Embed presentation

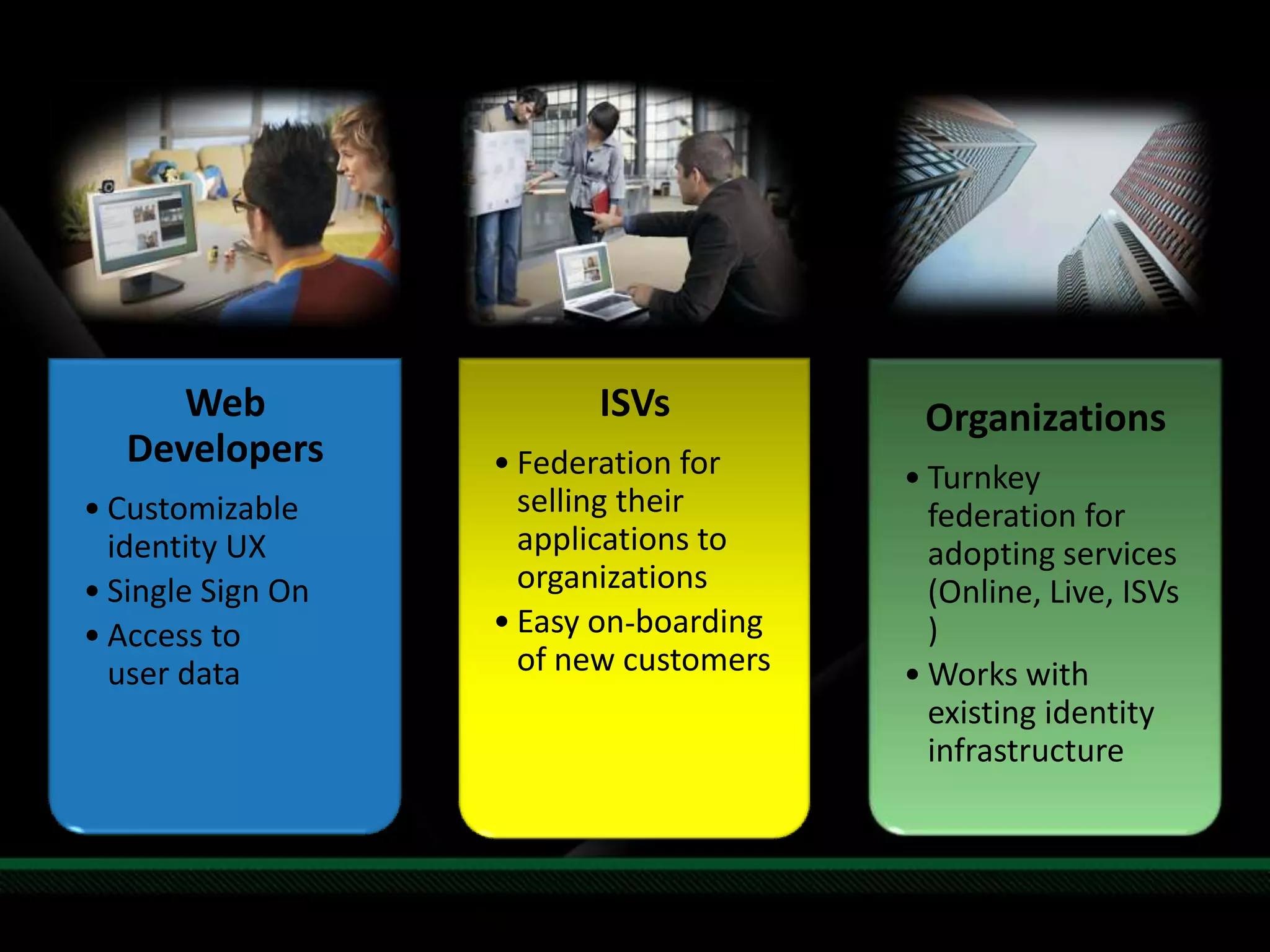
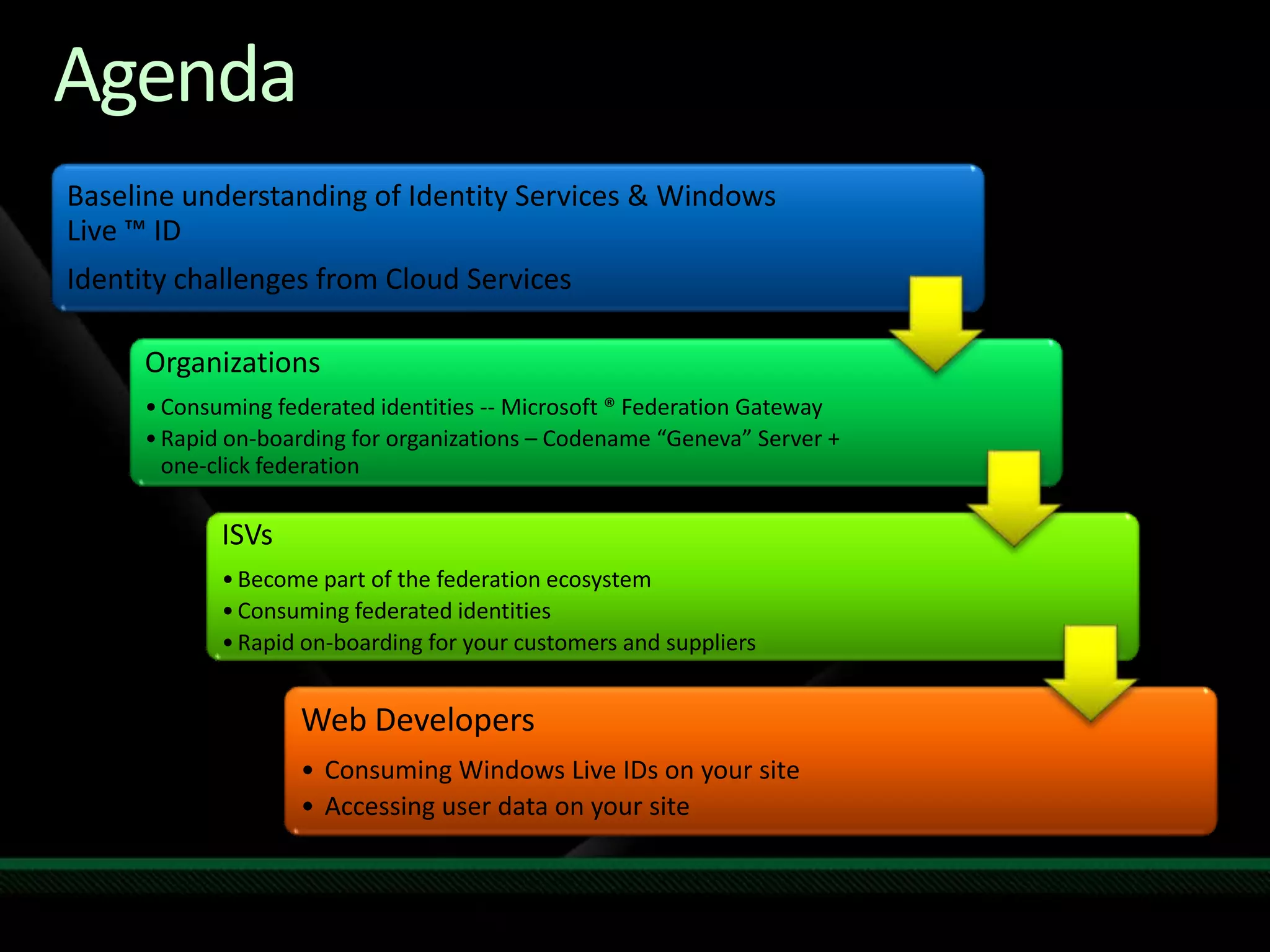
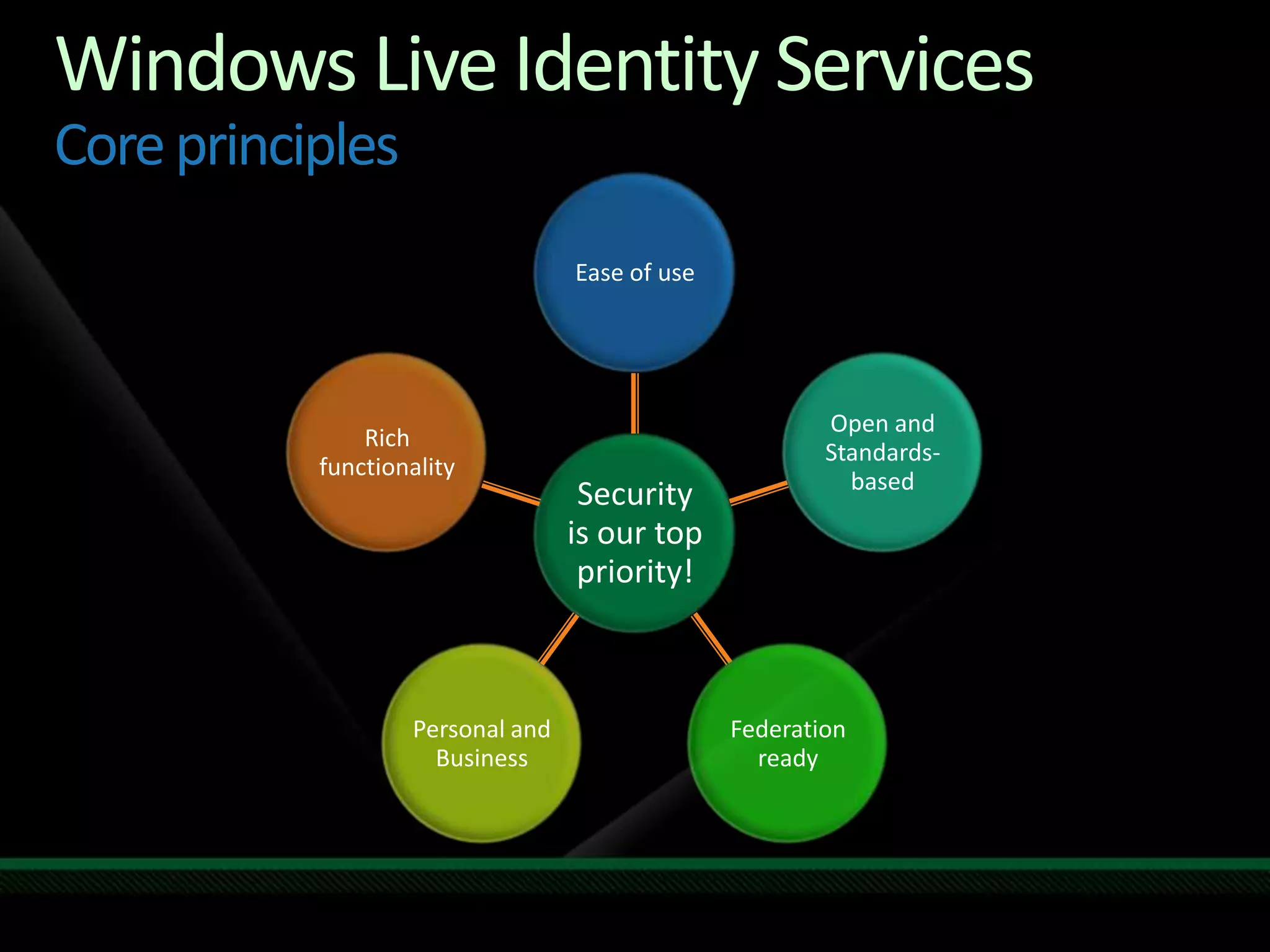
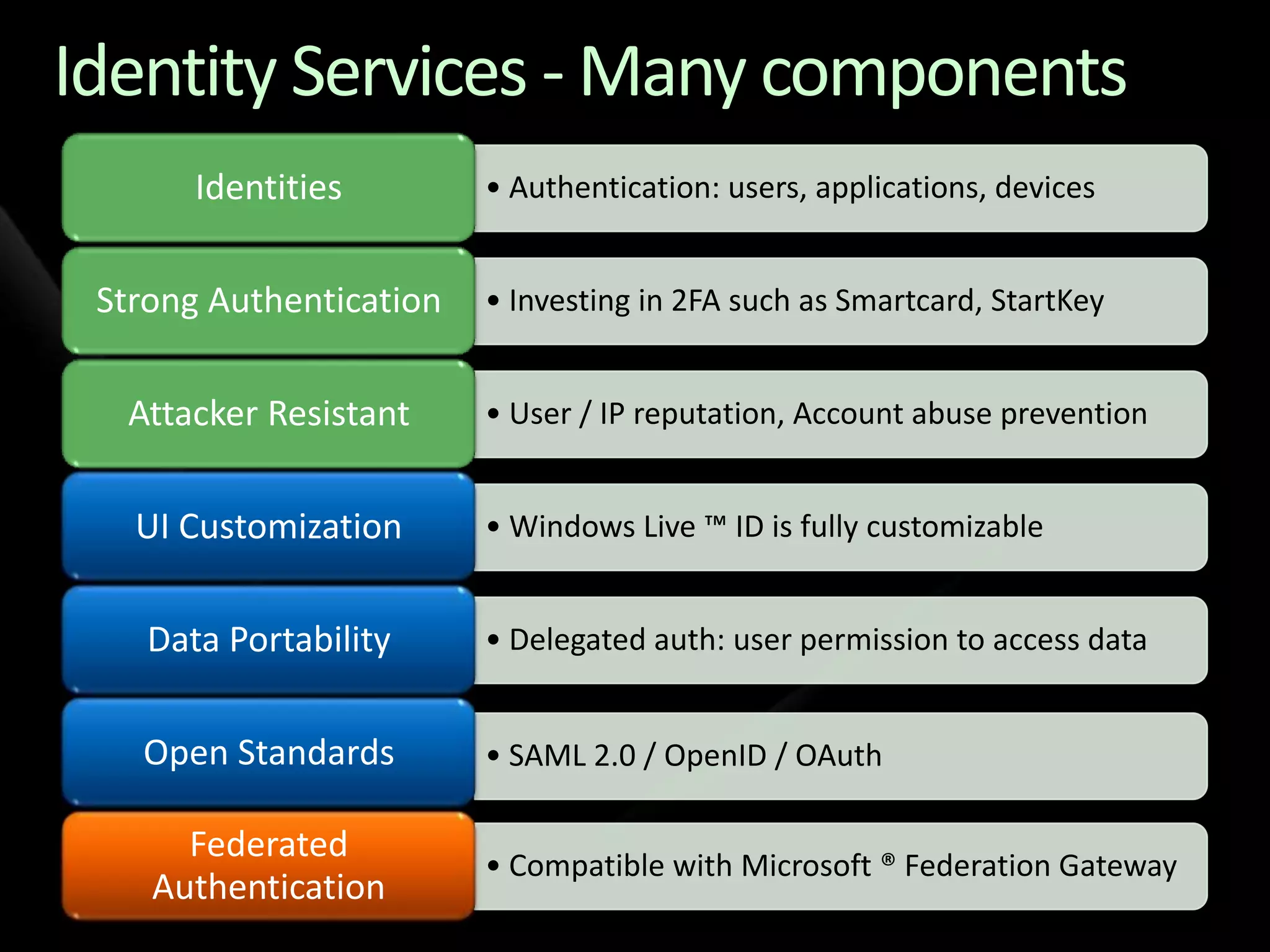

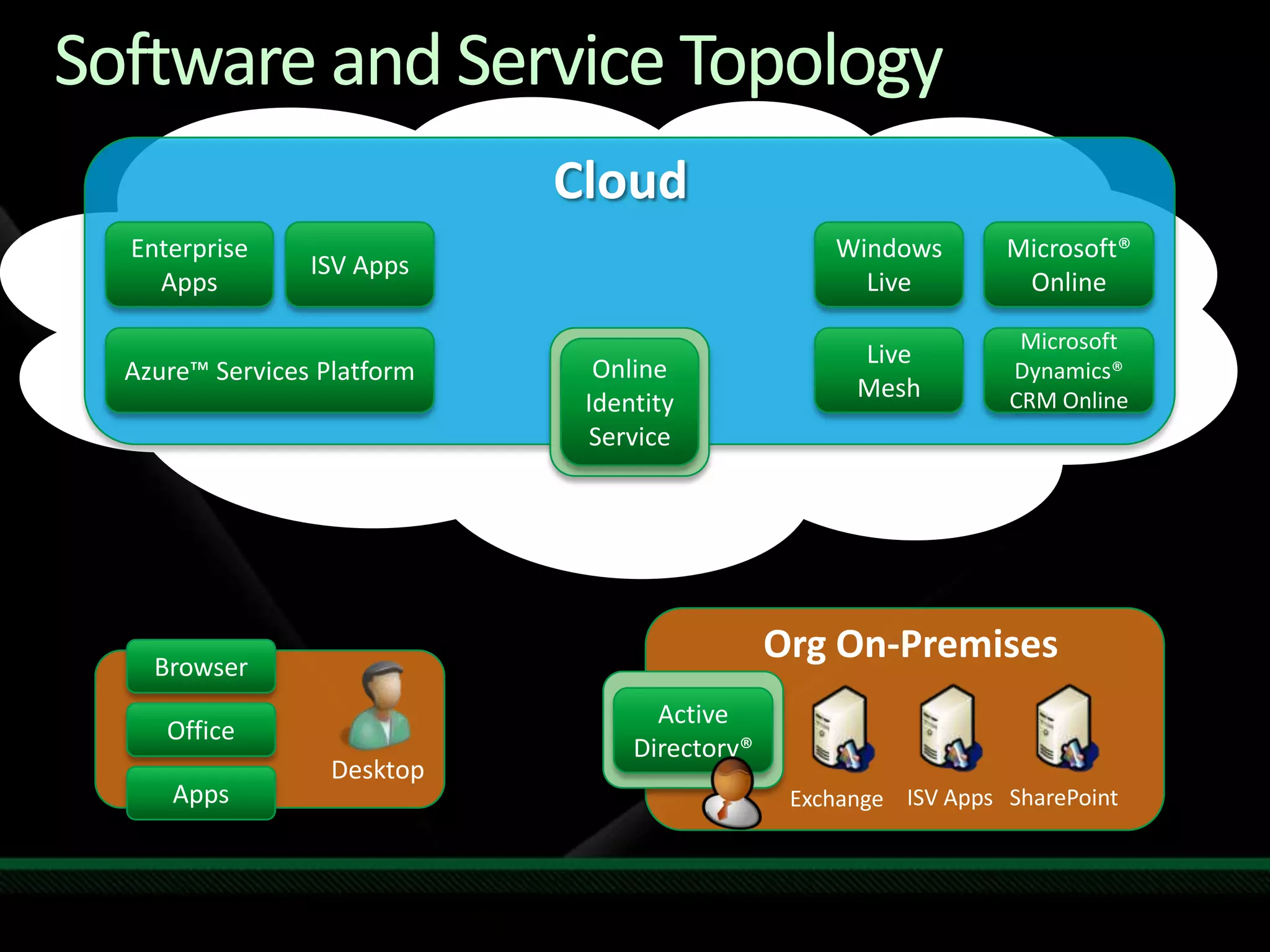
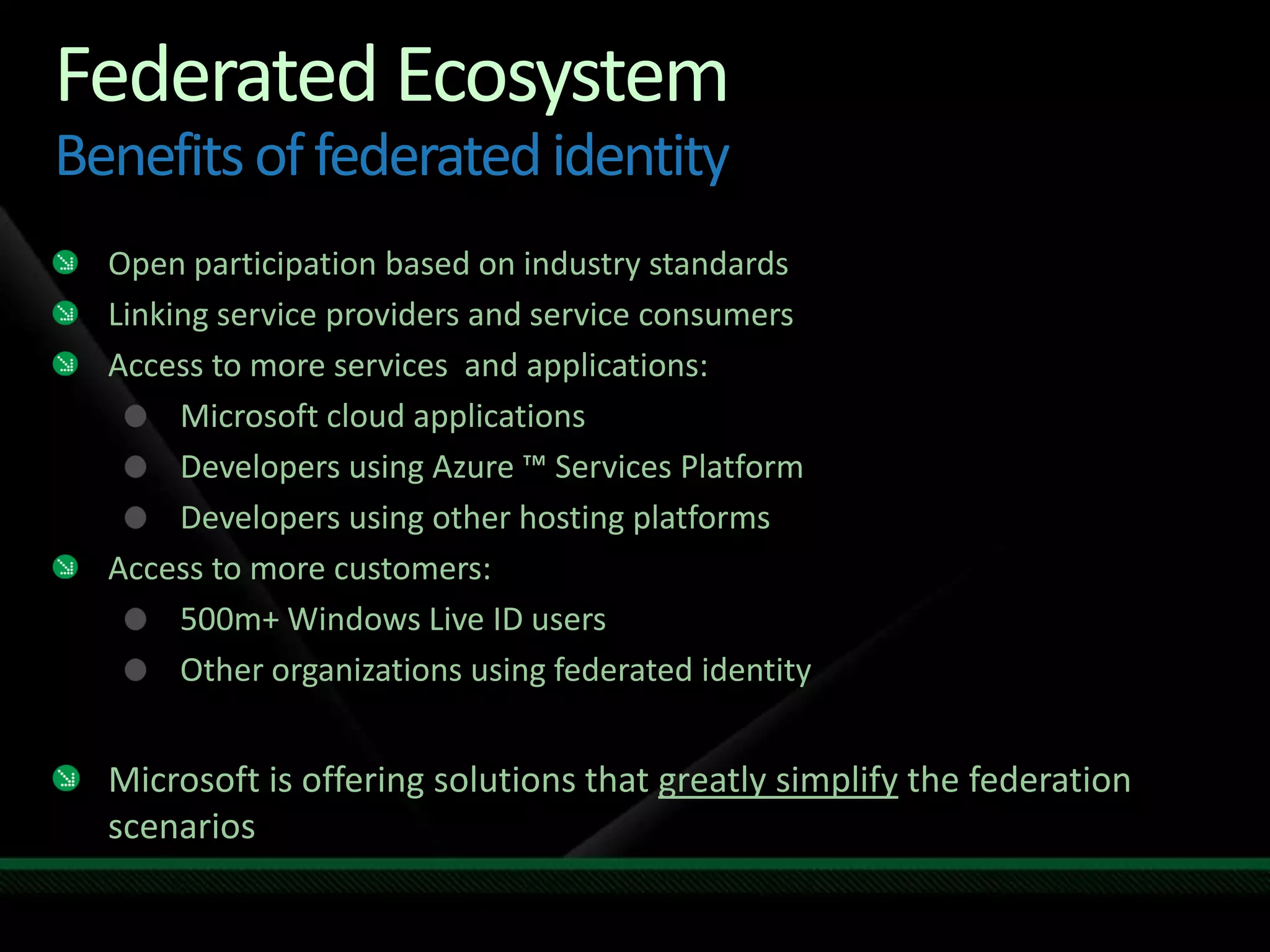
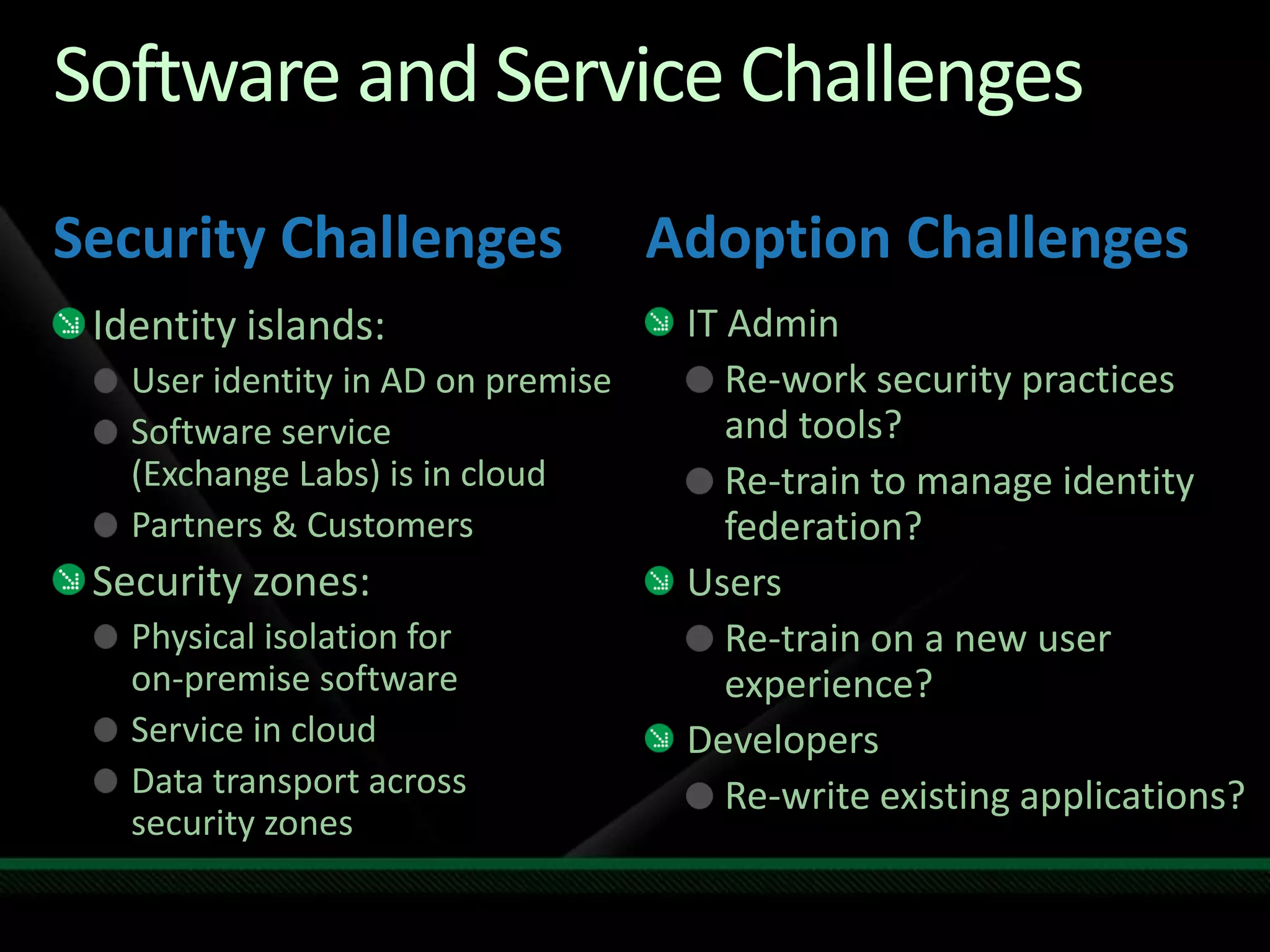
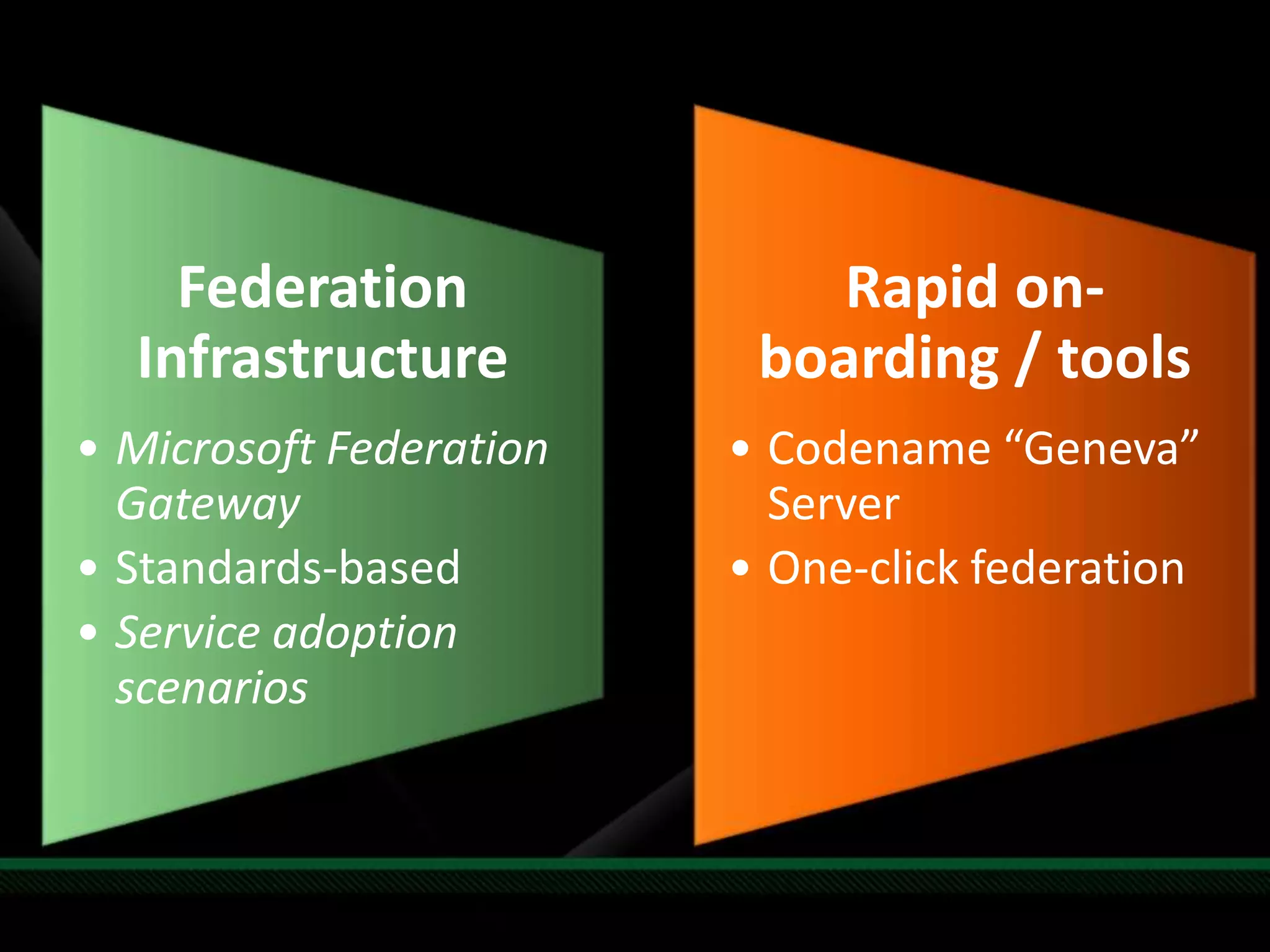
