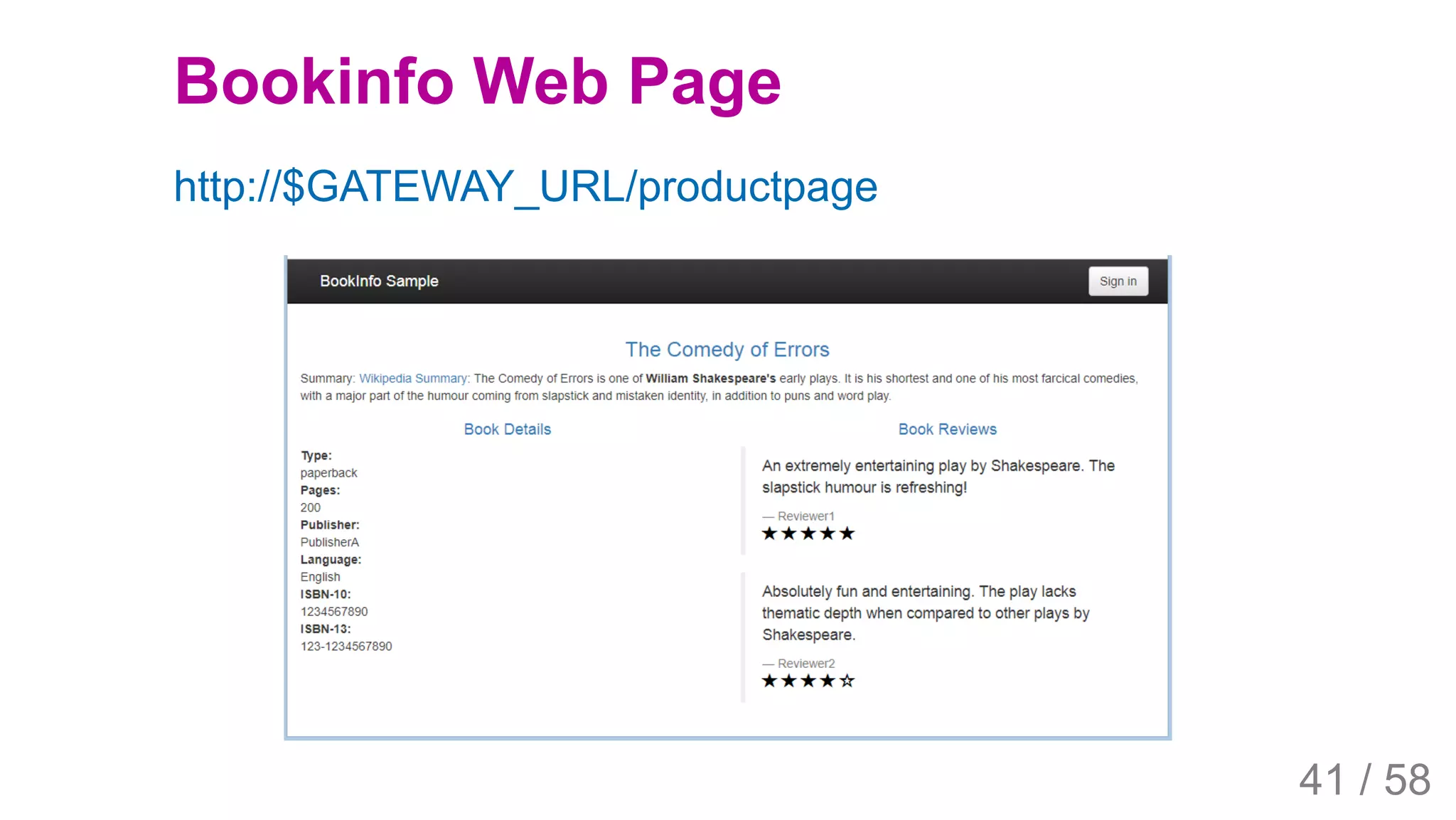
