This document is an industrial attachment logbook for Paullaster Amolo Okoth, an undergraduate student in the Department of Information Technology at Multimedia University of Kenya. Over the course of a 7 week internship period from May 6th to August 6th 2019, the logbook details the various IT-related tasks completed each day, including configuring networks and printers, installing software, troubleshooting connectivity issues, and providing other technical support. The logbook is submitted in partial fulfillment of the requirements for a Bachelor of Science degree in Information Technology.

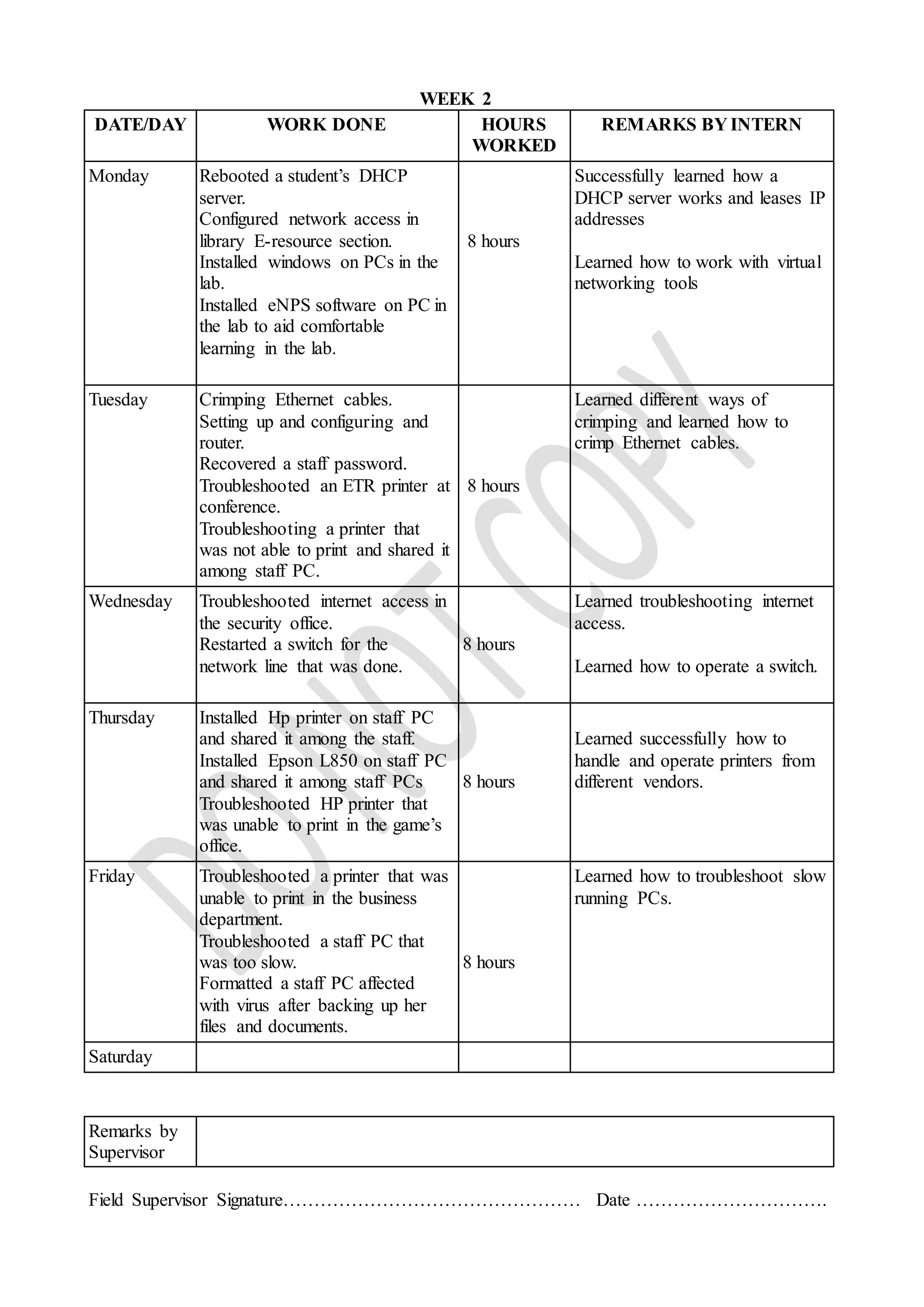
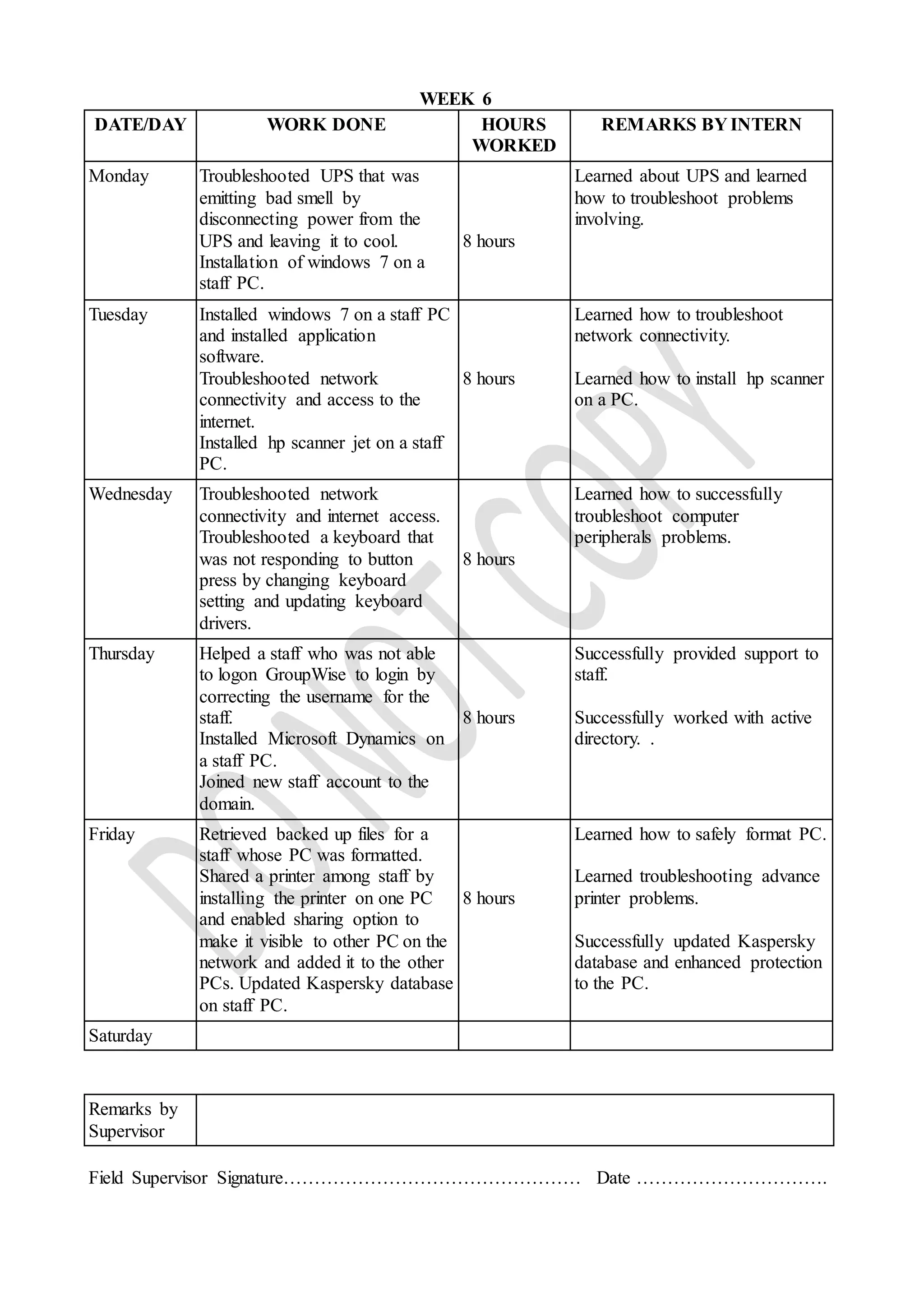
![STUDENT’S WEEKLY REPORT (WEEK 4)
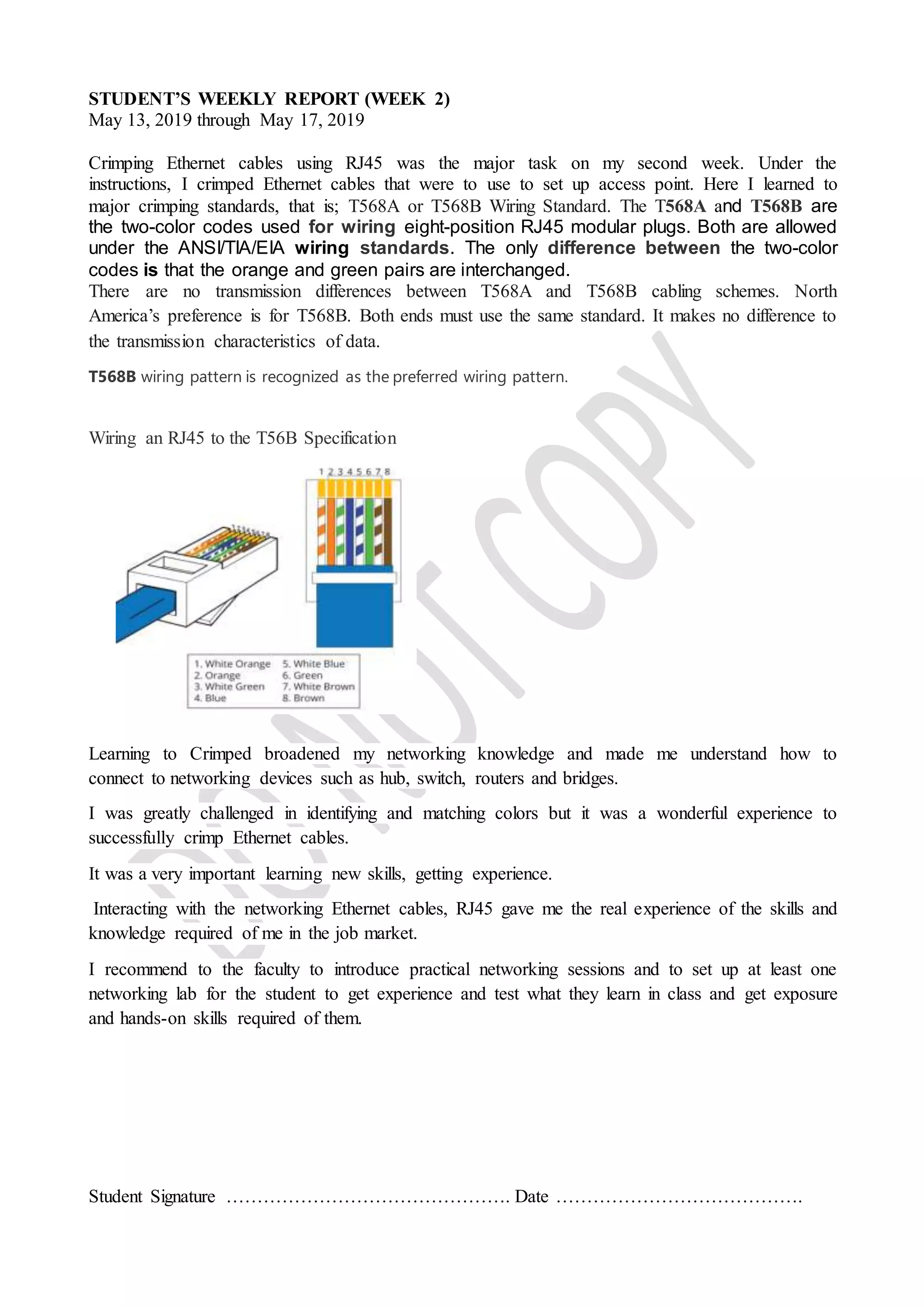
May 27, 2019 through May 31, 2019
Configuring a Cisco.
Configuring Global Parameters.
configure terminal
2. hostname name
3. enablesecret password
4. no ip domain-lookup
Configuring Gigabit Ethernet WAN Interfaces
configure terminal
2. interface gigabitethernet slot/port
3. ip address ip-address mask
4. no shutdown
5. exit
Configuring a Loopback Interface
configure terminal
2. interface type number
3. ip address ip-address mask
4. exit
Configuring Command-Line Access
configure terminal
2. line [aux| console |tty | vty] line-number
3. password password
4. login
5. exec-timeout minutes [seconds ]
6. line [aux| consoletty |vty] line-number
7. password password
8. login
9. end
Configuring a Cisco router broadened my networking proficiency and working knowledge of
routers, gateways and access point and how the broadcast.
I recommend to the faculty to introduce a lab session where student is practically taught to
configure access points and routers from different vendors.](https://image.slidesharecdn.com/paullastermmulogbook-191023103826/75/Student-s-industrial-attachment-logbook-13-2048.jpg)