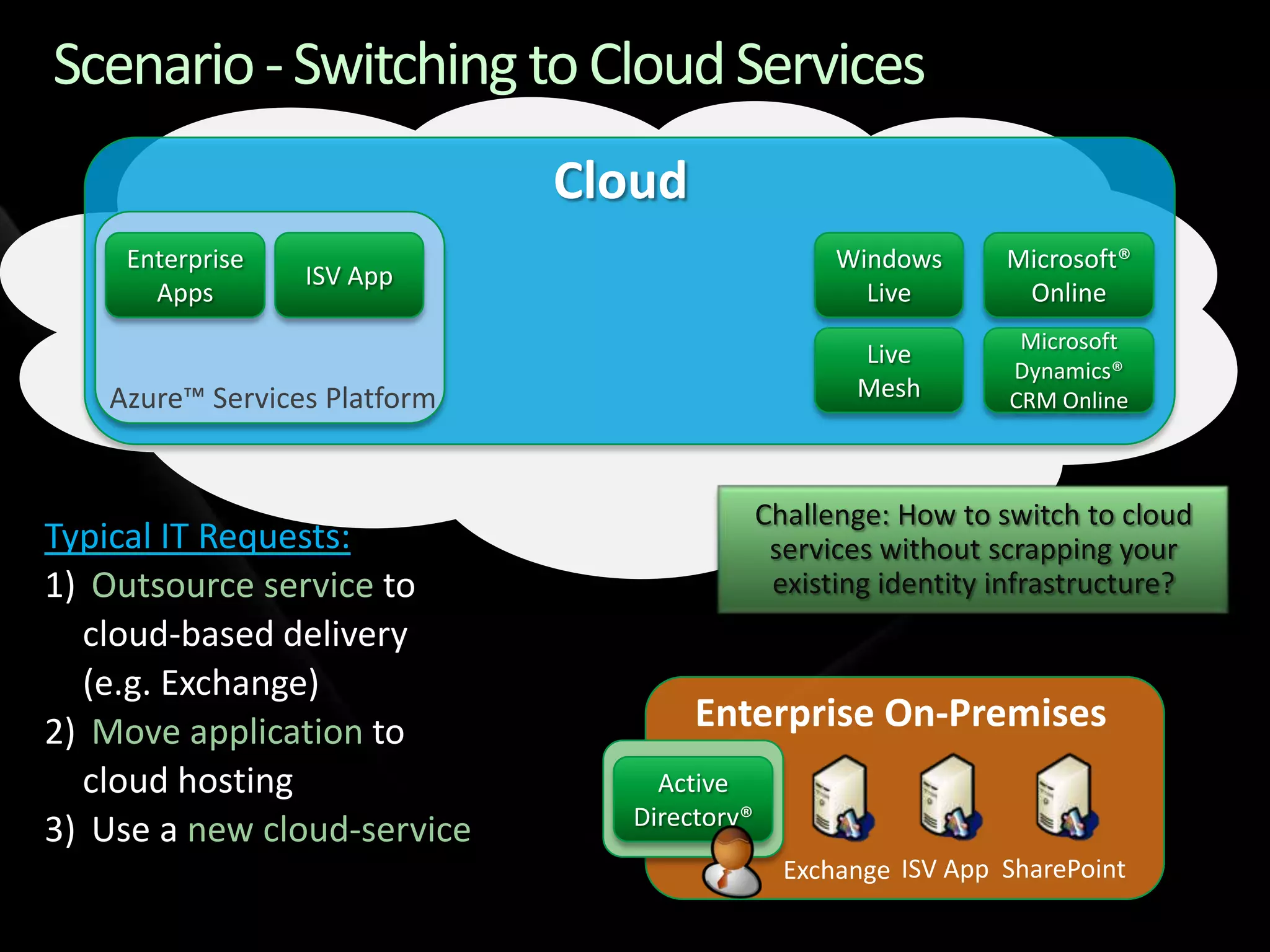
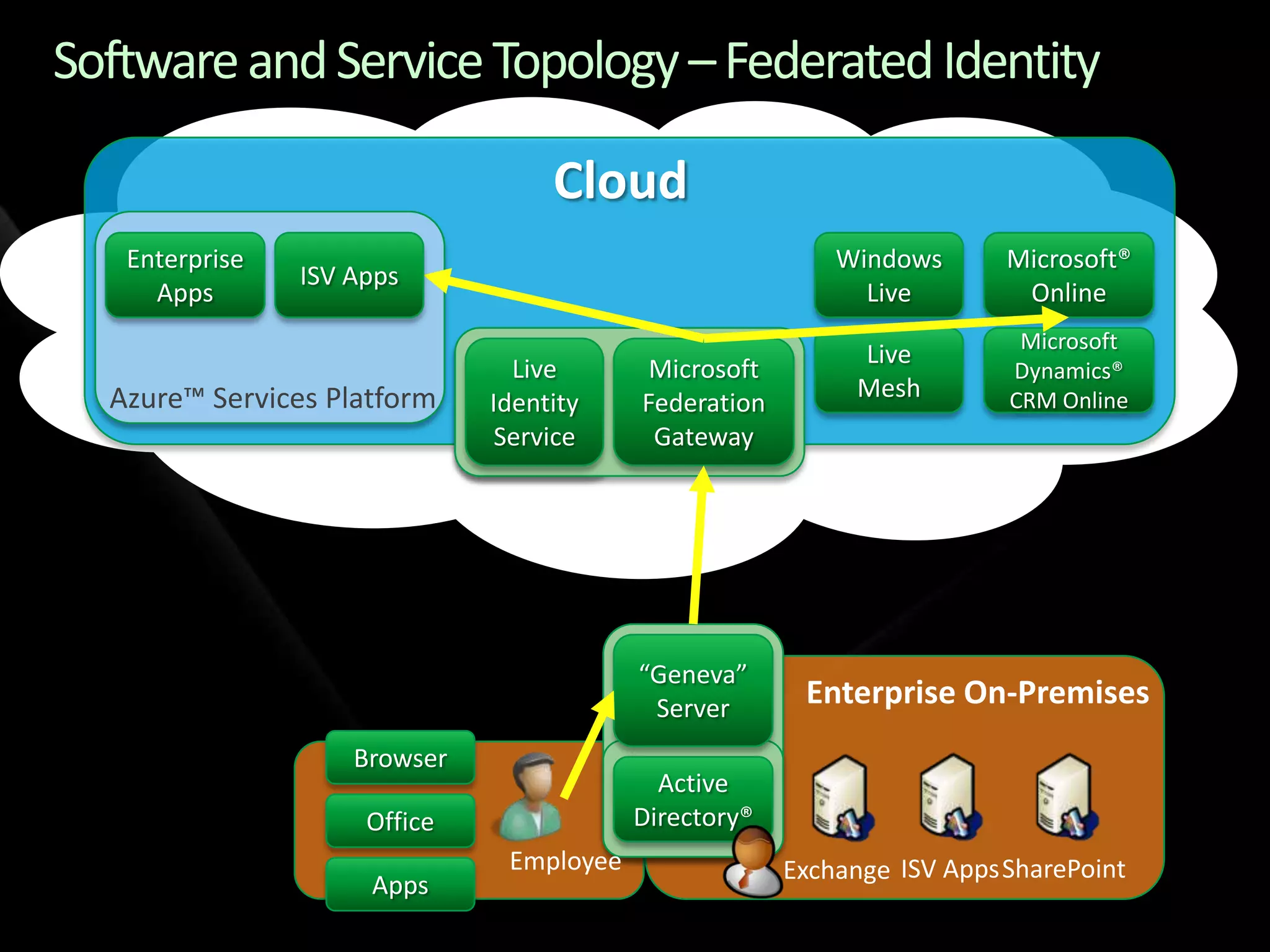
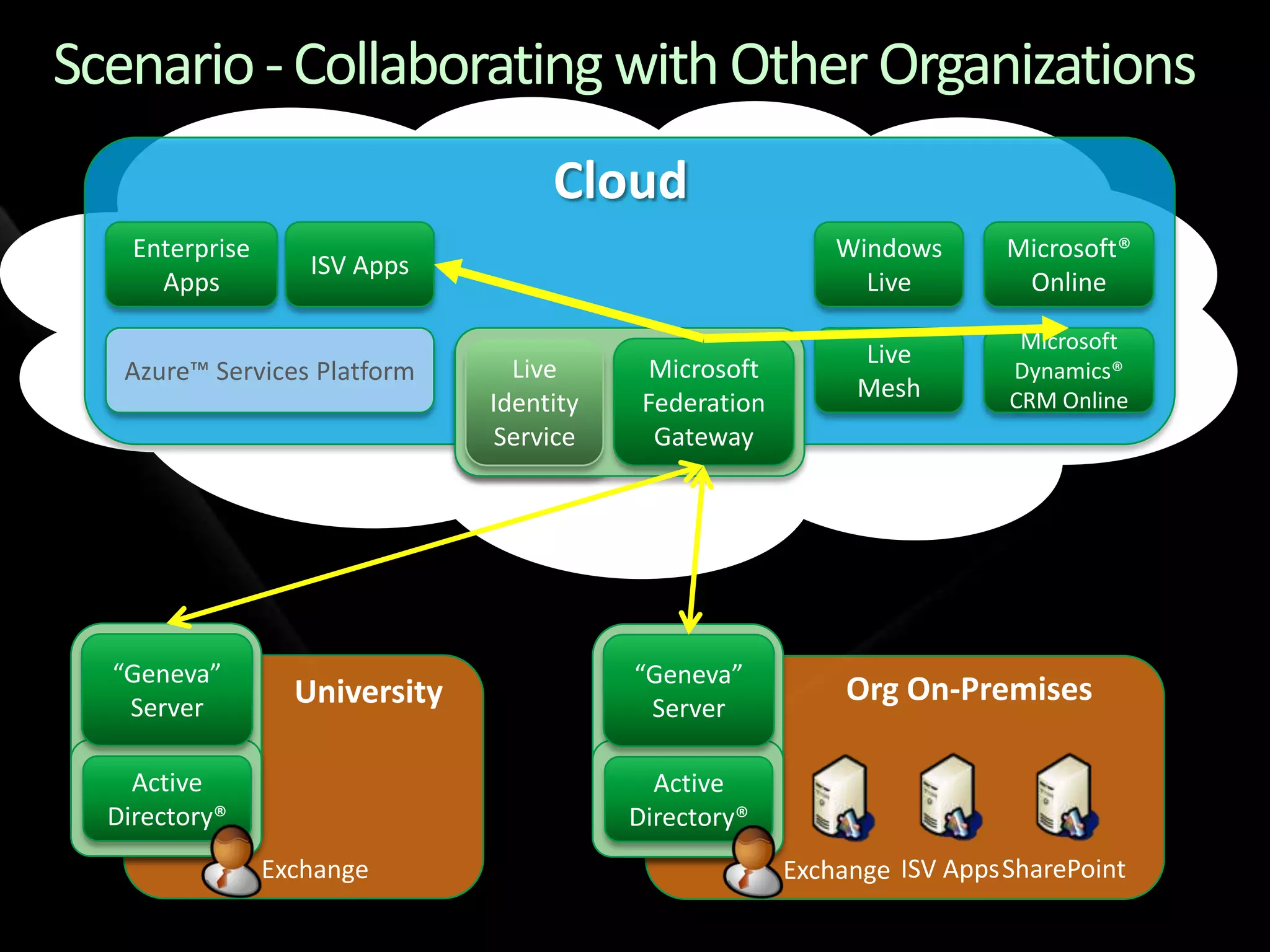
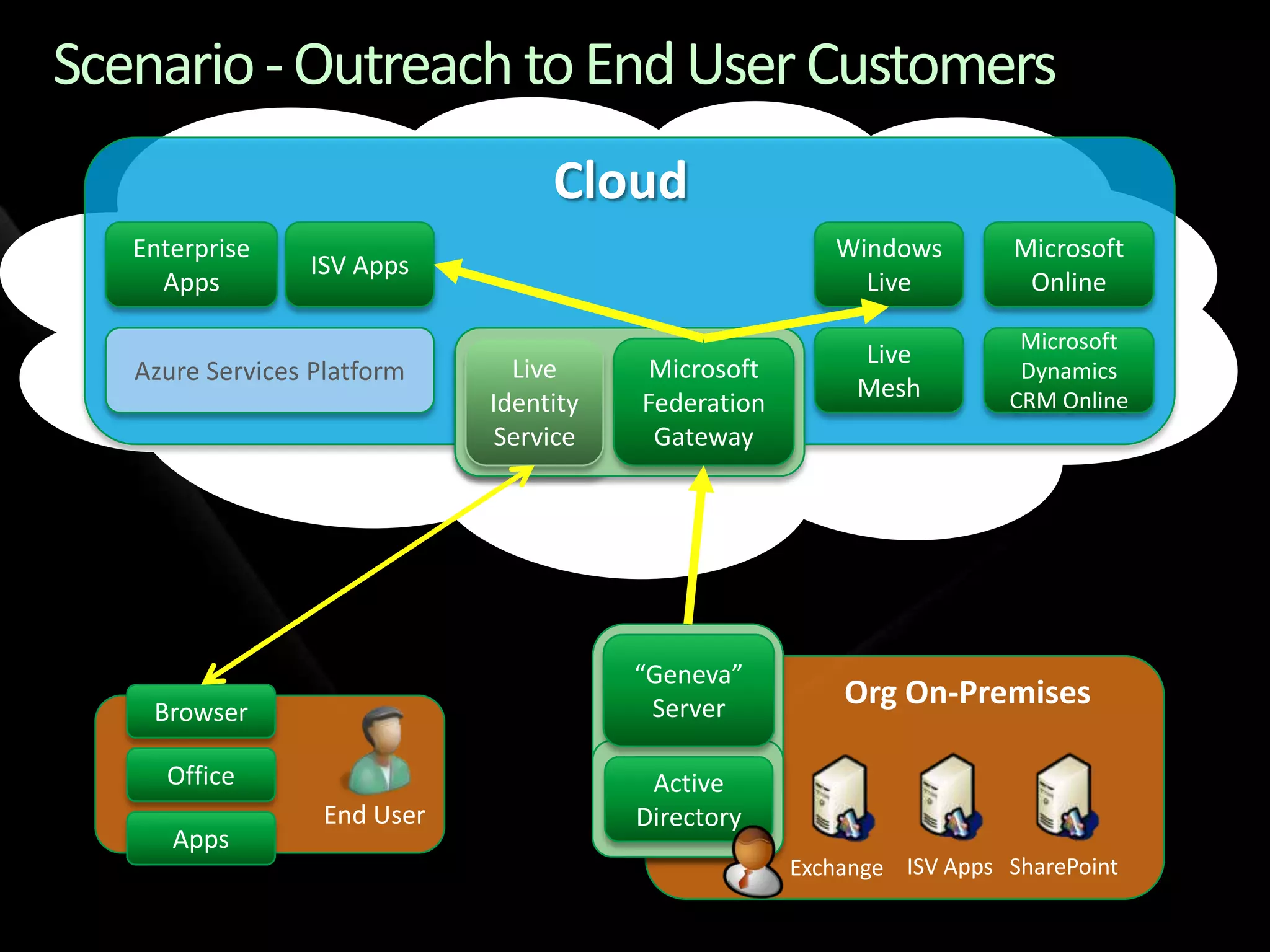
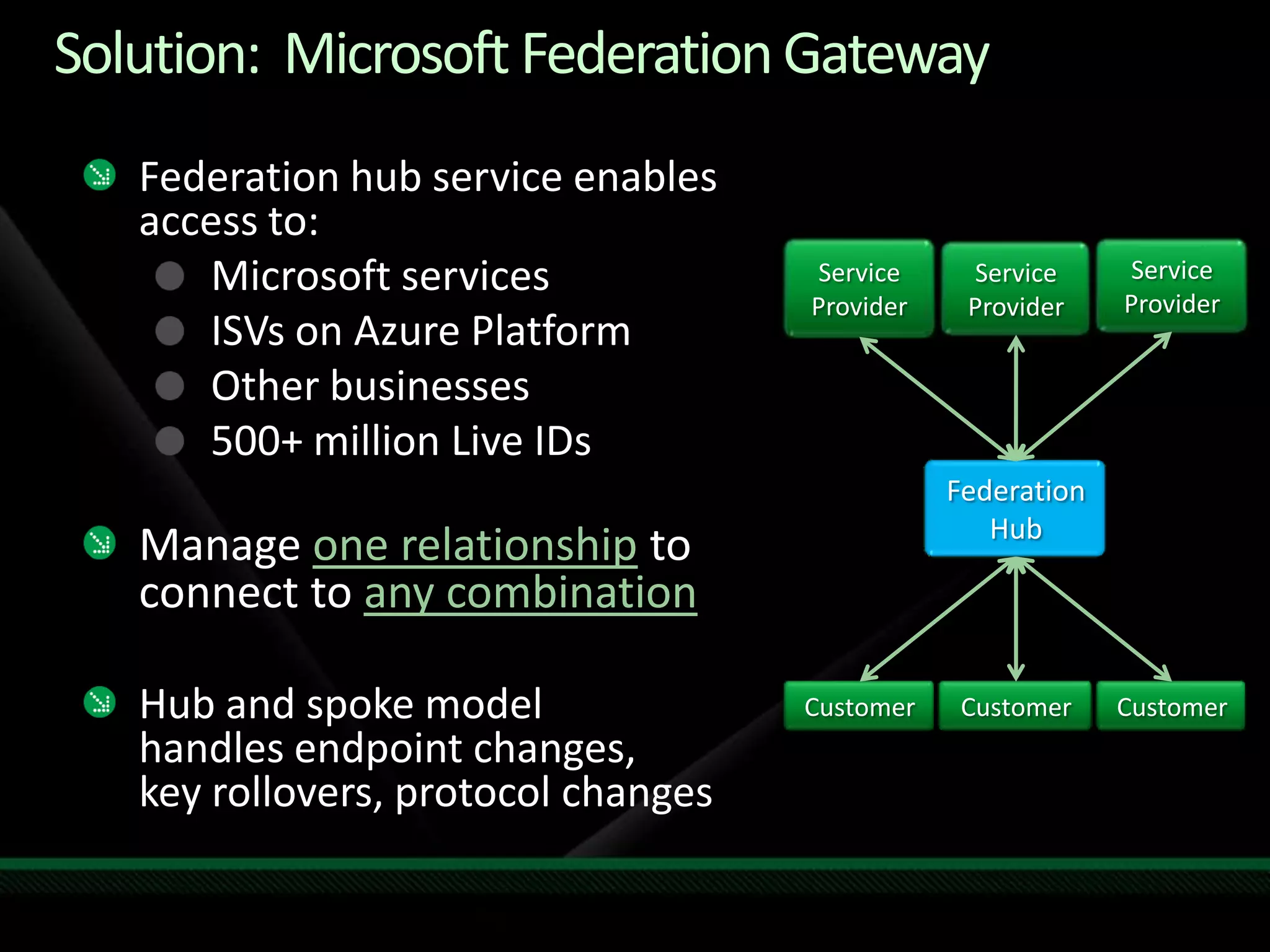
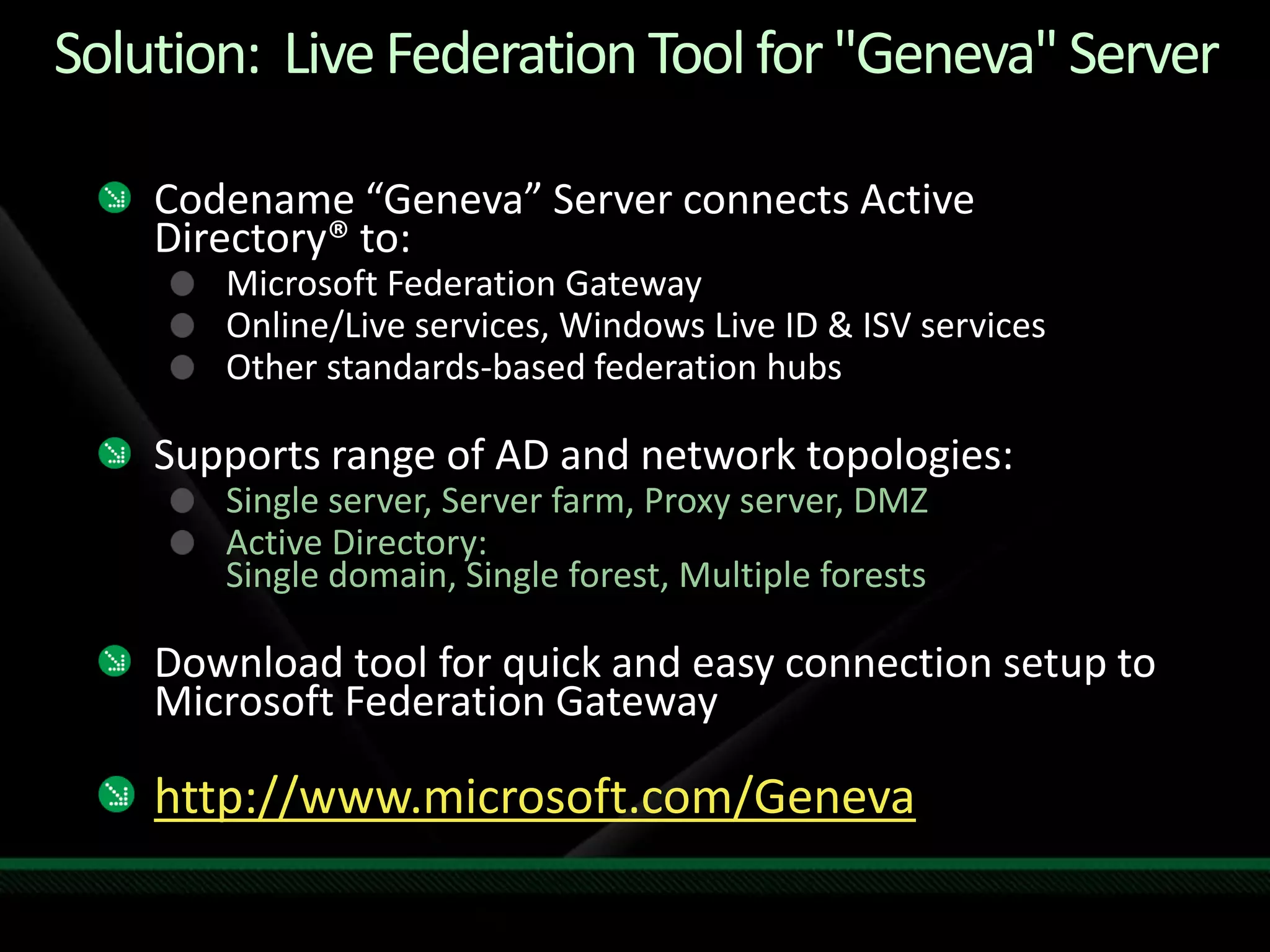

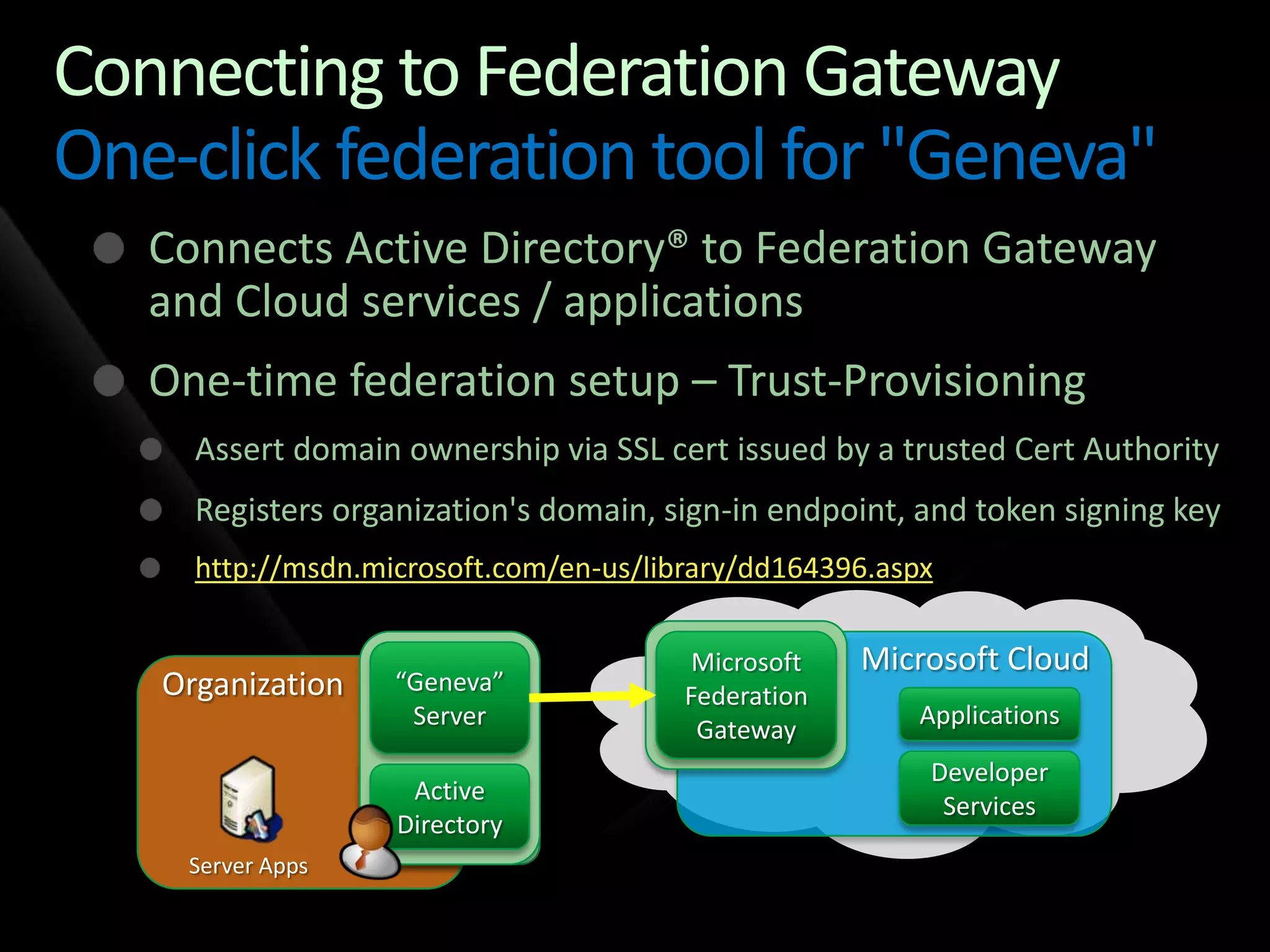
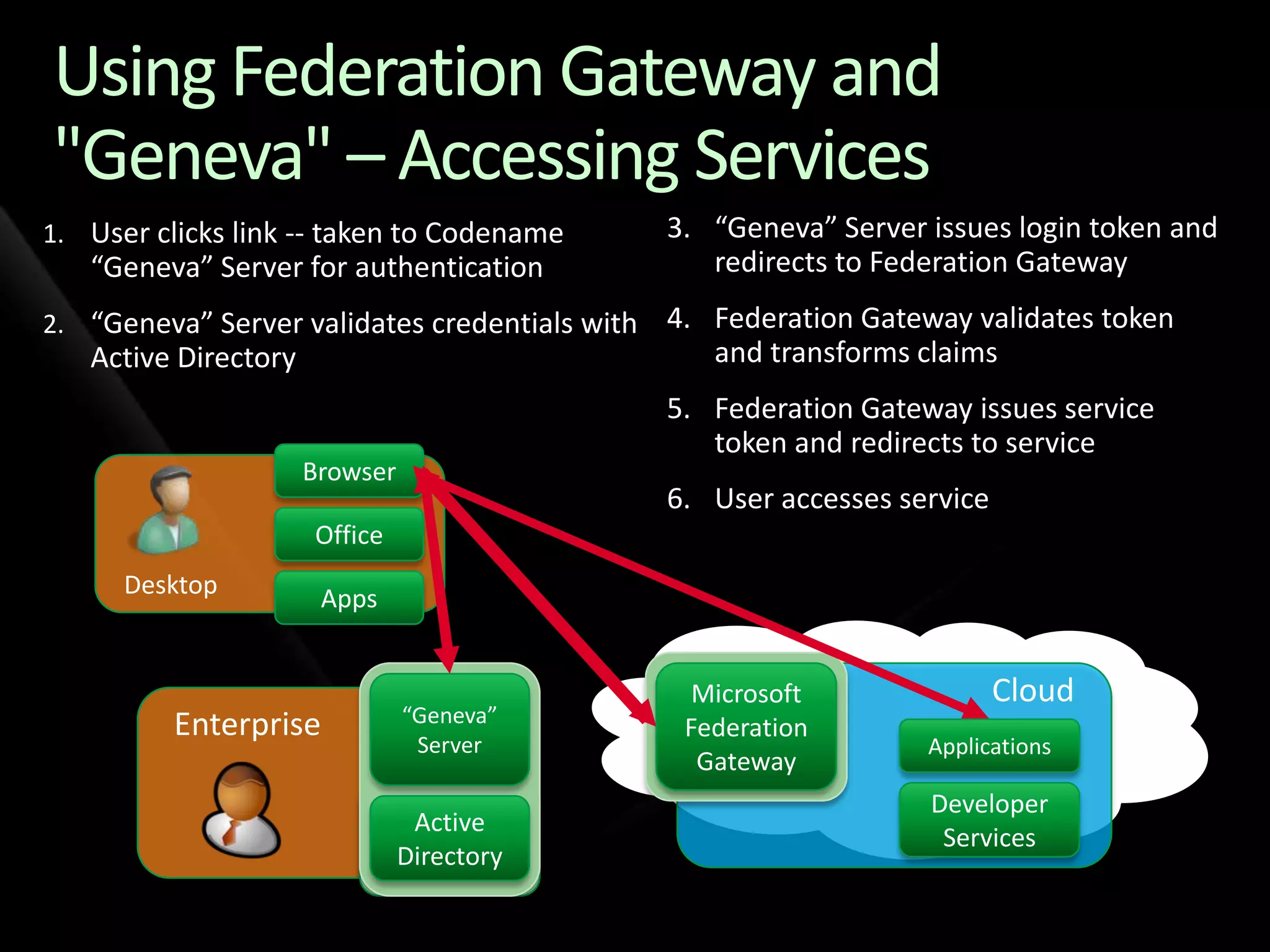
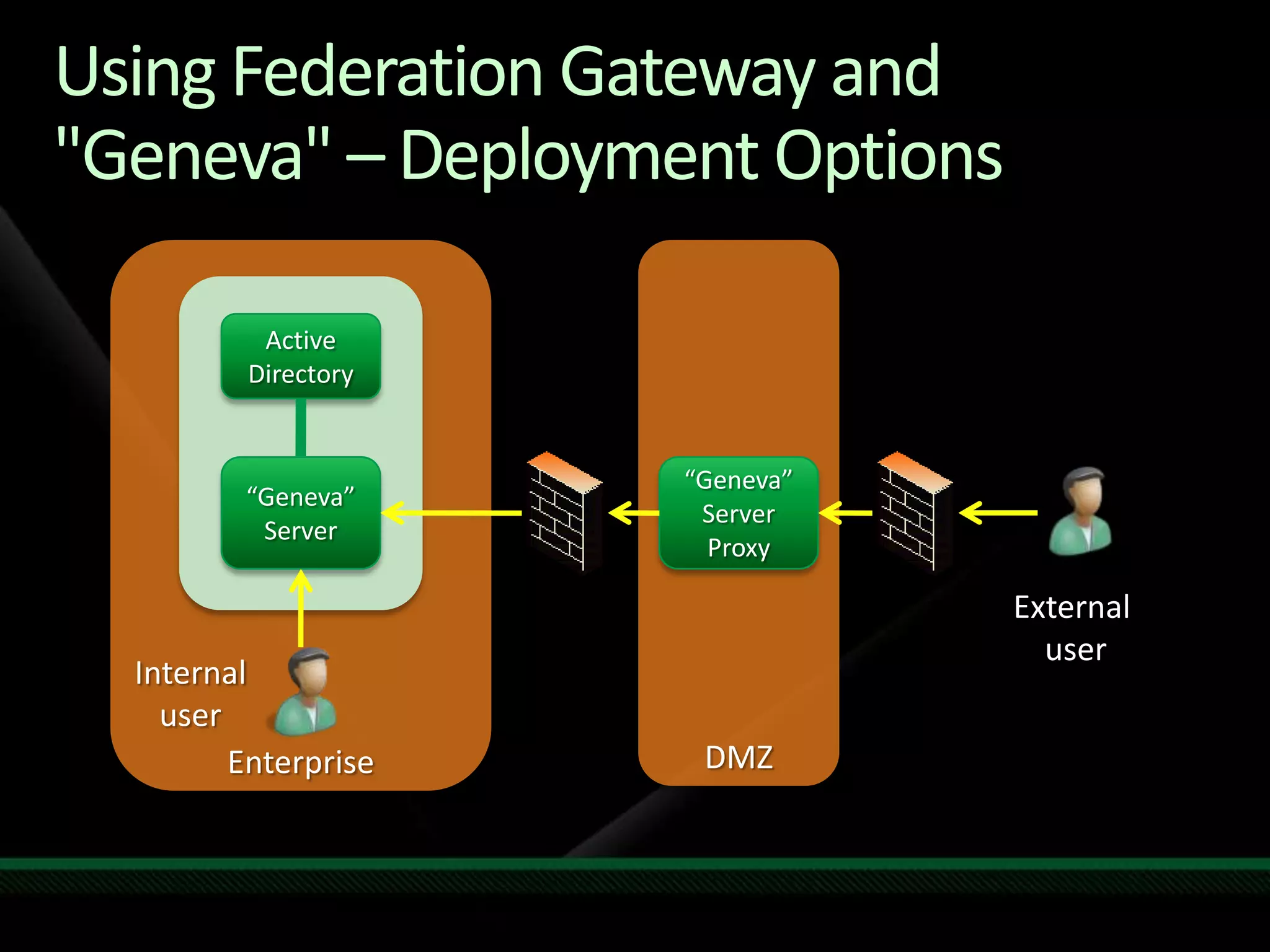

