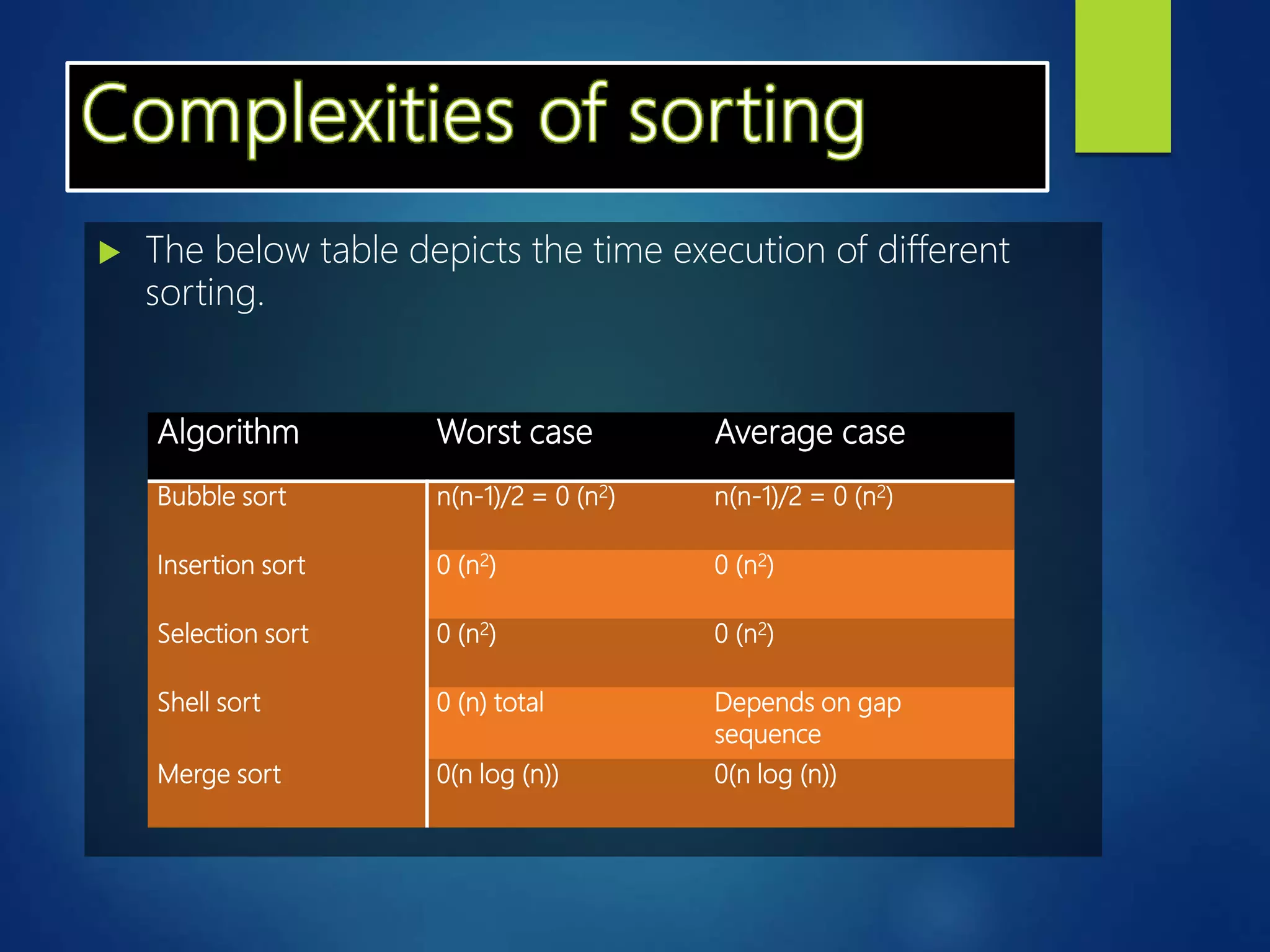
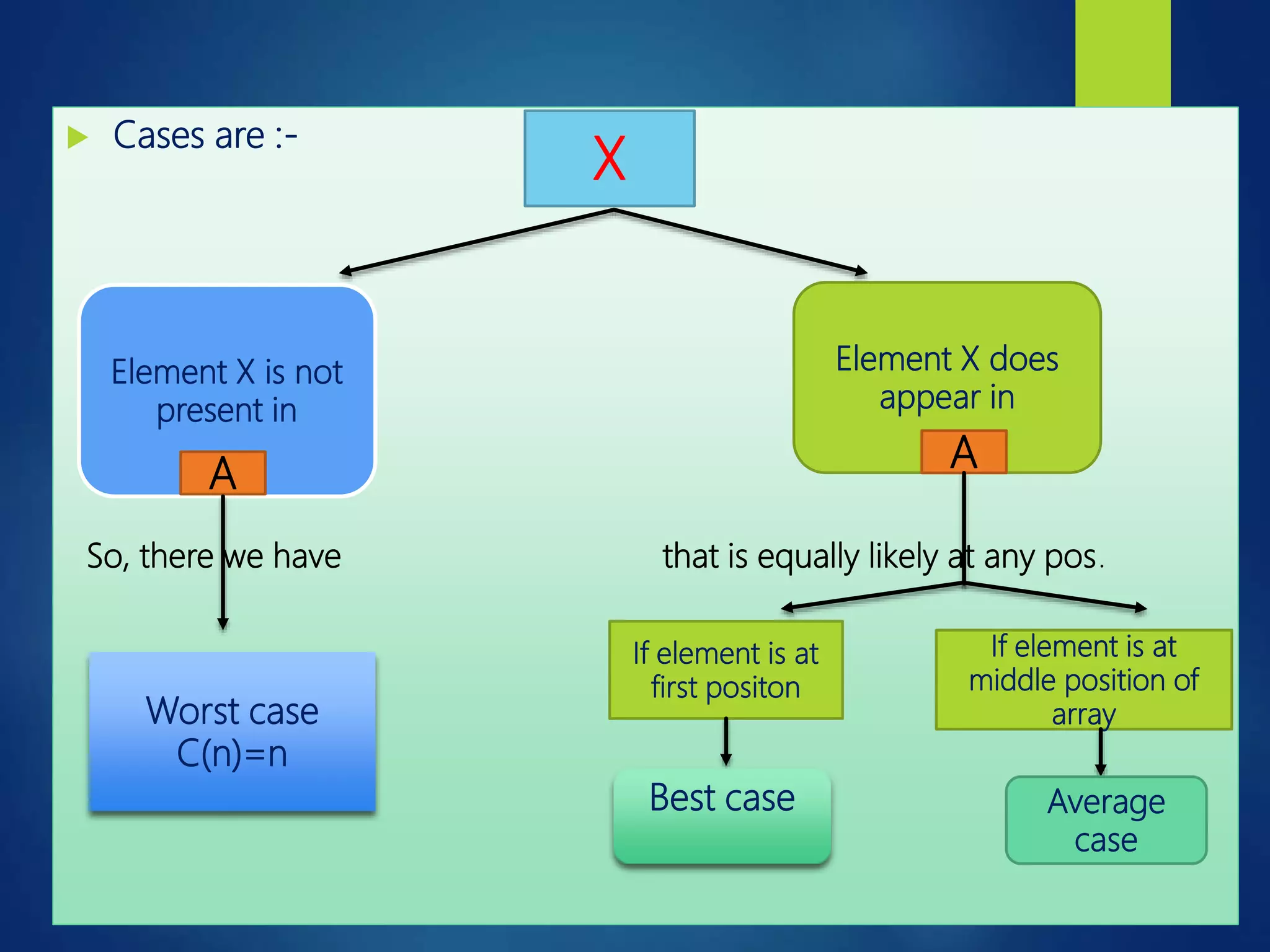
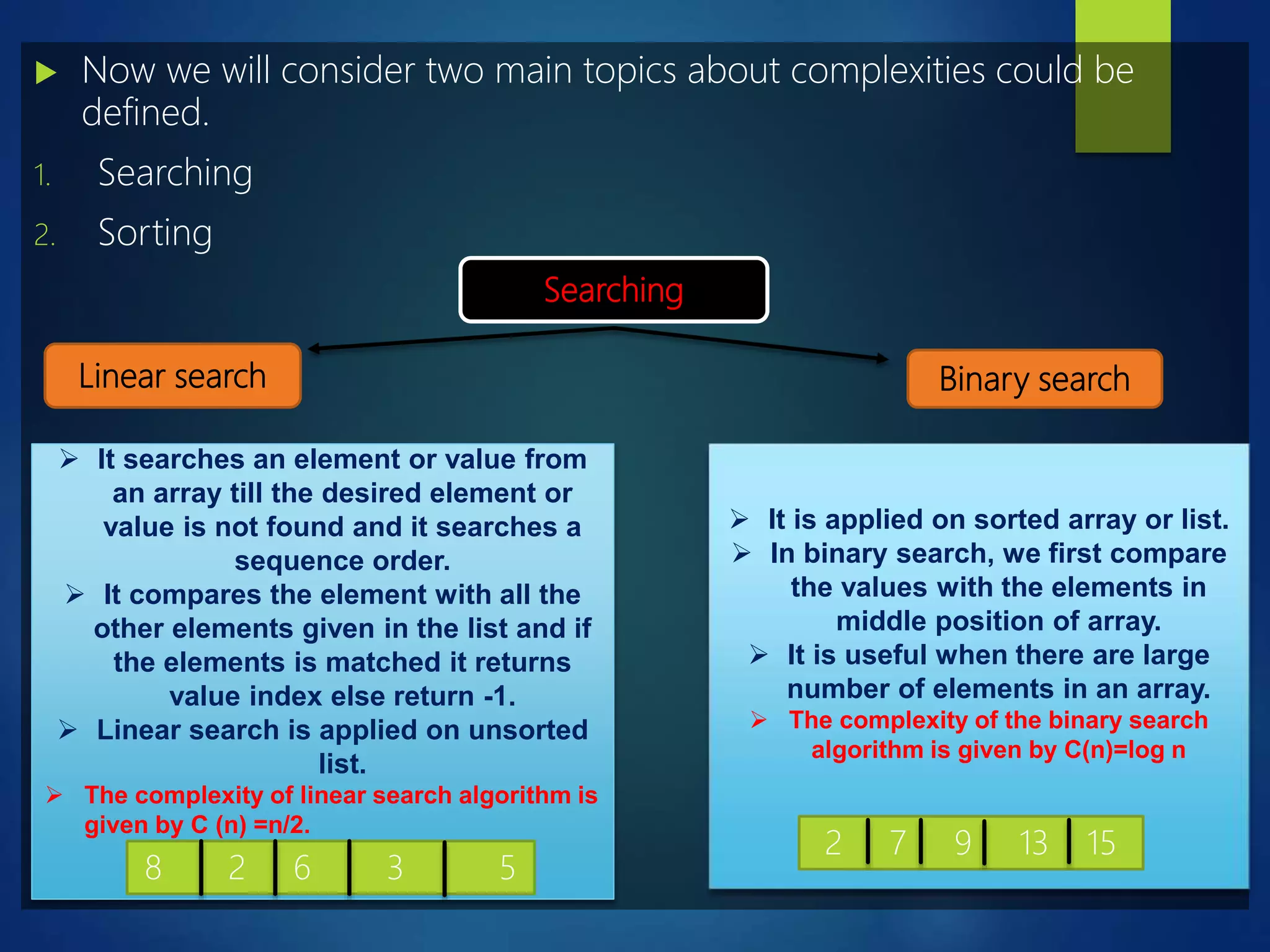
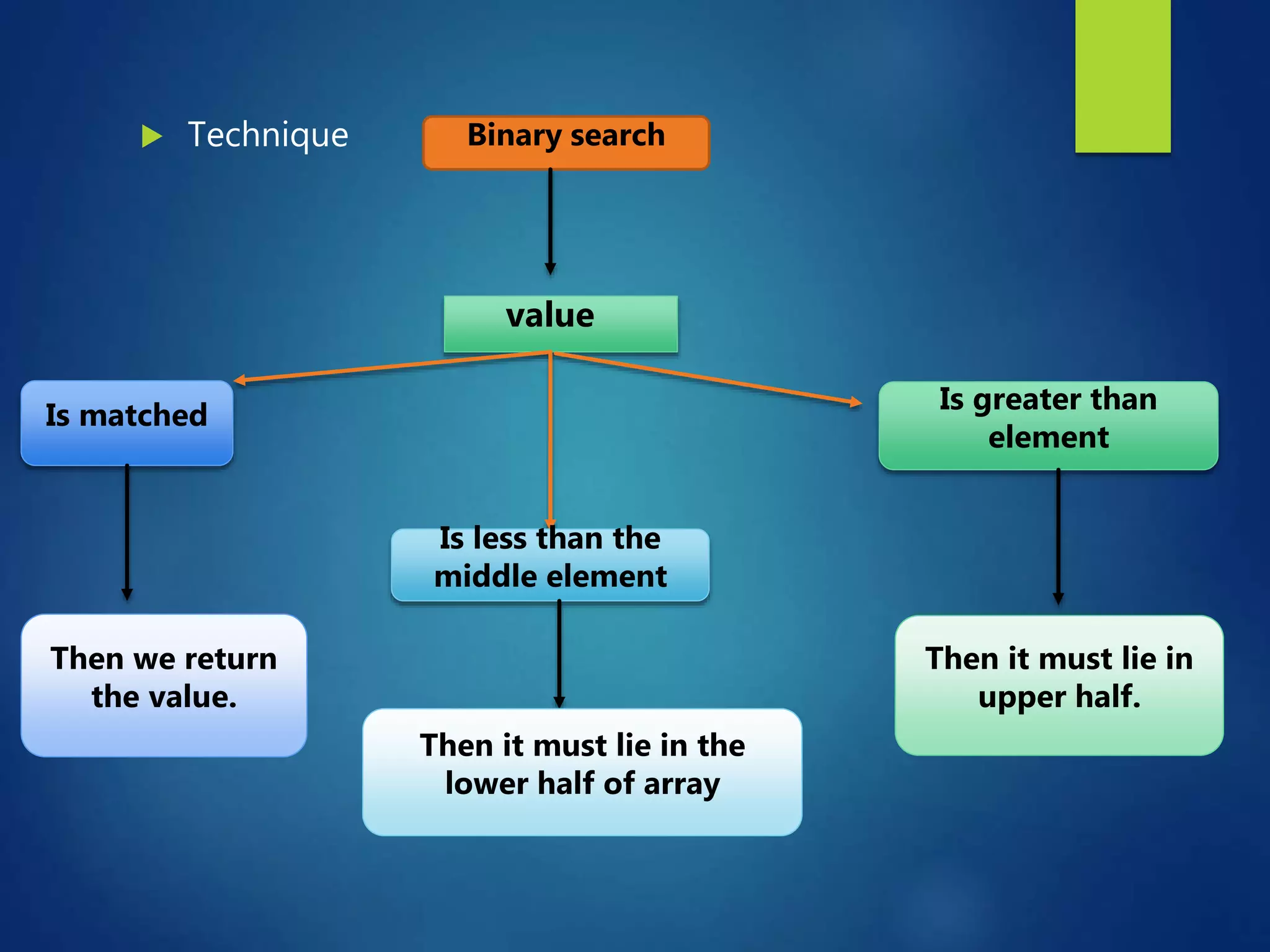
The document discusses the concept of time complexity in algorithms, emphasizing its importance in evaluating the efficiency of algorithms based on input size. It explains various notations used to express complexity, such as Big O, Big Omega, and Big Theta, alongside the significance of average, best, and worst-case scenarios. It also outlines common sorting and searching algorithms and their time complexities, highlighting that the choice of an algorithm often involves trade-offs between time and space efficiency.