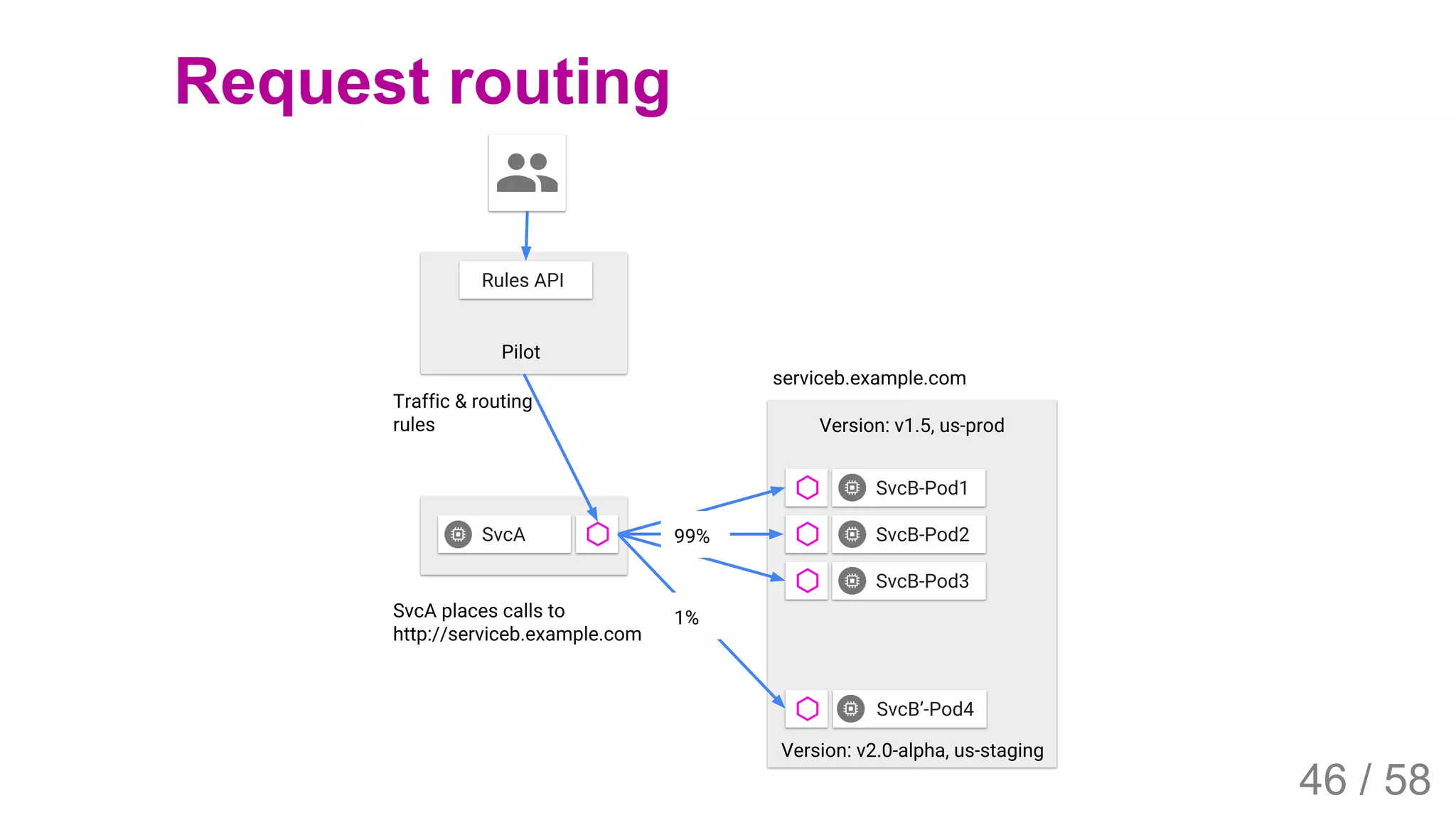