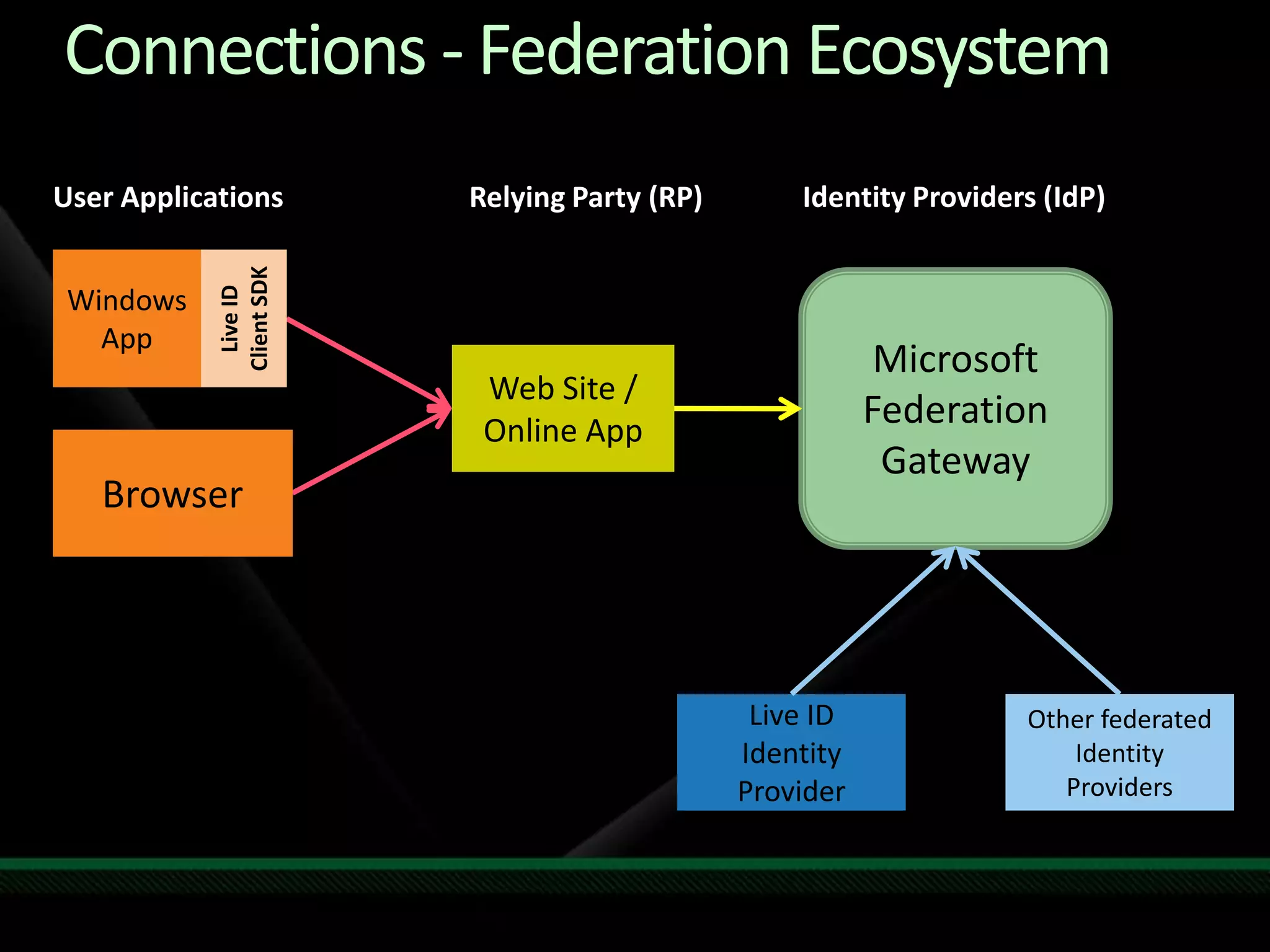
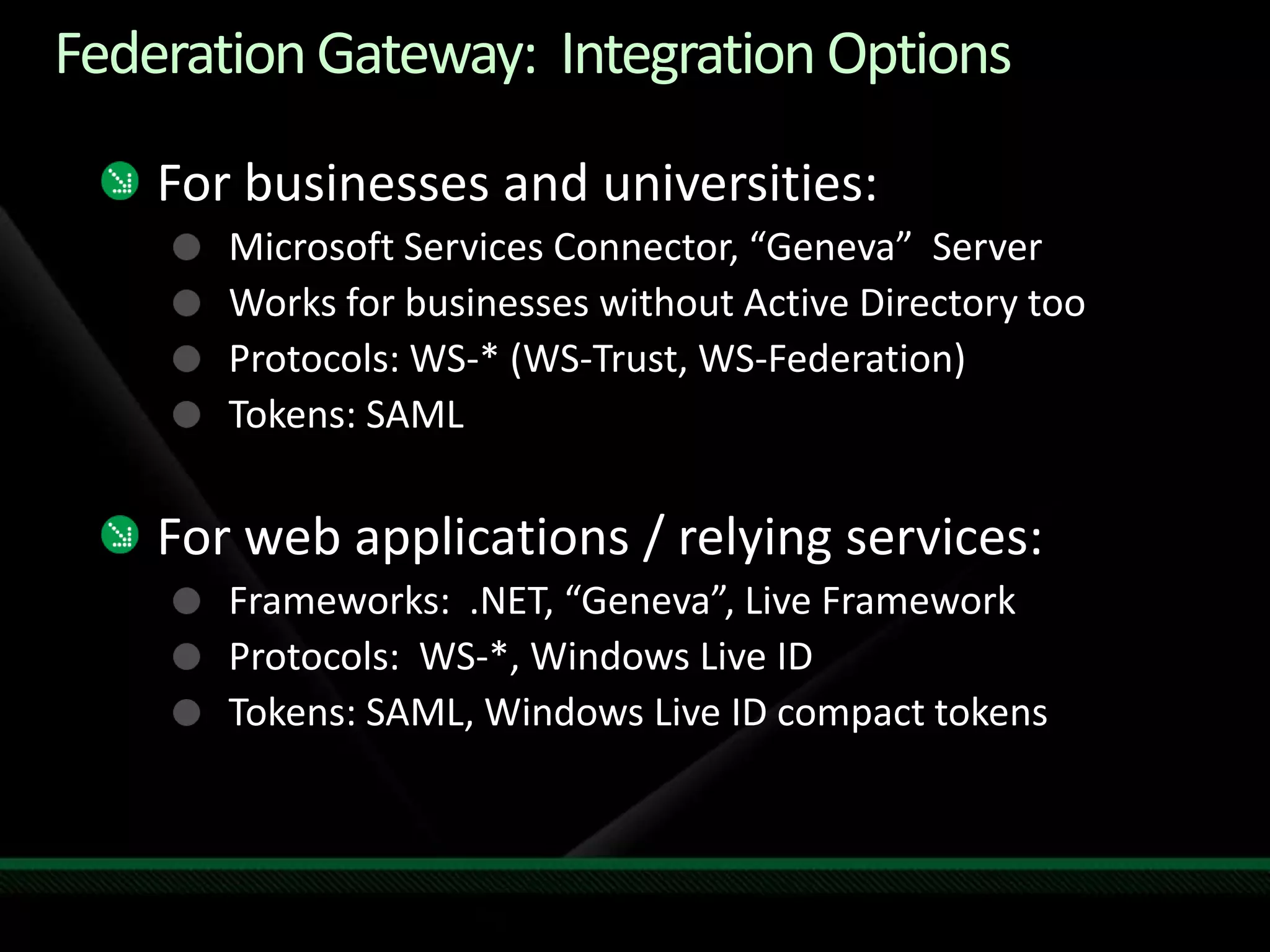

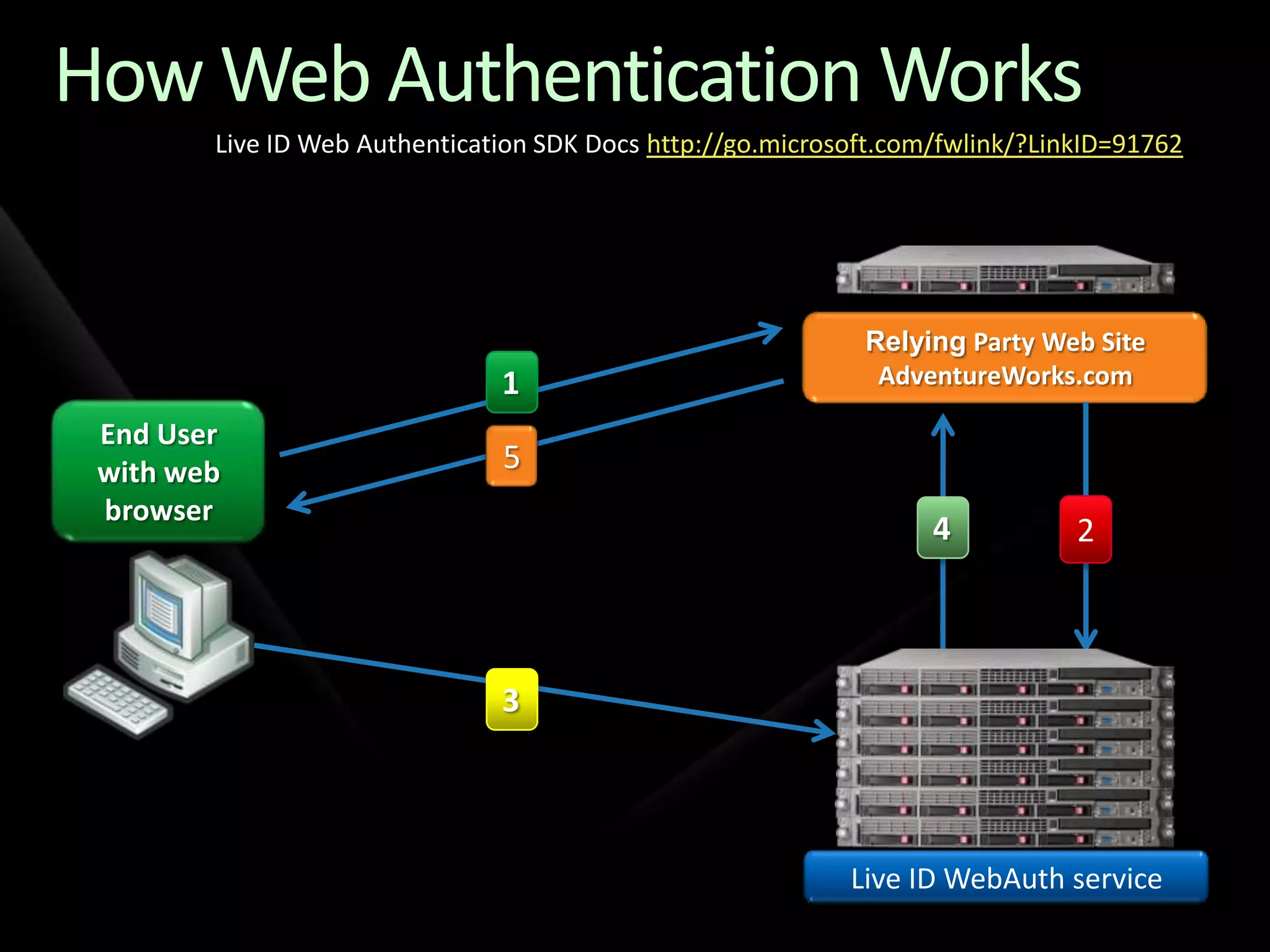

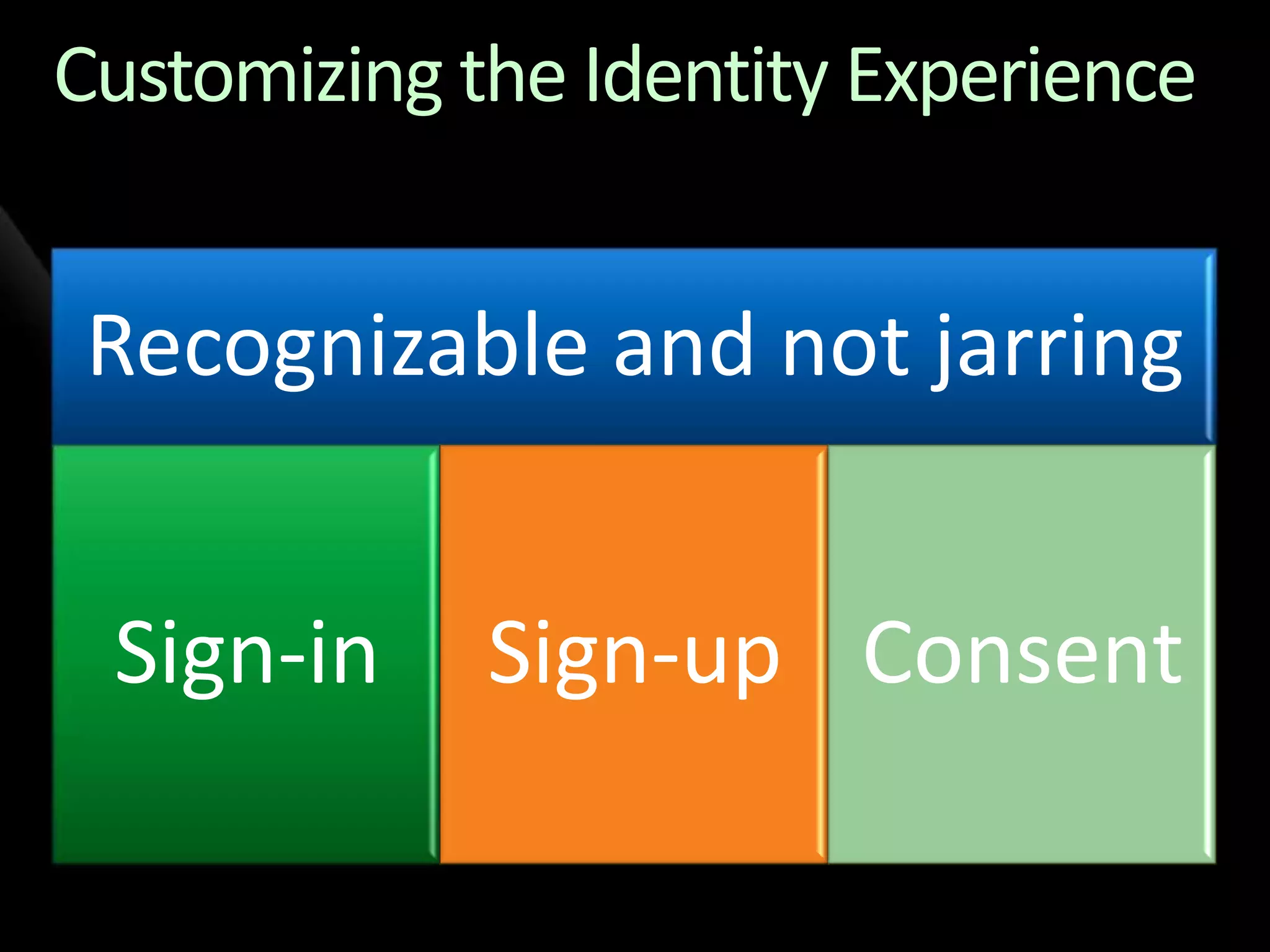
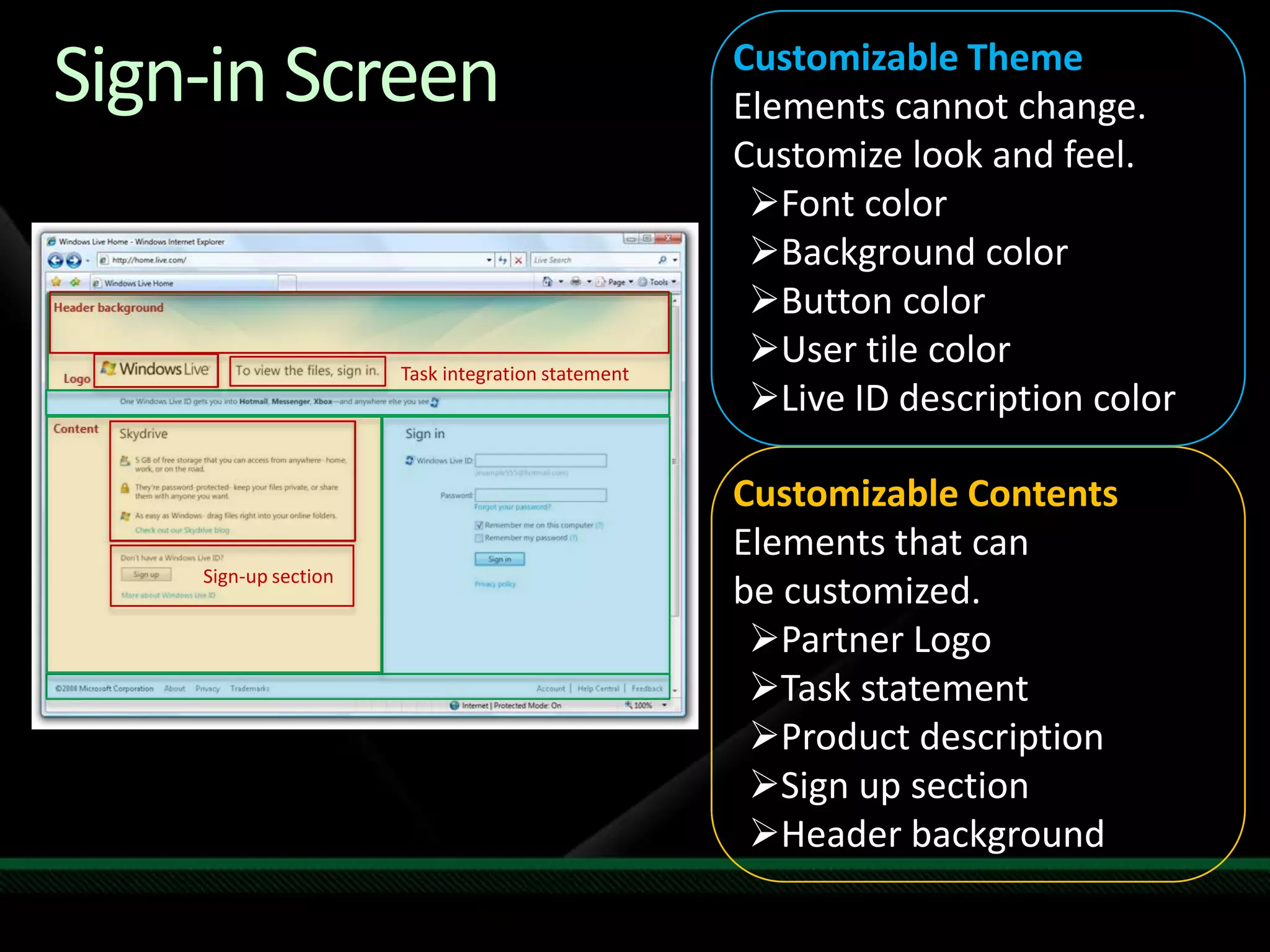
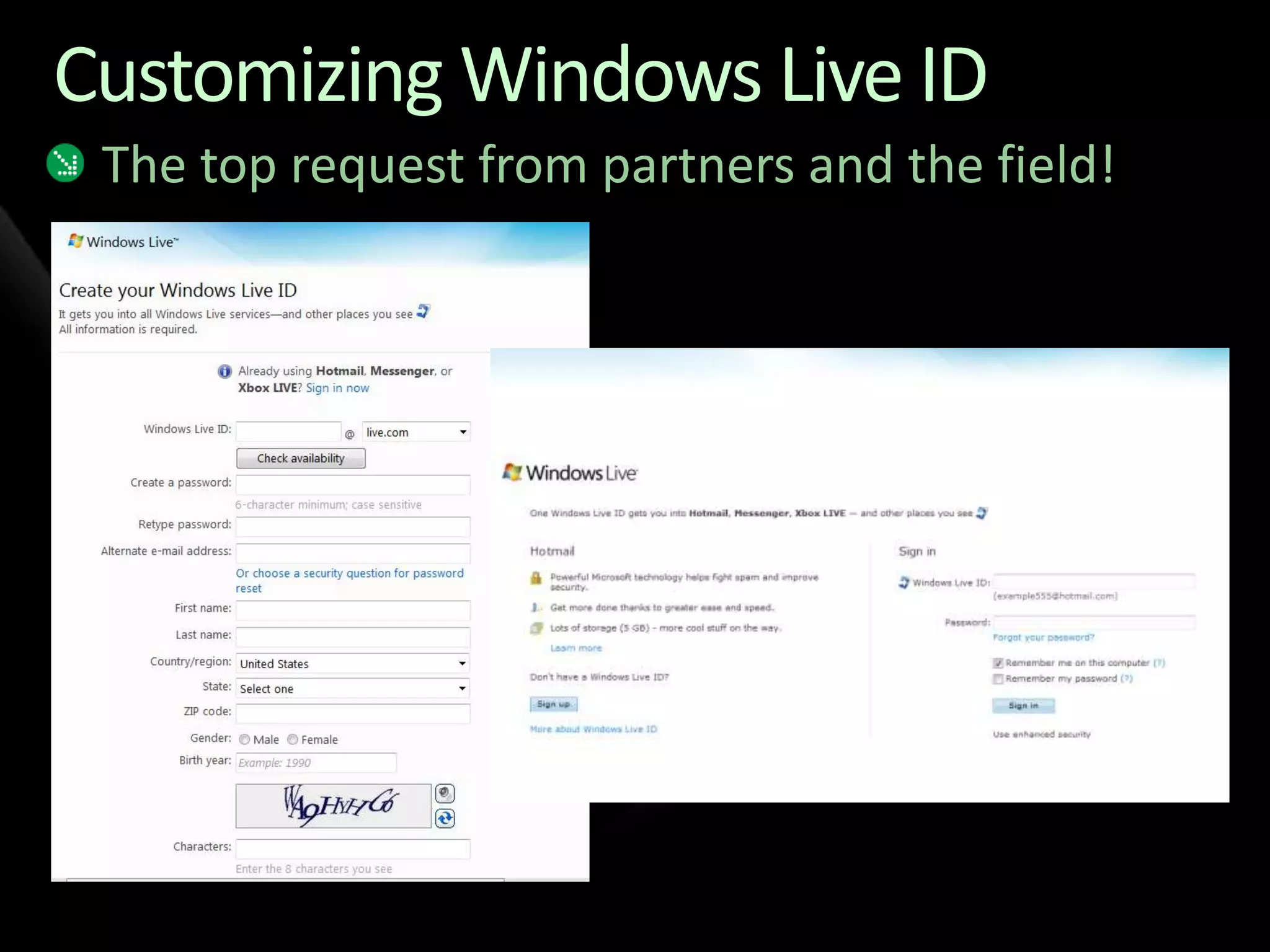
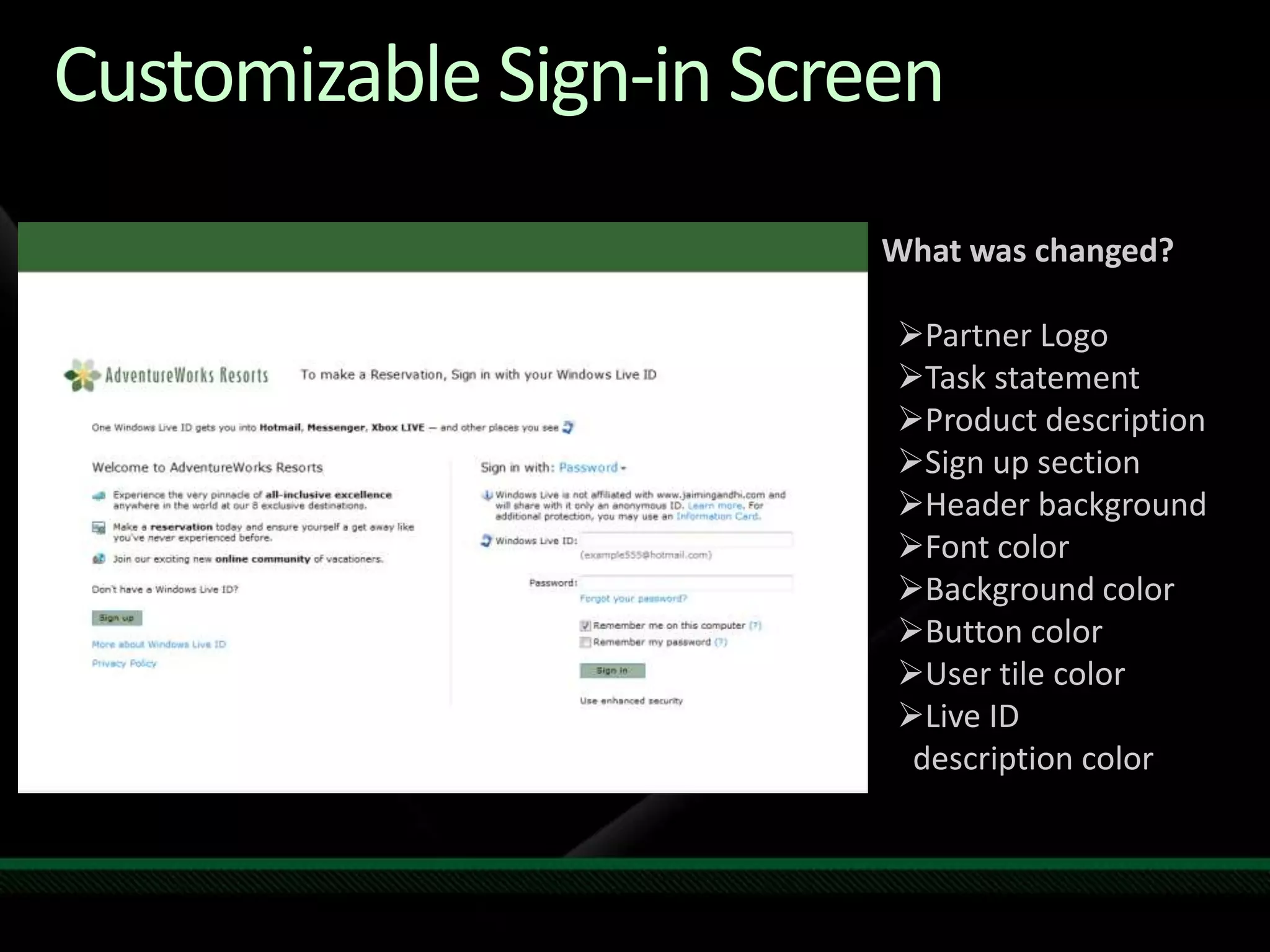
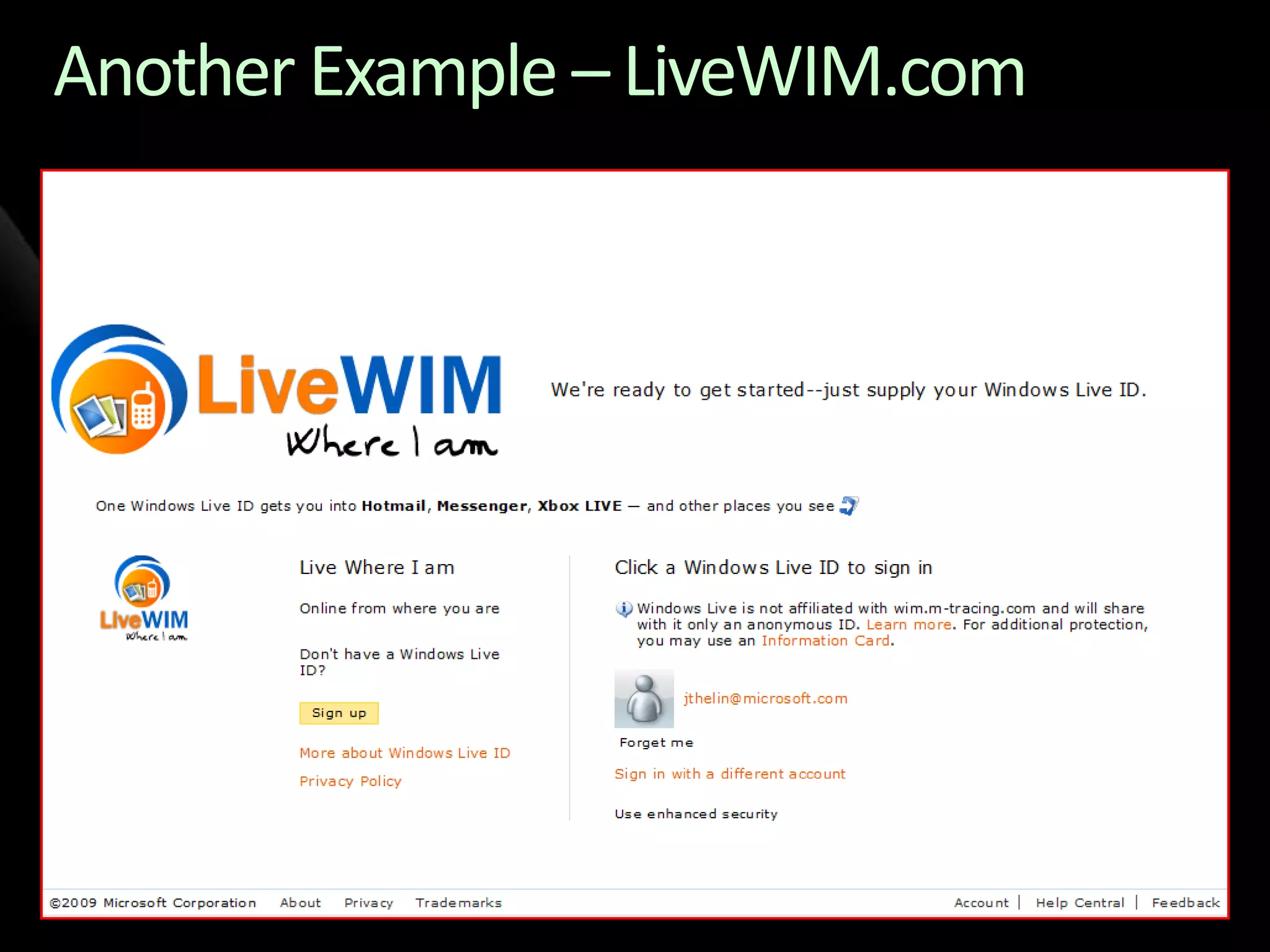
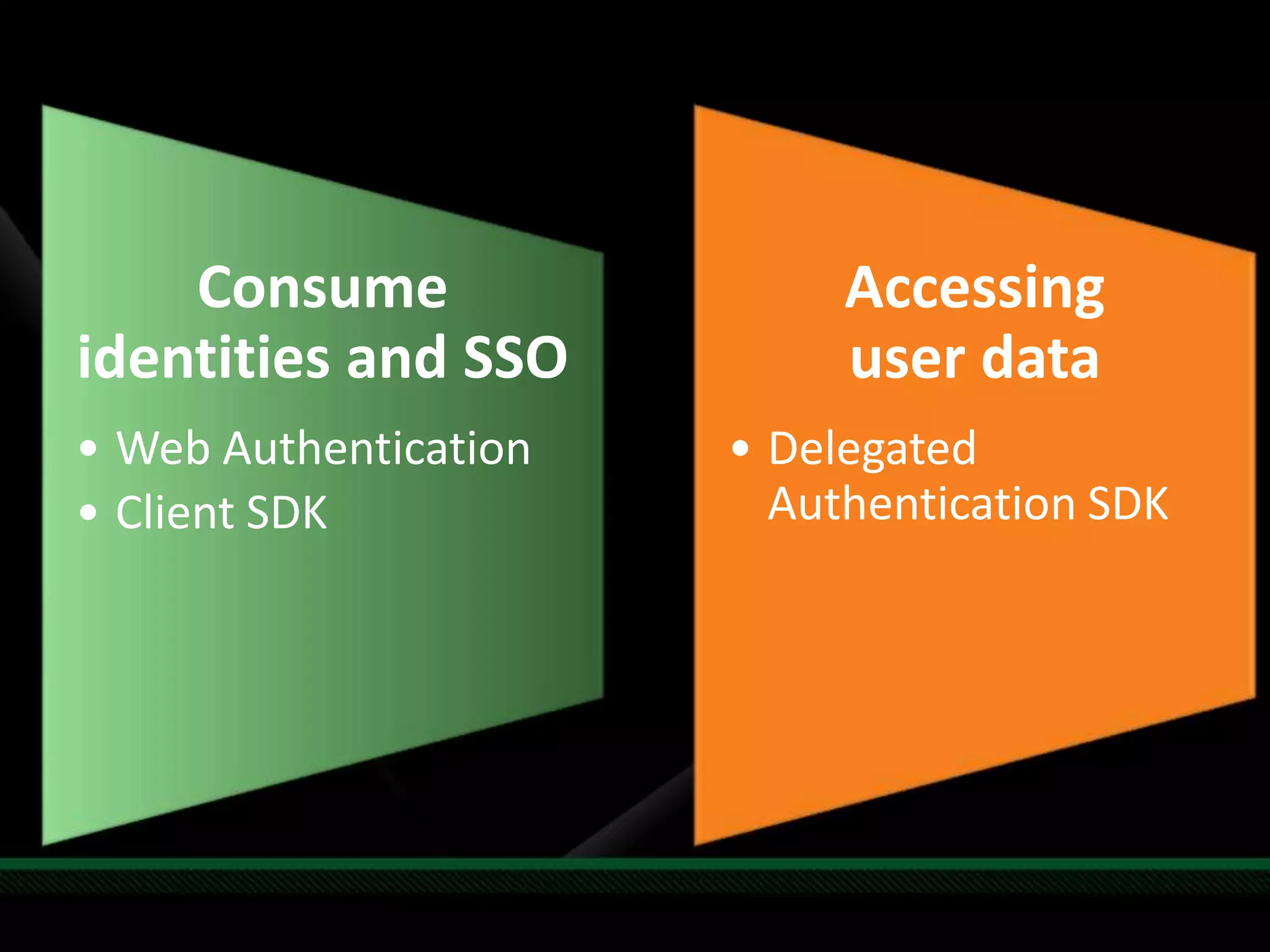