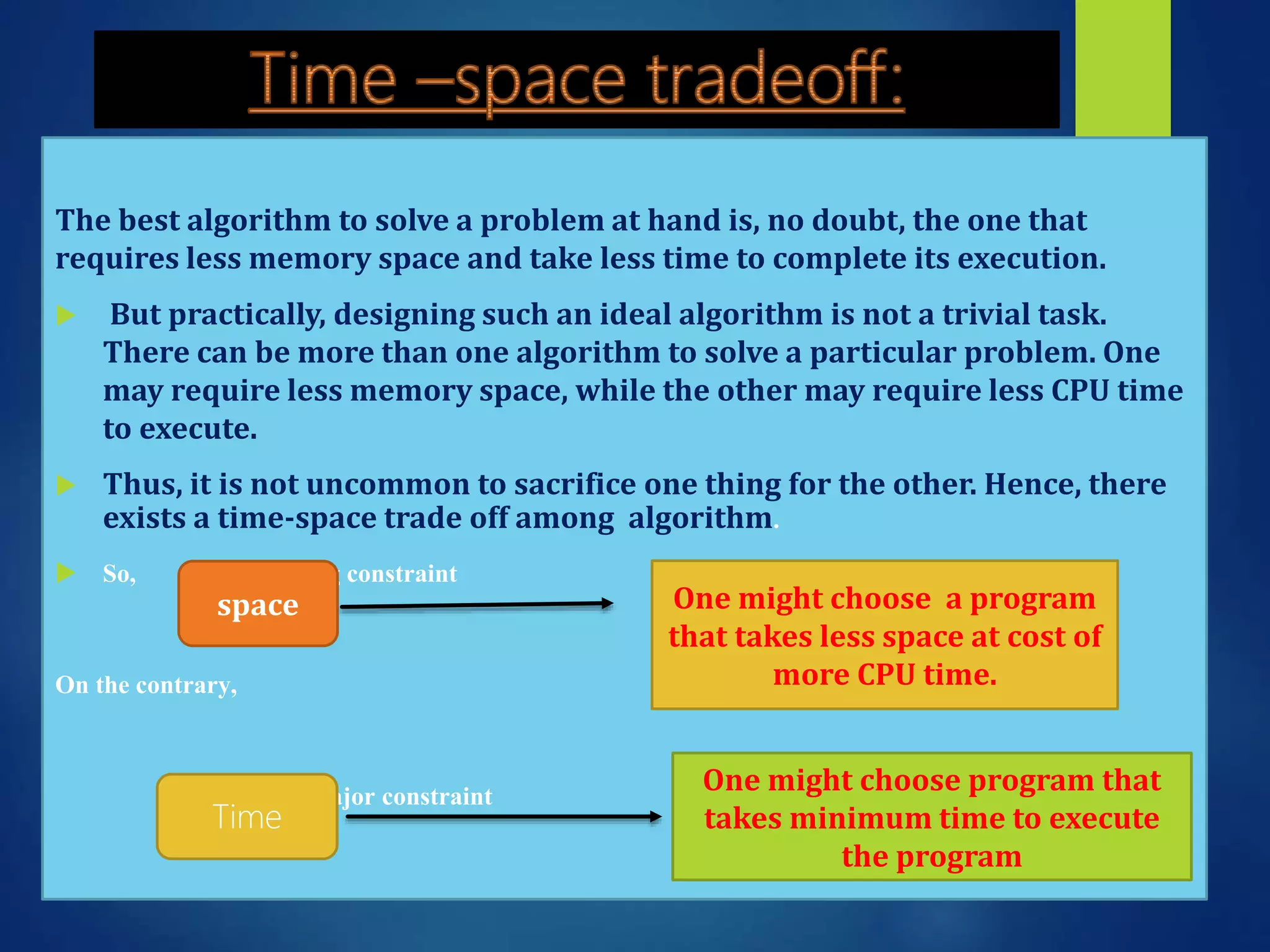
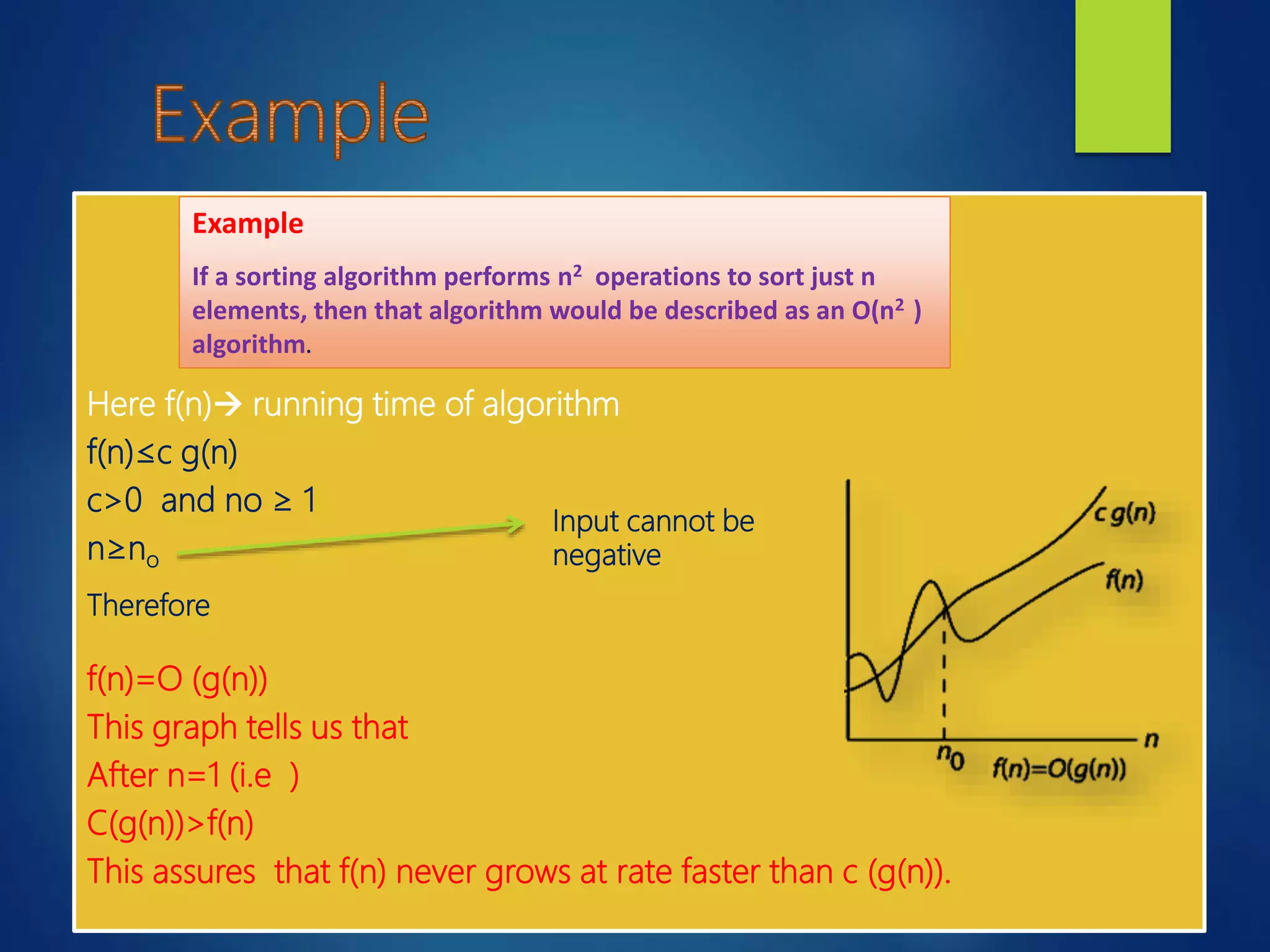
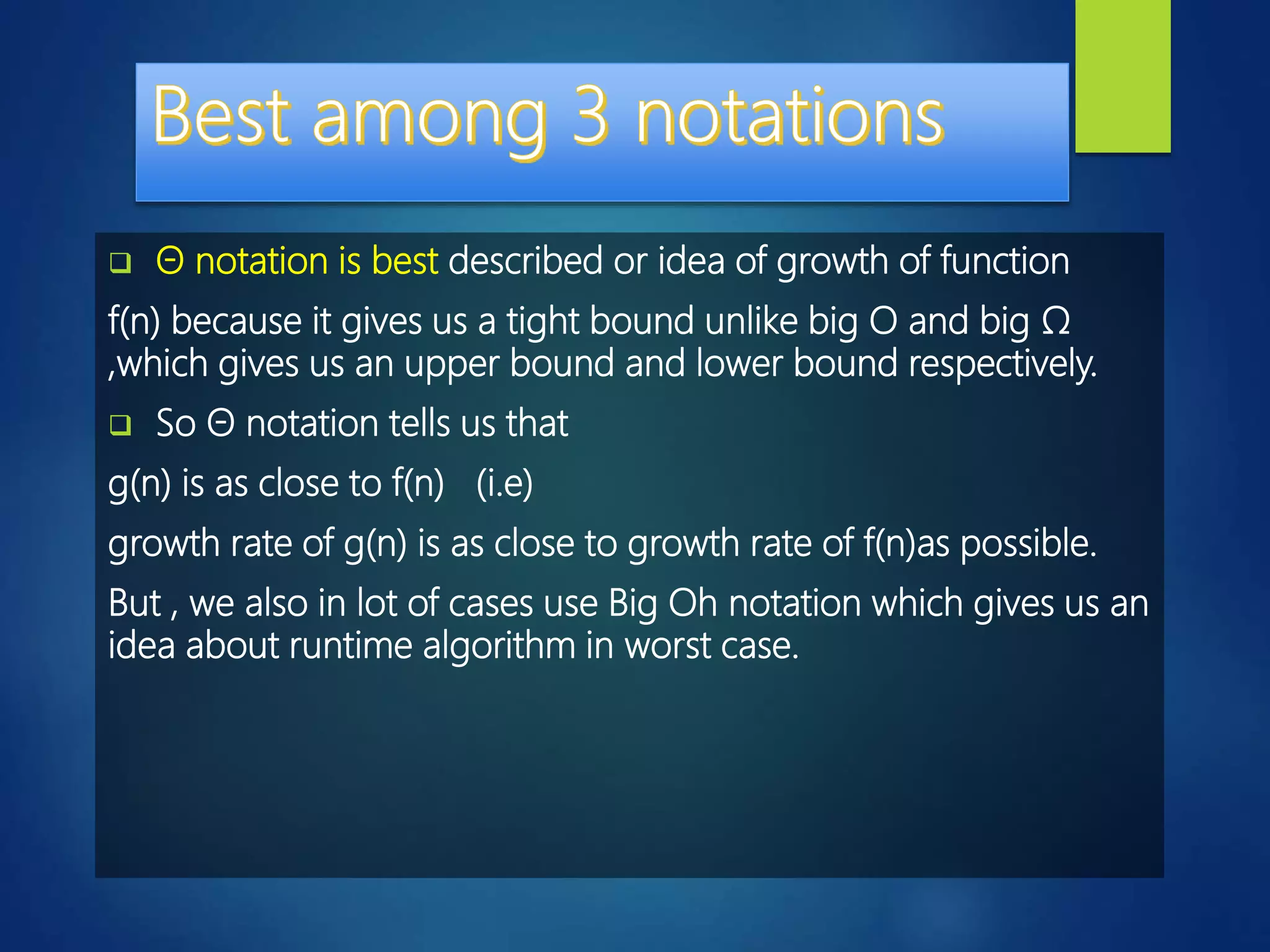
![Example
sum of two number
Sum (a , b)
{ return a + b;
}
If time taken is a T sum
here T sum = 2 units
Therefore we can say that time
