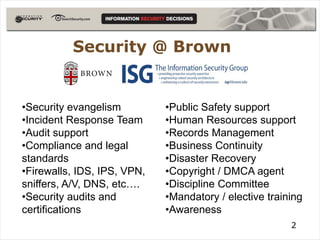
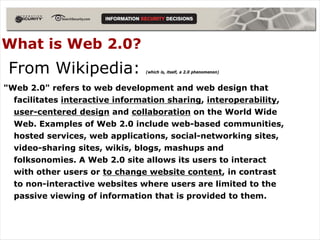
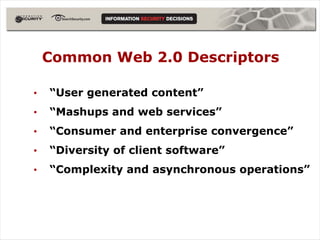
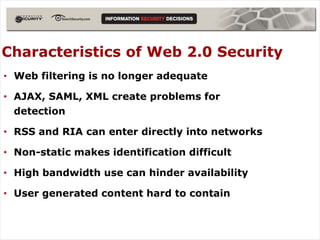
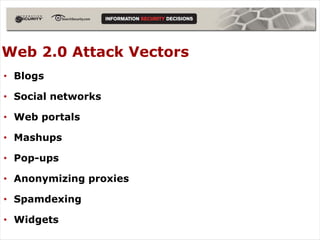
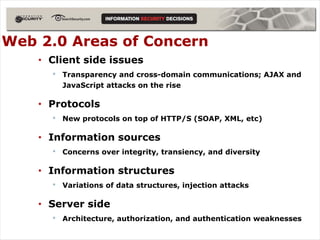
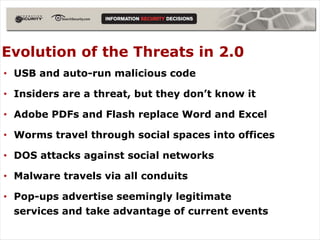
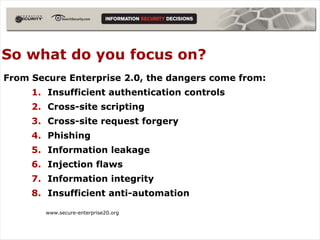
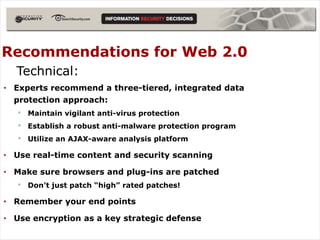
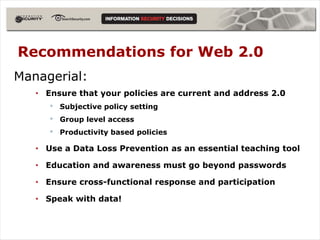
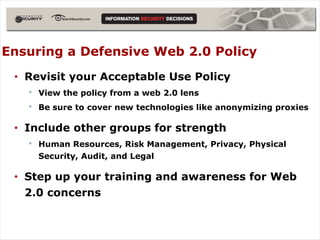
The document discusses the evolving threats posed by Web 2.0 technologies, highlighting security challenges such as identity theft, data leaks, and cross-site scripting. It emphasizes the need for a multi-faceted approach to security that includes both technical and managerial recommendations, advocating for updates to policies and the use of advanced protective measures. The conclusion stresses the importance of a holistic security strategy to address the unique risks associated with interactive web technologies.