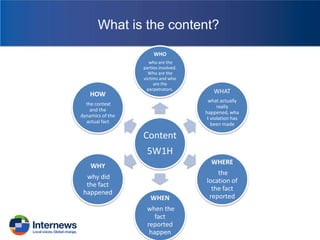
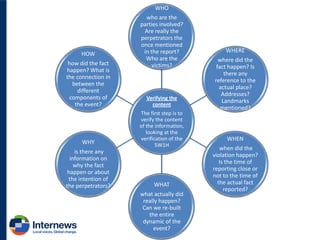
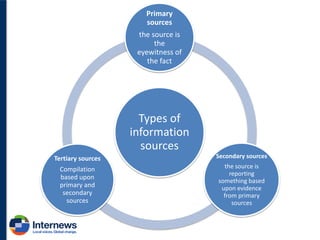
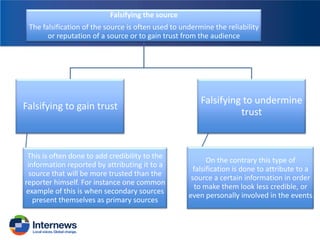
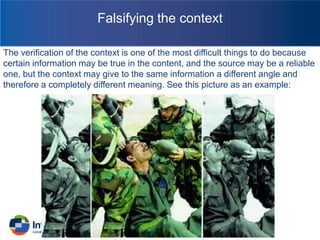
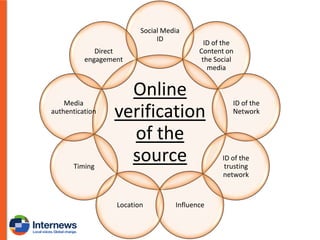
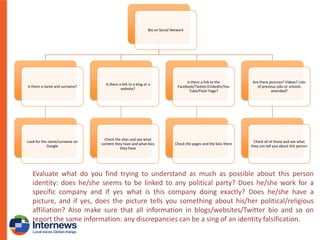
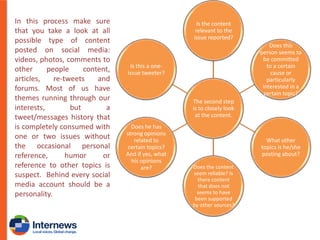
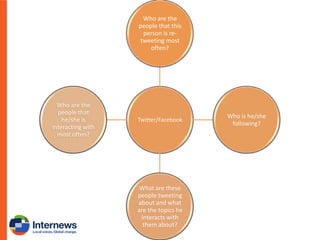
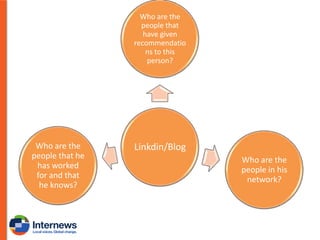
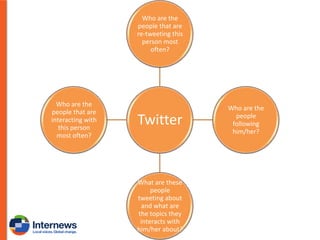
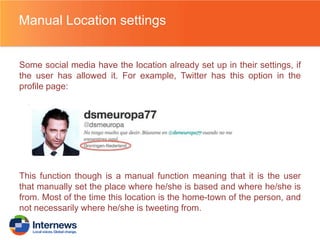
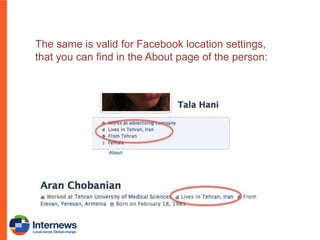
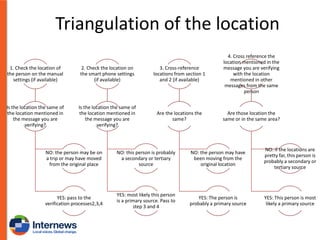
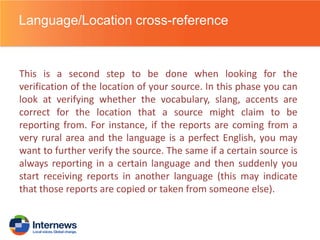
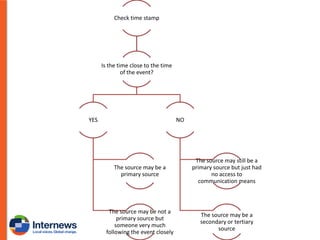
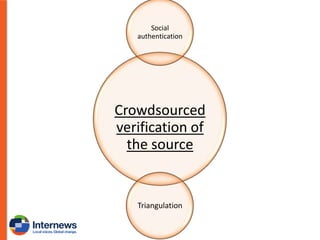
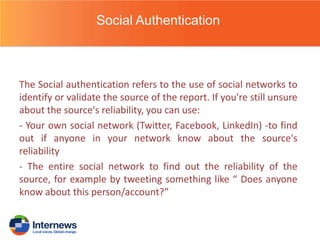