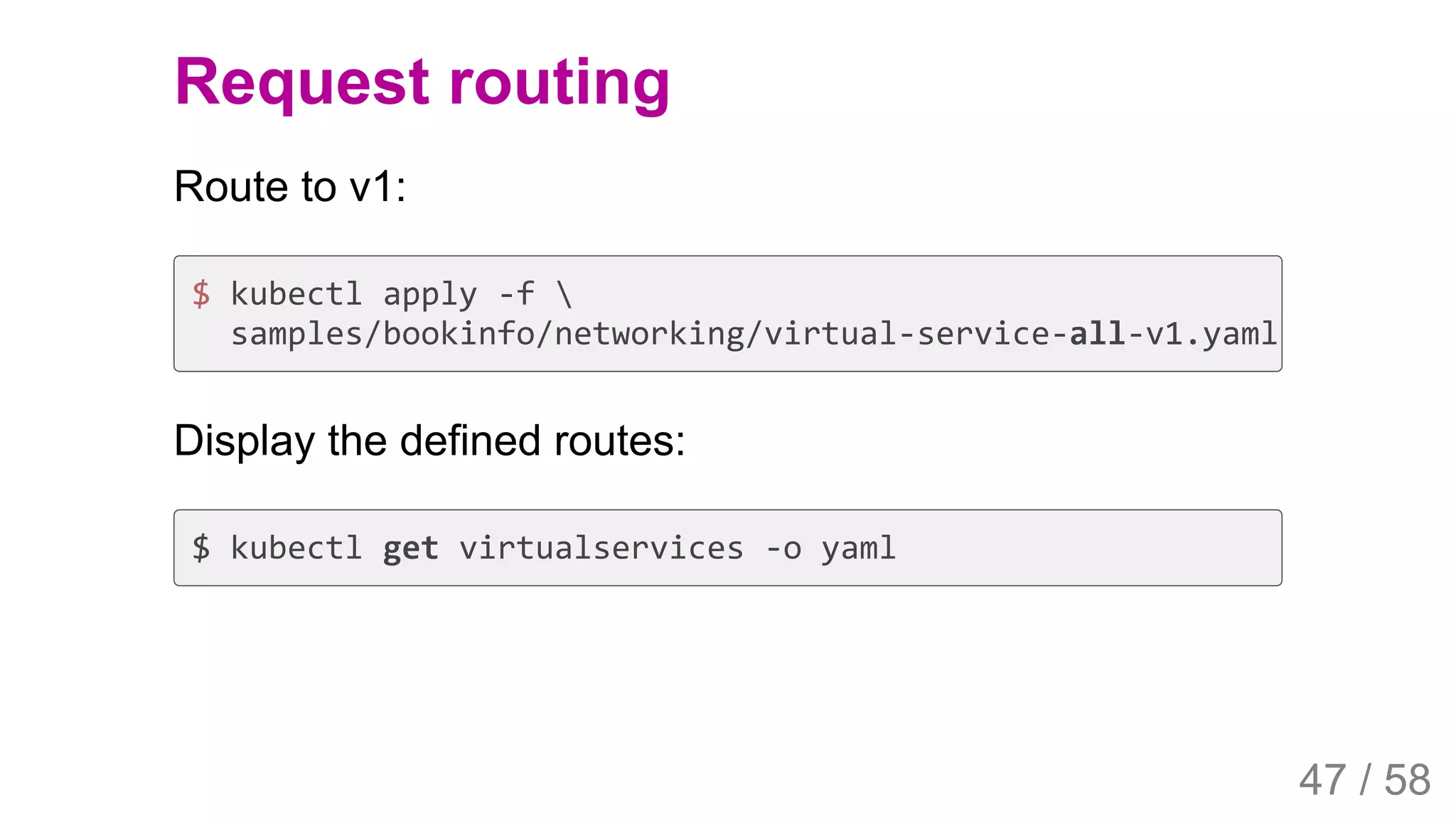
