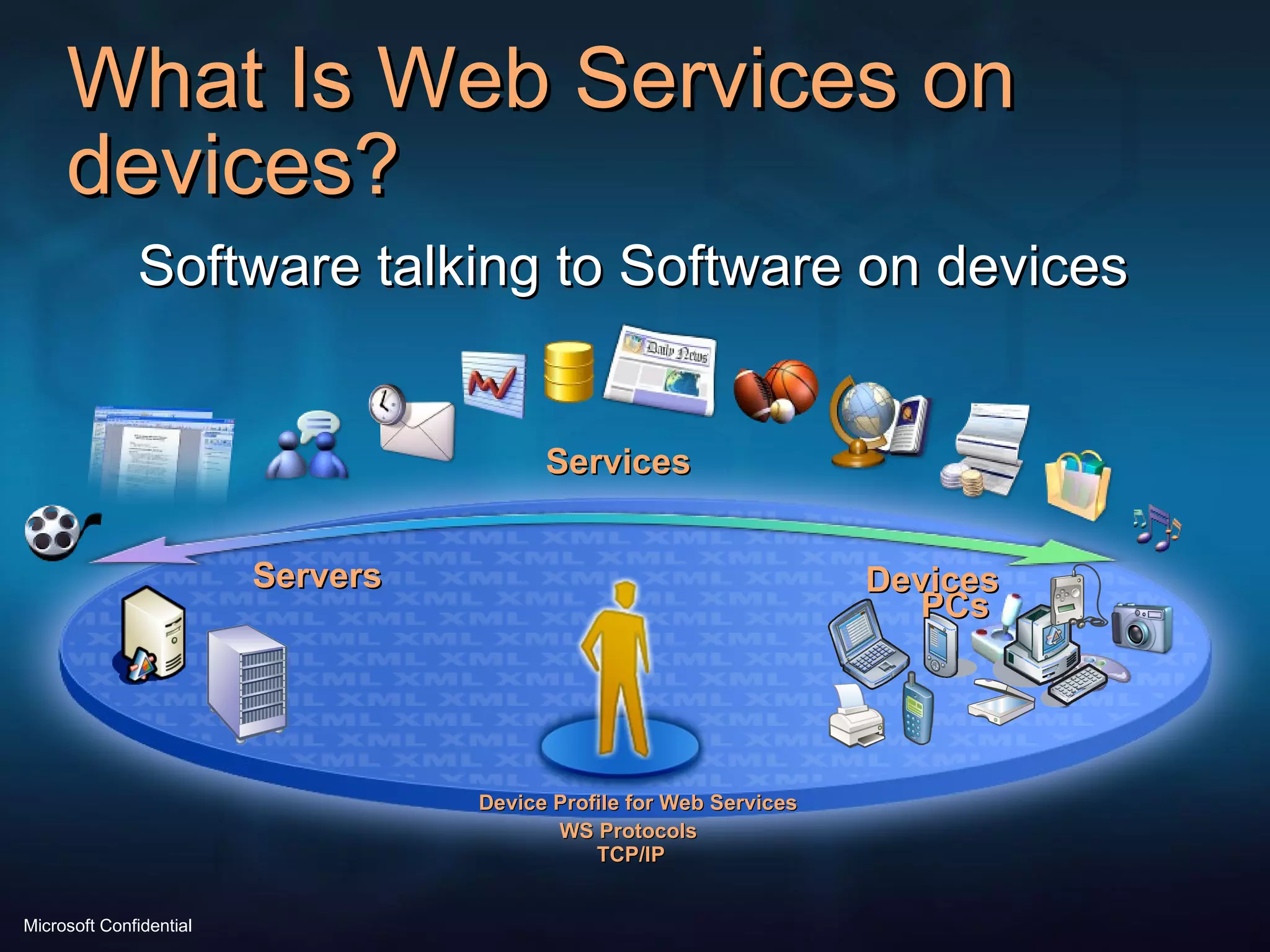
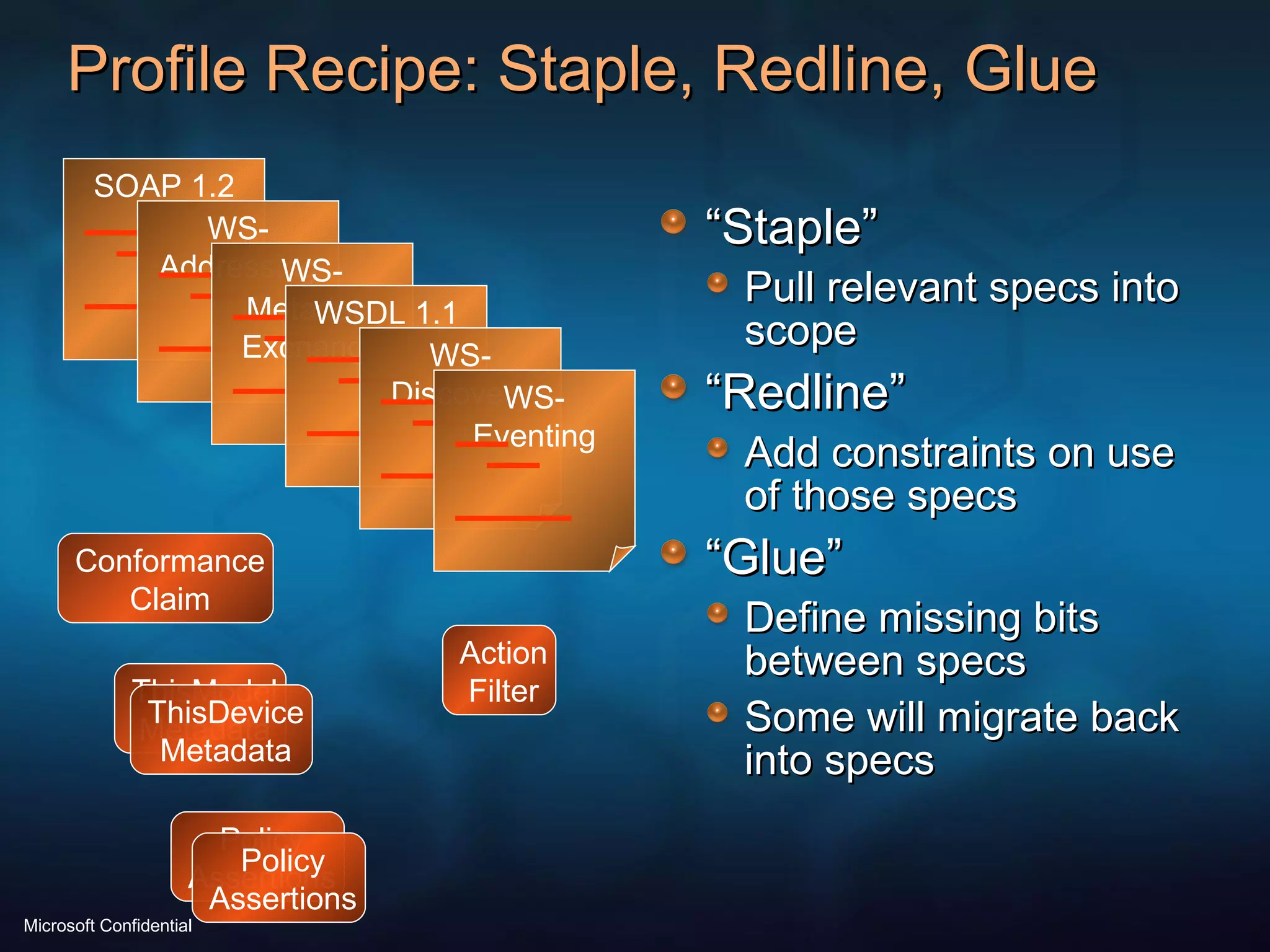
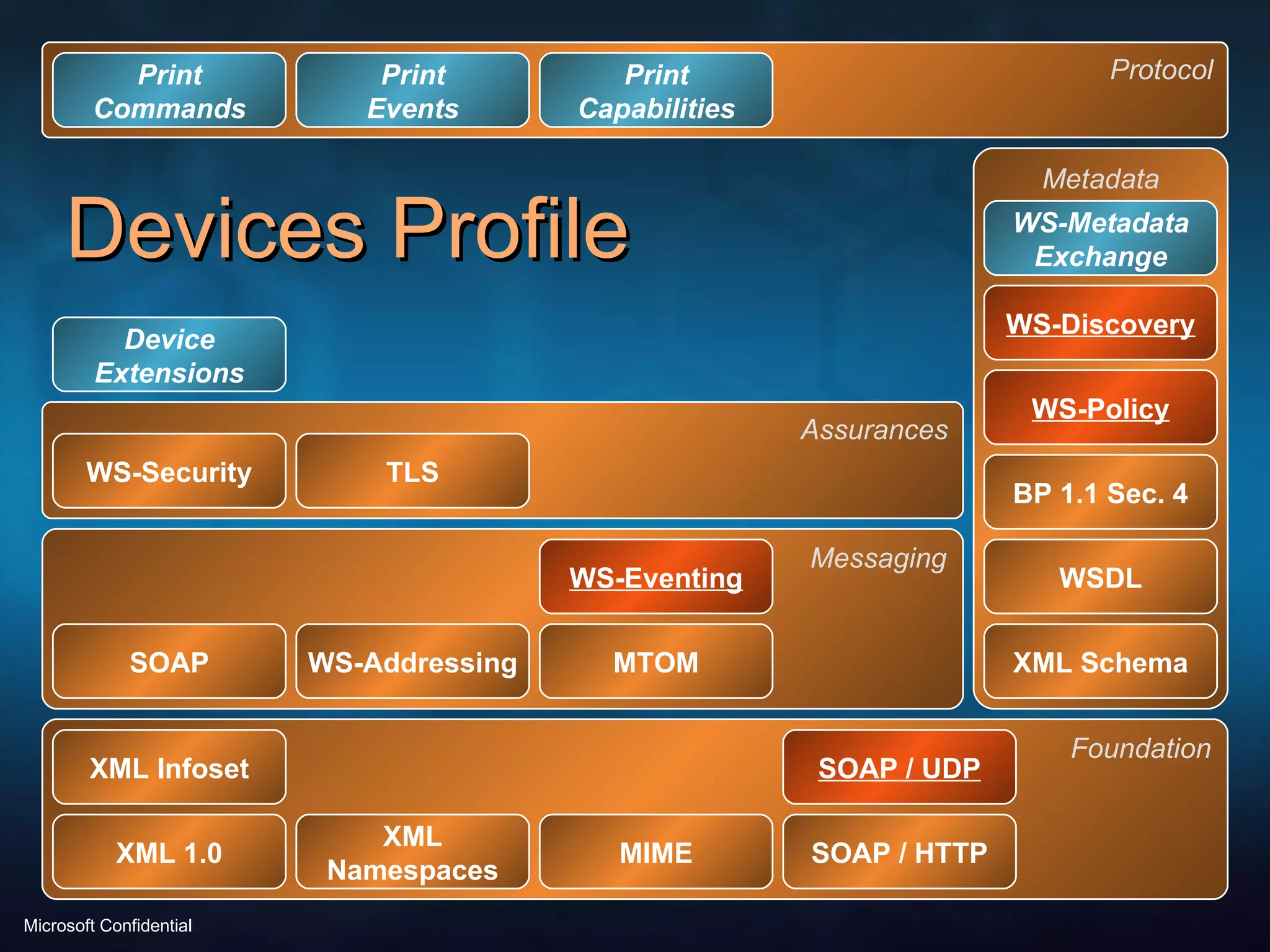
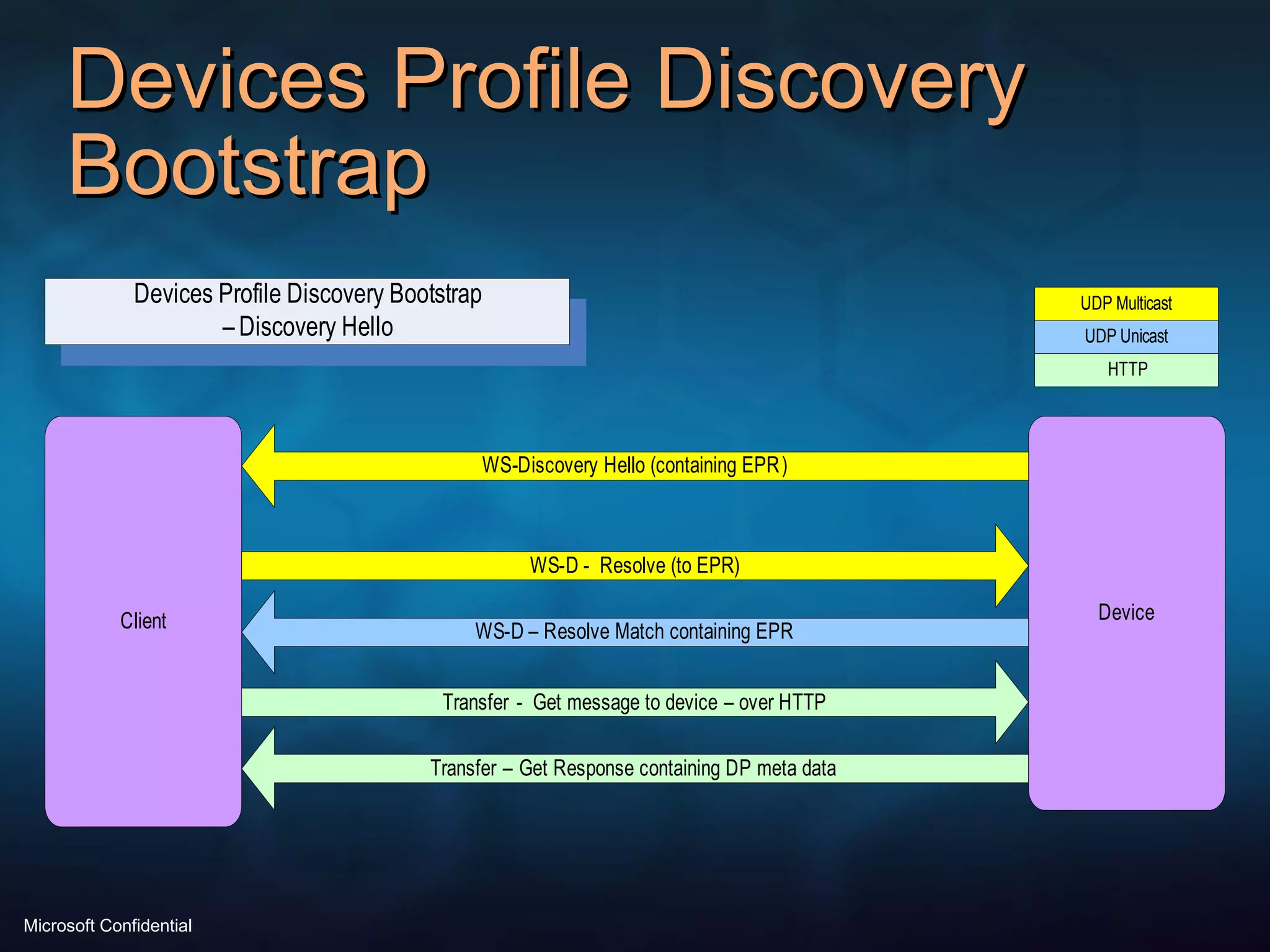
