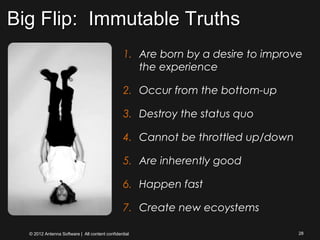
The document discusses how mobility is impacting the financial services market and driving a "Big Flip". Key points:
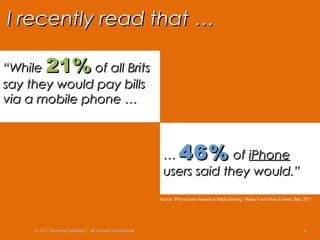
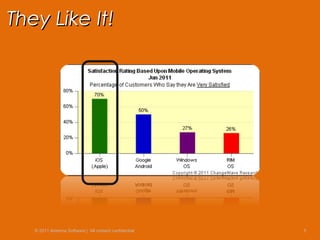
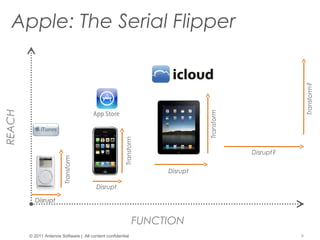
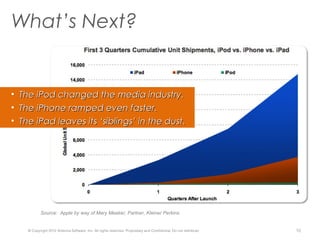
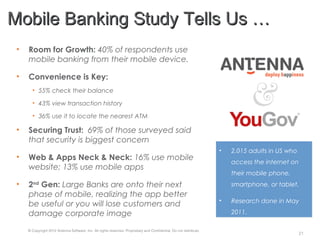
- Smartphones and mobile adoption are growing rapidly worldwide, especially among younger users, and this is driving increased demand for mobile banking services.
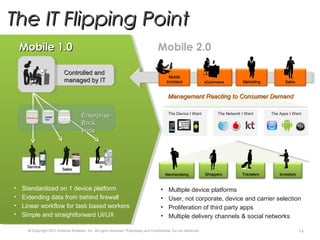
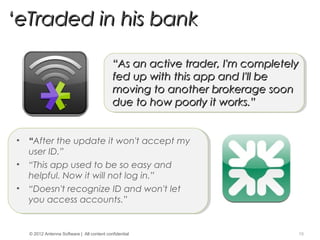
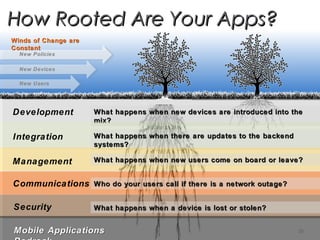
- Enterprises are struggling to manage numerous mobile devices, apps, and changing technologies, while users expect to use their preferred devices and apps for work.
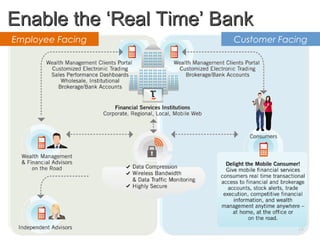
- Case studies show how banks are using mobile apps to provide many services to customers like account access, payments, and research.
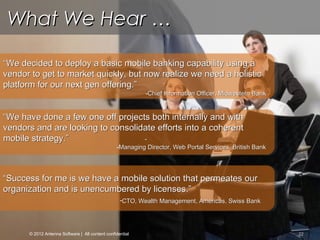
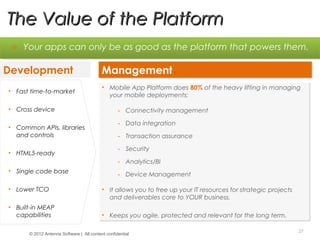
- A mobile platform can help financial firms manage deployments and keep up with constant mobile changes, while focusing resources on core business priorities.