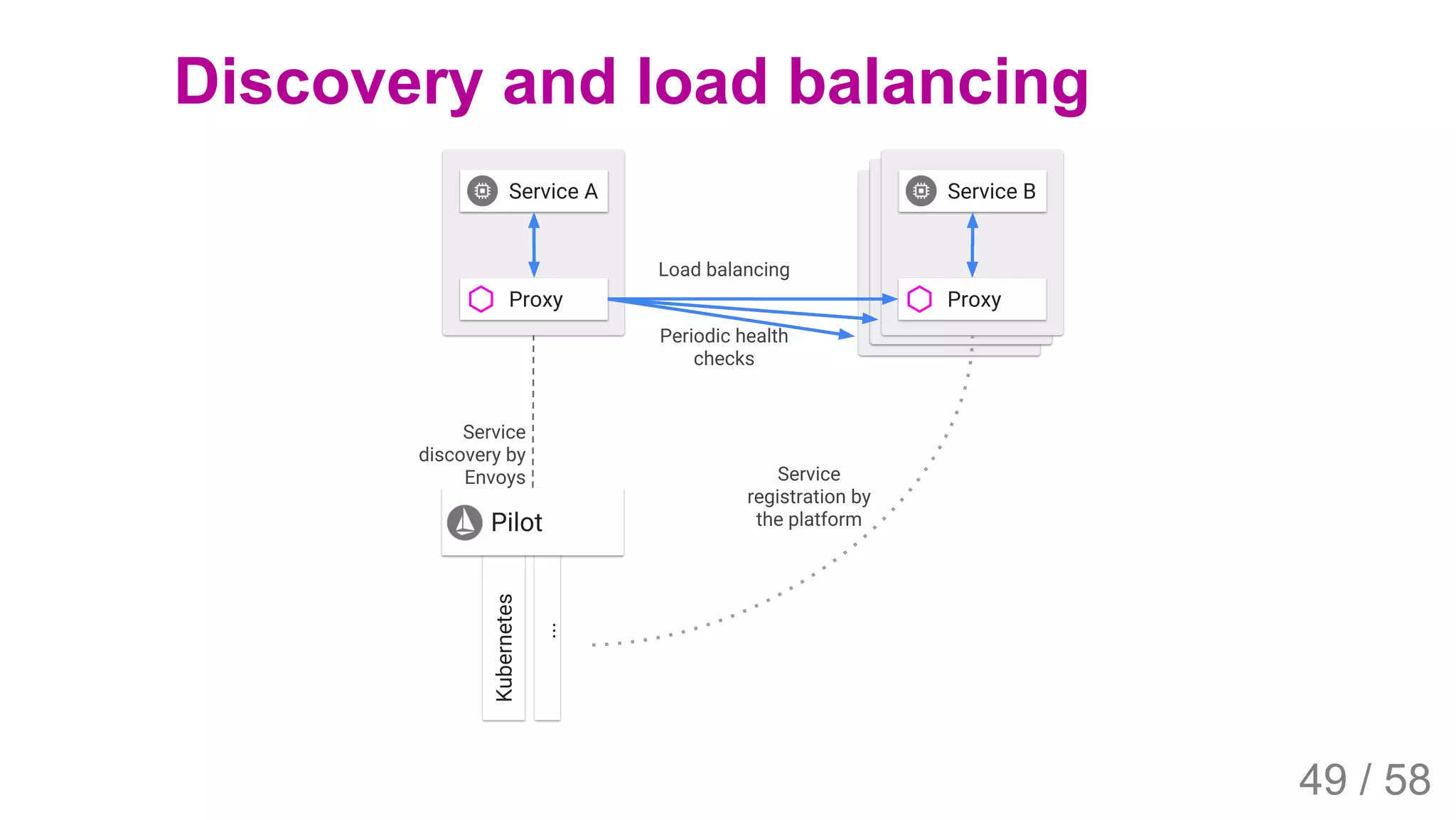
