an Early stage of Code generation](https://image.slidesharecdn.com/compilers-111229101725-phpapp02/85/Compilers-14-320.jpg)
![Concrete Parse tree
Abstract syntax tree
Converted into a linear sequence of instructions
Results in 3AC [ 3 Address Code]](https://image.slidesharecdn.com/compilers-111229101725-phpapp02/85/Compilers-15-320.jpg)
![ Loop optimization
Data flow
Code generation
Functional language
Interprocedural optimizations
SSA [Static Single Assignment] based
optimizations](https://image.slidesharecdn.com/compilers-111229101725-phpapp02/85/Compilers-22-320.jpg)