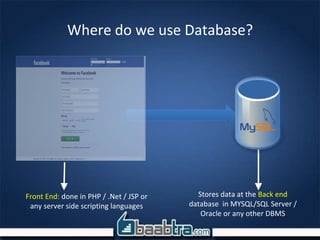
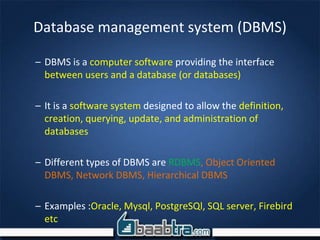
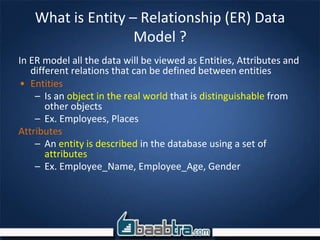
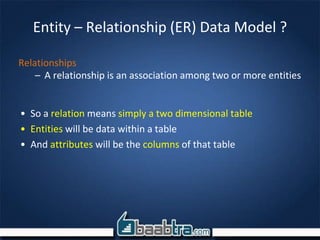
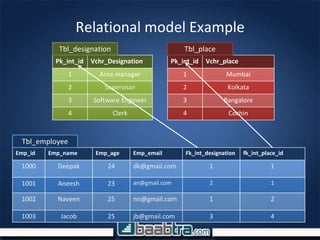
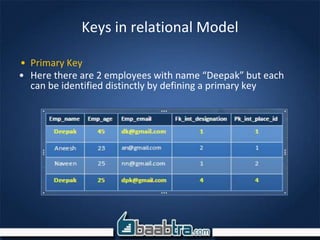
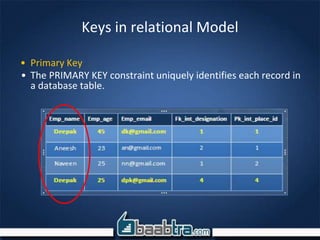
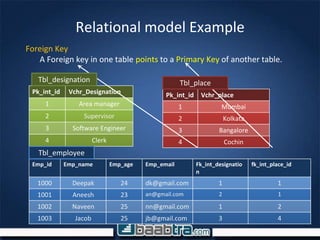
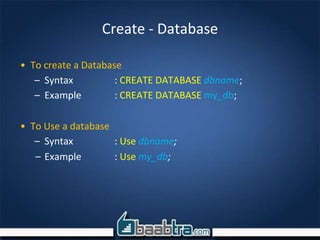
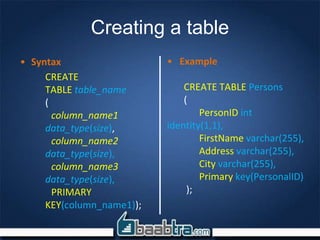
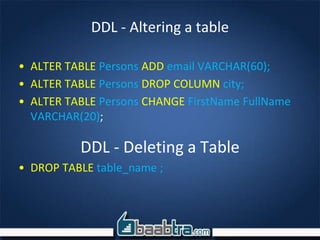
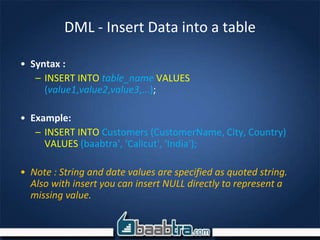
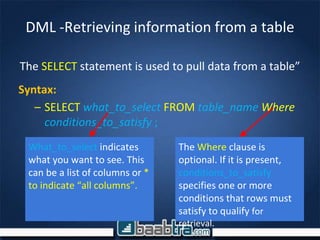
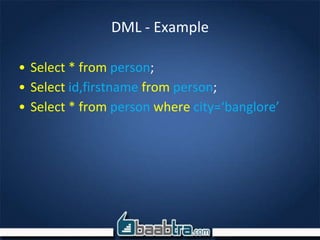
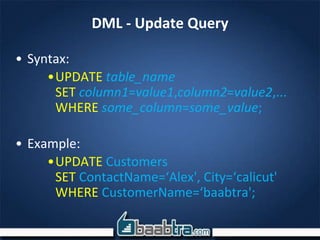
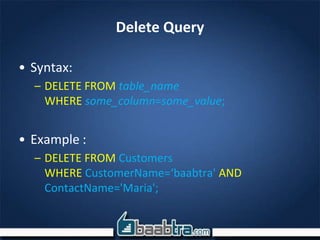
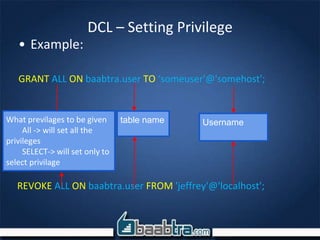
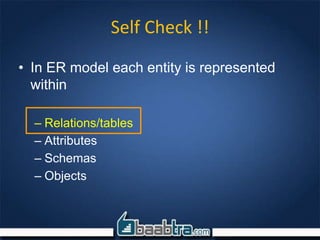
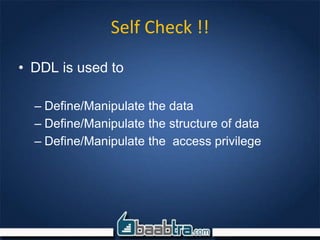
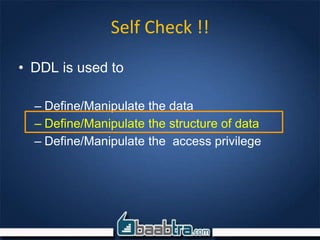
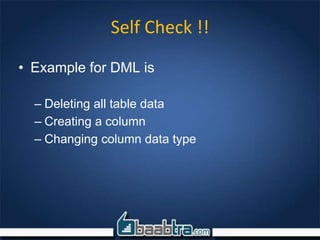
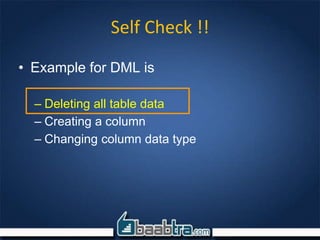
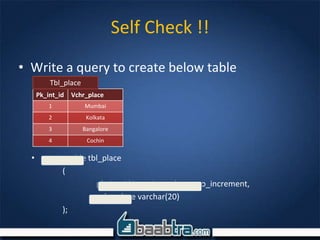
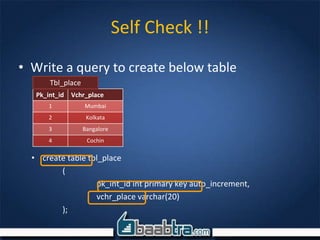
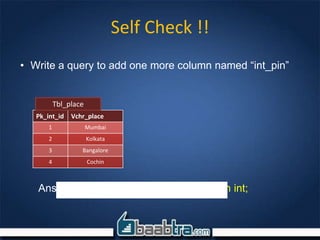
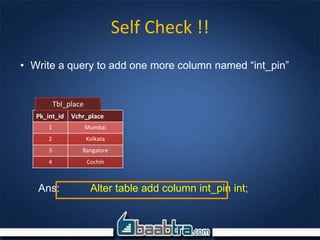
This document provides an introduction to database management systems (DBMS) and SQL Server. It discusses what a database is and where databases are used. It then explains what a DBMS is and some examples of DBMS software. The document goes on to describe the relational database model including entities, attributes, relationships and keys. It also discusses the entity-relationship model. Finally, it covers SQL statements including DDL, DML, and DCL and provides examples of commands for creating tables, inserting and updating data, and setting privileges.