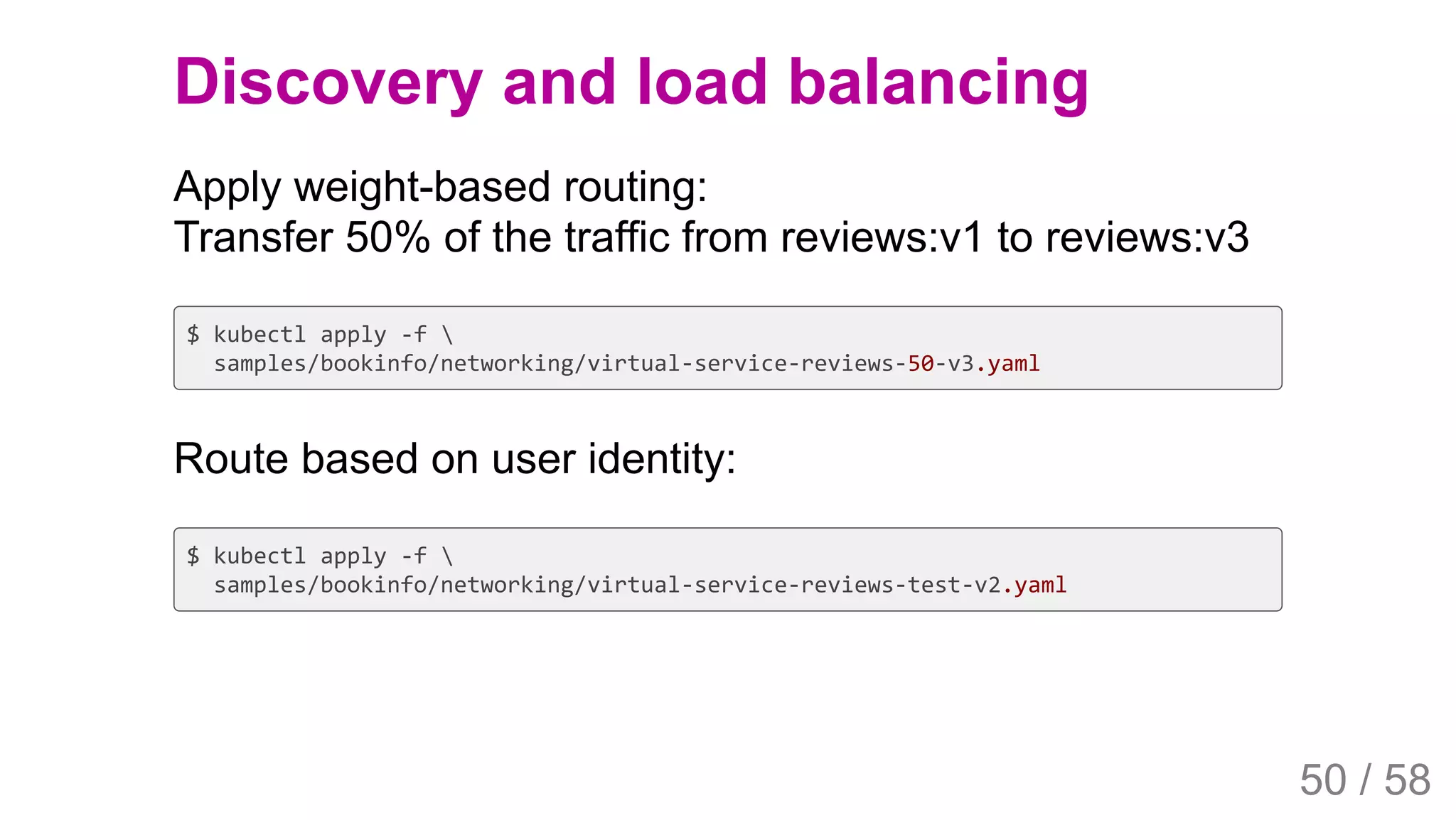
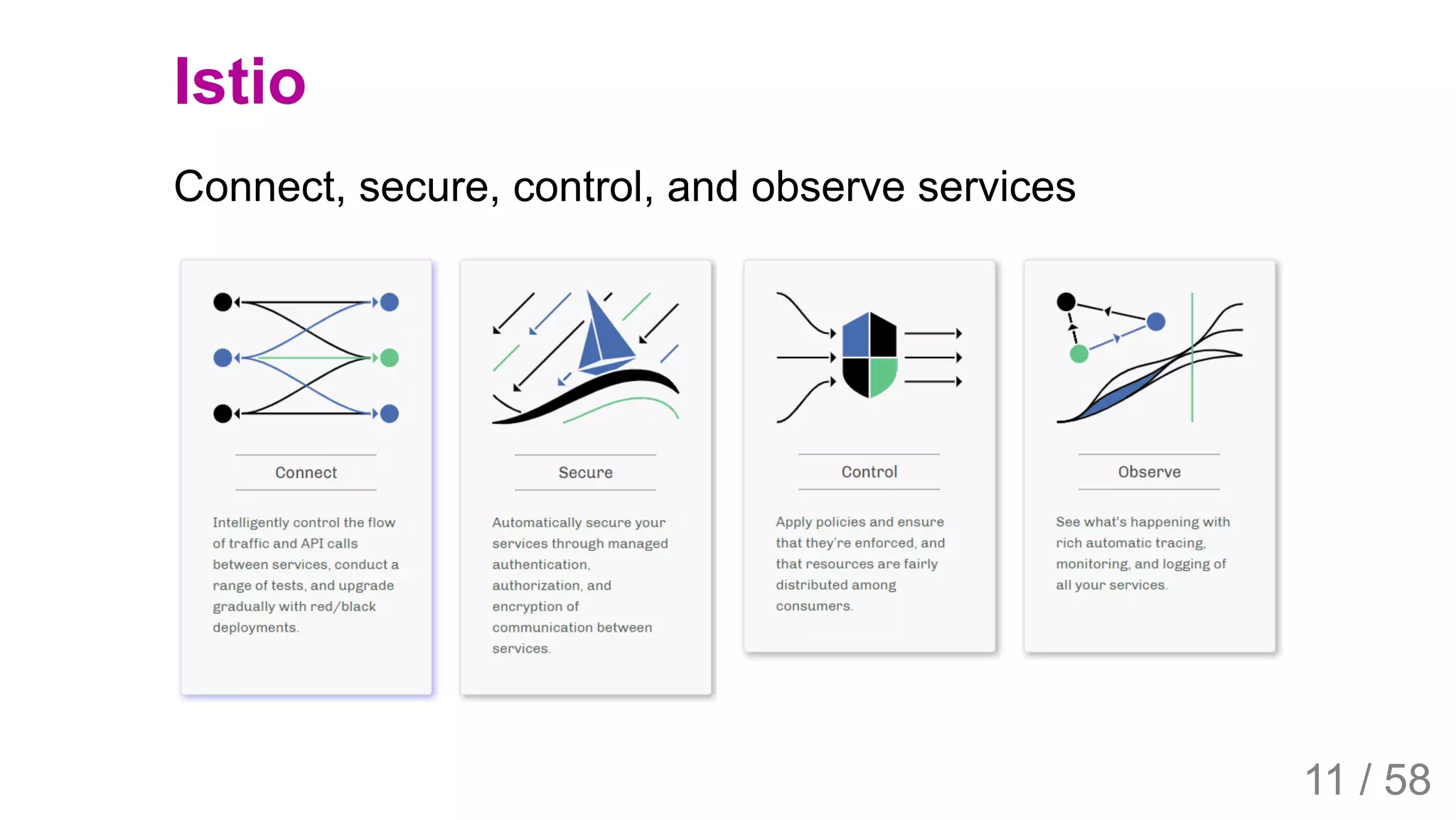