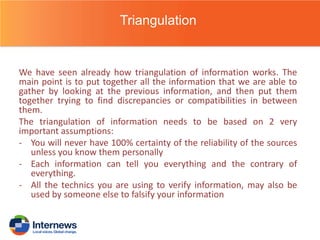
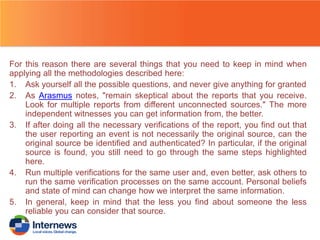
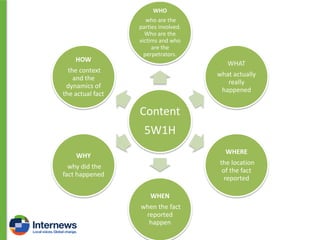
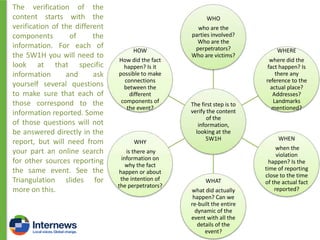
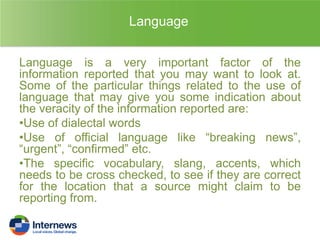
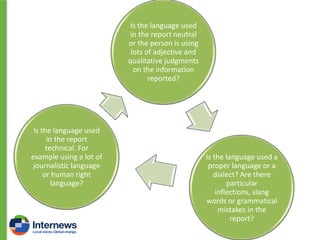
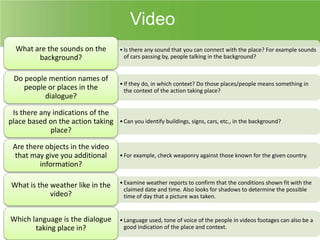
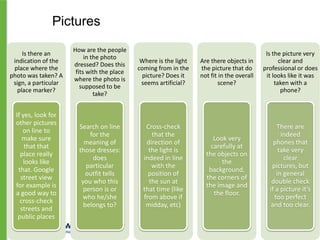
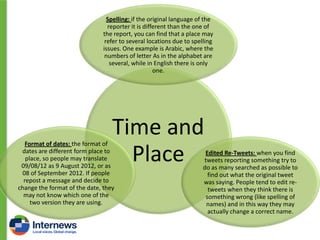
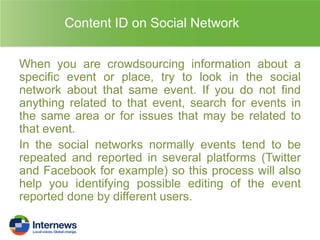
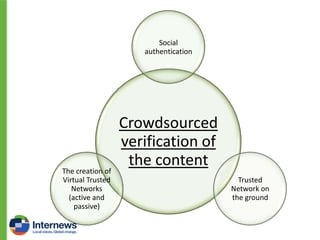
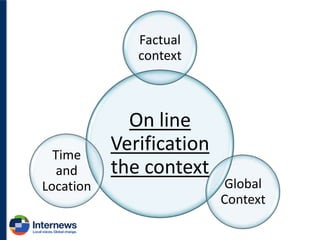
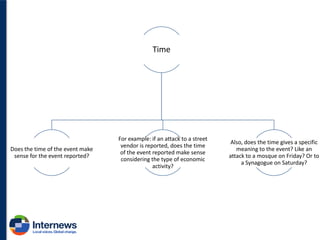
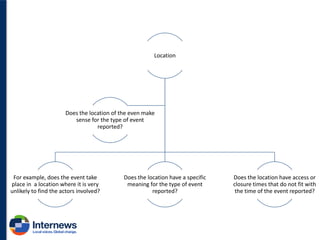
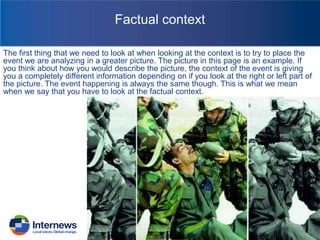
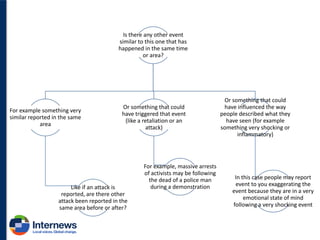
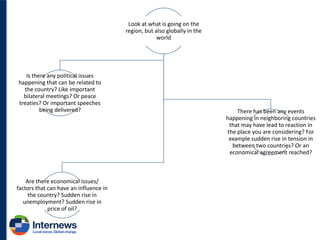
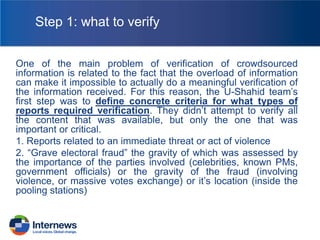
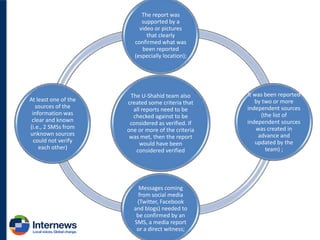
