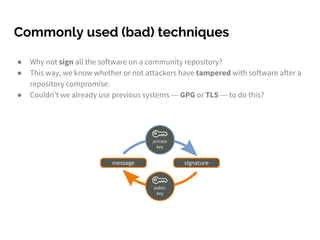
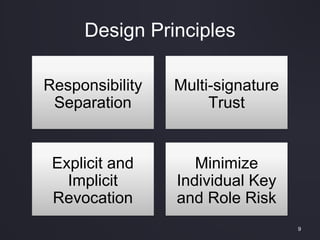
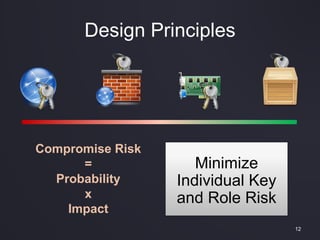
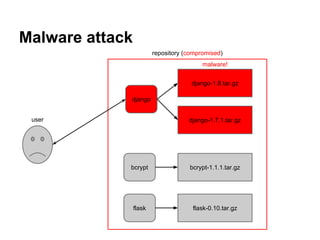
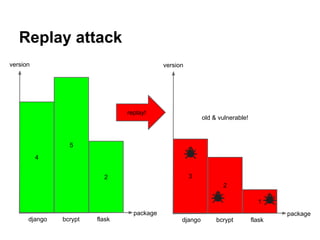
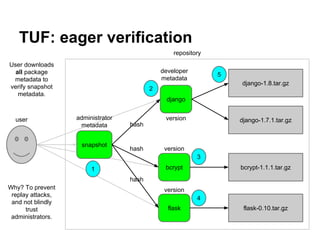
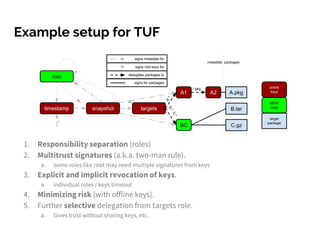
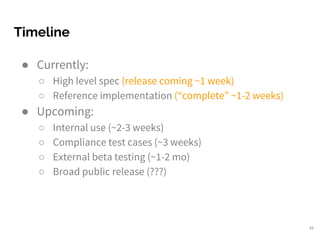
The document discusses the challenges of securing software distribution, highlighting various past software update hacks and their impacts. It introduces The Update Framework (TUF) as a solution, emphasizing principles like responsibility separation, multi-signature trust, and minimizing key compromise risks. The framework aims to provide a robust and resilient system for software updates amidst evolving security threats.






































![My background... (2003-2008)
● Built the first package manager designed specifically for OSVMs (Stork)
○ Deployed on the research infrastructure “PlanetLab”
■ Practical experience: thousands of VM instances over 8 years of use
○ Packages are cached in a special VM and shared
■ Disk, memory, and bandwidth savings
■ Additional security risks [USENIX ATC 2005], [LISA 2007]](https://image.slidesharecdn.com/tufdockersummit2016-161010203221/85/Talking-TUF-Securing-Software-Distribution-53-320.jpg)