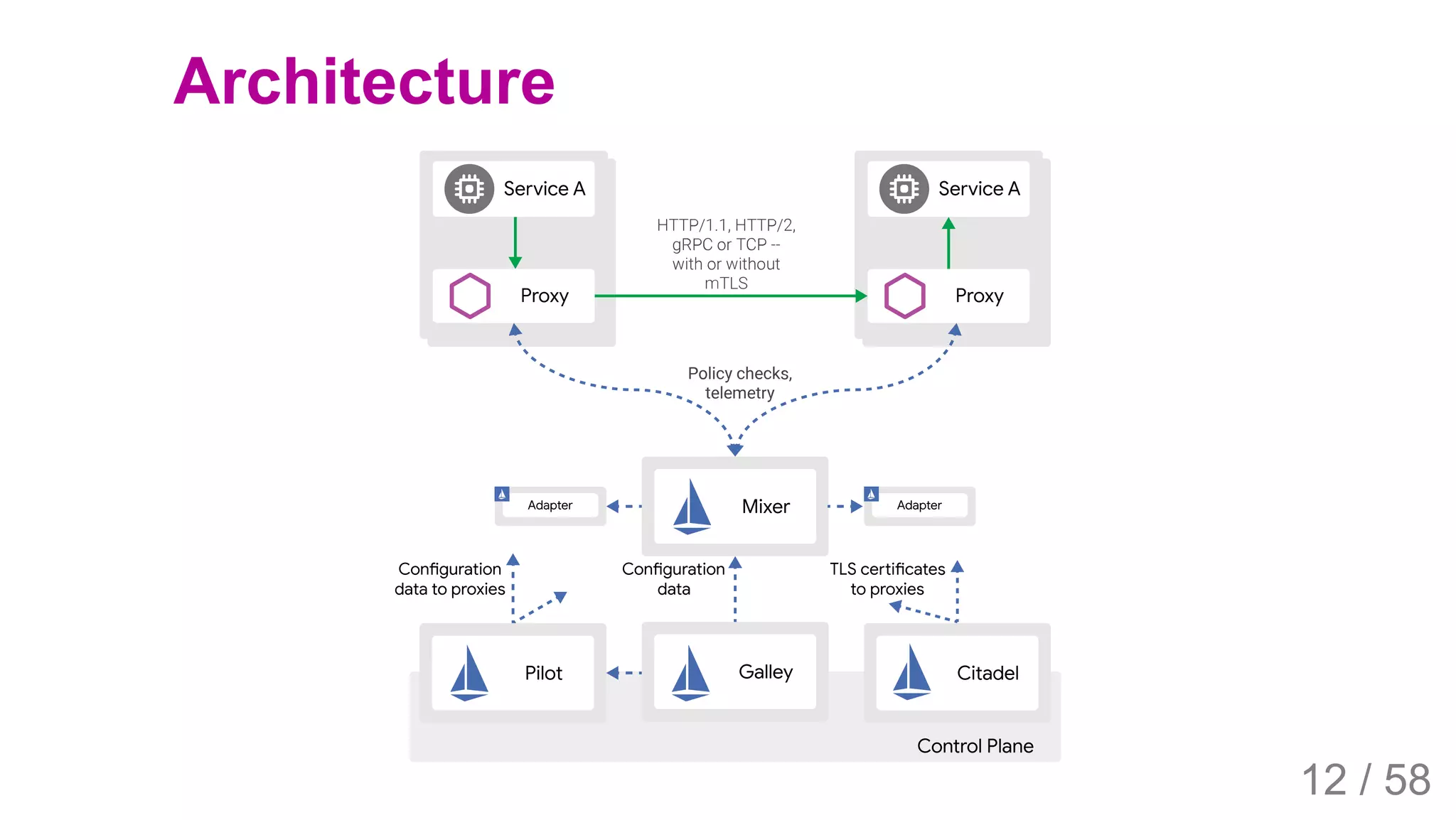