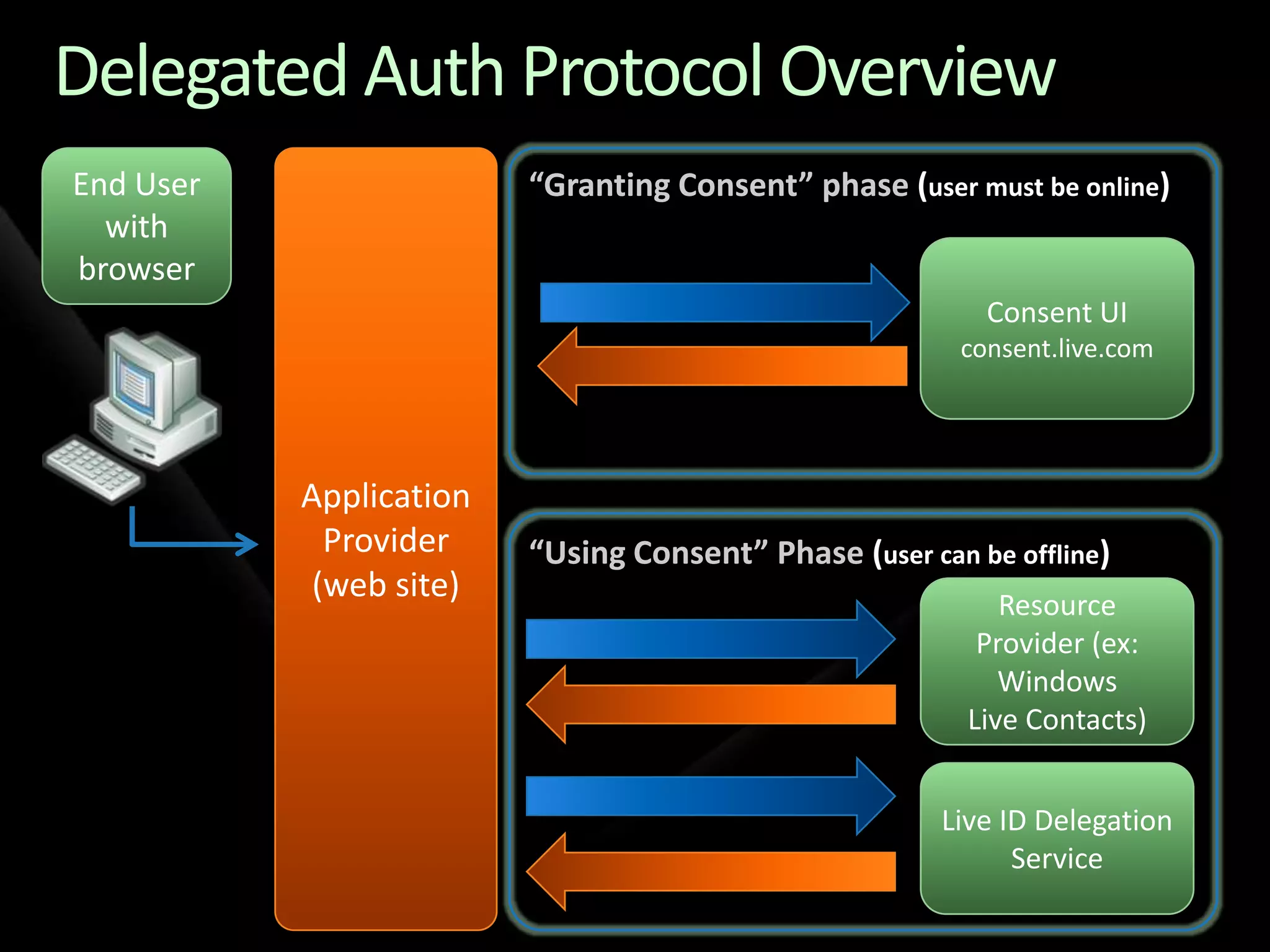
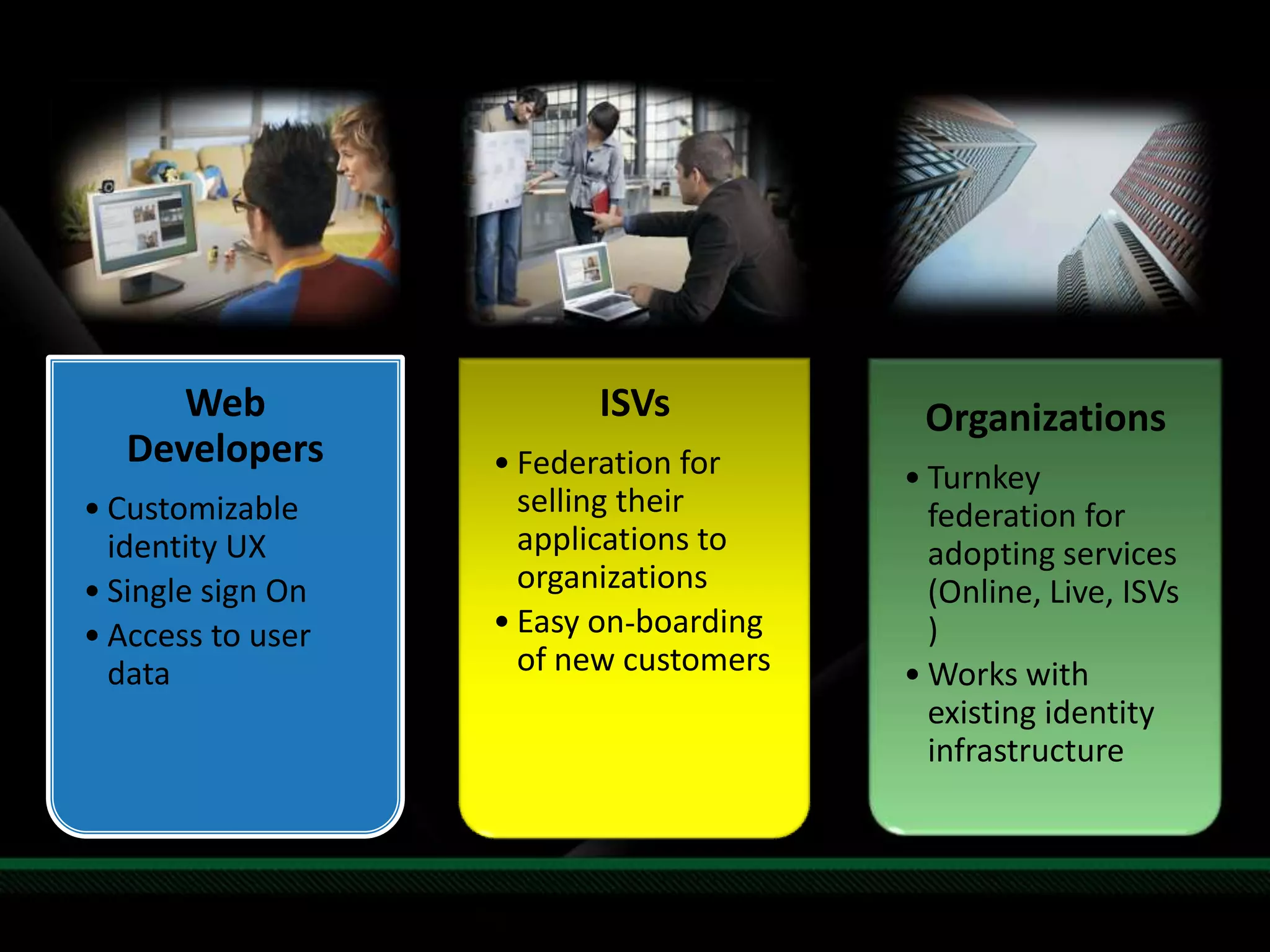

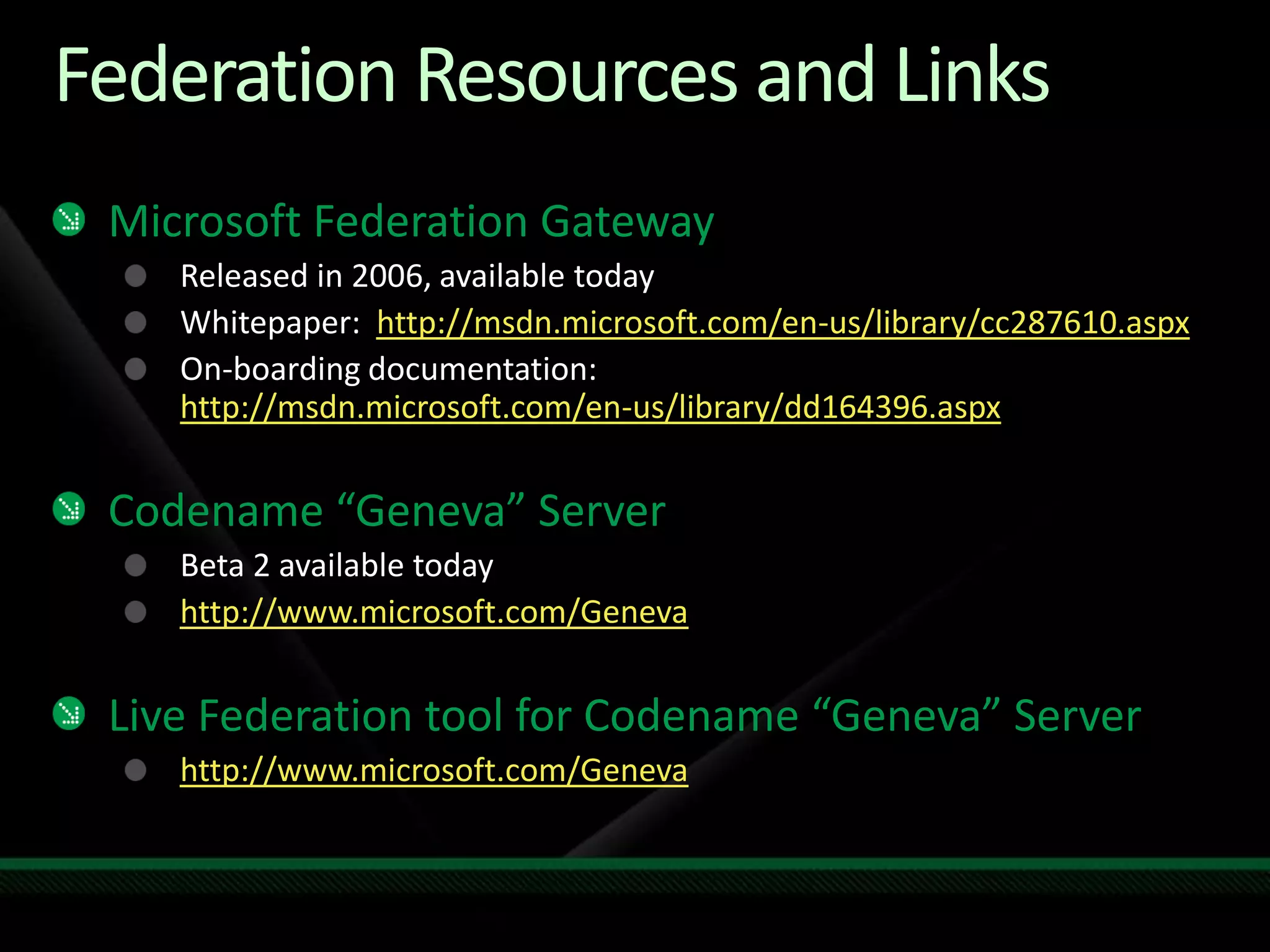
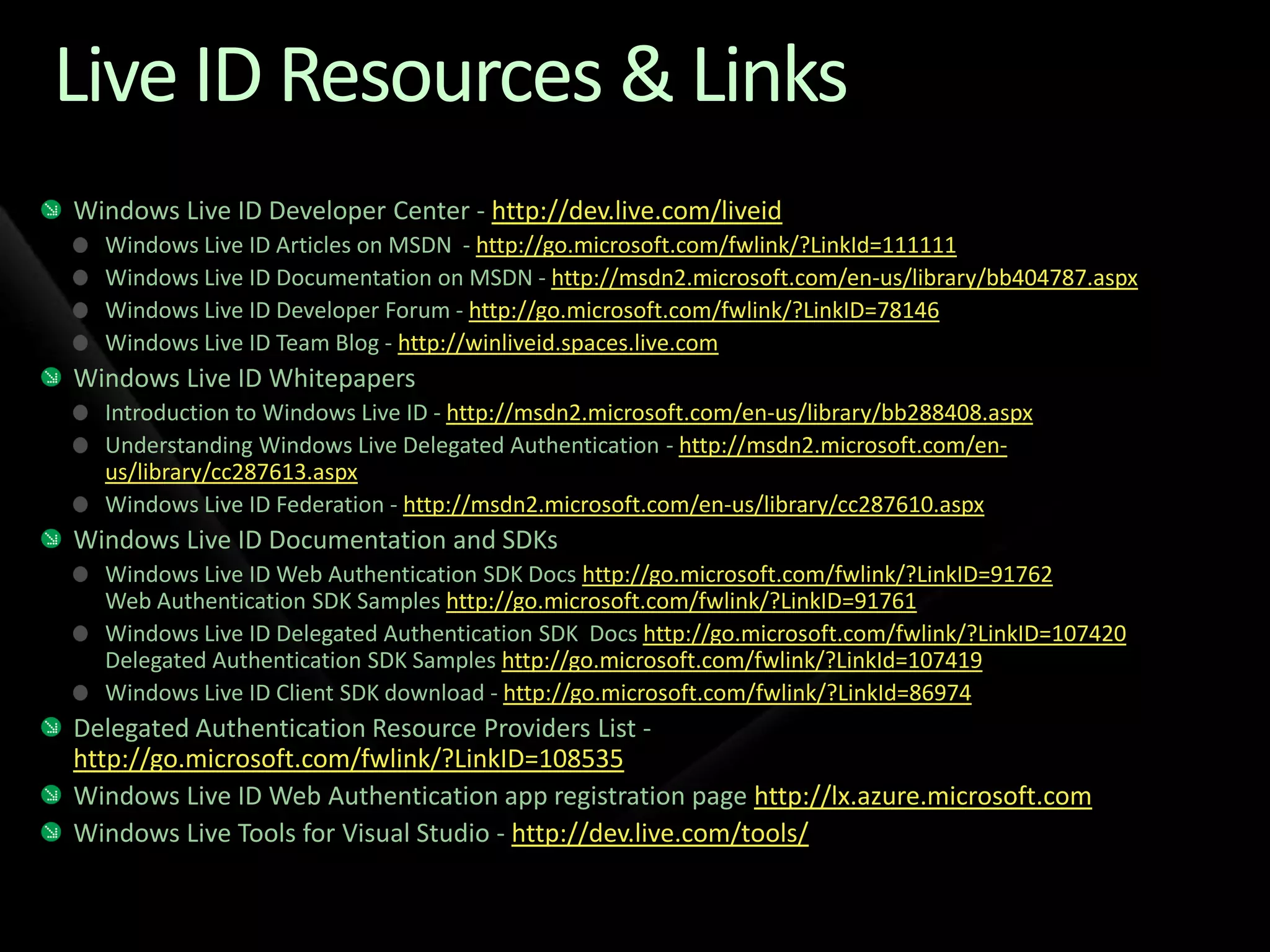


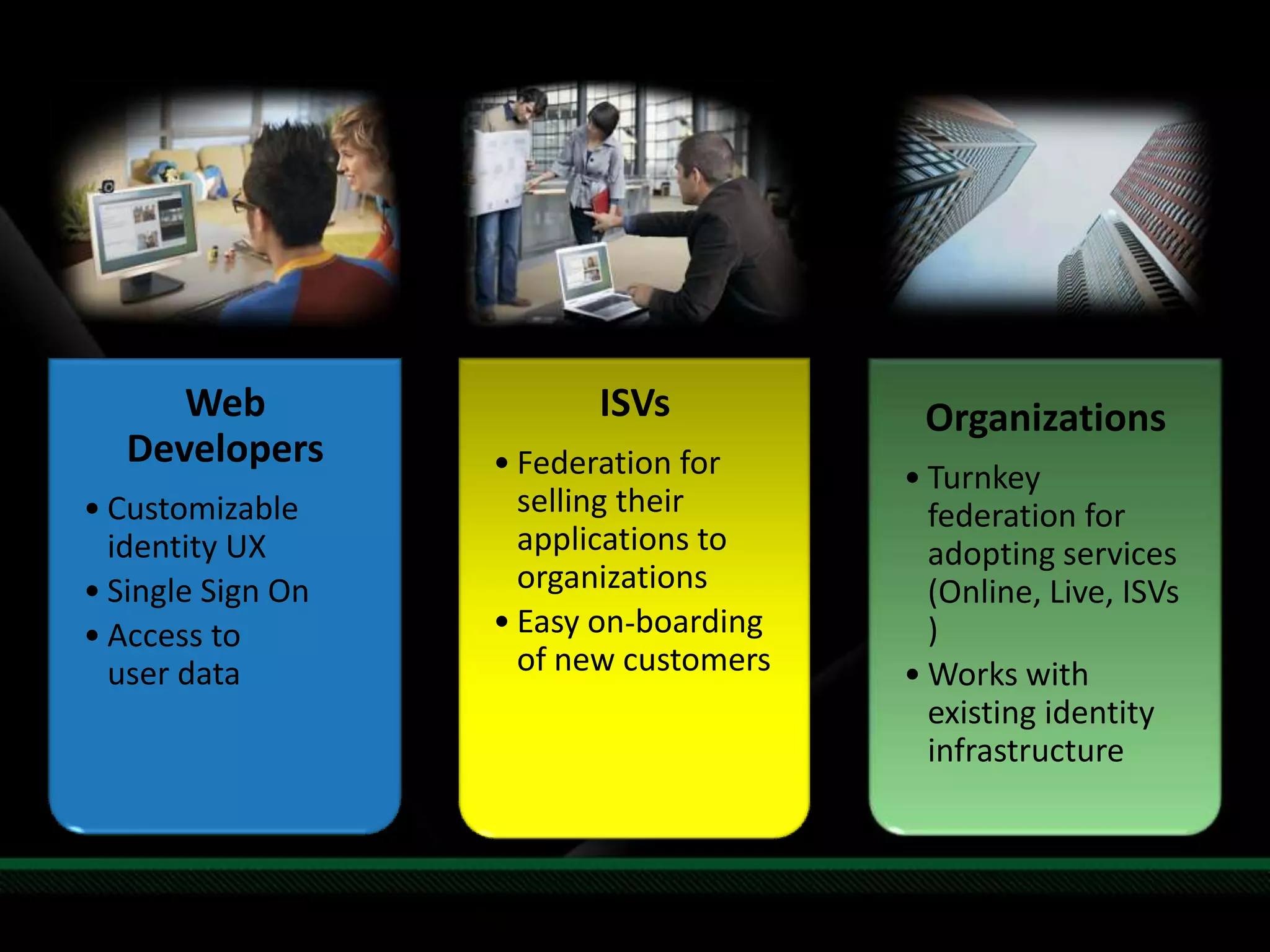
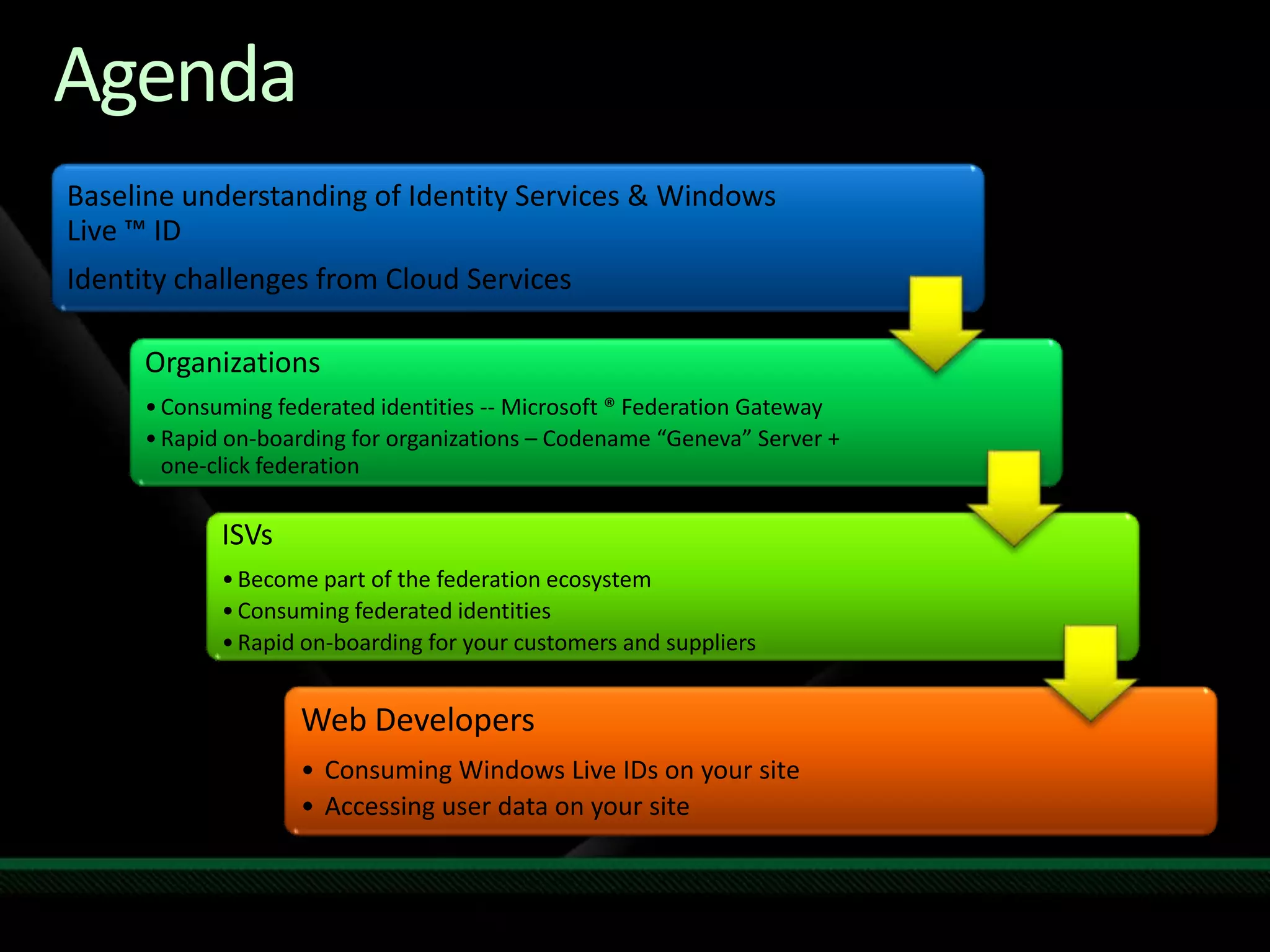
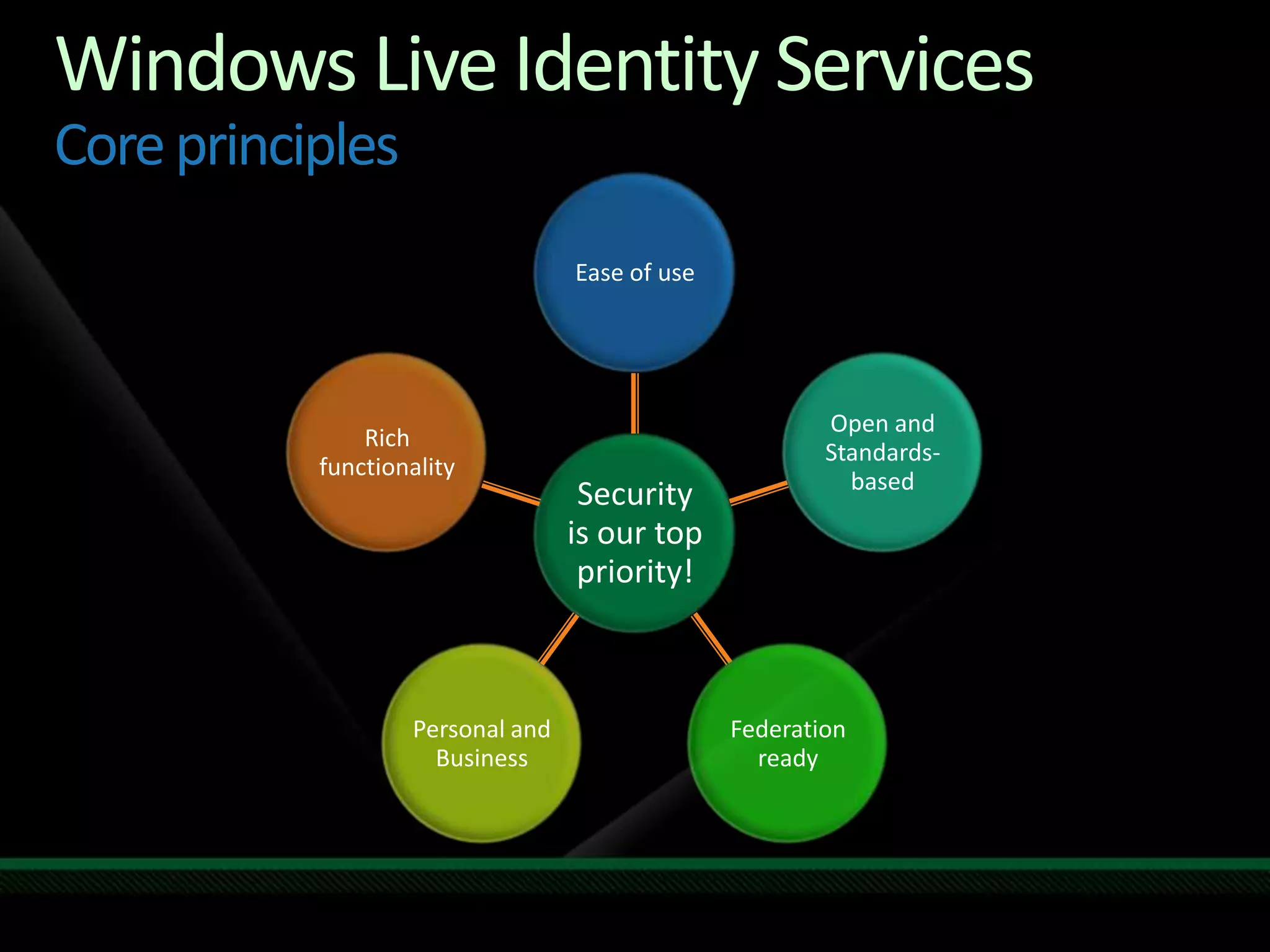
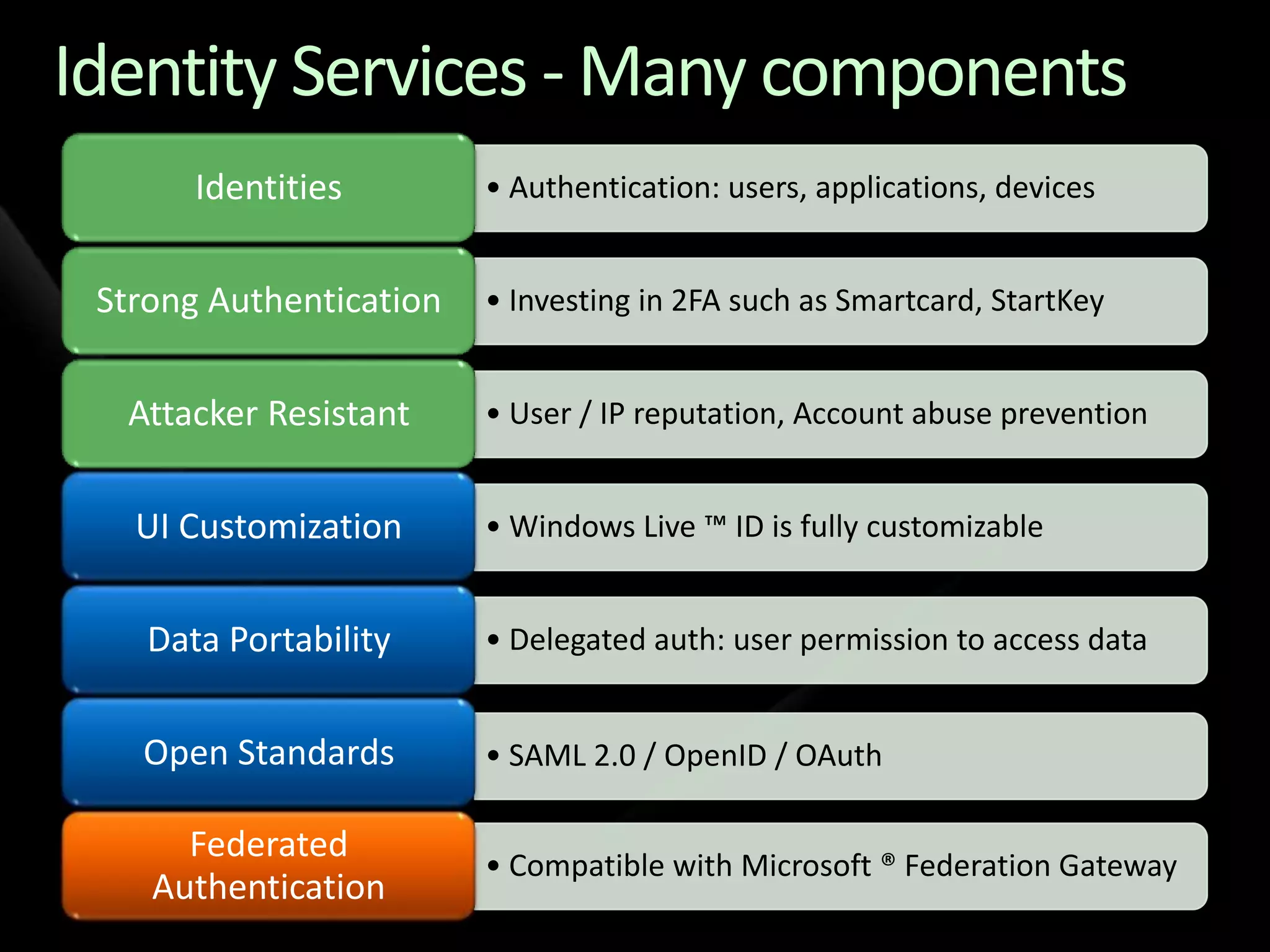
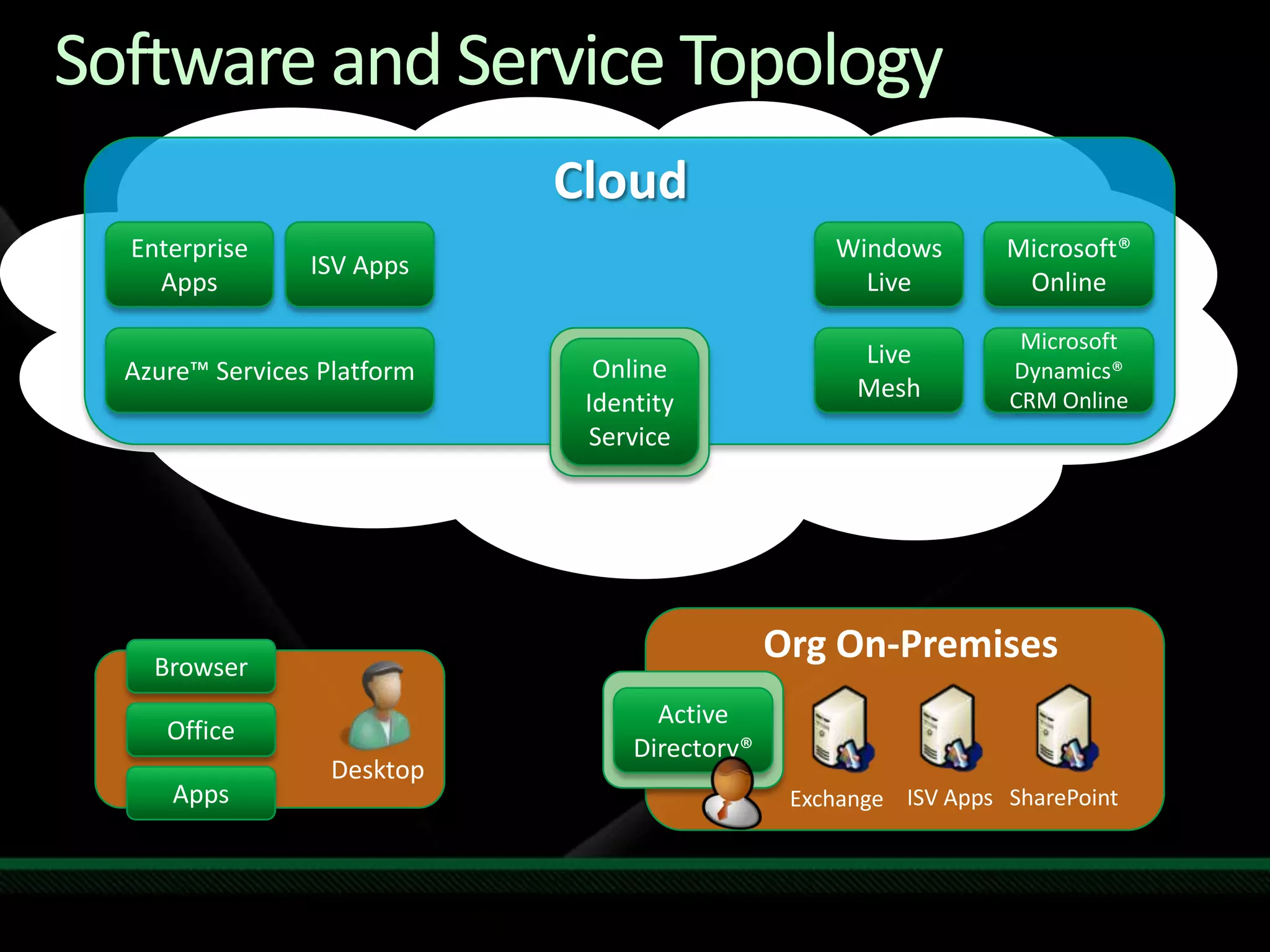
