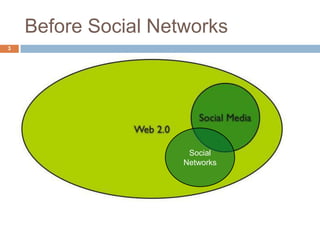
This document discusses security and privacy issues related to social networks. It begins by defining social networks and providing examples. It then outlines common web vulnerabilities like phishing, spam, XSS attacks, and discusses how these risks are increased in social networks due to features like third-party apps, public profiles, and the amount of personal data shared. The document provides tips for securing accounts including using strong unique passwords, checking privacy settings, and being wary of emails or links asking for private information.




















![Information Leakage
24
cont’d
A simple lack of error handling leaking information
http://www.examplesite.com/home.html?day=Mon
dayDrivers(0x80040E14)
I add a little something onto the URL
http://www.examplesite.com/home.html?day=Mon
day AND userscolumn=2
No error handling = information leakage
Microsoft OLE DB Provider for ODBC
Drivers(0x80040E14) [Microsoft][ODBC SQL Server
Driver][SQL Server]Invalid column
name/examplesite/login.asp, line 10](https://image.slidesharecdn.com/socialnetworkssecurityrisks-121014032907-phpapp02/85/Social-networks-security-risks-24-320.jpg)