Test Table for Wireless NIC
•Download as DOCX, PDF•
0 likes•338 views
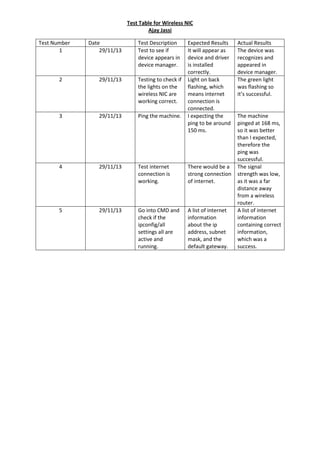
This is a test table that was created when testing the wireless NIC. It can also be used as a guide, to show how to test a Wi-Fi connection. It includes a number different tests which include ping, ipconfig,and drivers. This document is part of my IT coursework*
Report
Share
Report
Share
Recommended
Testing for wireless nic, helpful guide.

This is a test table for a Wireless NIC, it can be used as a guide for yourself.
I have included several tests such as testing for ping and testing the device manager.
It is also P1 of my UNIT 3 in my Cisco coursework.
Recommended
Testing for wireless nic, helpful guide.

This is a test table for a Wireless NIC, it can be used as a guide for yourself.
I have included several tests such as testing for ping and testing the device manager.
It is also P1 of my UNIT 3 in my Cisco coursework.
Tôi đã sai lầm khi yêu người con gái quá dễ dãi

Khi tôi vừa “gợi ý” xong “chuyện ấy”, không ngờ Uyên lại ôm lấy tôi và gật đầu khiến tôi quá bất ngờ. Cô ấy còn dúi vào tay tôi một vật, tôi mở ra thì càng bất ngờ hơn…
Installation and Testing of Hardware

This presentation is about installing a wireless NIC into a computer system and testing it for its functionality. It also explains how problems can be solved if any precautions happen.
This presentation is part of my IT coursewok*
Troubleshooting-computer-system-network-1.pptx

Troubleshooting-computer system-network troubleshooting tle grade 9
Installation of a selected piece of hardware

the selected piece of hardware for the installation, is a wireless NIC, it has also been tested for functionality.
IT Essentials (Version 7.0) - ITE Chapter 6 Exam Answers

Full link: https://itexamanswers.net/it-essentials-ite-v6-0-v7-0-chapter-6-exam-answers-100.html
Student's industrial attachment logbook

Bachelor of science in computer science, information technology and any related course....
Commands used in Assessing Network layout & Security

Commands used in Assessing Network layout & Security
More Related Content
Viewers also liked
Tôi đã sai lầm khi yêu người con gái quá dễ dãi

Khi tôi vừa “gợi ý” xong “chuyện ấy”, không ngờ Uyên lại ôm lấy tôi và gật đầu khiến tôi quá bất ngờ. Cô ấy còn dúi vào tay tôi một vật, tôi mở ra thì càng bất ngờ hơn…
Viewers also liked (8)
Similar to Test Table for Wireless NIC
Installation and Testing of Hardware

This presentation is about installing a wireless NIC into a computer system and testing it for its functionality. It also explains how problems can be solved if any precautions happen.
This presentation is part of my IT coursewok*
Troubleshooting-computer-system-network-1.pptx

Troubleshooting-computer system-network troubleshooting tle grade 9
Installation of a selected piece of hardware

the selected piece of hardware for the installation, is a wireless NIC, it has also been tested for functionality.
IT Essentials (Version 7.0) - ITE Chapter 6 Exam Answers

Full link: https://itexamanswers.net/it-essentials-ite-v6-0-v7-0-chapter-6-exam-answers-100.html
Student's industrial attachment logbook

Bachelor of science in computer science, information technology and any related course....
Commands used in Assessing Network layout & Security

Commands used in Assessing Network layout & Security
Network Troubleshooting

I have discussed about the common problem of network issues of a computer . How we can find out what is the bug on our network wizerd and what should we do for that perticular problem . I also discussed about the physical hardware problem and how to find out what the problem is and what is the way to find the solution for it . If you think for a problem that i am finished or my machine is finished it is your foolishness . So you can read my slides and can find out the problem and their solution .
Positive Hack Days. Pavlov. Network Infrastructure Security Assessment

A participant will acquire basic skills of searching for vulnerabilities on switches and routers from various vendors. The masterclass will cover both common network vulnerabilities, and exceptive cases that can be detected in the process of security assessment of real networks.
Similar to Test Table for Wireless NIC (20)
IT Essentials (Version 7.0) - ITE Chapter 6 Exam Answers

IT Essentials (Version 7.0) - ITE Chapter 6 Exam Answers
Commands used in Assessing Network layout & Security

Commands used in Assessing Network layout & Security
Positive Hack Days. Pavlov. Network Infrastructure Security Assessment

