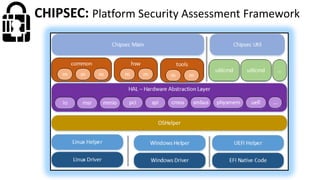
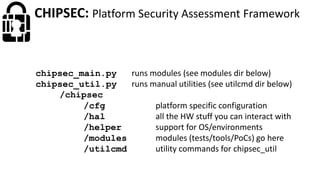
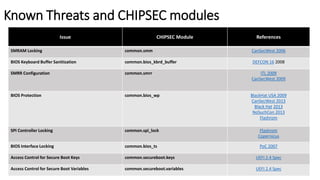
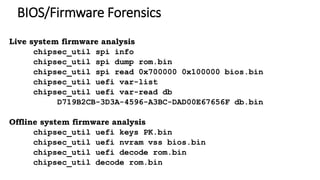
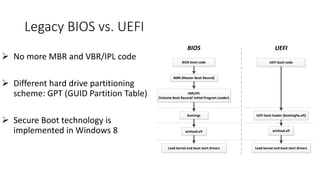
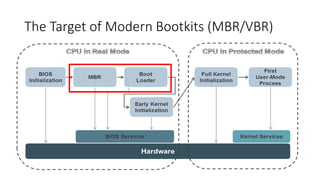
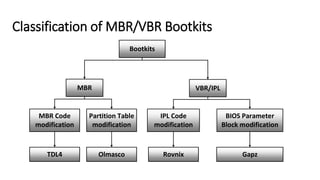
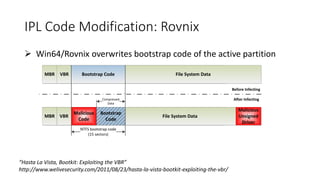
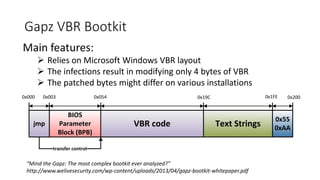
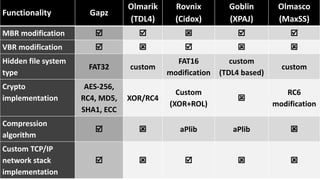
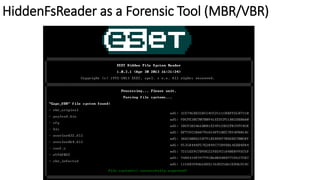
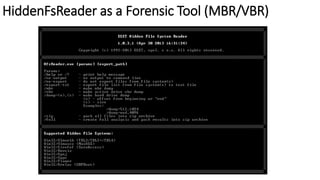
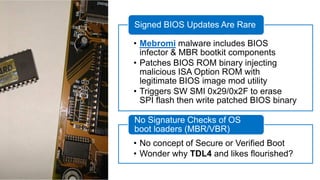
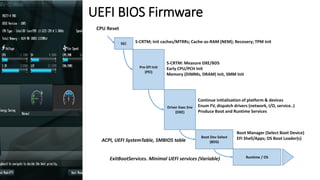
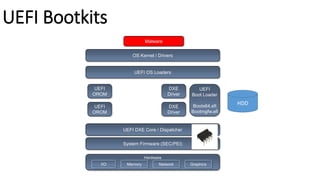
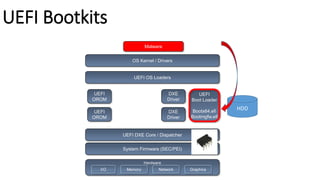
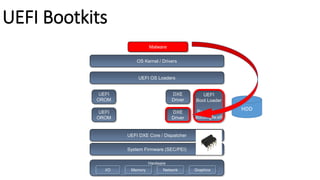
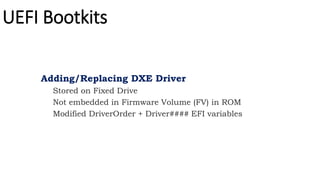
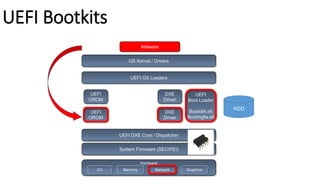
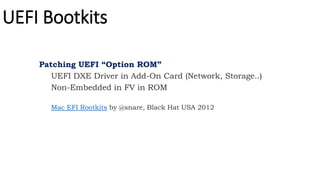
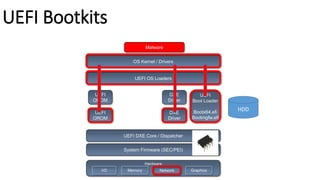
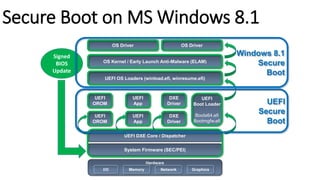
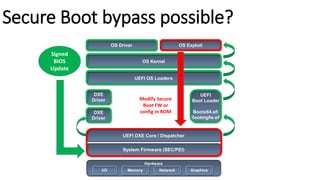
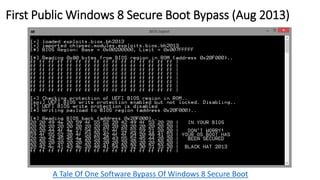
The document discusses the evolution of bootkits, comparing legacy BIOS and UEFI boot environments, and detailing various malwares that exploit these technologies. It highlights bootkit implementation strategies, attacks against secure boot, and forensic tools like hiddenfsreader. Furthermore, it addresses concerns around secure boot and the evolving threat landscape, illustrating techniques used by modern bootkits and the vulnerabilities associated with firmware and BIOS protections.
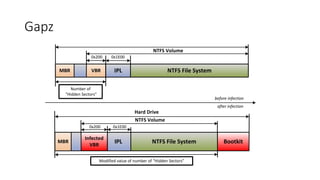
![Gapz BPB Layout
struct BIOS_PARAMETER_BLOCK
{
WORD BytesPerSector;
BYTE SecPerCluster;
WORD ReservedSectors;
BYTE Reserved[5];
BYTE MediaDescriptorID;
WORD Reserved2;
WORD SectorsPerTrack;
WORD NumberOfHeads;
DWORD HiddenSectors;
DWORD Reserved3[2];
LONGLONG TotalSectors;
LONGLONG StartingCluster;
LONGLONG MFTMirrStartingCluster;
DWORD ClustersPerMFTRecord;
DWORD ClustersPerIndexBuffer;
LONGLONG VolumeSerialNumber;
DWORD Reserved4;
};](https://image.slidesharecdn.com/rodionovmatrosovvb2014-160216090454/85/Bootkits-Past-Present-Future-Virus-Bulletin-9-320.jpg)


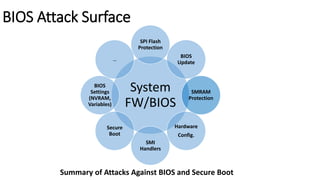

![From Analytics, and Scalability, and UEFI Exploitation by Teddy Reed
Patch attempts to enable BIOS write protection (sets
BIOS_CONTROL[BLE]). Picked up by Subzero](https://image.slidesharecdn.com/rodionovmatrosovvb2014-160216090454/85/Bootkits-Past-Present-Future-Virus-Bulletin-34-320.jpg)