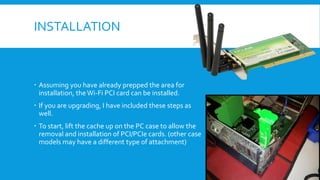
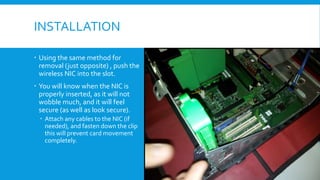
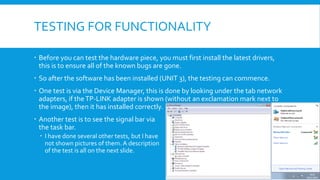
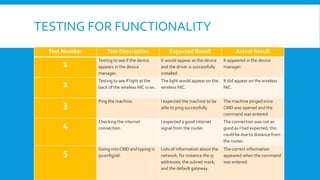
The document details the installation process of a wireless NIC PCI card, including preparation, removal of the old card, and proper insertion of the new card. It also explains testing methods to ensure functionality, such as checking device manager recognition and signal strength. Potential problems such as ESD damage, incorrect fitting, and overheating are discussed along with preventive measures.