taken by program is always
constant.
Sum of all elements in list
Sumoflist (int A, n)
1. { total=0;
2. for i= 0 to n-1
3. { total = total + A[i];
}
4. return total;
}
T sum of list = 1+2(n+1)+2n+1
= 4n+4
also T(n)= C n + C’
1unit1unit
Cost No of time
2
1
2
1
1
n+1
n
1](https://image.slidesharecdn.com/ntccppt-170702003841/75/TIME-EXECUTION-OF-DIFFERENT-SORTED-ALGORITHMS-9-2048.jpg)
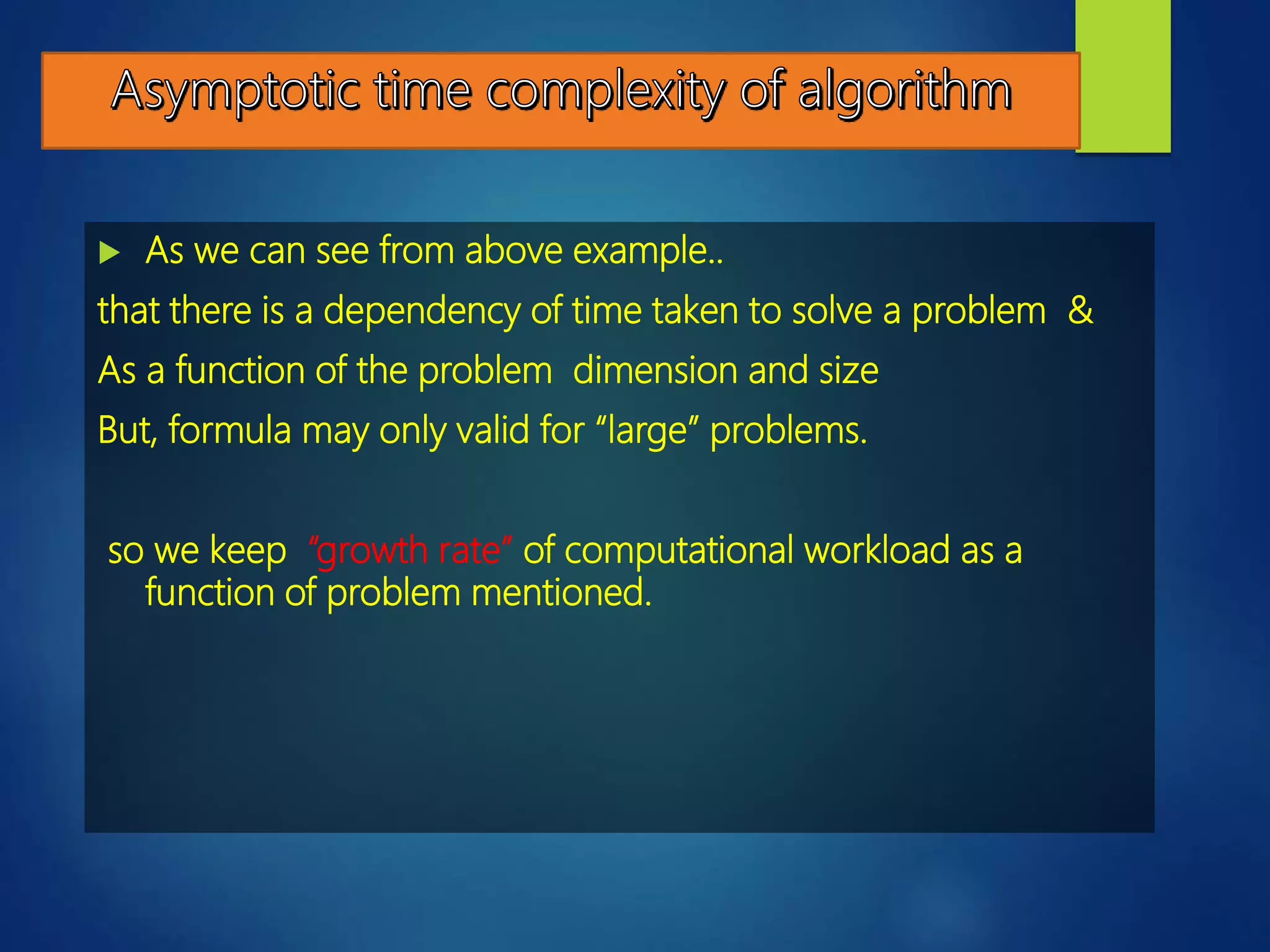
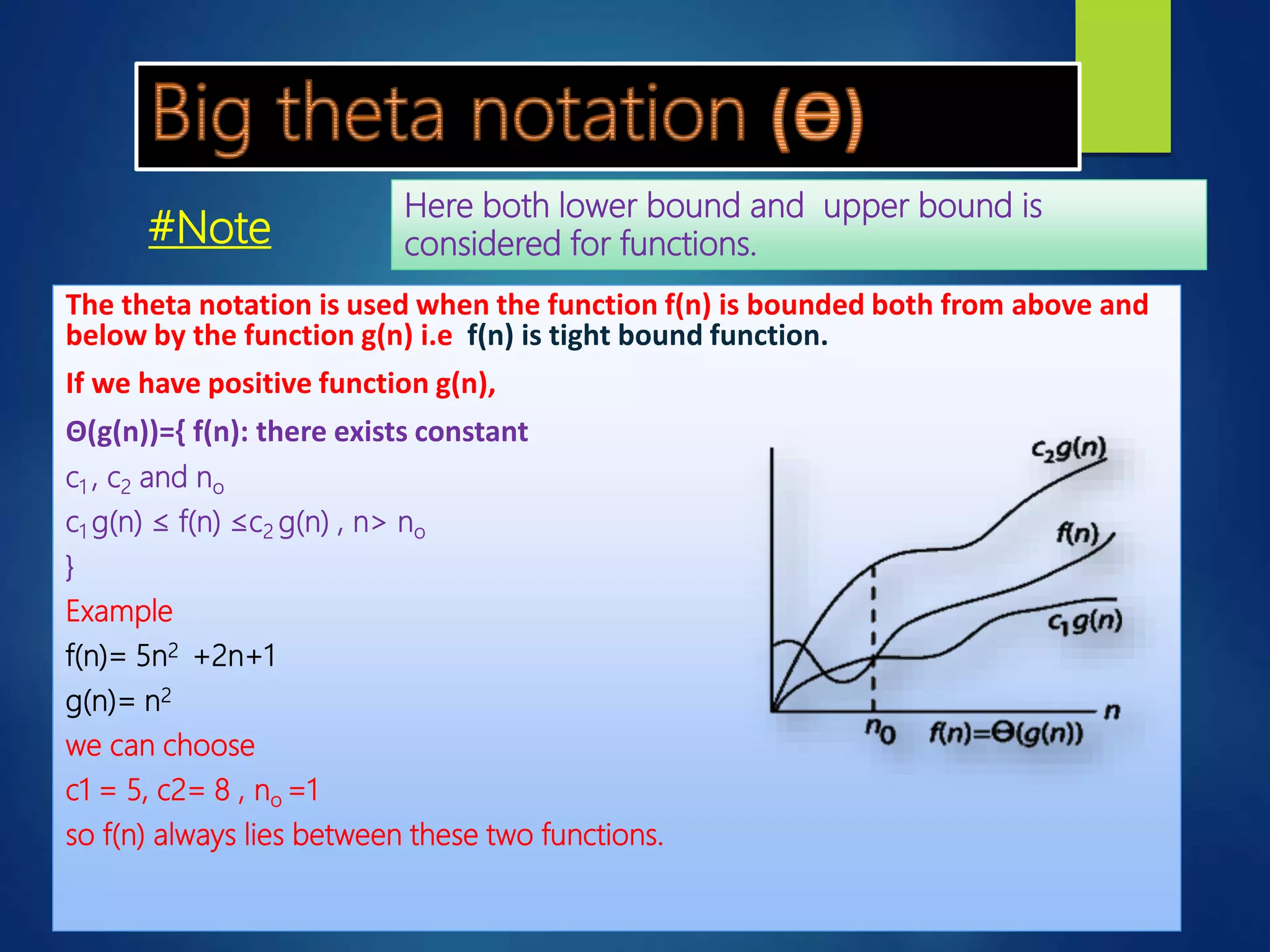
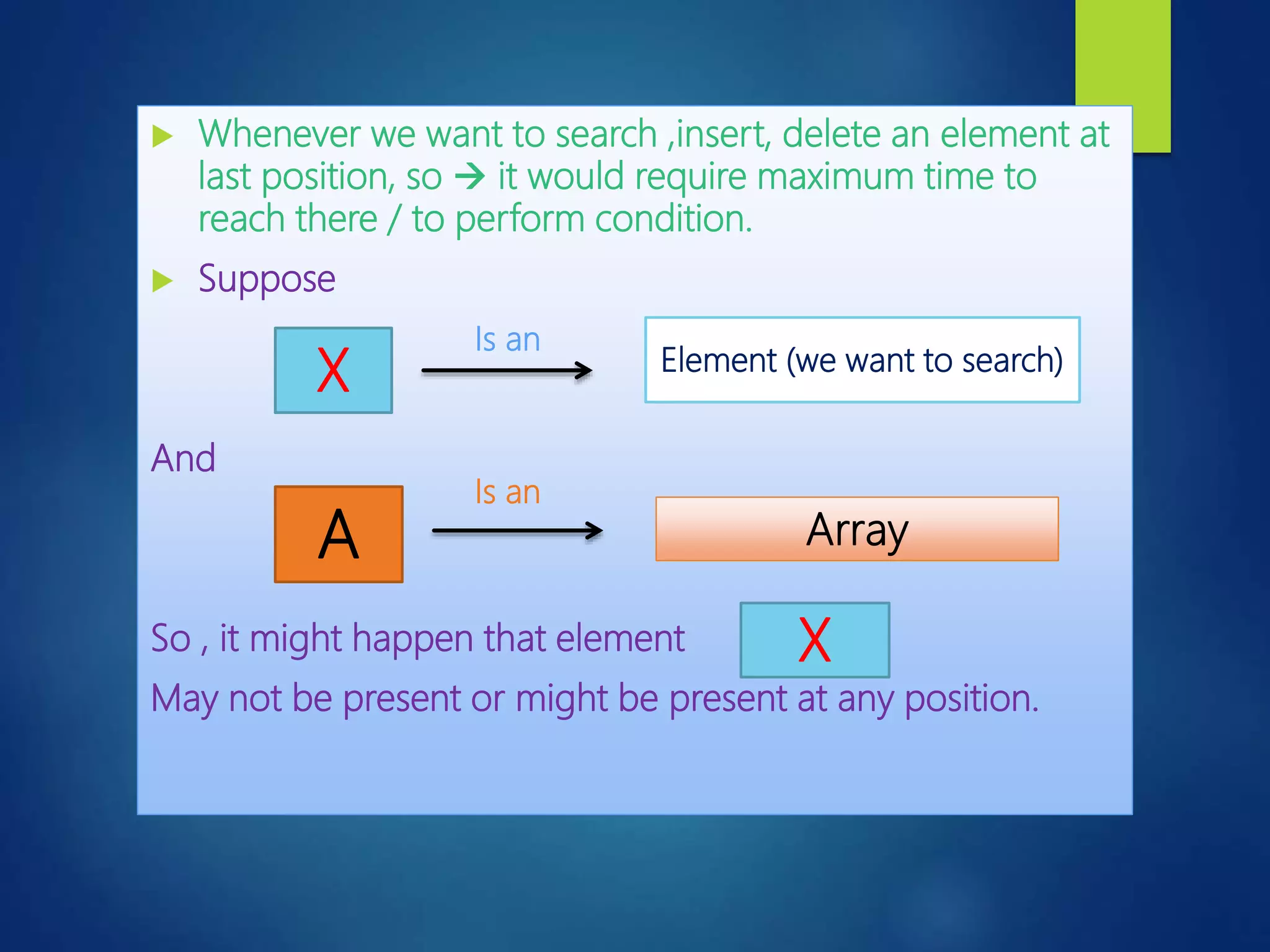
![ An operation that segregates items into groups according to specified
collection
For example- array A[ ]={ 10,7,15, 2, 20, 4 } before sorting
array A[ ] = { 2, 4, 7, 10, 15, 20} after sorting
Deals with deals with
Sorting
Internal sorting External sorting
Sorting the data
stored in computer’s
memory.
Sorting the data stored
in files.
It is applied for
voluminous data](https://image.slidesharecdn.com/ntccppt-170702003841/75/TIME-EXECUTION-OF-DIFFERENT-SORTED-ALGORITHMS-26-2048.jpg)