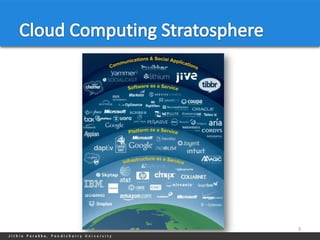
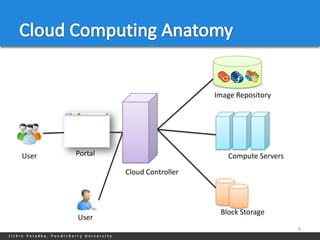
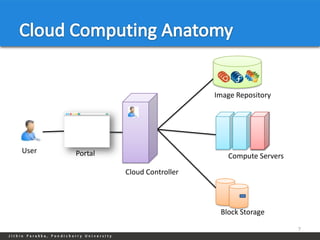
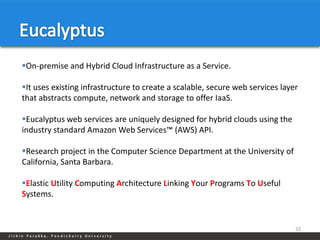
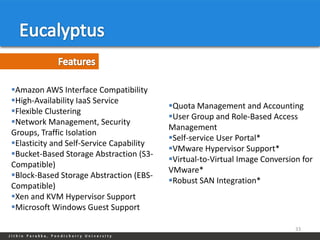
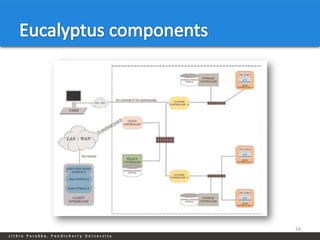
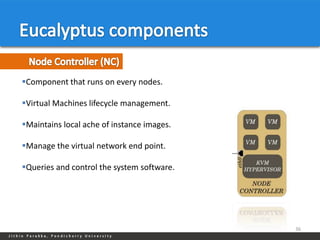
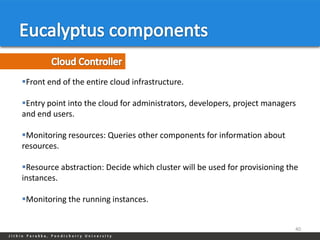
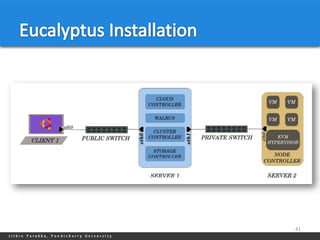
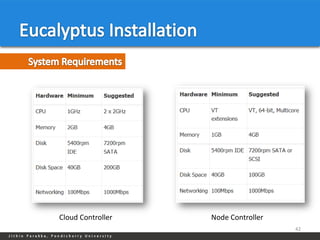
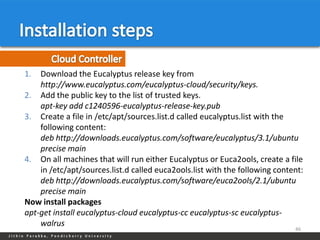
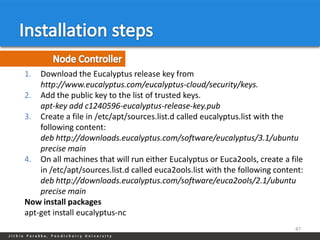
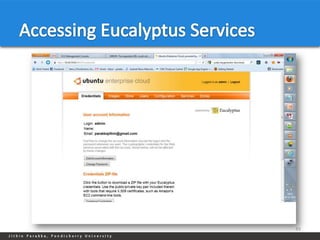
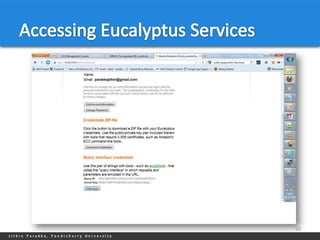
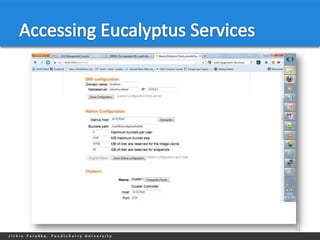
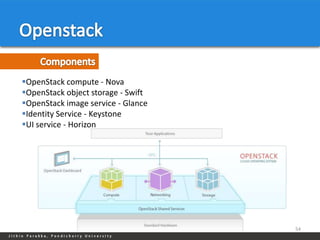
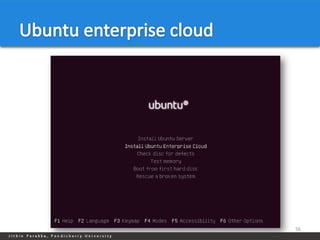
The document discusses cloud middleware and various cloud platforms. It provides details about Eucalyptus, OpenStack, Ubuntu Enterprise Cloud, Amazon EC2, Google App Engine, and their components. Eucalyptus is an open-source software for building private and hybrid clouds. It implements Amazon Web Services APIs and interfaces. OpenStack is an open-source cloud platform consisting of modules like Nova, Swift, Glance, Keystone and Horizon. Ubuntu Enterprise Cloud is a commercial version of Eucalyptus that provides tools for managing infrastructure and users. Amazon EC2 and Google App Engine are commercial cloud platforms that allow deploying and scaling web applications.