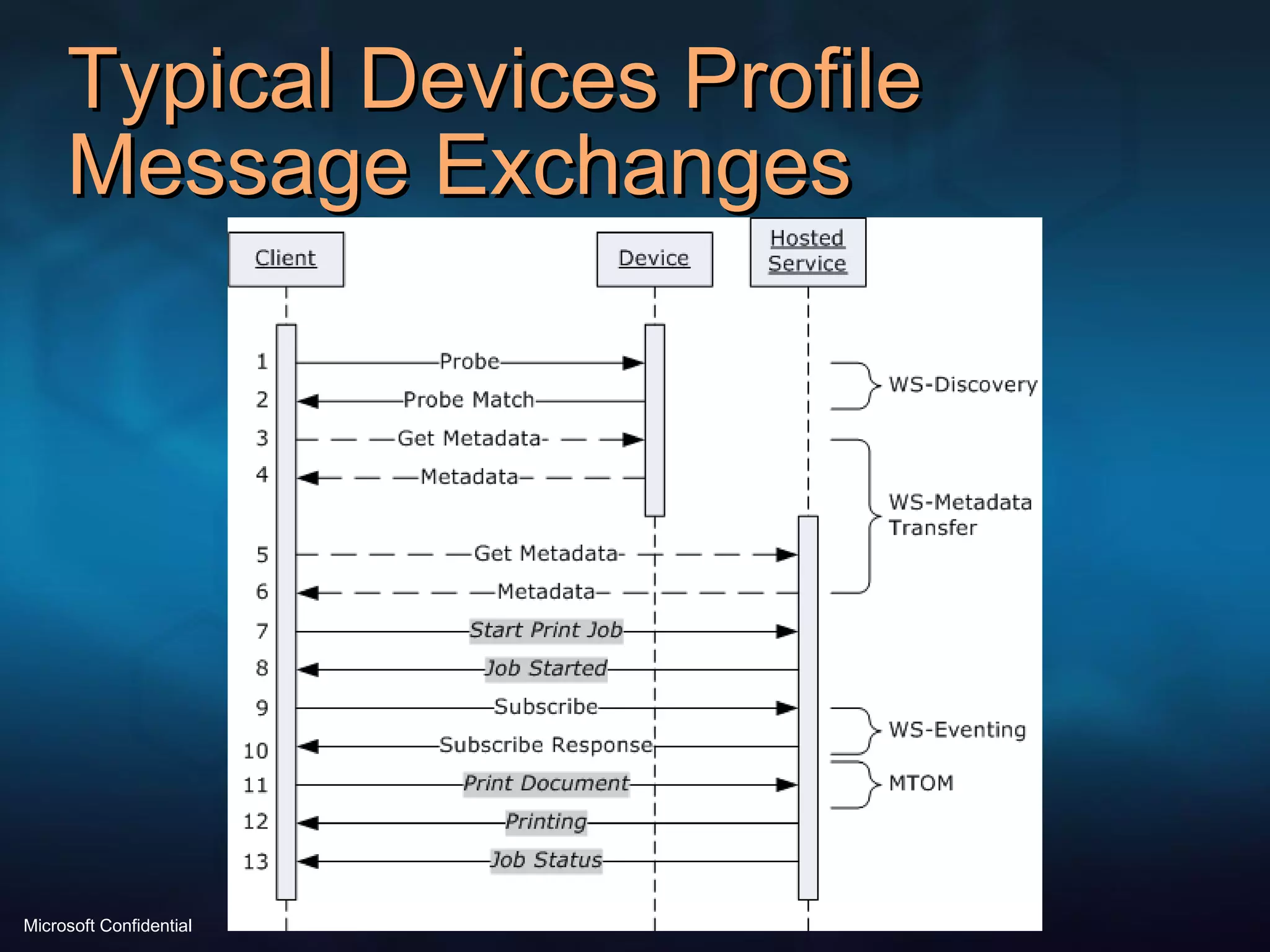
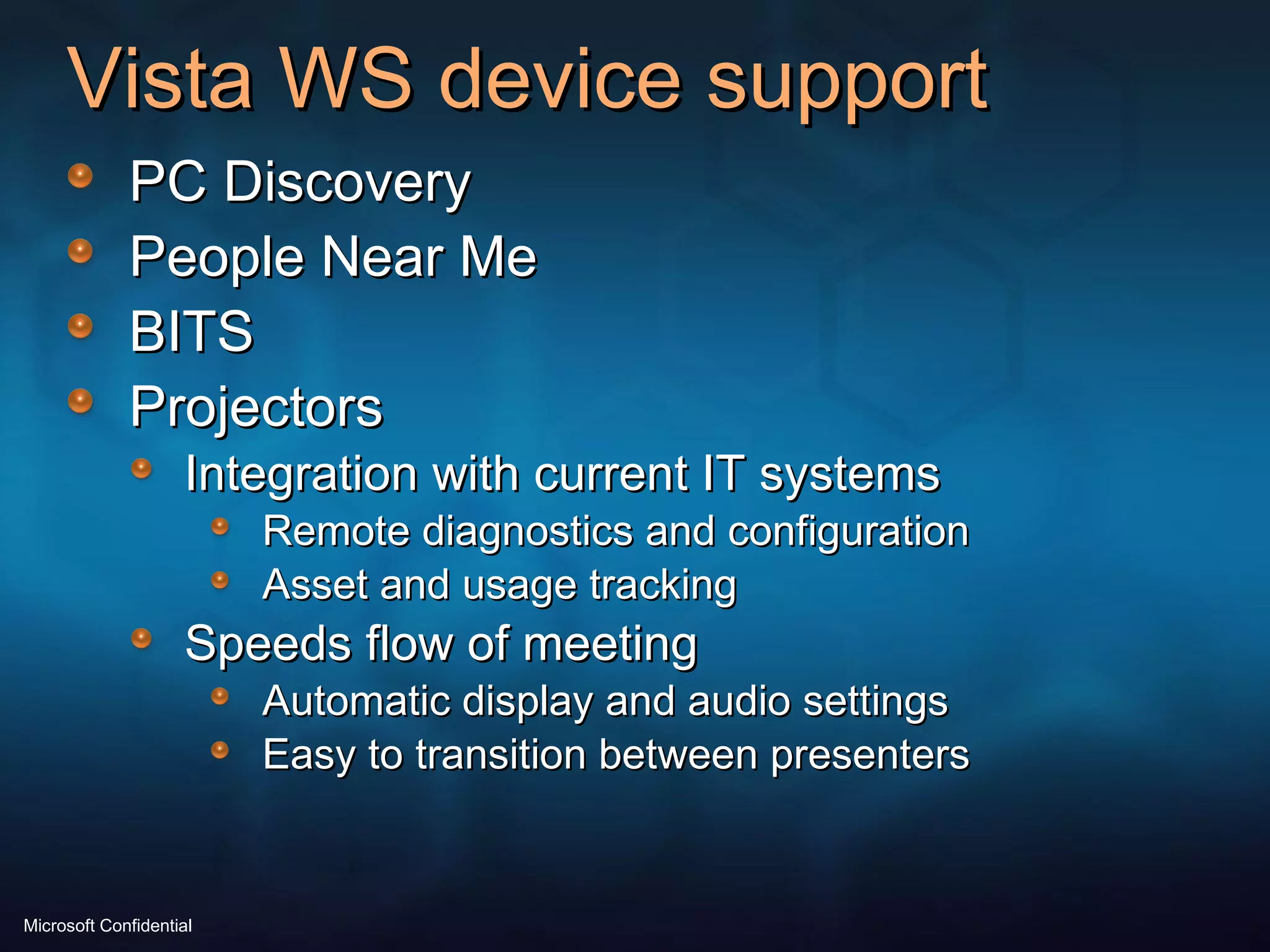
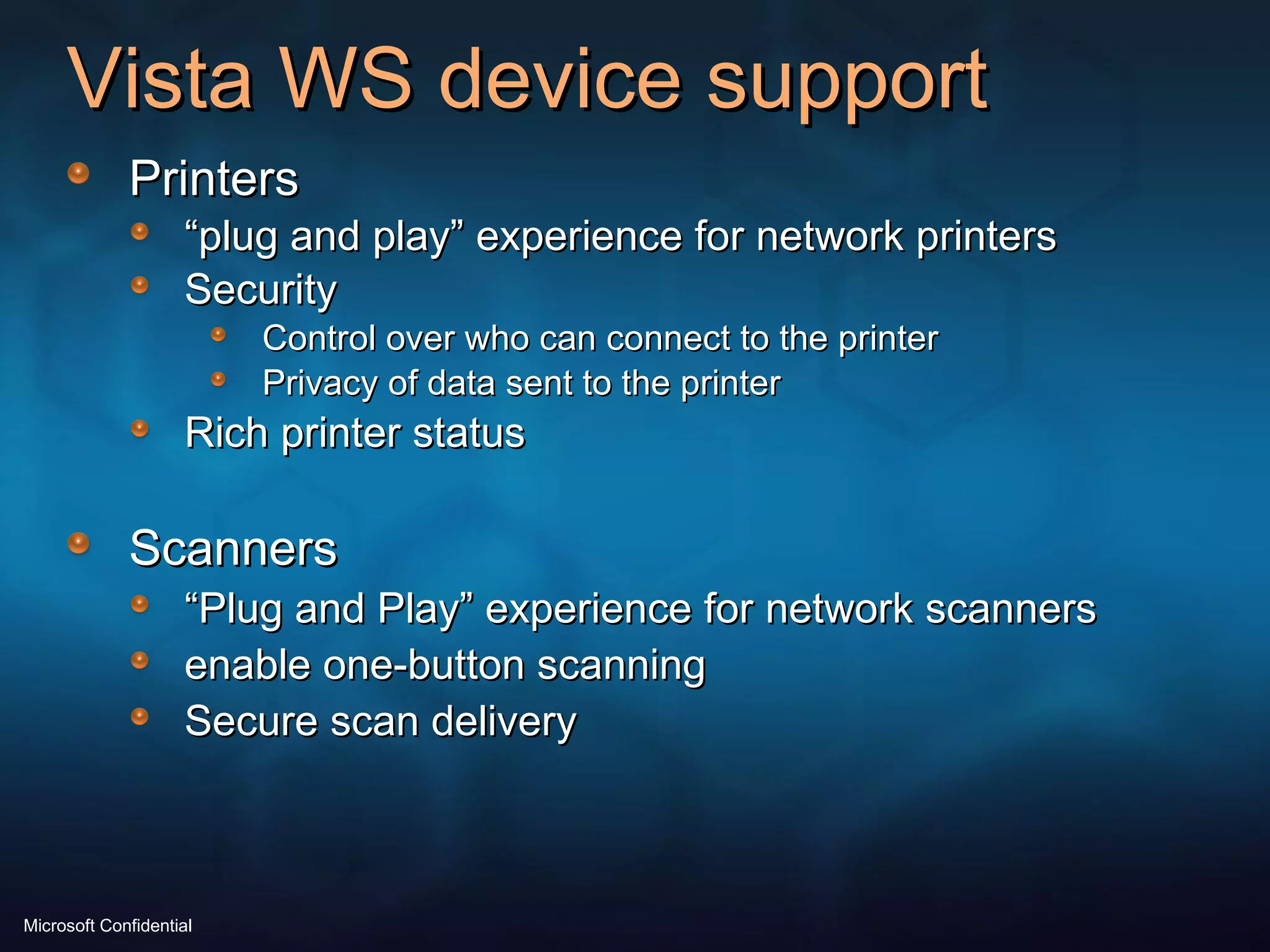
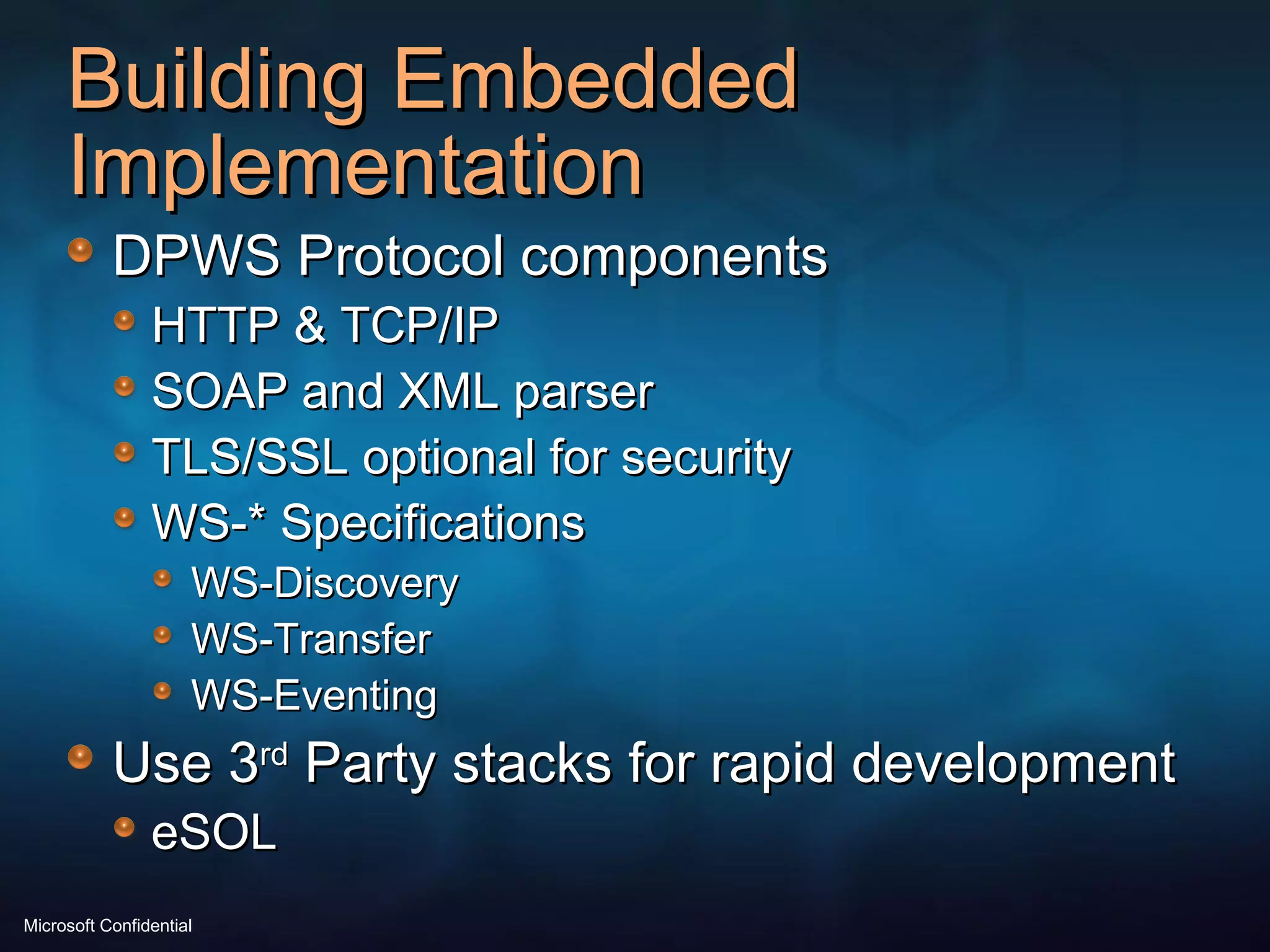