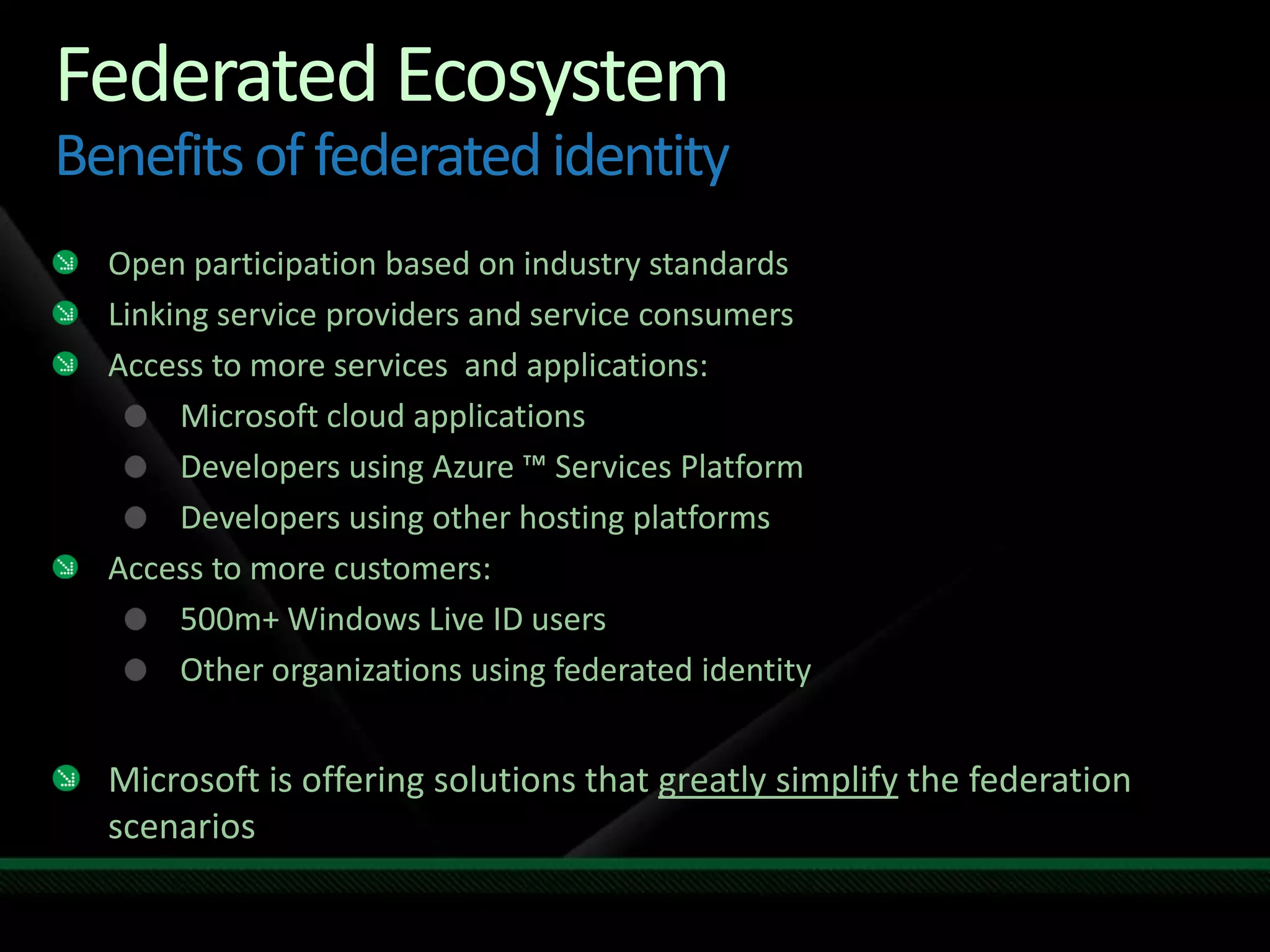
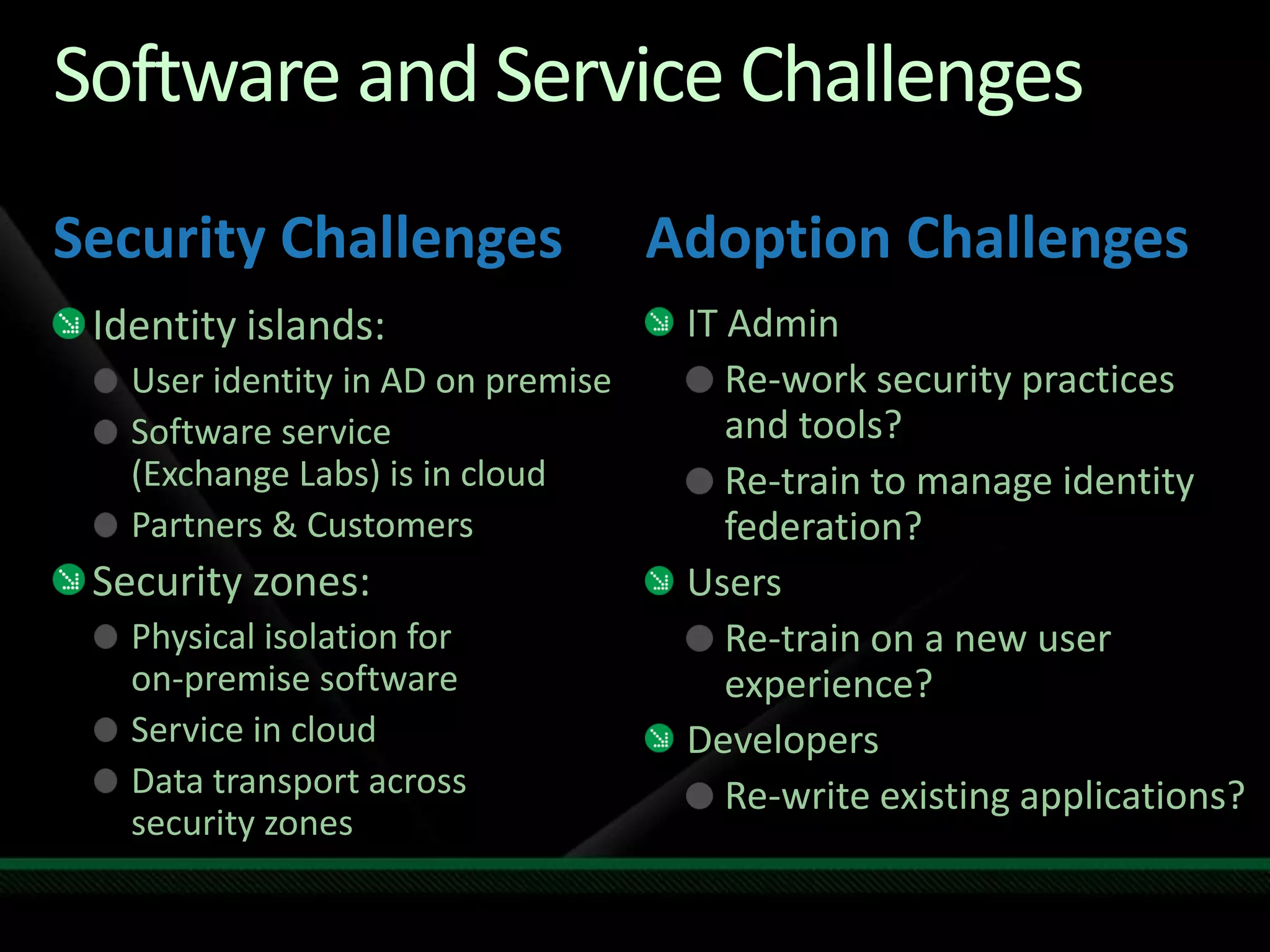
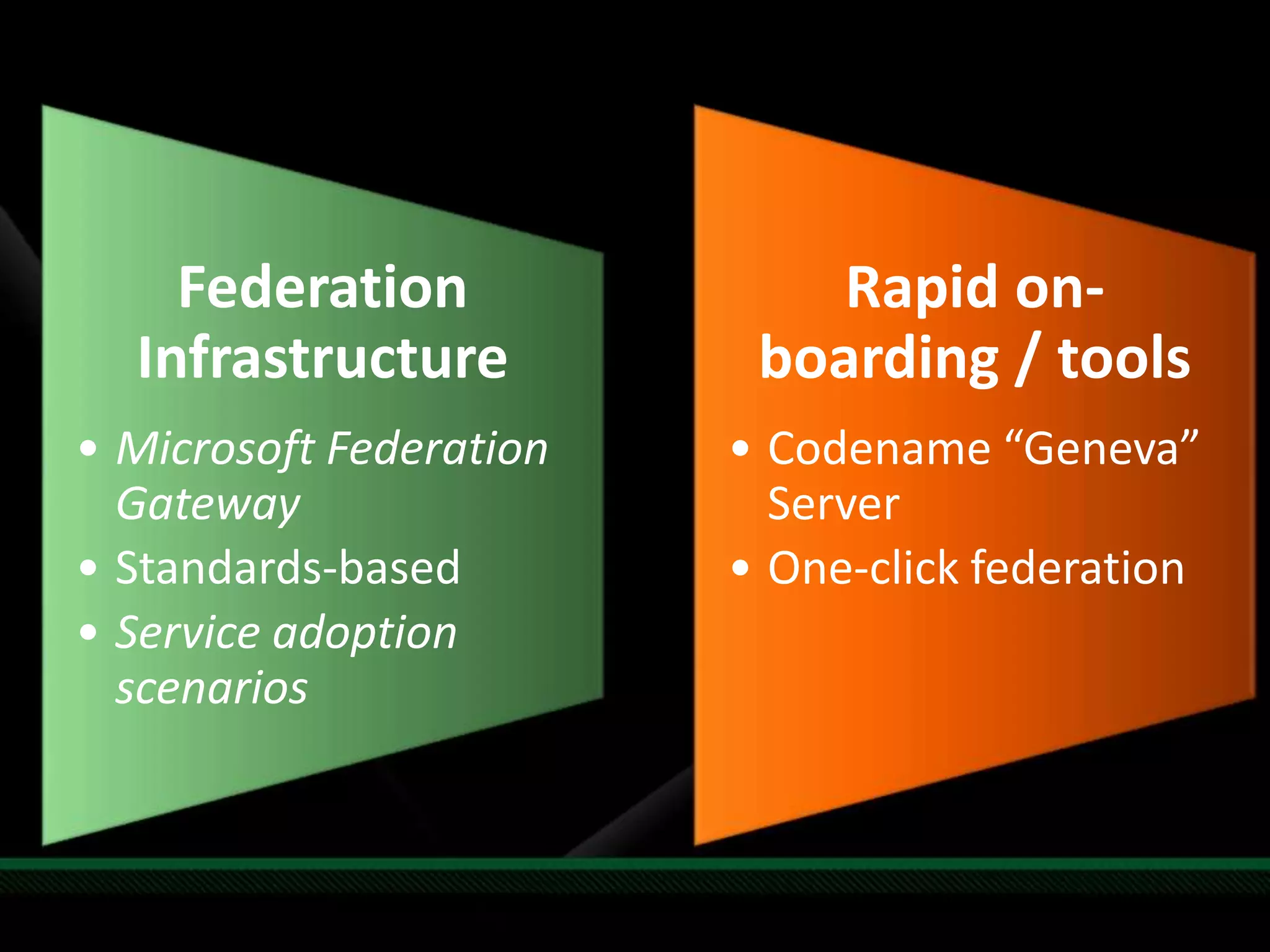
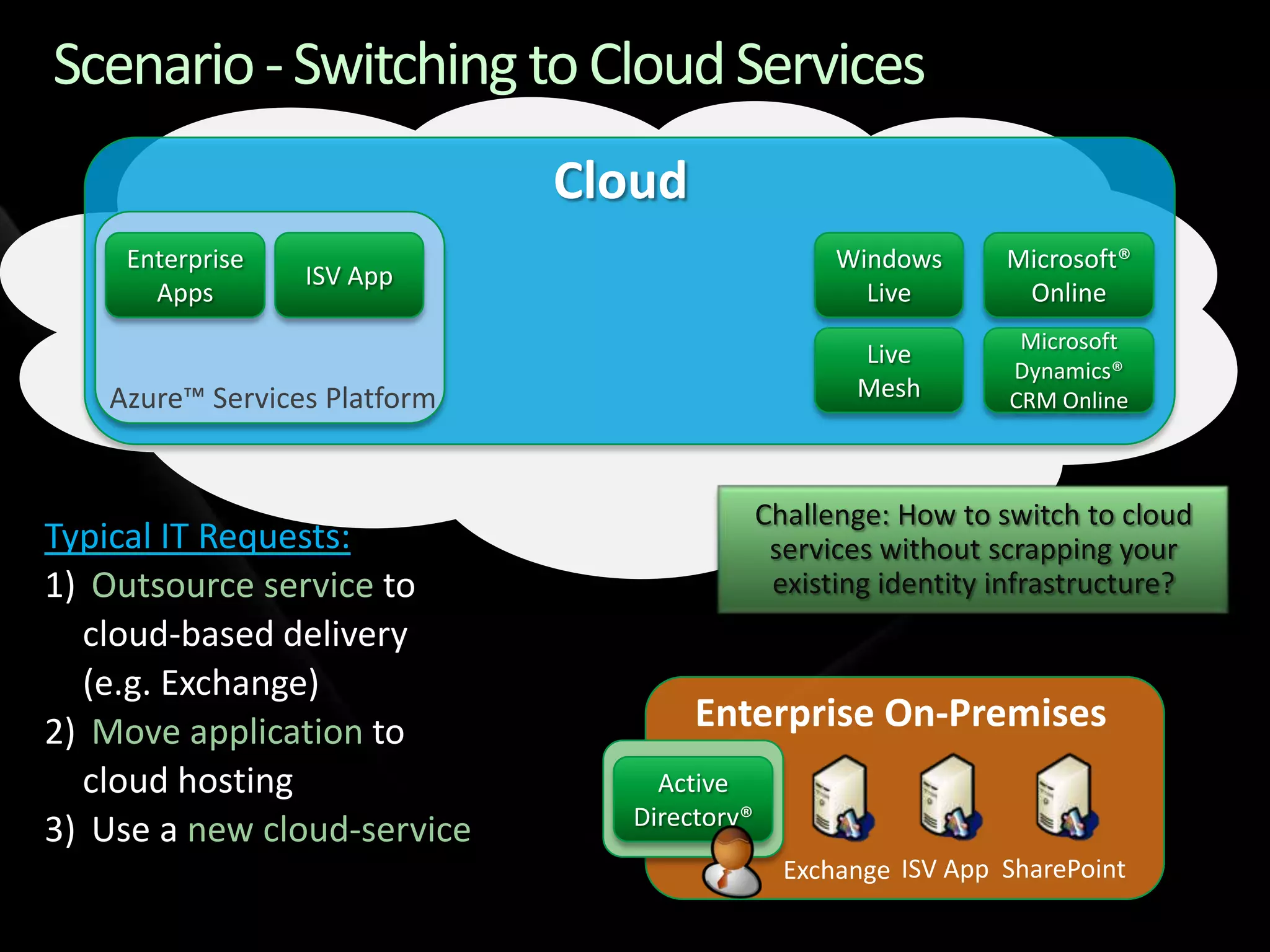
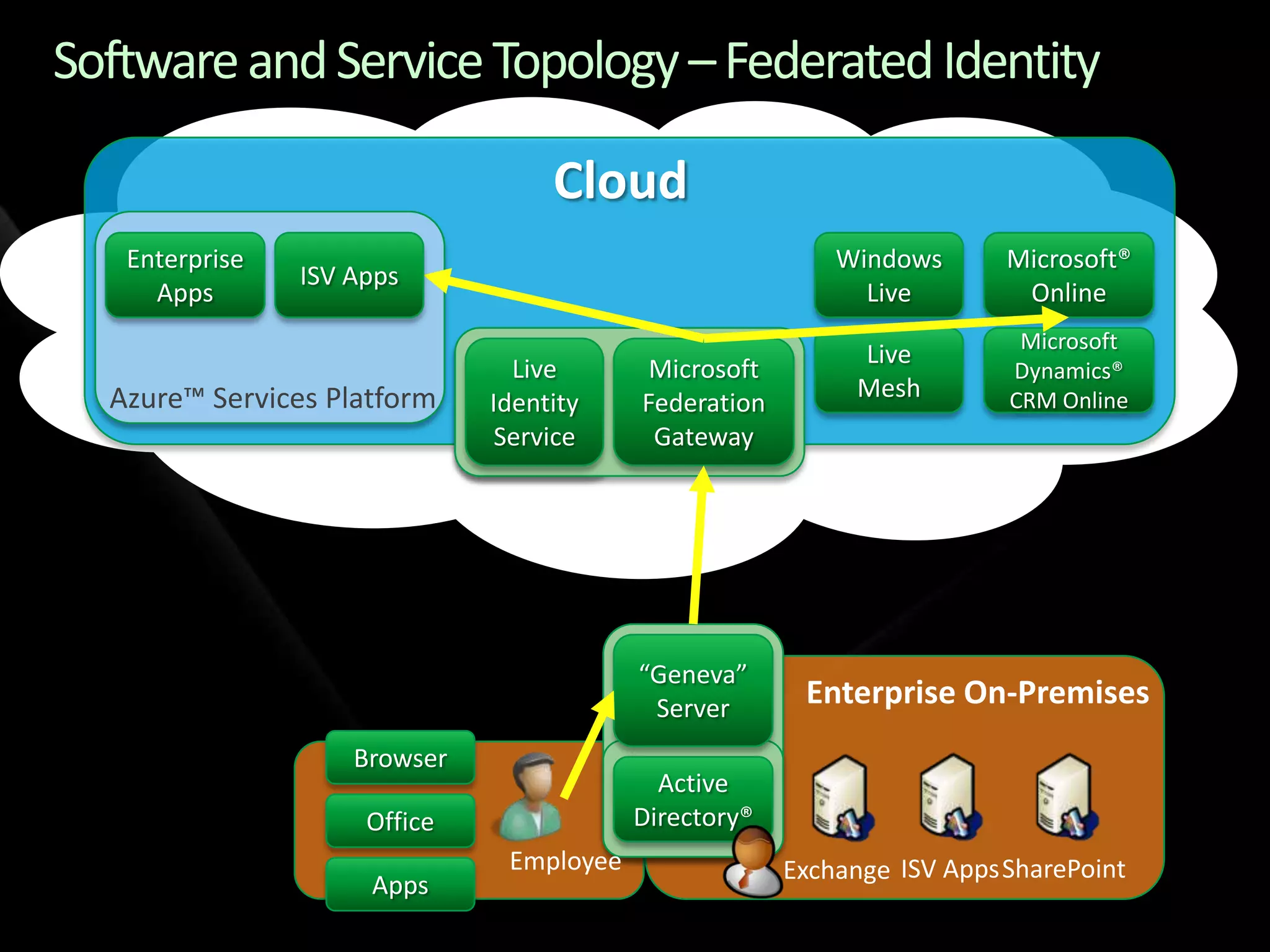
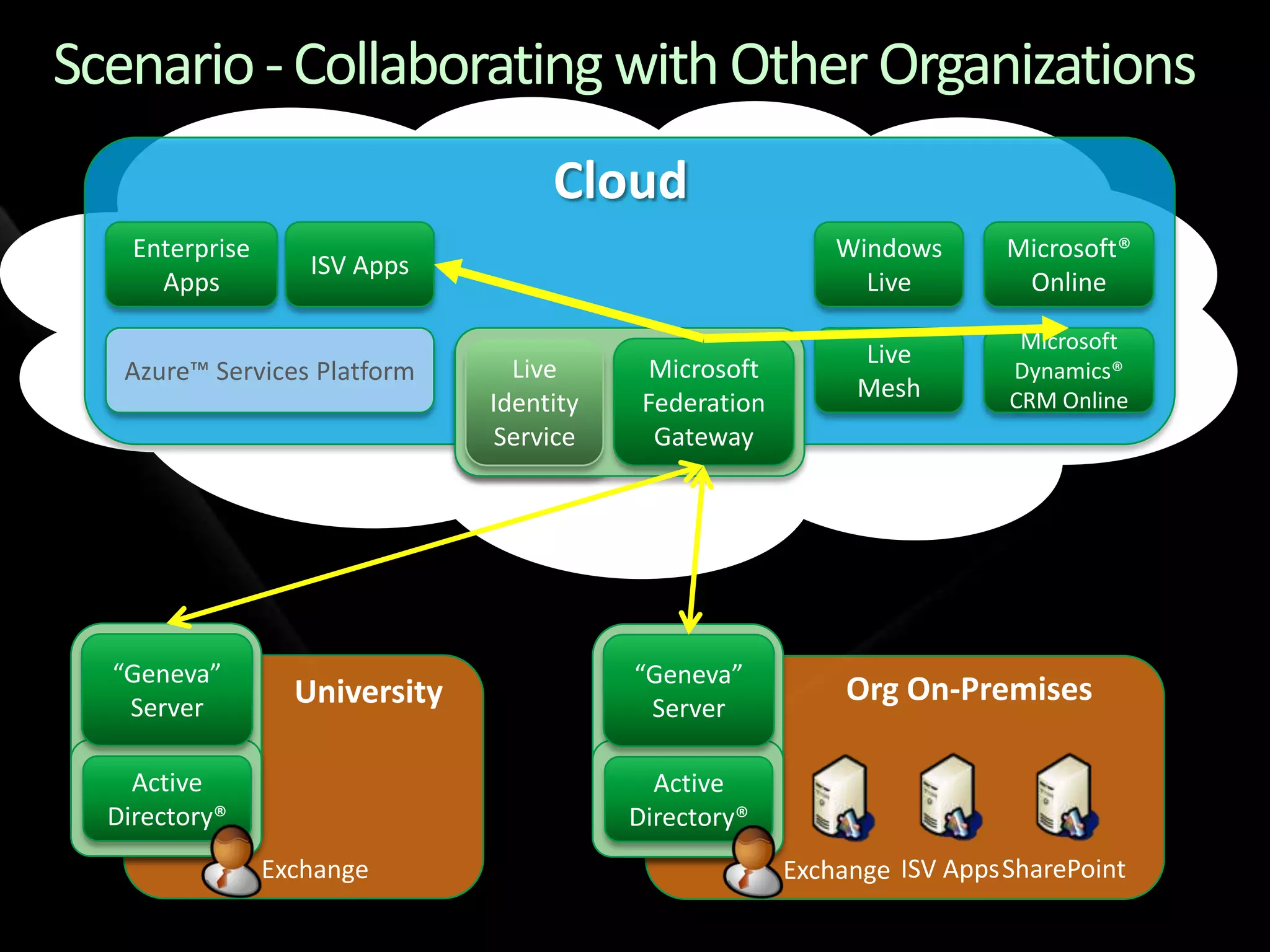
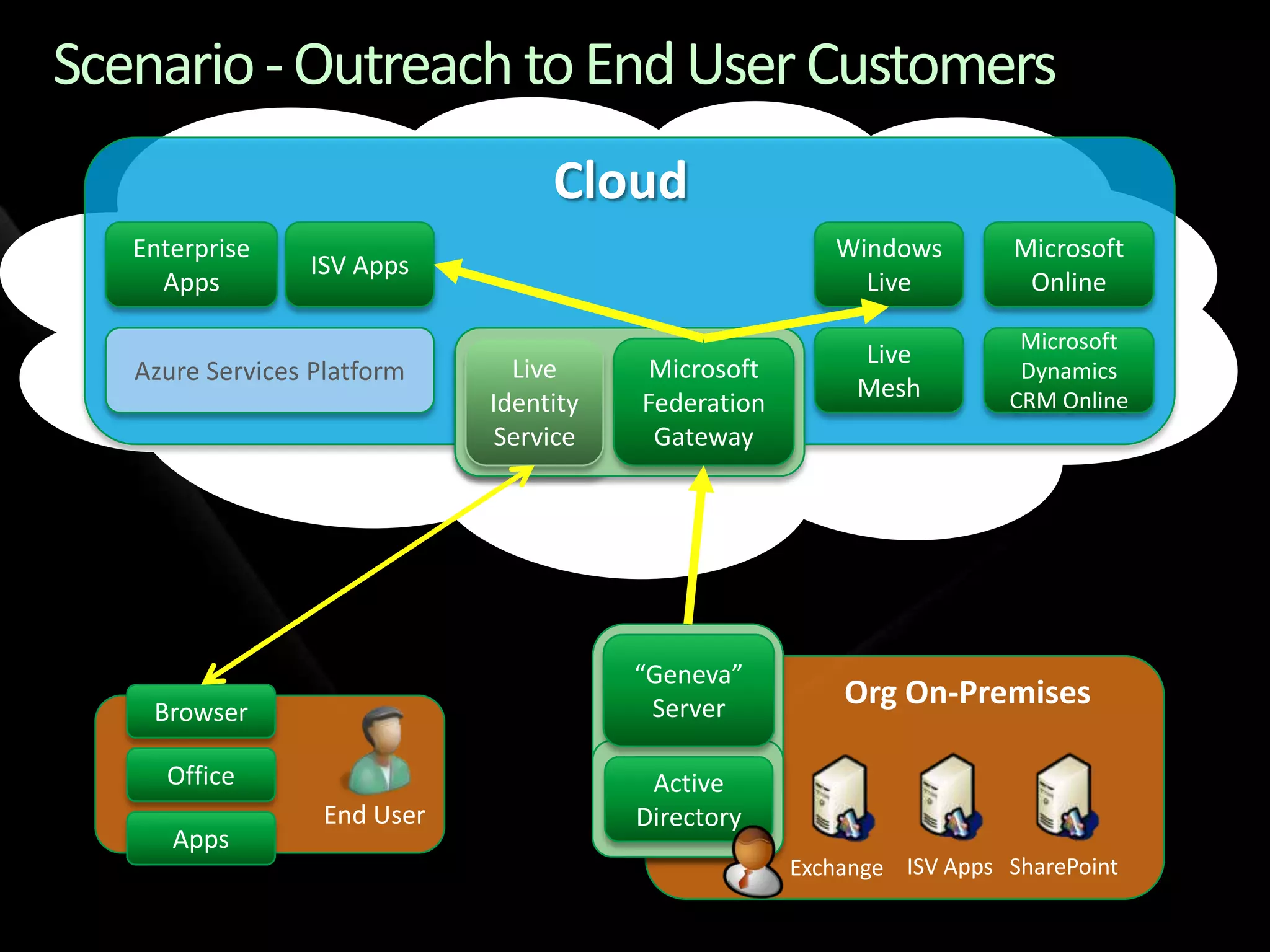
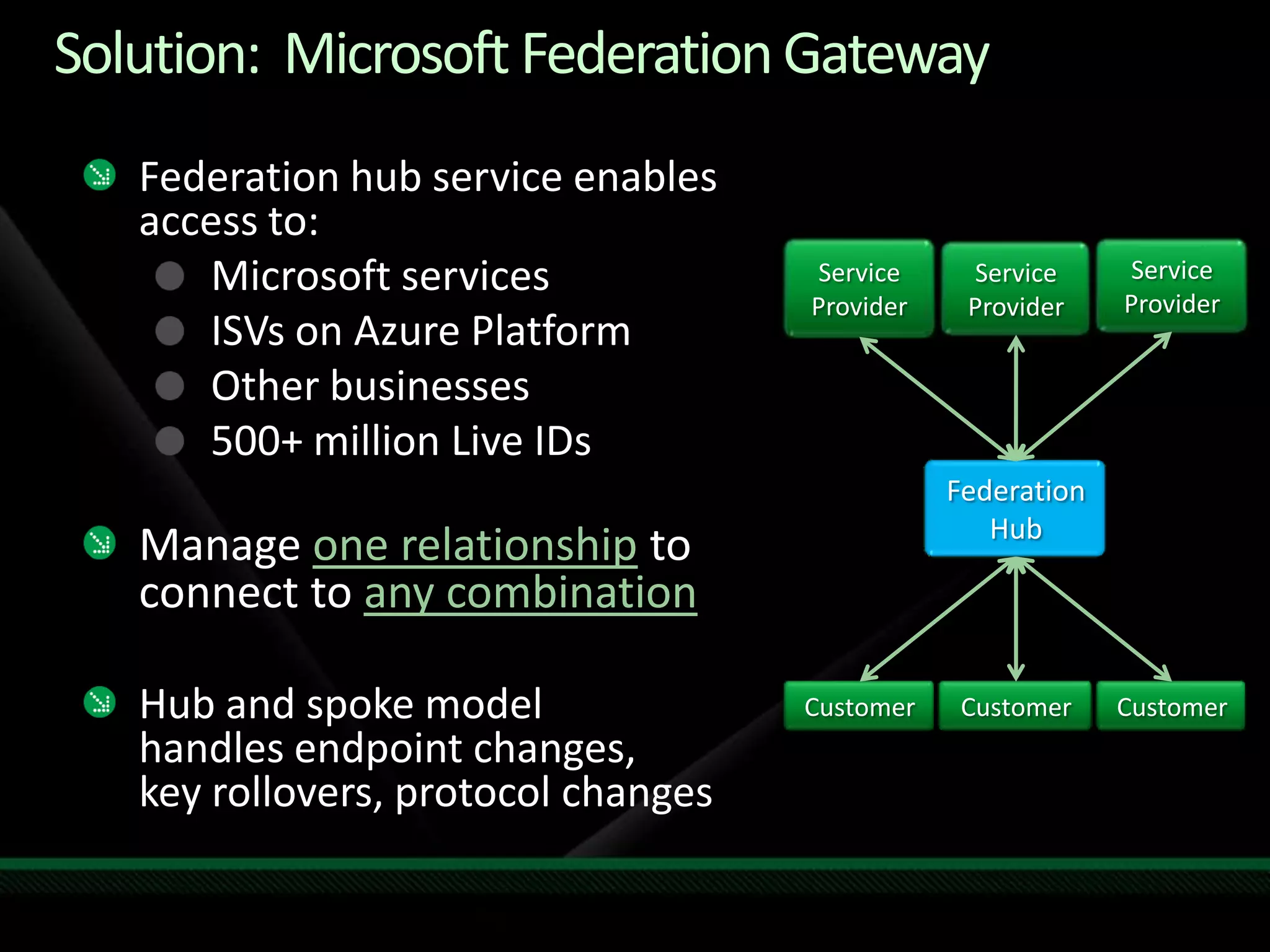
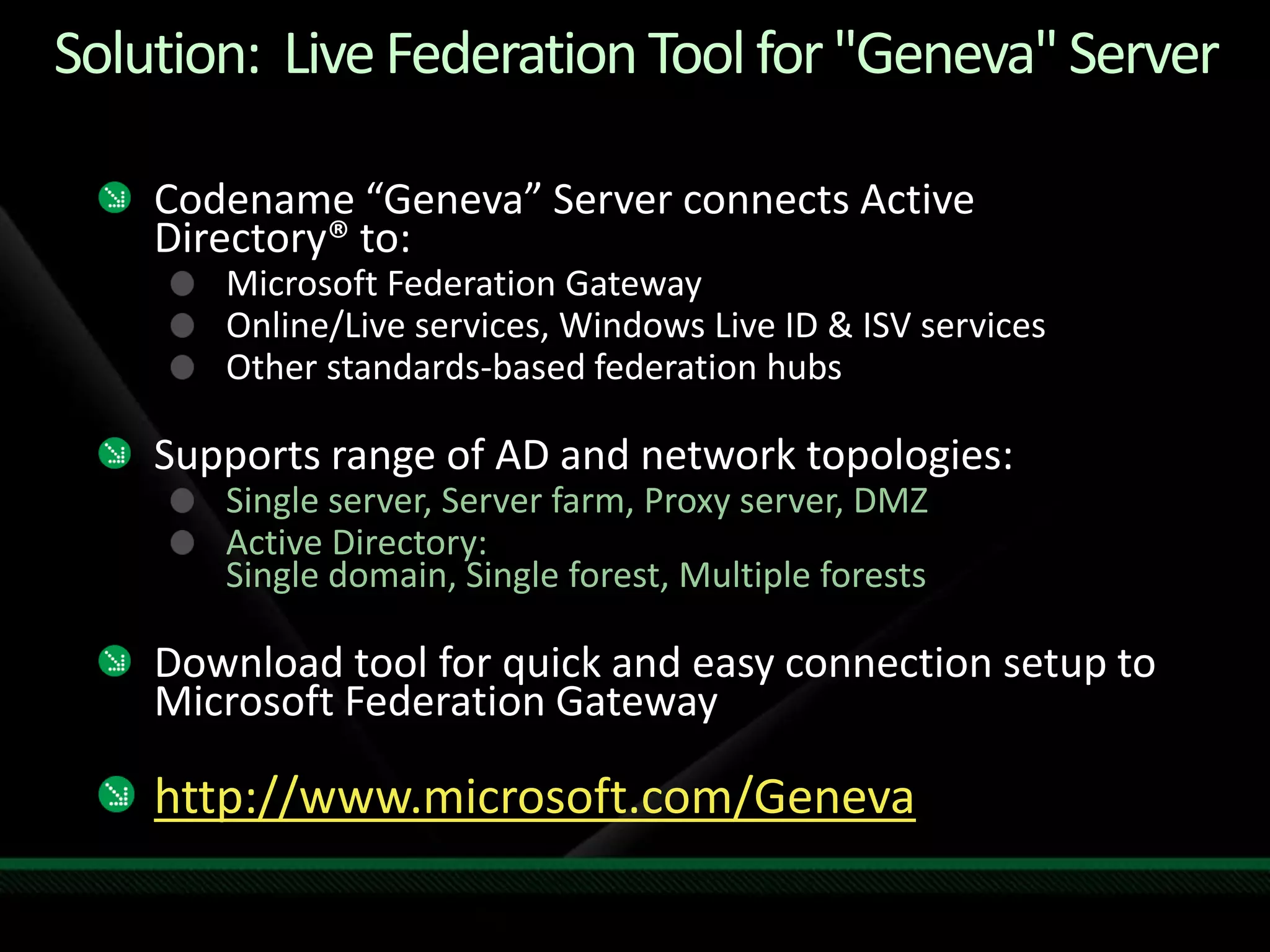
