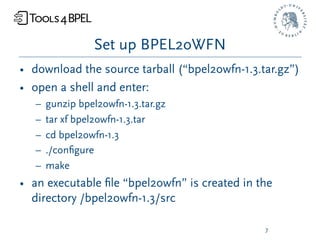
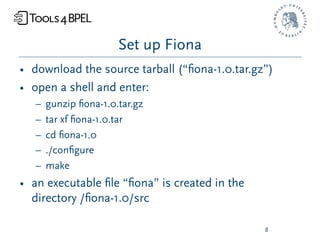
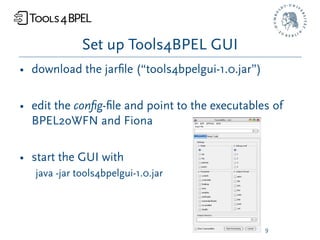
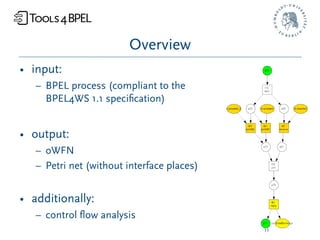
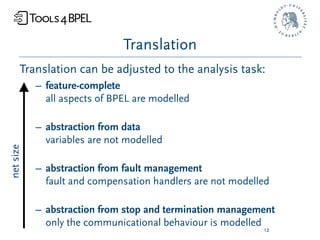
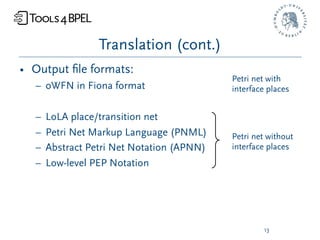
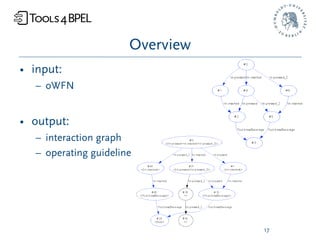
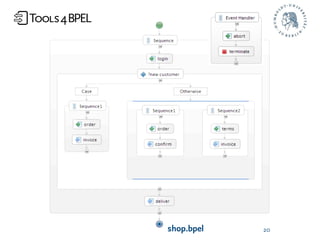
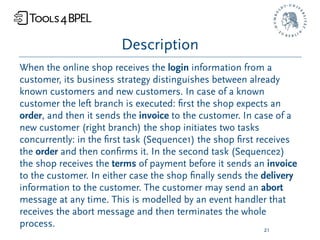
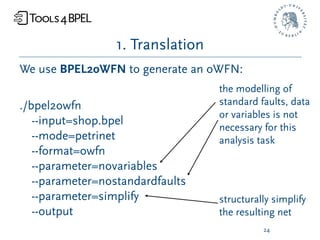
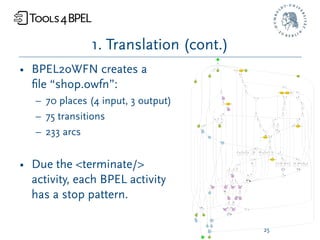
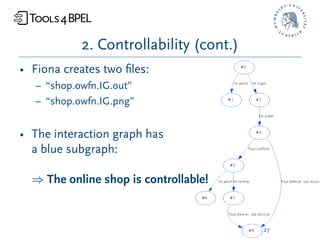
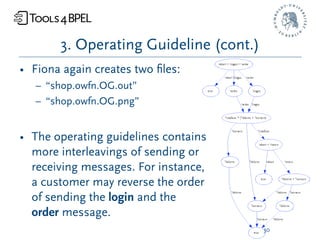
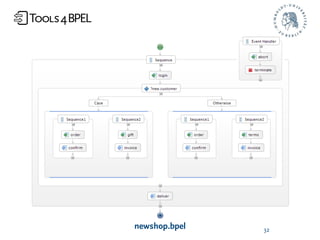
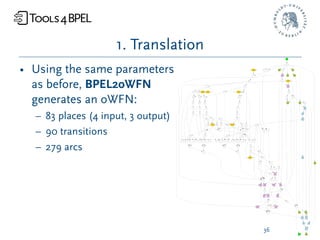
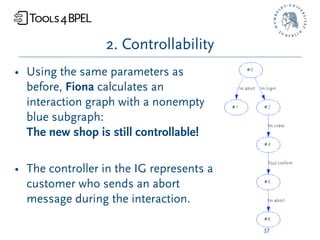
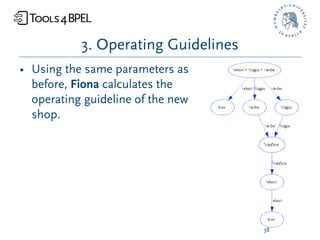
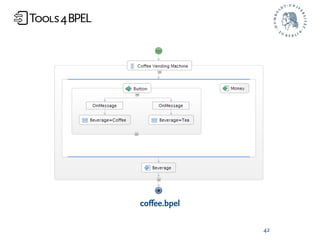
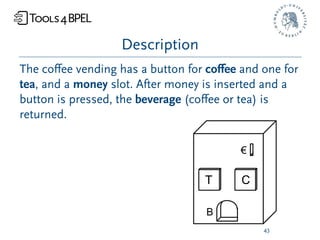
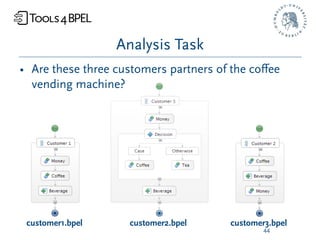
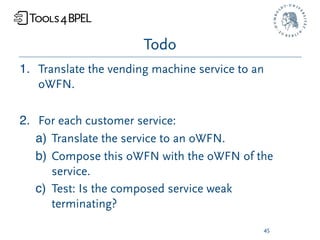
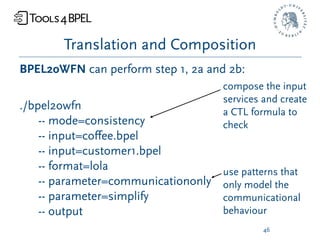
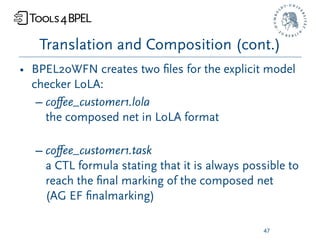
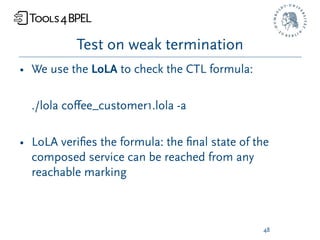
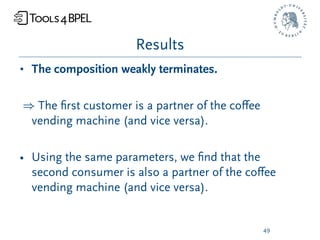
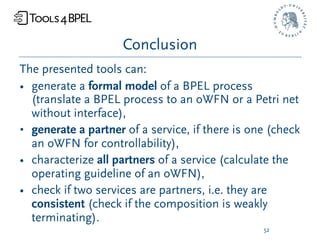
The document provides an overview of the tools4bpel tutorial, detailing the functionalities of tools such as bpel2owfn and fiona, which translate BPEL services into OWFN and analyze their interactions. It outlines the setup process, requirements, and provides examples of how to employ these tools for analyzing BPEL processes, controlling flow, and characterizing service partners. Additionally, it includes instructions for running examples and references for further information.