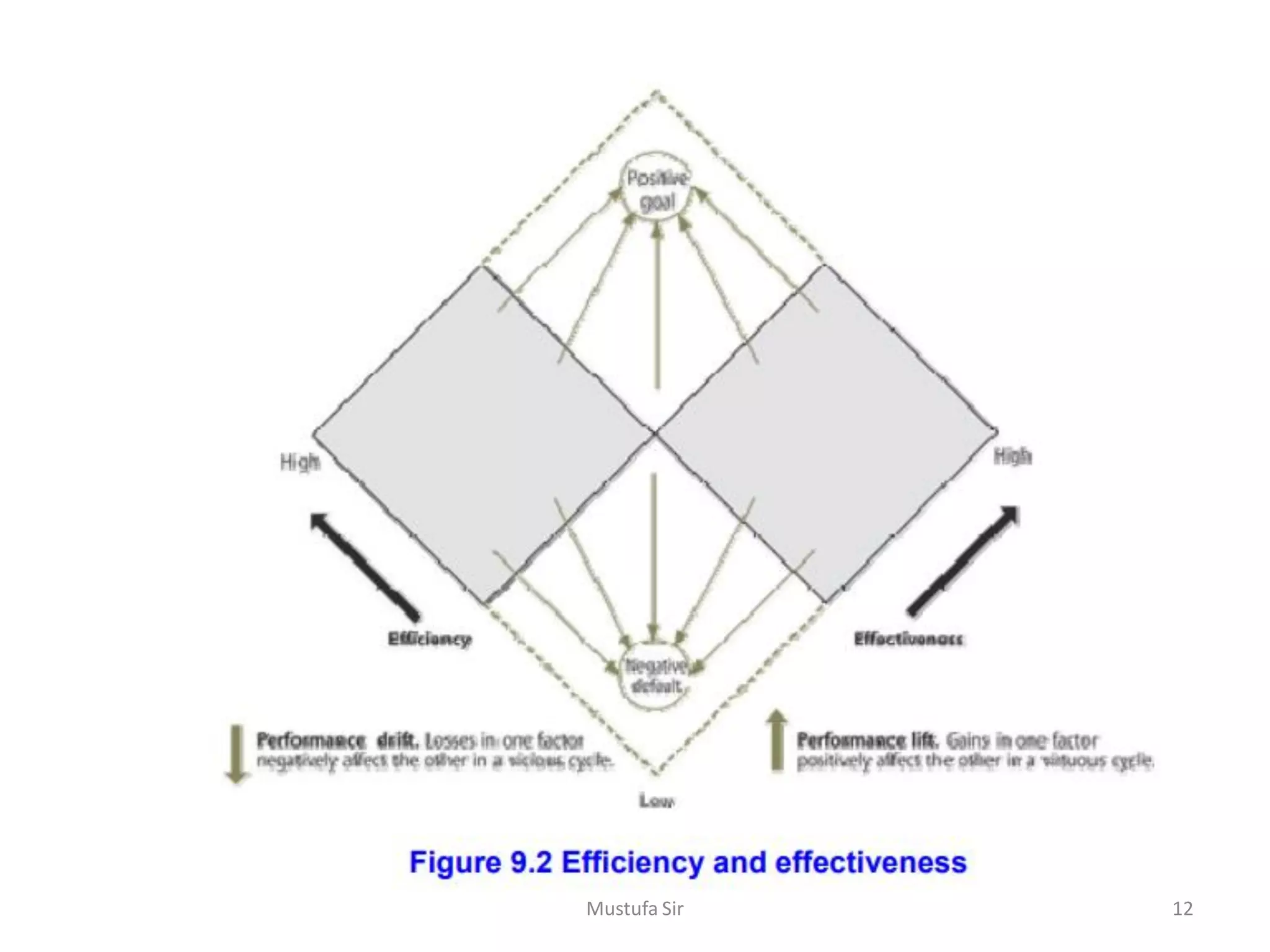
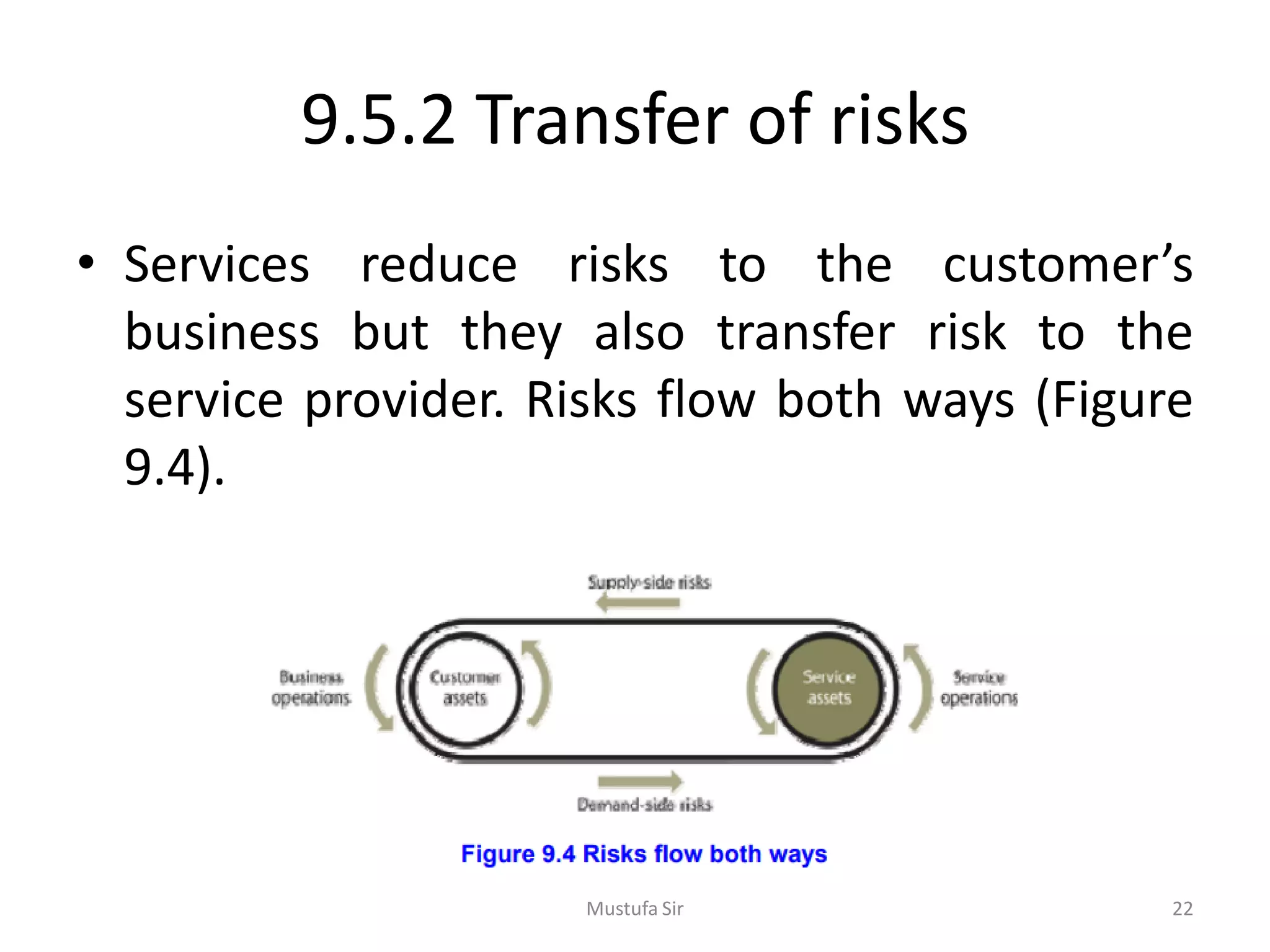
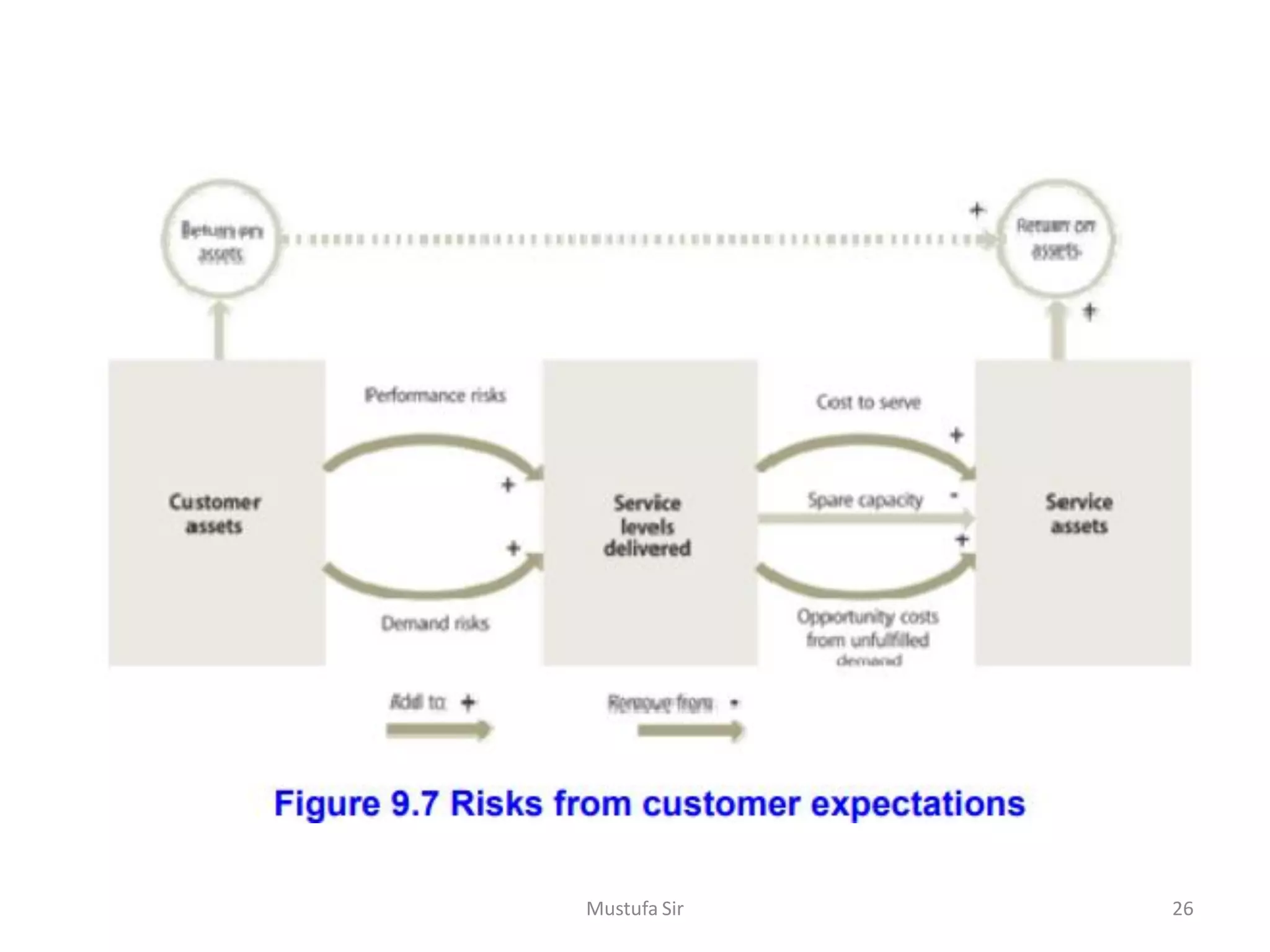
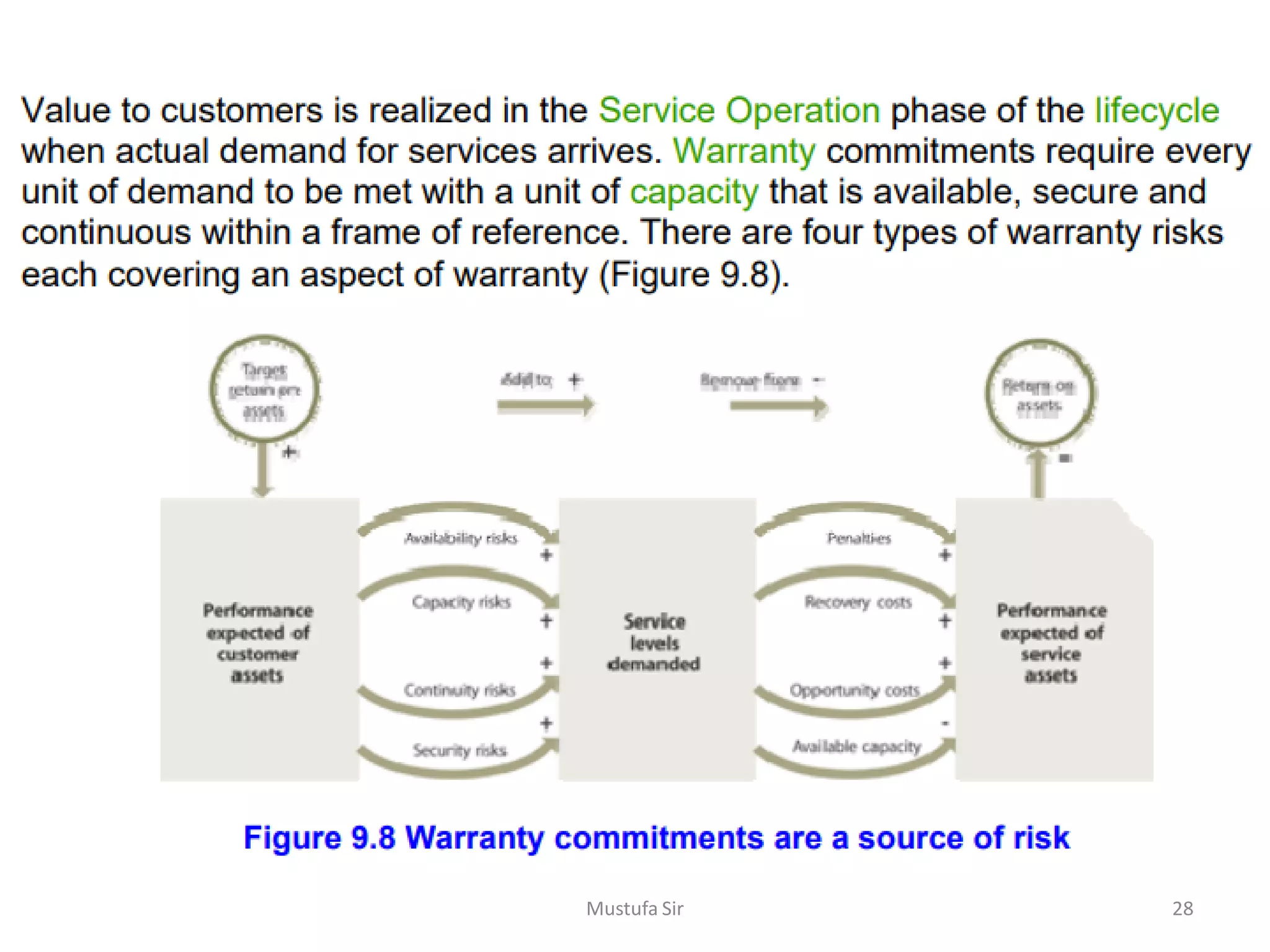
The document discusses the complexity of IT organizations, emphasizing that their interdependent systems require effective coordination and control to manage specialized roles and responsibilities efficiently. It highlights the importance of measuring performance in relation to external customer satisfaction while also addressing various risks associated with service management, including operational and market risks. Ultimately, effective service management can create value for customers while ensuring the service provider's viability through strategic differentiation and consolidation.