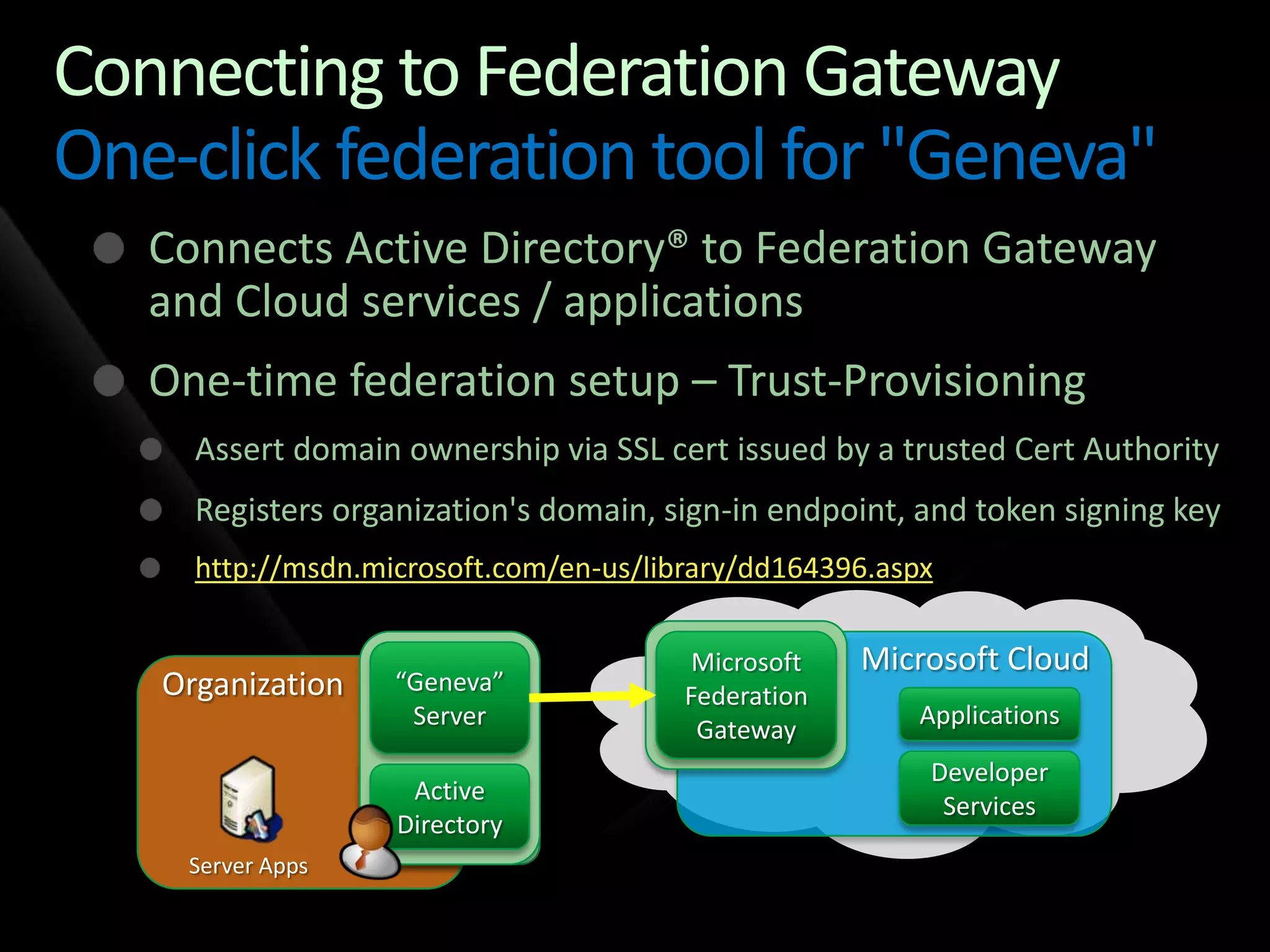
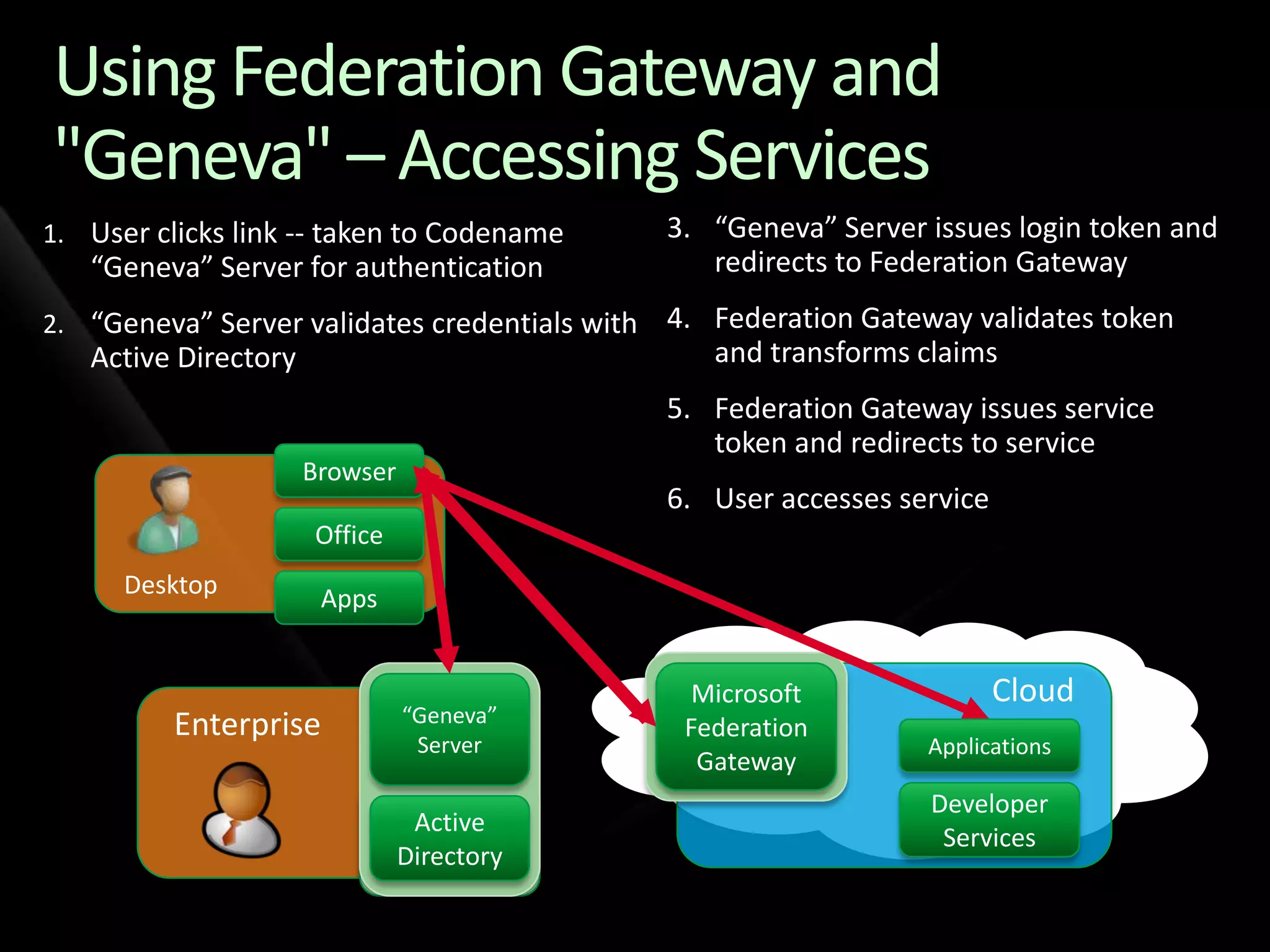
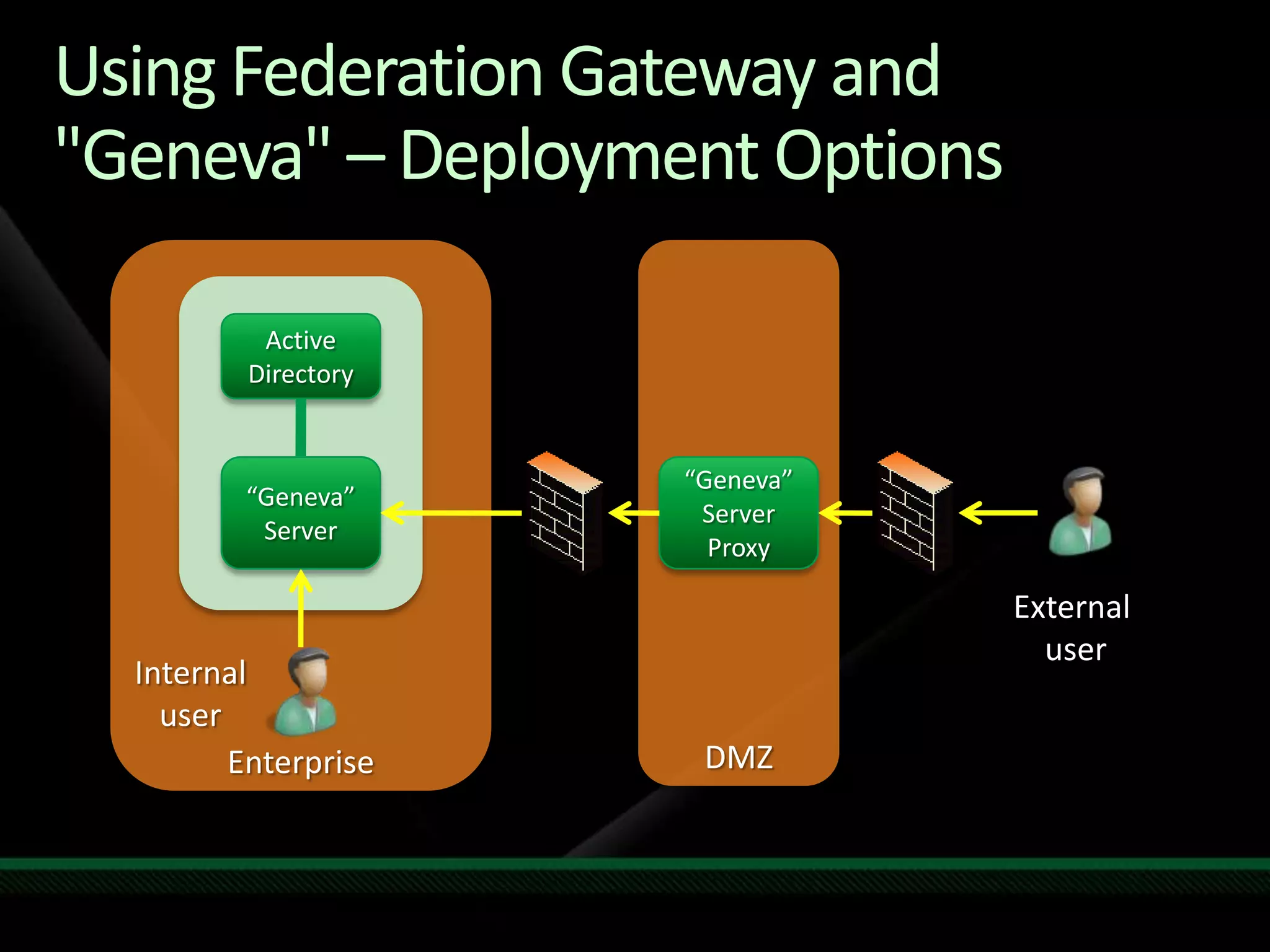
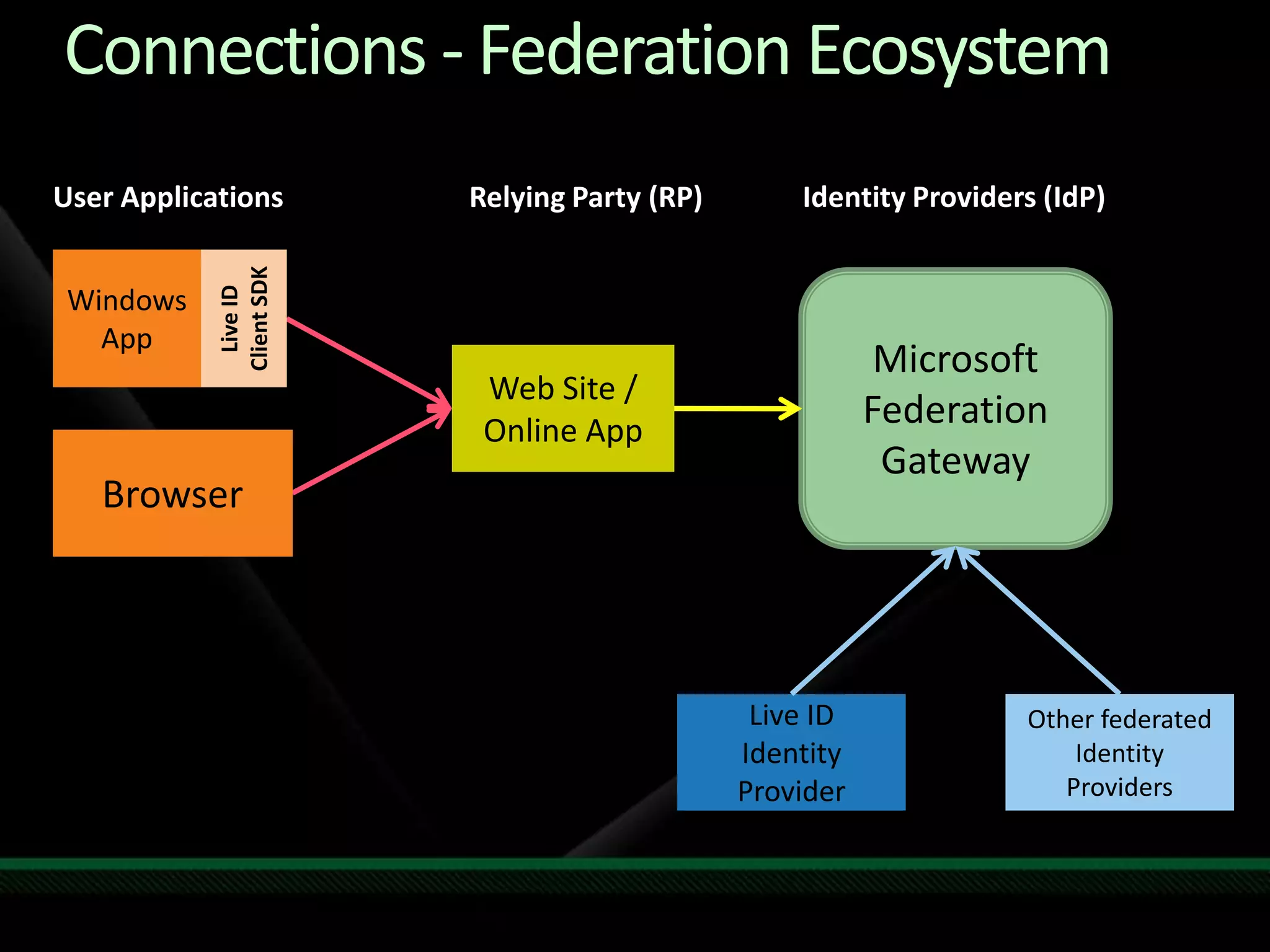
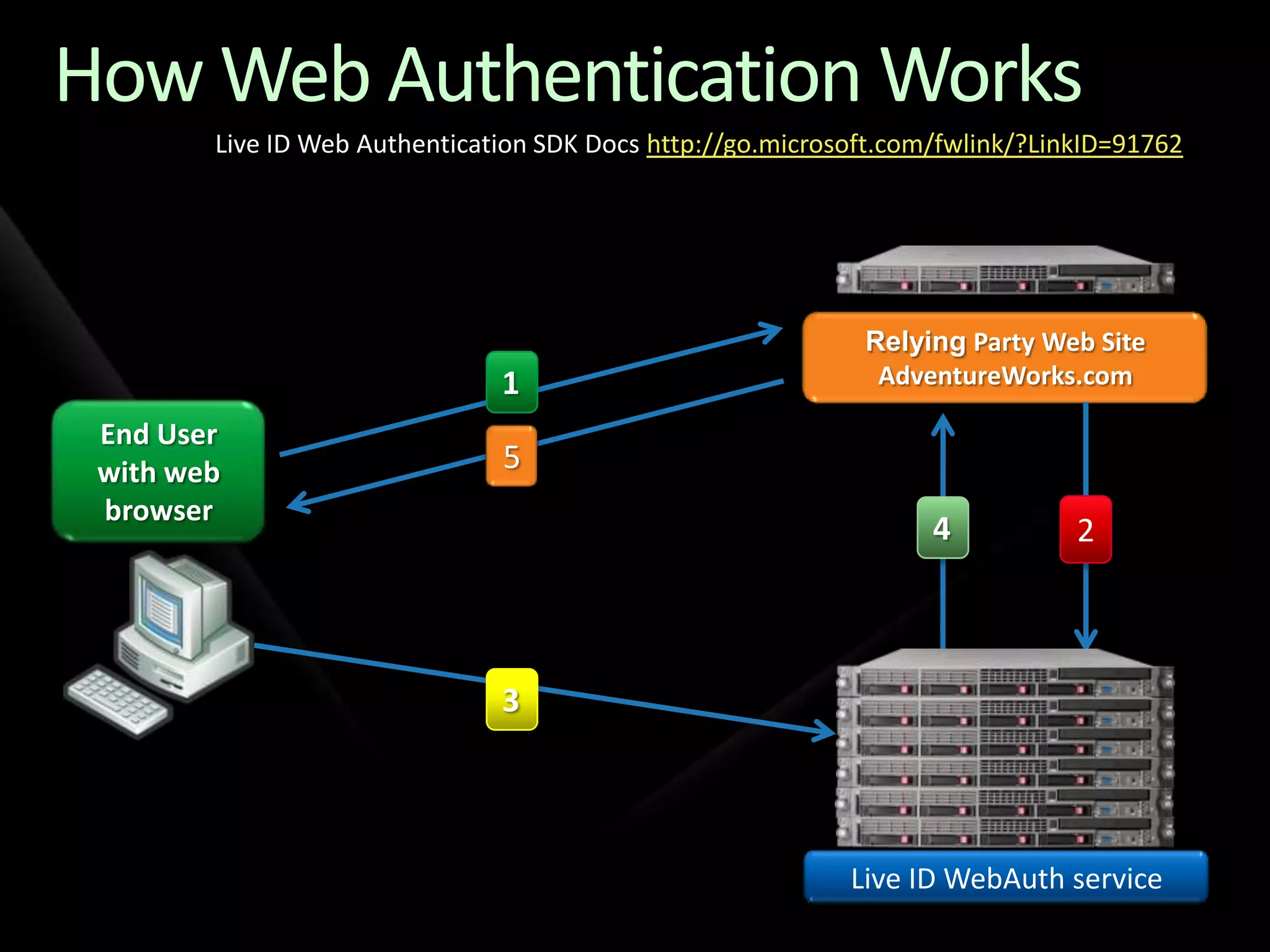
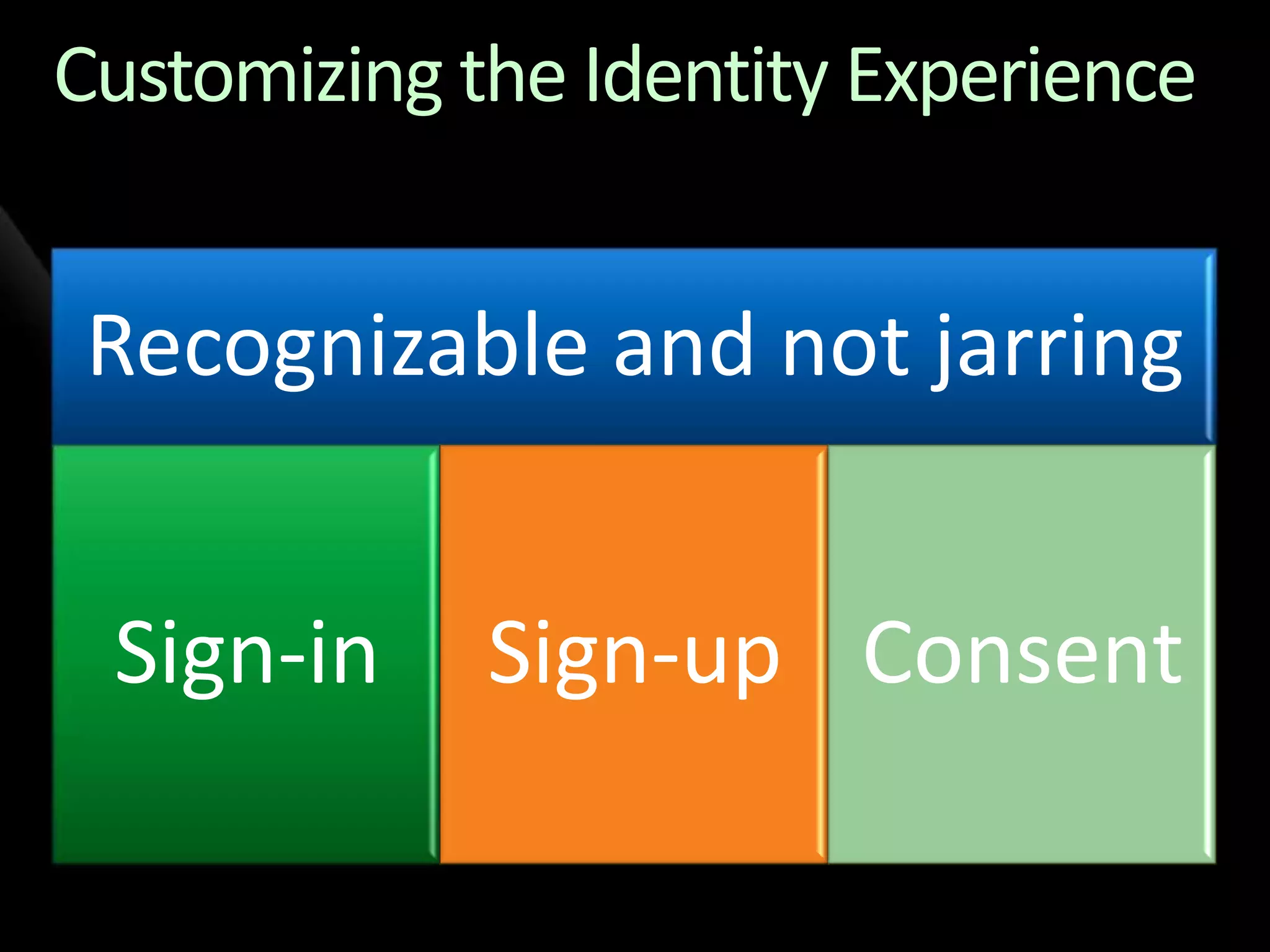
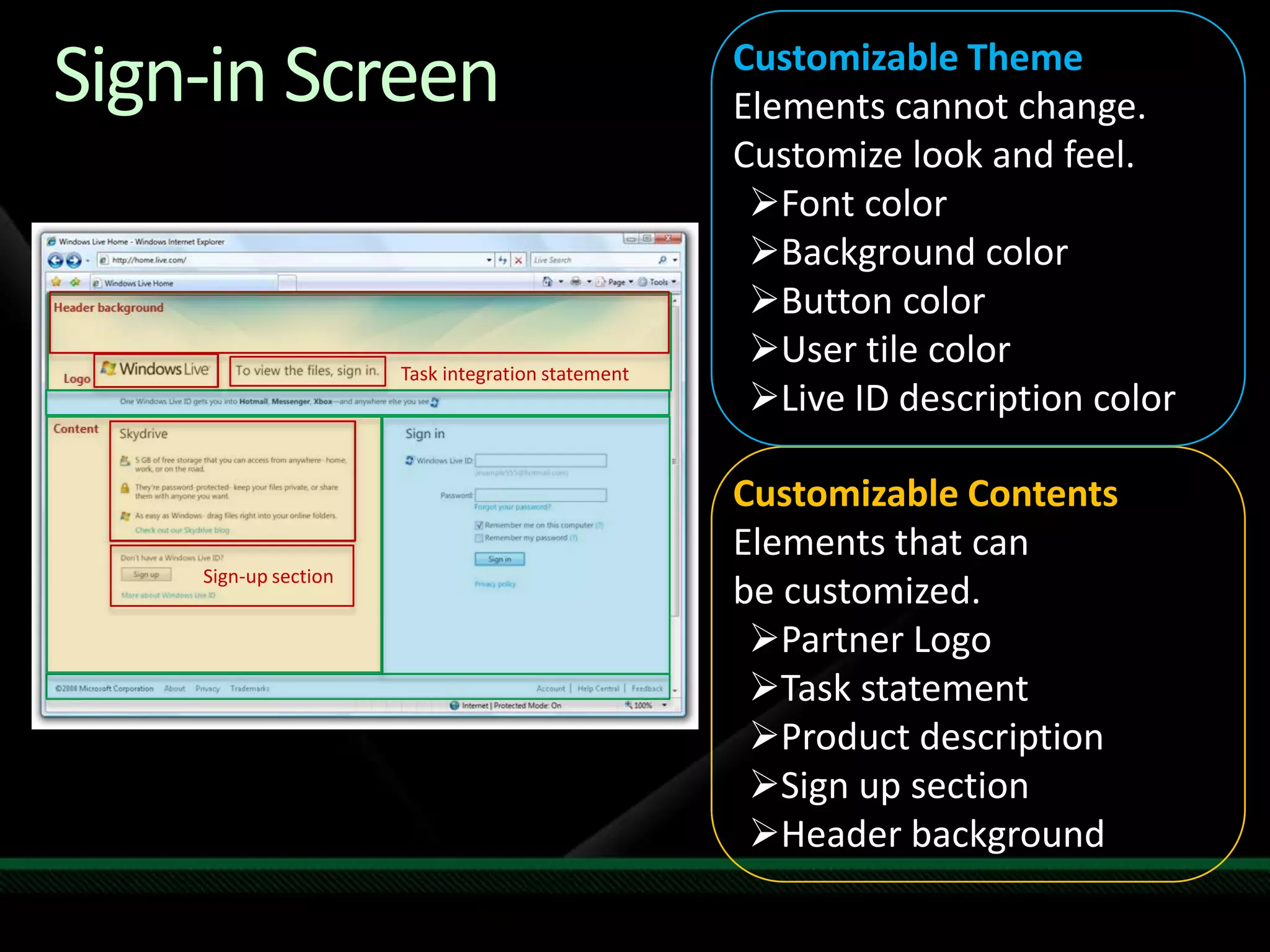
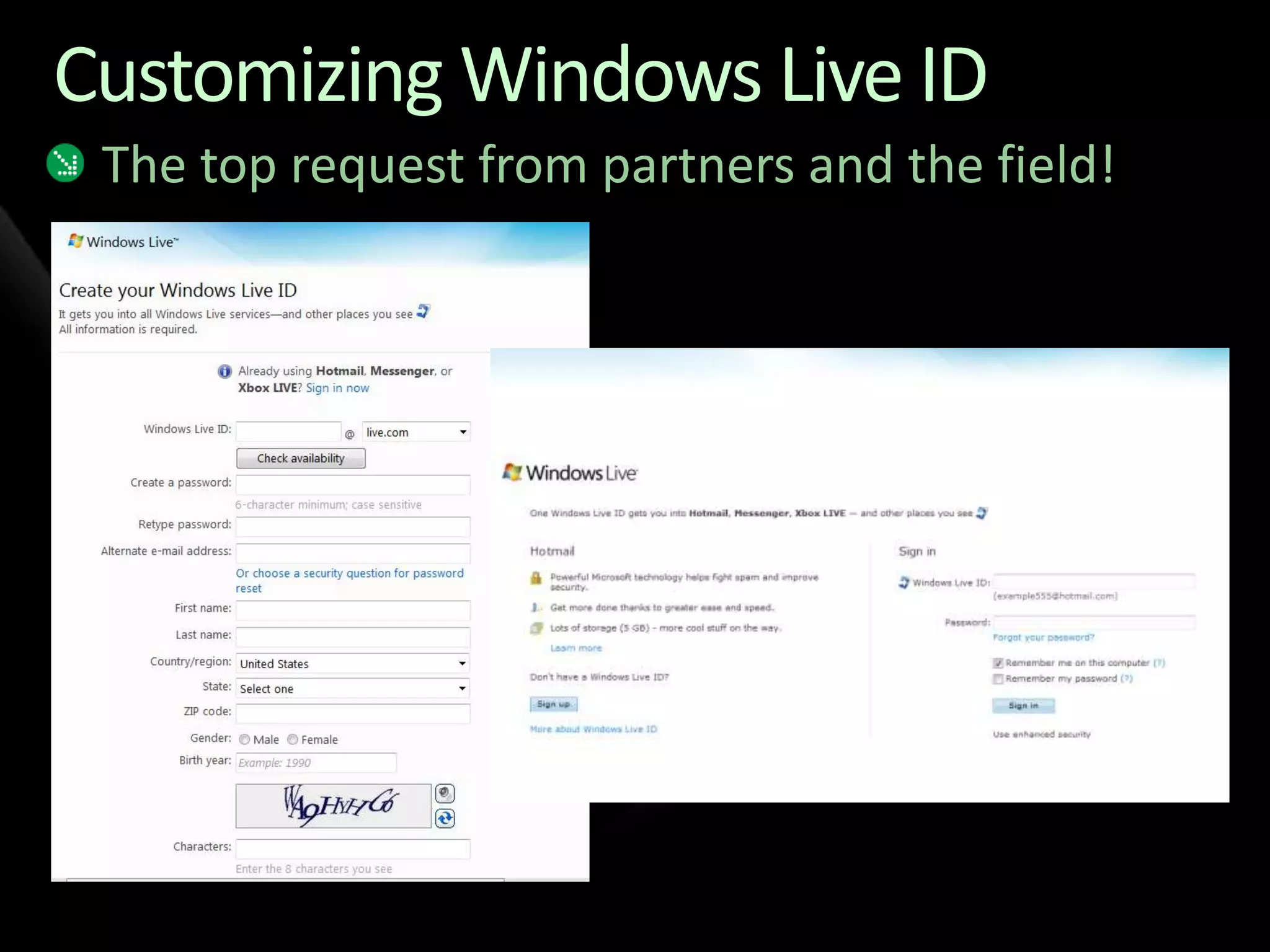
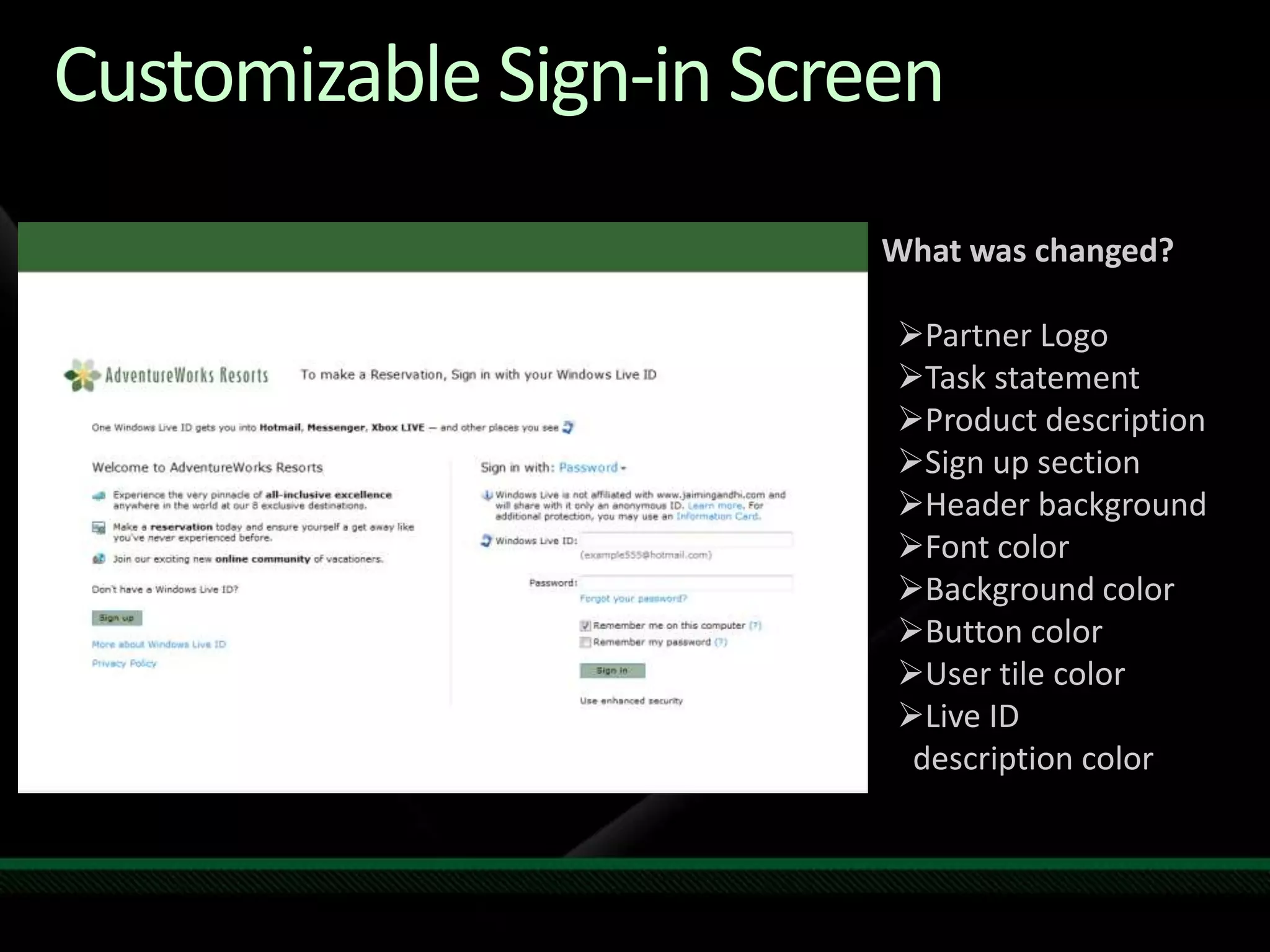