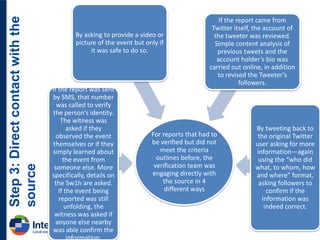
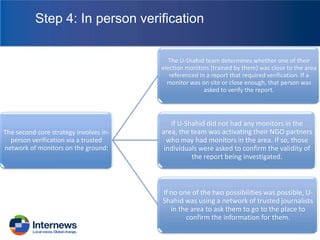
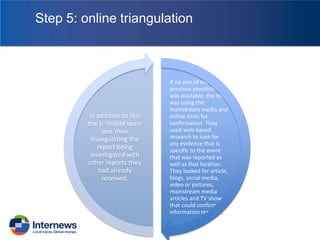
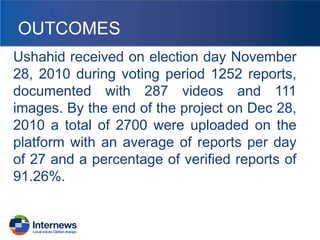
This document details a comprehensive framework for verifying crowdsourced information during elections, emphasizing the importance of a multi-level approach to ascertain the accuracy of reports. It covers various types of verification: content, context, and sources, and outlines methods such as triangulation, social authentication, and direct engagement with sources to assess credibility. The document highlights the complexities of online verification, including factors like timing, location, and language, which are critical in determining the reliability of reported information.