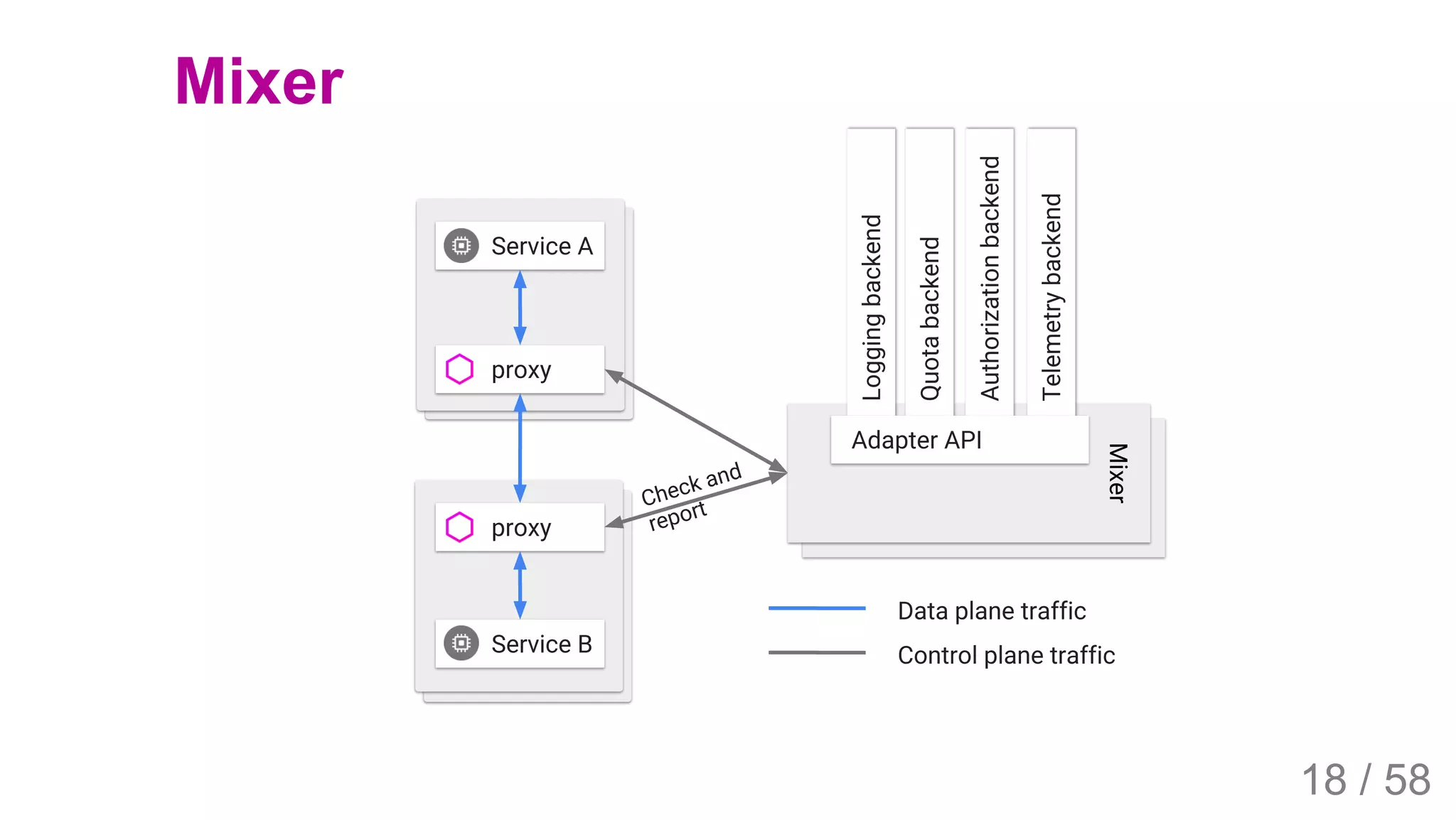