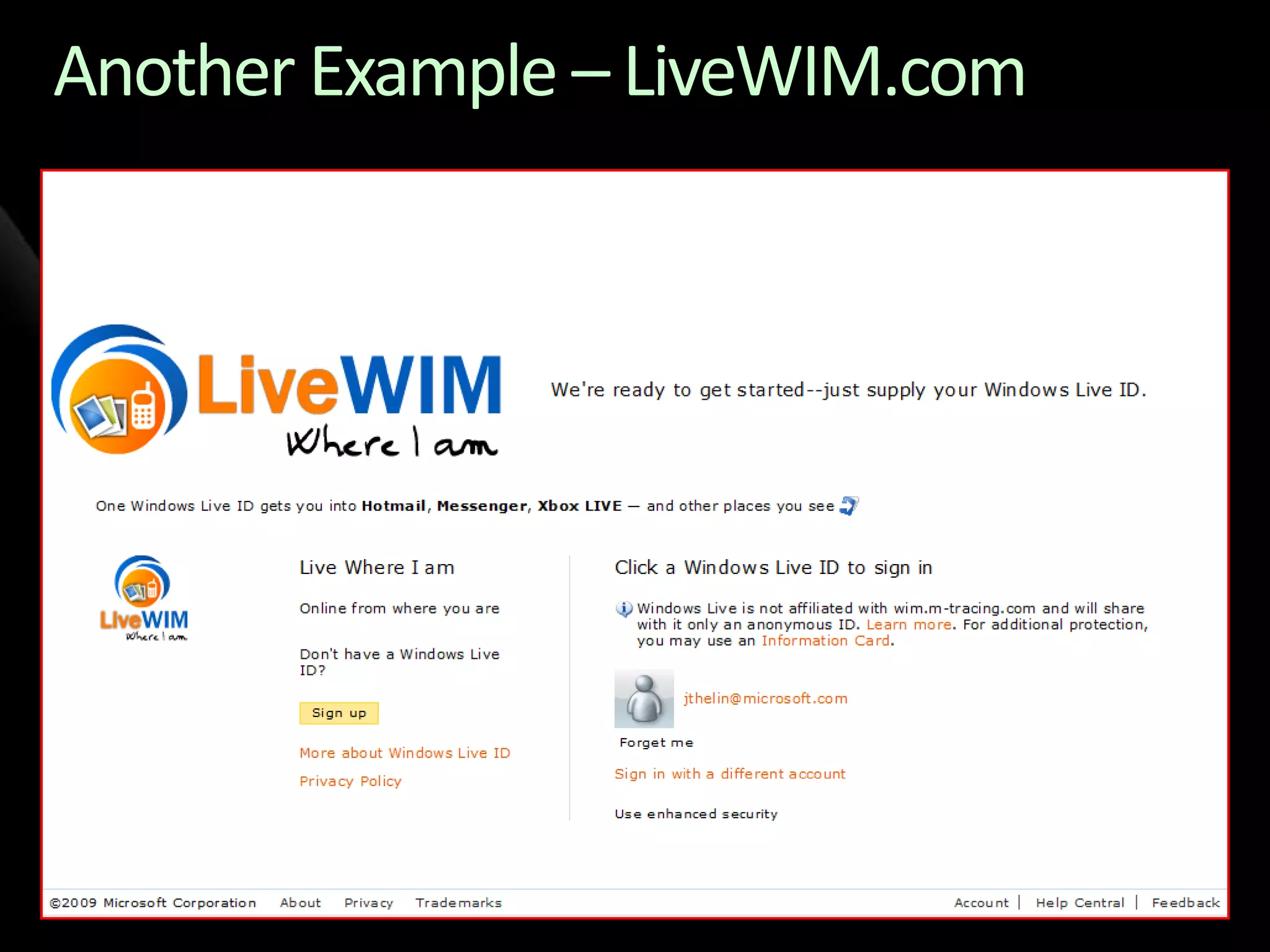
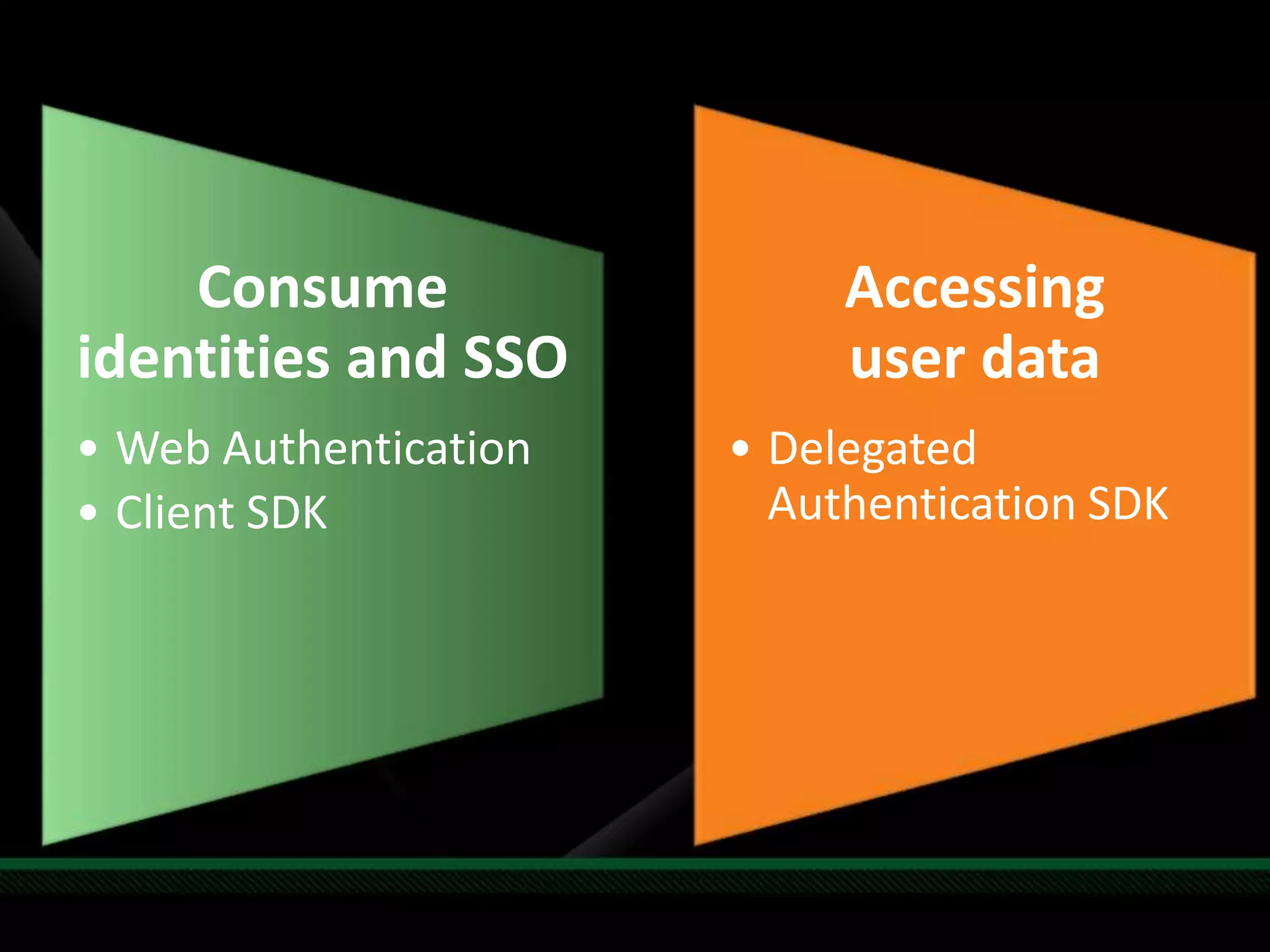
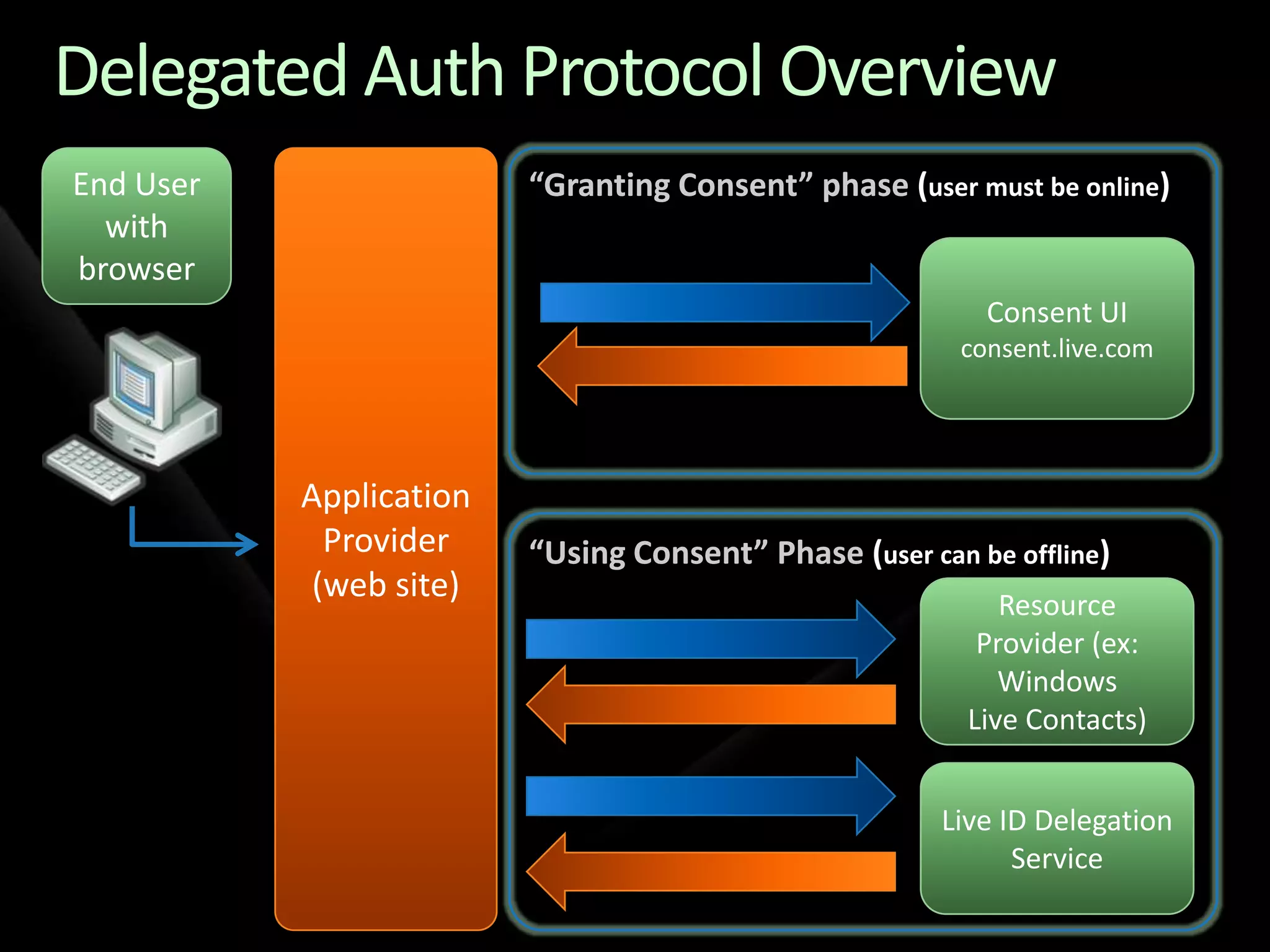
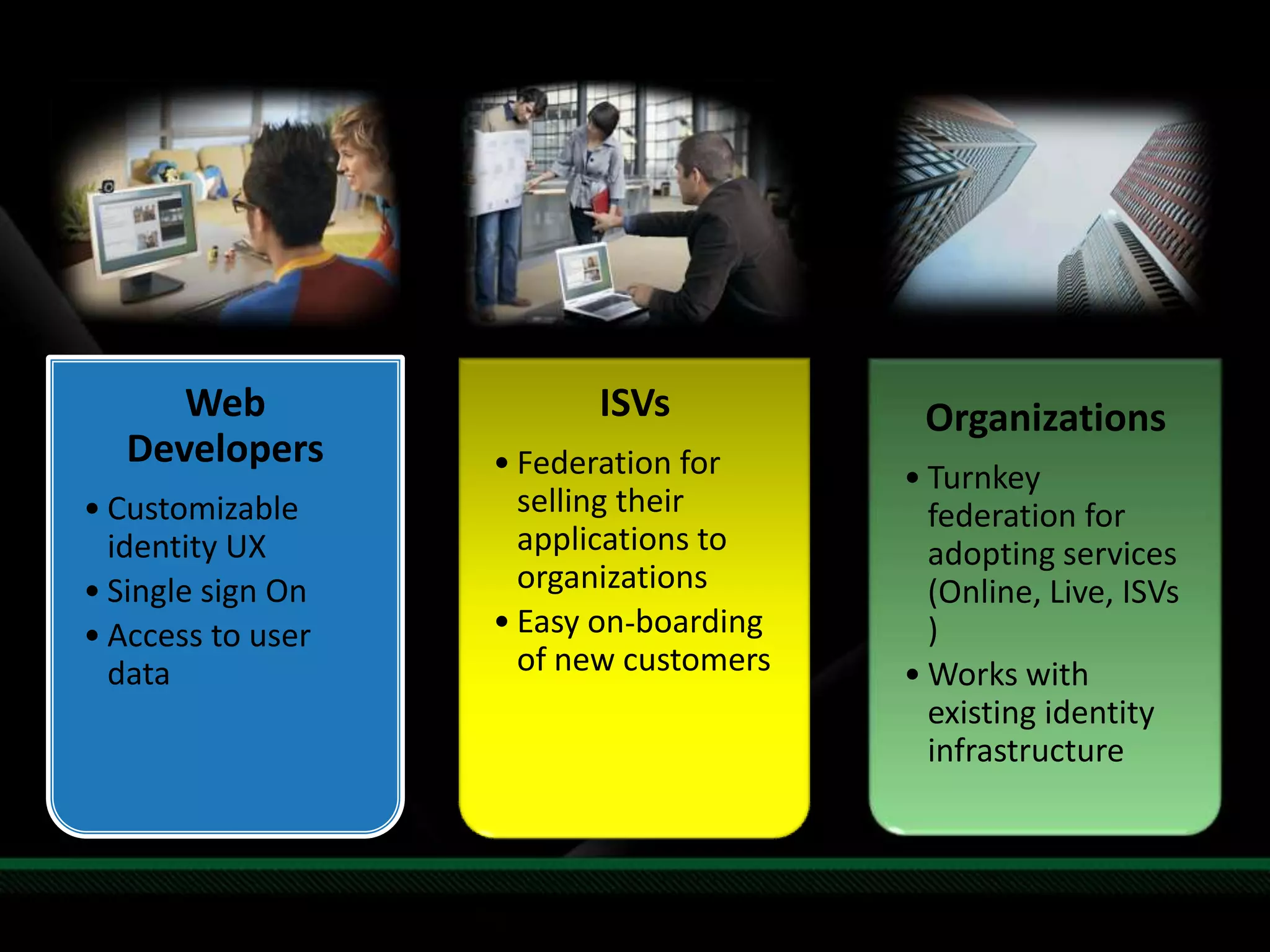
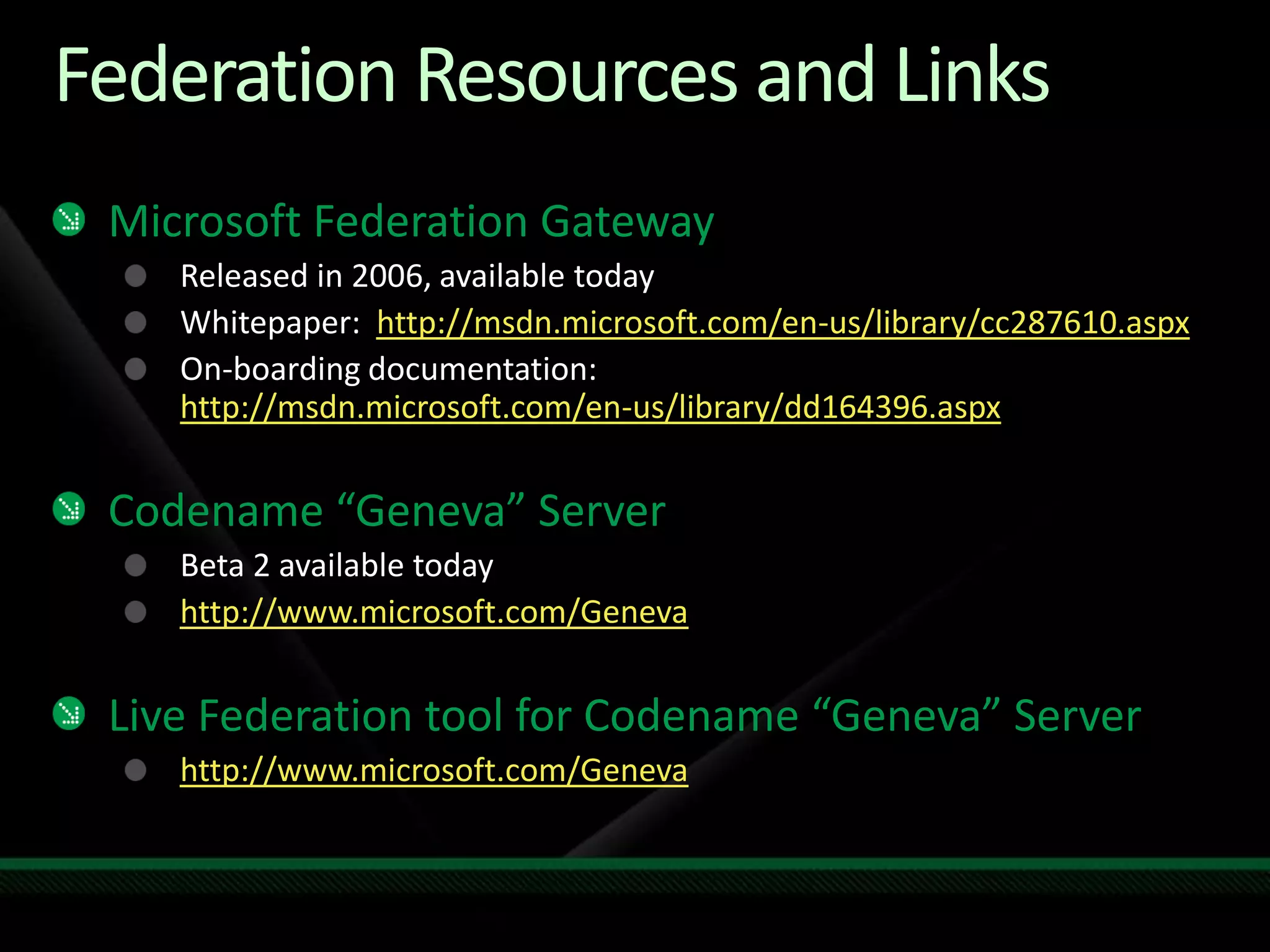
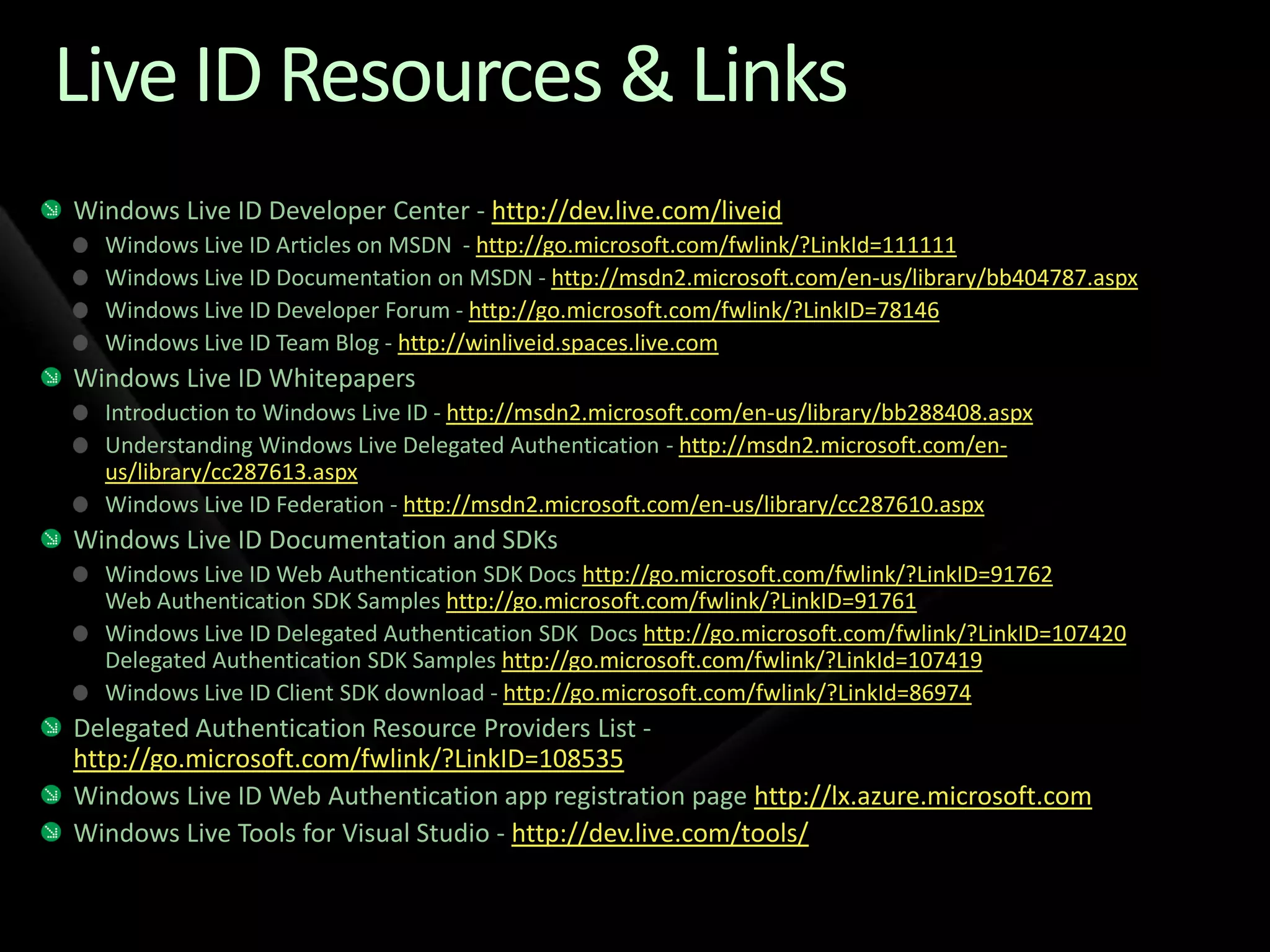
The document details Microsoft's identity services, focusing on the federation for customizable single sign-on (SSO) solutions. It discusses the Microsoft Federation Gateway and the 'Geneva' server, which enable rapid onboarding of organizations and improve access to user data while maintaining security. Additionally, it outlines the benefits of federated identity, including reduced costs and simplified integration for businesses transitioning to cloud services.