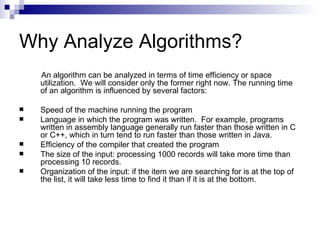
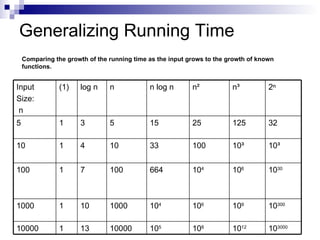
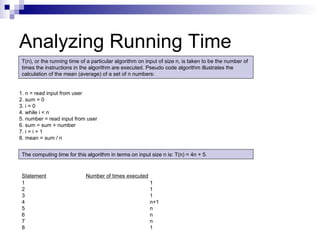
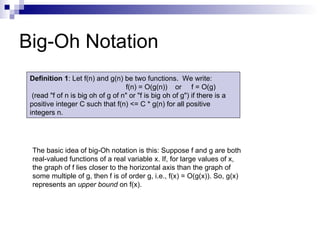
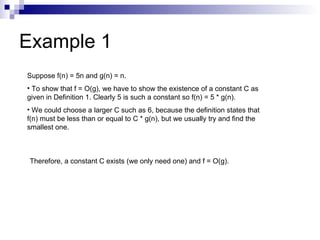
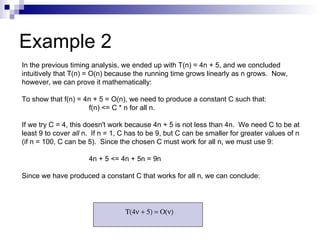
The document discusses analyzing the running time of algorithms using Big-O notation. It begins by introducing Big-O notation and how it is used to generalize the running time of algorithms as input size grows. It then provides examples of calculating the Big-O running time of simple programs and algorithms with loops but no subprogram calls or recursion. Key concepts covered include analyzing worst-case and average-case running times, and rules for analyzing the running time of programs with basic operations and loops.
![Example 8 Consider the sorting algorithm shown below. Find the number of instructions executed and the complexity of this algorithm. 1) for (i = 1; i < n; i++) { 2) SmallPos = i; 3) Smallest = Array[SmallPos]; 4) for (j = i+1; j <= n; j++) 5) if (Array[j] < Smallest) { 6) SmallPos = j; 7) Smallest = Array[SmallPos] } 8) Array[SmallPos] = Array[i]; 9) Array[i] = Smallest; } The total computing time is: T(n) = (n) + 4(n-1) + n(n+1)/2 – 1 + 3[n(n-1) / 2] = n + 4n - 4 + (n 2 + n)/2 – 1 + (3n 2 - 3n) / 2 = 5n - 5 + (4n 2 - 2n) / 2 = 5n - 5 + 2n 2 - n = 2n 2 + 4n - 5 = O(n 2 )](https://image.slidesharecdn.com/analysisofalgorithmsi-090902055847-phpapp02/85/Analysis-Of-Algorithms-I-19-320.jpg)
![Example 9 What is the complexity of this C++ code? 1) cin >> n; // Same as: n = GetInteger(); 2) for (i = 1; i <= n; i ++) 3) for (j = 1; j <= n; j ++) 4) A[i][j] = 0; 5) for (i = 1; i <= n; i ++) 6) A[i][i] = 1; The following program segment initializes a two-dimensional array A (which has n rows and n columns) to be an n x n identity matrix – that is, a matrix with 1’s on the diagonal and 0’s everywhere else. More formally, if A is an n x n identity matrix, then: A x M = M x A = M, for any n x n matrix M.](https://image.slidesharecdn.com/analysisofalgorithmsi-090902055847-phpapp02/85/Analysis-Of-Algorithms-I-20-320.jpg)
![Example 10 Here is a simple linear search algorithm that returns the index location of a value in an array. /* a is the array of size n we are searching through */ i = 0; while ((i < n) && (x != a[i])) i++; if (i < n) location = i; else location = -1; 1 + 3 + 5 + ... + (2n - 1) / n = (2 (1 + 2 + 3 + ... + n) - n) / n We know that 1 + 2 + 3 + ... + n = n (n + 1) / 2, so the average number of lines executed is: [2[n(n+1)/2] – n]/n =n =O(n) Average number of lines executed equals:](https://image.slidesharecdn.com/analysisofalgorithmsi-090902055847-phpapp02/85/Analysis-Of-Algorithms-I-21-320.jpg)