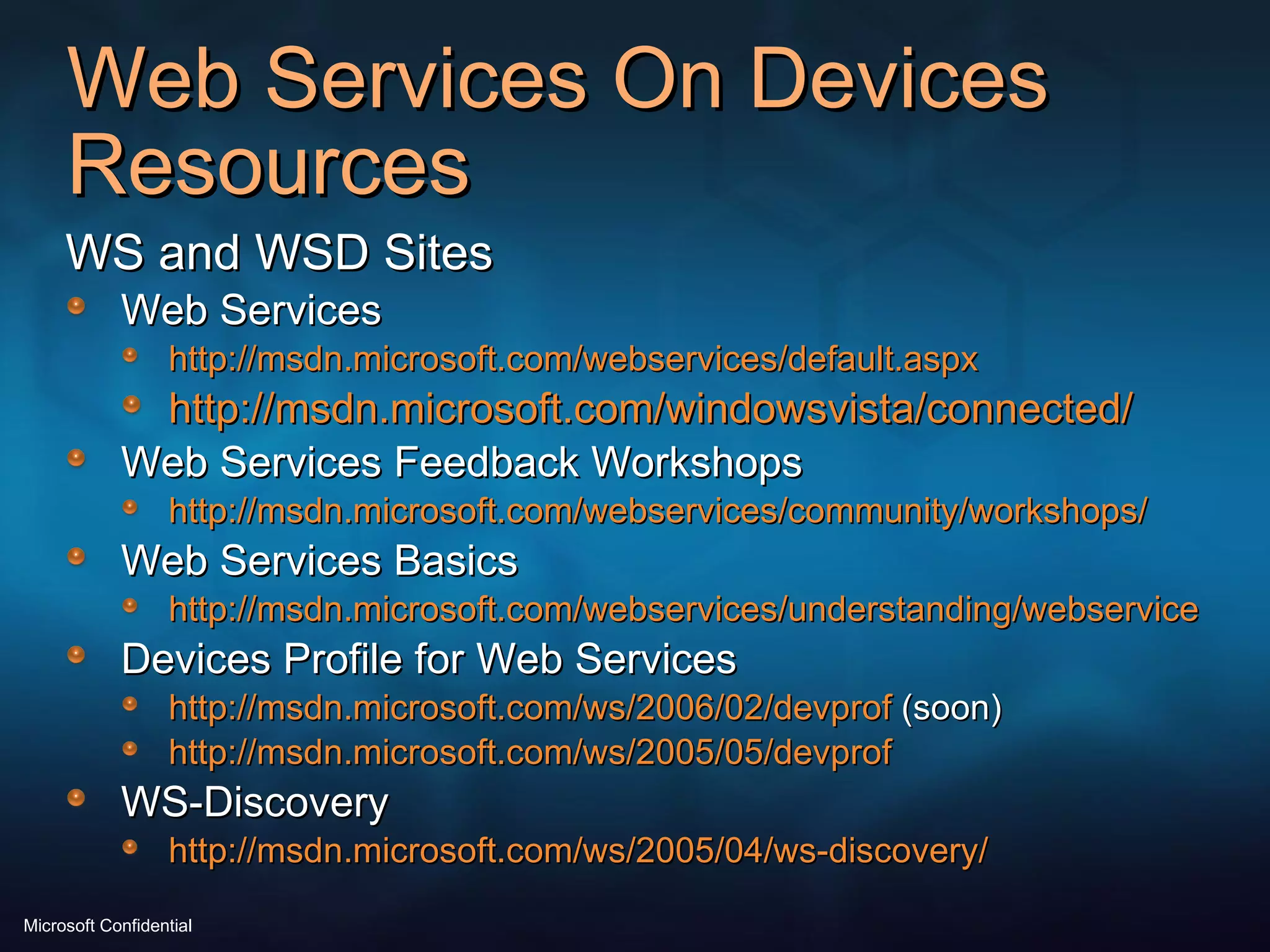
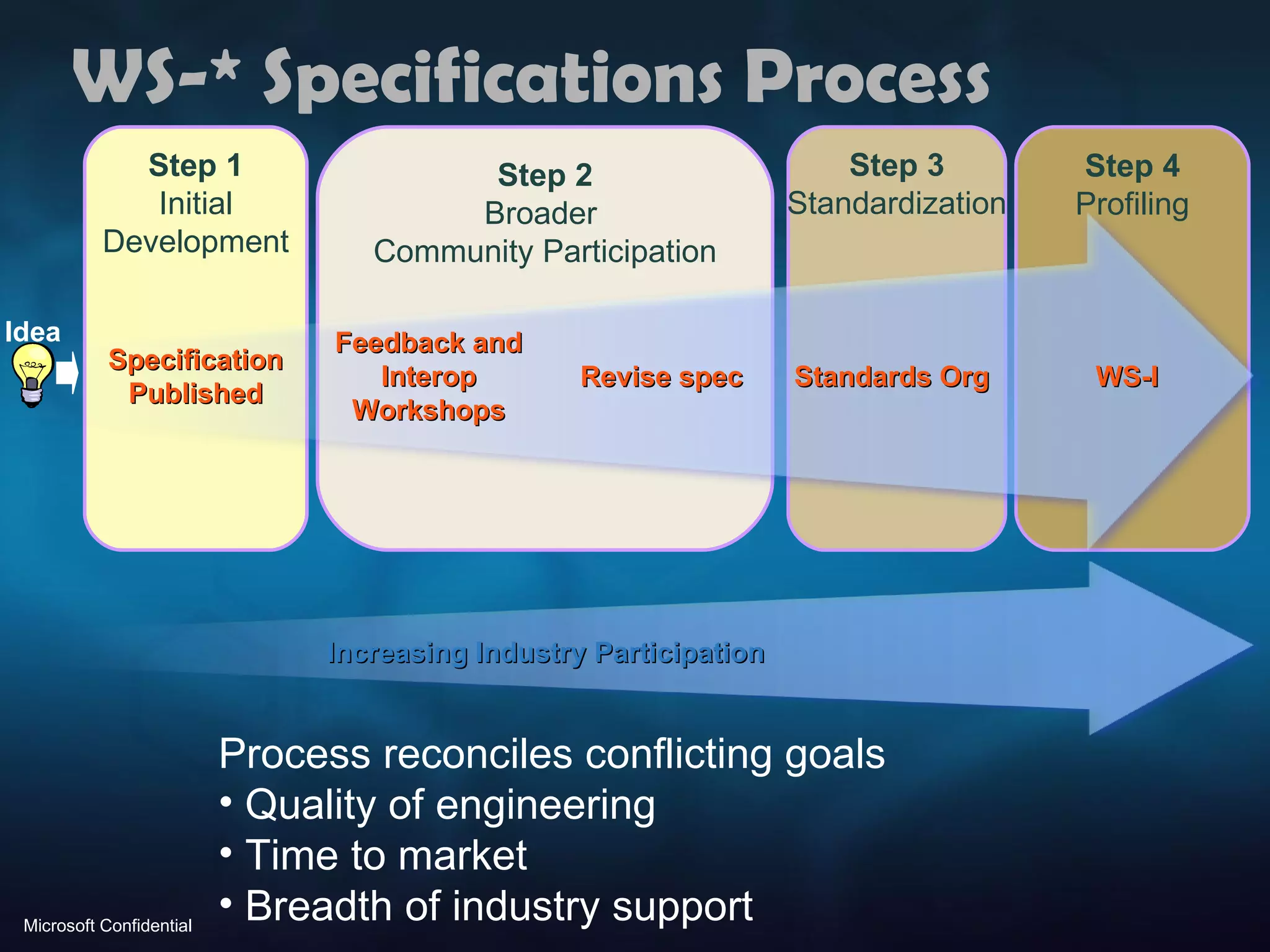
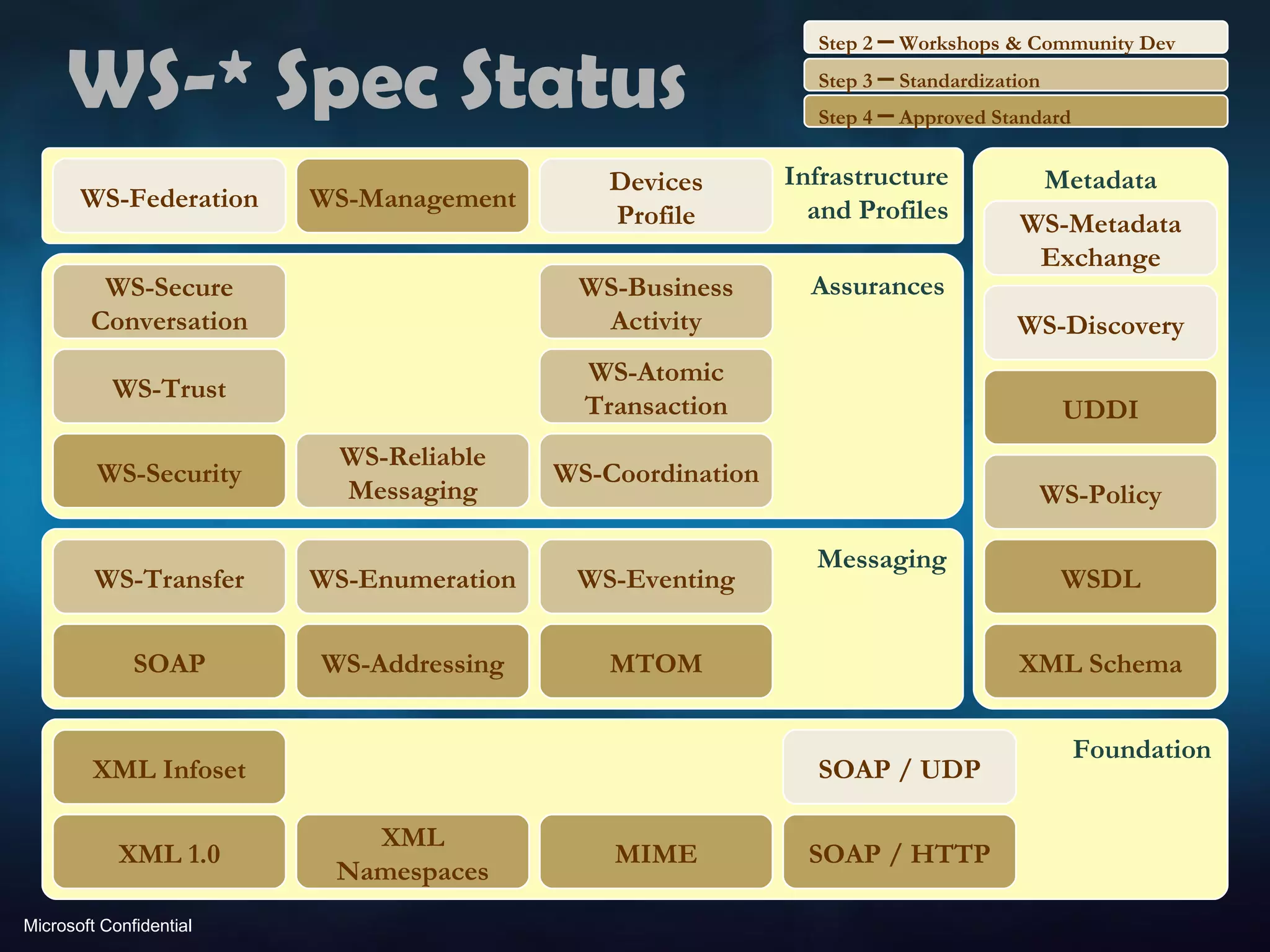
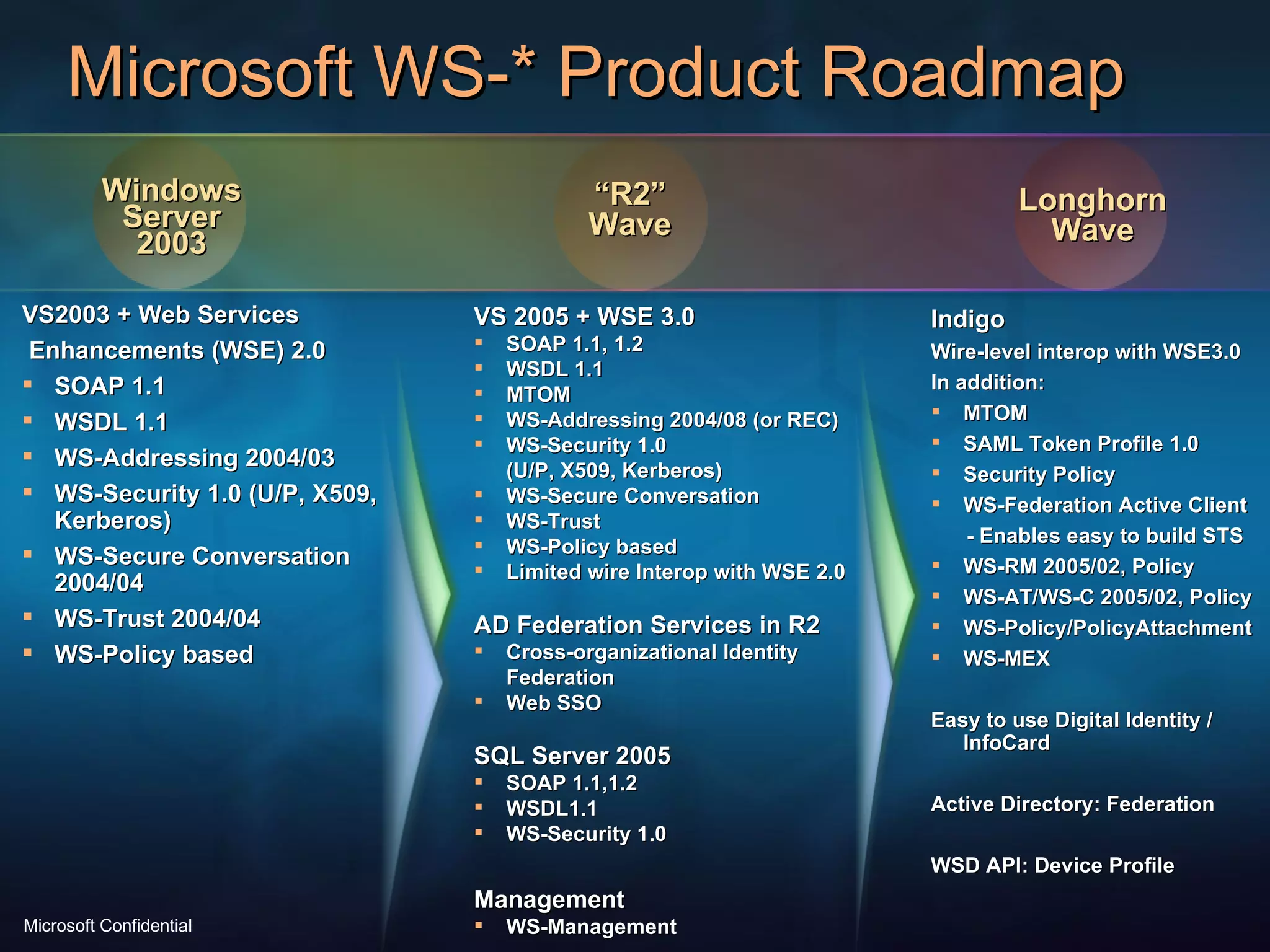
