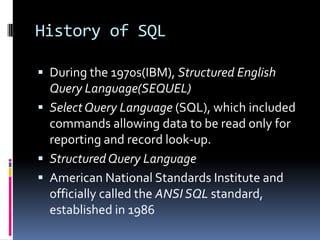
This document provides an overview of SQL programming. It covers the history of SQL and SQL Server, SQL fundamentals including database design principles like normalization, and key SQL statements like SELECT, JOIN, UNION and stored procedures. It also discusses database objects, transactions, and SQL Server architecture concepts like connections. The document is intended as a training guide, walking through concepts and providing examples to explain SQL programming techniques.



















































![SELECTSELECT select_list (describes the columns of the result set.)[ INTO new_table_name ] (specifies that the result set is used to create a new table)FROM table_list (Contains a list of the tables from which the result set data is retrieved)[ WHERE search_conditions ] (filter that defines the conditions each row in the source tables must meet)[ GROUP BY group_by_list ] (partitions the result set into groups based on the values)[ HAVING search_conditions ] (an additional filter that is applied to the result set)[ ORDER BY order_list [ ASC | DESC ] ] (defines the order in which the rows in the result set are sorted)](https://image.slidesharecdn.com/t-sql-090709172122-phpapp01/85/T-SQL-Overview-53-320.jpg)












![UNIONSELECT zip FROMhotel.customerWHERE zip > '90000‘UNION [ALL]SELECT zip FROMhotel.hotelWHERE zip > '90000‘ Creates one table with rows from both SELECTs Suppresses duplicate rows](https://image.slidesharecdn.com/t-sql-090709172122-phpapp01/85/T-SQL-Overview-66-320.jpg)















![Views - StoredCREATEVIEW[Current Product List] ASSELECTProductID,ProductNameFROM ProductsWHERE Discontinued=No A view does not store data If you do insert, update, delete on a view the data values in the underlying tables will be updated This is not possible on all views Computed columns cannot be updated Not permitted on aggregate views or views with set operators Join views may or may not be updateable](https://image.slidesharecdn.com/t-sql-090709172122-phpapp01/85/T-SQL-Overview-82-320.jpg)