Positive Hack Days. Pavlov. Network Infrastructure Security Assessment
More from Ajay Jassi
Security Plan for Small Networks/Offices 

This document is a security plan that was created ideally for any home network or small businesses.
This is part of my IT coursework*
Managing IT Security

This is a presentation about taking security features into IT, securing computer systems and data in a business.
This is part of my IT coursework*
Impact on IT system breaches

This is a presentation about how system breaches can affect computer systems and data in business.
This is part of my IT coursework*
Testing software

This is a presentation about testing pieces of software that has been previously installed testing for its functionality. The software that was tested was OpenOffice, Skype and AVG.
This is part of my IT coursework*
Configuring personal desktop

This is a presentation about personalising a computer system for a user.
This is part of my IT coursework*
Preaparation for new software application

This is a documentation that is for users who are installing software to their a computer system.
This is part of my IT coursework*
Software Licences

This is a documentation about software licences, legal requirements, processes involved, benefits of registering software, and implications of installing software.
This document is part of my IT coursework*
Hardware Documentation and Benefits of Hardware Provider

This documentation is about a piece of hardware that has been installed and how some providers can benefit the users.
This document is part of my IT coursework*
IT job role description for Technical Support Engineer

This is a brief job description about a Technical Support Engineer in the IT Industry. This will be explaining the requirements, qualifications and experience that is needed for the role. It also shows the salary for this specific information, the responsibilities and the main roles that will be done on everyday basics.
This is part of my IT coursework*
Characteristics for IT Employee (P1)

This is a mind map created in Microsoft Word, which explains and tells the importances of characteristics that are required for IT employees whilst working in the IT industry.
This document is part of my IT coursework*
Preparation for Installing Hardware

This is a presentation about what processes are required before installing and opening up a computer system.Images and annotations will be shown in, note this is a basic presentation.
This is partf my IT coursework*
Reasons why Hardware is Installed and Potential Problems and the Precautions

In this presentation it explains why hardware is installed and the problems that can happen, It also explains how it can be prevented.
This presentation is part of my IT coursework*
Installation of Windows 7 using USB

This is a presentation about how Windows 7 is installed fresh, using a memory stick. This is a basic step-by-step with images.
This is part of my IT coursework*
Potential problems that occur during hardware installation

This presentation is about the risk that my occur when installing hardware. It explains how it happens and how it can be prevented.
This is part of my IT coursework*
Building Computer System

In this presentation, I used Virtual Desktop to take screenshots and explain how a computer system is build starting with the tower.
This presentation is part of my IT coursework*
Installation and configuration of Wireless NIC

This is a presentation showing how to install wireless NIC hardware and software. Images and annotations are used, to make it clear.
This is part of my IT coursework*
Comparison between Windows 8 and Mavericks OS X

This is a presentation about comparing two operating systems. The OS is chose were Windows 8 and Mac Mavericks OS X. I chose these as Microsoft and Apple are competitors.
This presentation is part of my coursework*
Upgrade Invoice

This is an upgrade invoice I created for Mr Earl Atkinson.
This document is part of my IT coursework*
Personalising Desktop

This presentation is about personalising a pc; to modify the wallpaper, screensaver and icon size.
This document is part of my IT coursework*
Health and safety requirements for computer maintenance

This is a presentation about how employer keeps their employees safe by following the law, and this also shows how files are backed up easily.
This presentation is part of my IT coursework*
More from Ajay Jassi (20)
Hardware Documentation and Benefits of Hardware Provider

Hardware Documentation and Benefits of Hardware Provider
IT job role description for Technical Support Engineer

IT job role description for Technical Support Engineer
Reasons why Hardware is Installed and Potential Problems and the Precautions

Reasons why Hardware is Installed and Potential Problems and the Precautions
Potential problems that occur during hardware installation

Potential problems that occur during hardware installation
Health and safety requirements for computer maintenance

Health and safety requirements for computer maintenance
Recently uploaded
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Recently uploaded (20)
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Test Table for Wireless NIC
- 1. Test Table for Wireless NIC Ajay Jassi Test Number 1 Date 29/11/13 Test Description Test to see if device appears in device manager. Expected Results It will appear as device and driver is installed correctly. Light on back flashing, which means internet connection is connected. I expecting the ping to be around 150 ms. 2 29/11/13 Testing to check if the lights on the wireless NIC are working correct. 3 29/11/13 Ping the machine. 4 29/11/13 Test internet connection is working. There would be a strong connection of internet. 5 29/11/13 Go into CMD and check if the ipconfig/all settings all are active and running. A list of internet information about the ip address, subnet mask, and the default gateway. Actual Results The device was recognizes and appeared in device manager. The green light was flashing so it’s successful. The machine pinged at 168 ms, so it was better than I expected, therefore the ping was successful. The signal strength was low, as it was a far distance away from a wireless router. A list of internet information containing correct information, which was a success.