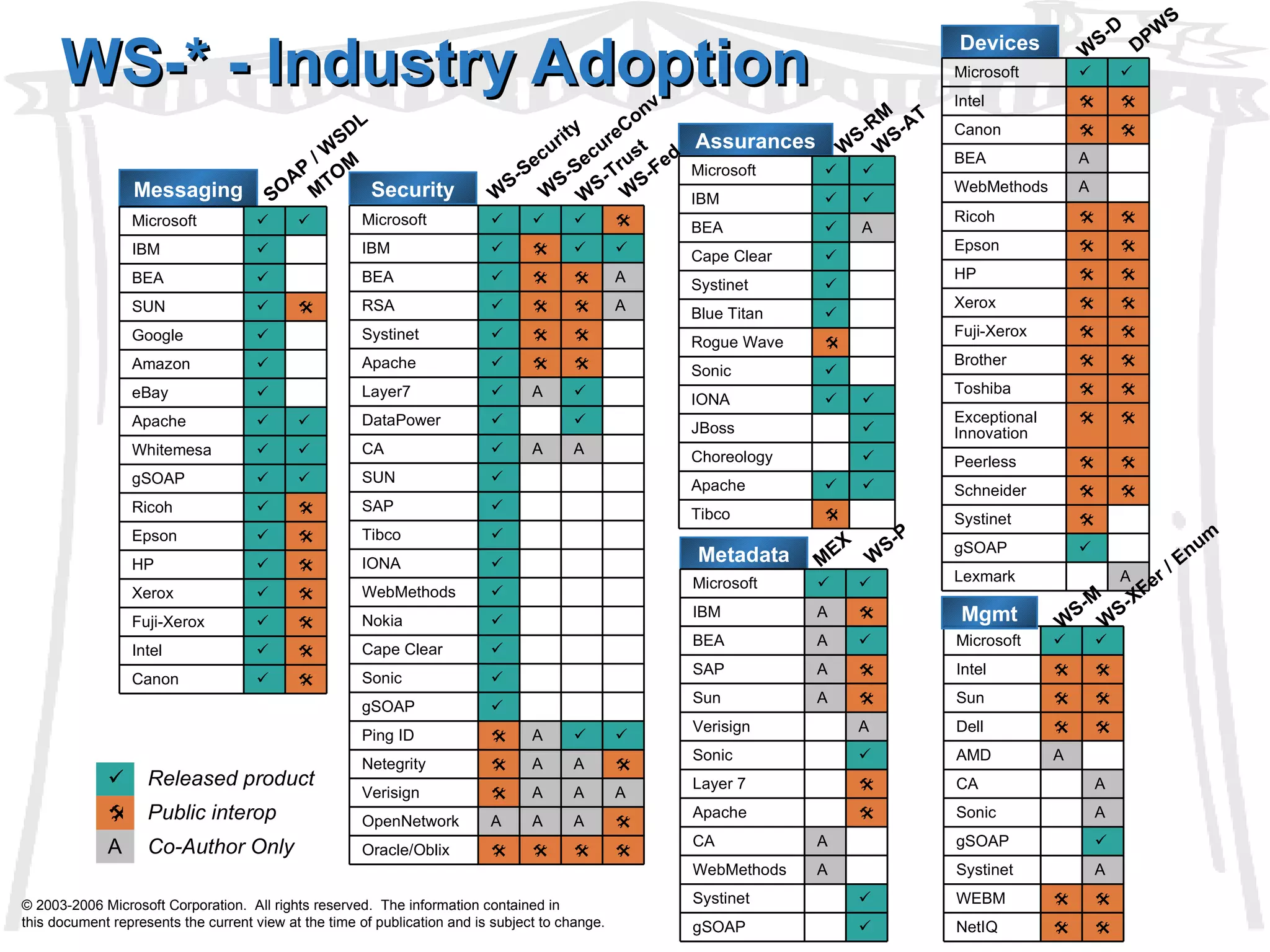
The document discusses Web Services and how they can be applied to devices using the Device Profile for Web Services. It describes how WS specifications can be scaled down to work on limited resource devices. The Device Profile defines a lightweight subset of WS specs for device communication and includes security, discovery, and other protocols. Microsoft's implementations in Windows Vista and .NET support these standards for printer, scanner, and other device integration.
![Web Services and the Devices Profile Jorgen Thelin Program Manager Connected Systems Division [email_address]](https://image.slidesharecdn.com/webservicesdpws-1227918649862523-9/75/Web-Services-and-Devices-Profile-for-Web-Services-DPWS-1-2048.jpg)