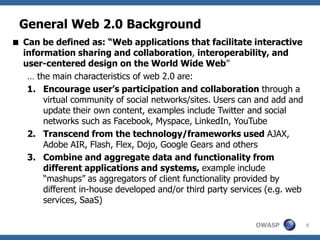
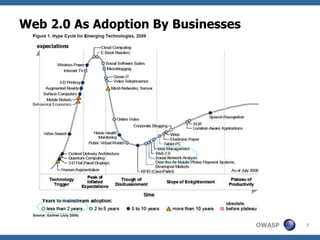
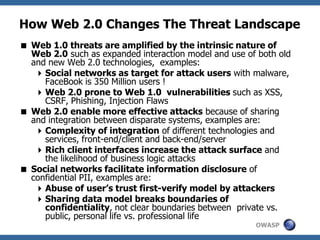
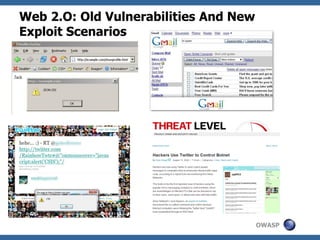
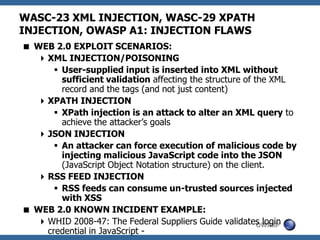
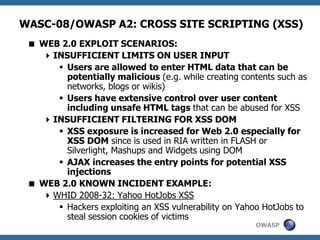
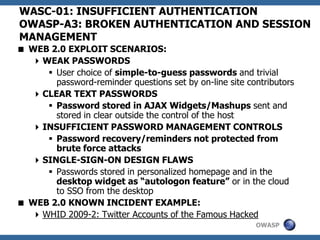
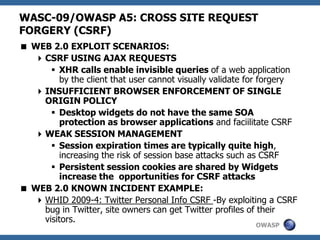
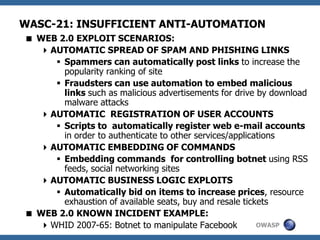
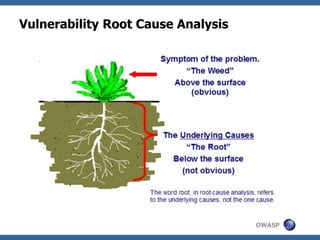
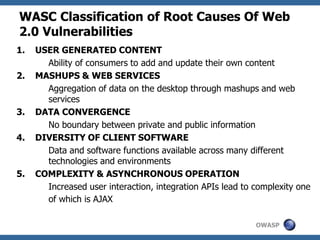
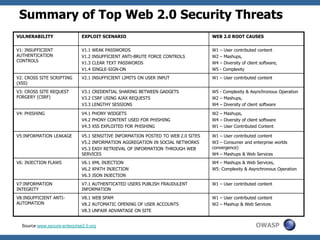
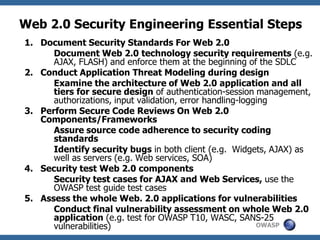
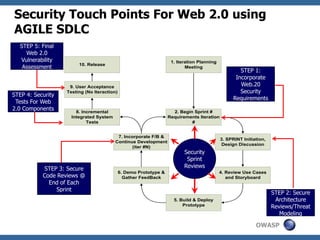
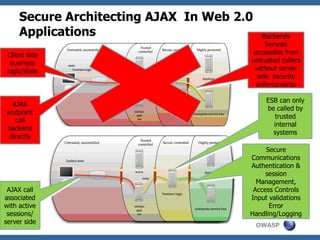
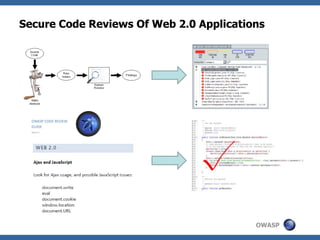
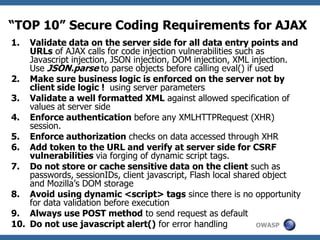
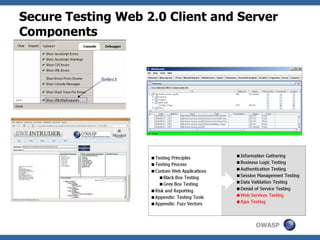
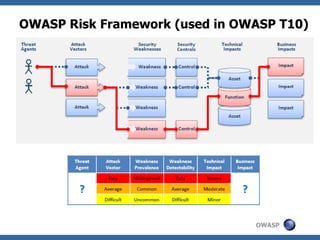
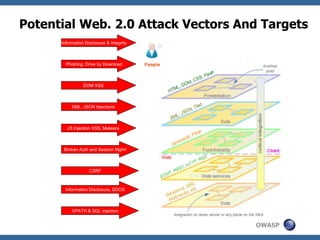
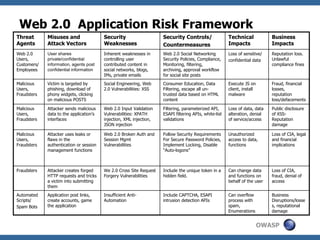
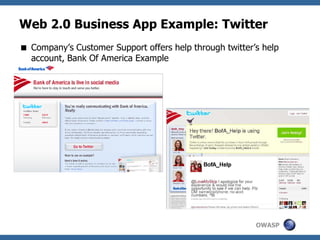
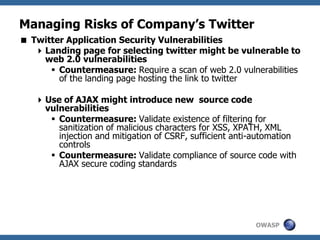
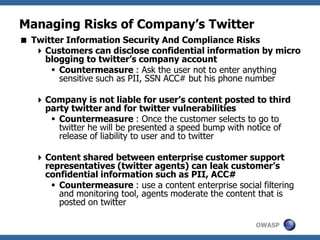
The document discusses security considerations for Web 2.0 applications. It begins with an overview of the evolution of Web 2.0 and its key characteristics that impact security, such as user-generated content and integration of data from different sources. The document then analyzes common Web 2.0 vulnerabilities like XSS, injection flaws, and broken authentication. It provides examples of how these vulnerabilities can be exploited in Web 2.0 and their root causes. Finally, the document outlines steps for building secure Web 2.0 applications, including threat modeling, secure code reviews, testing, and risk management.