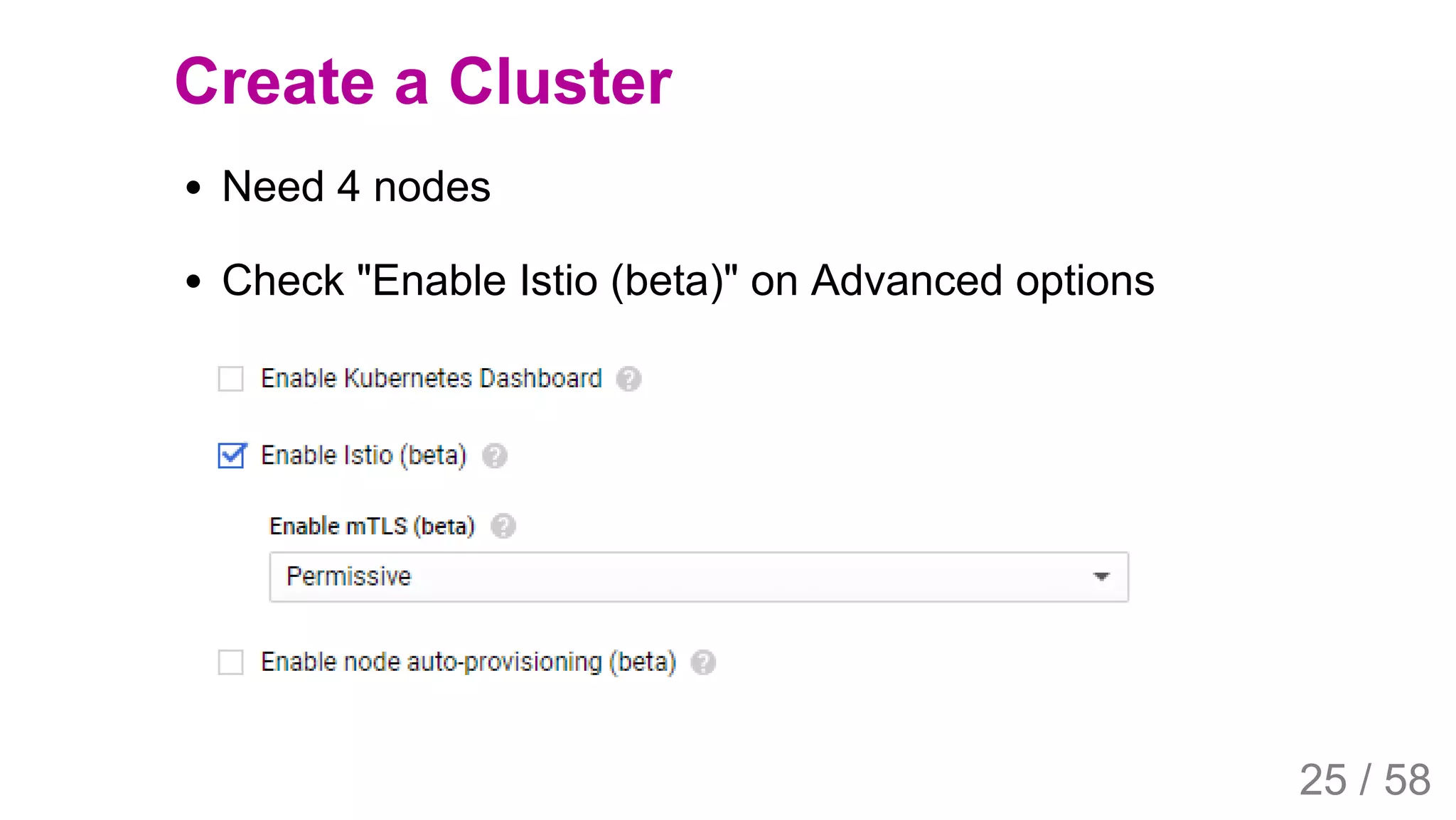
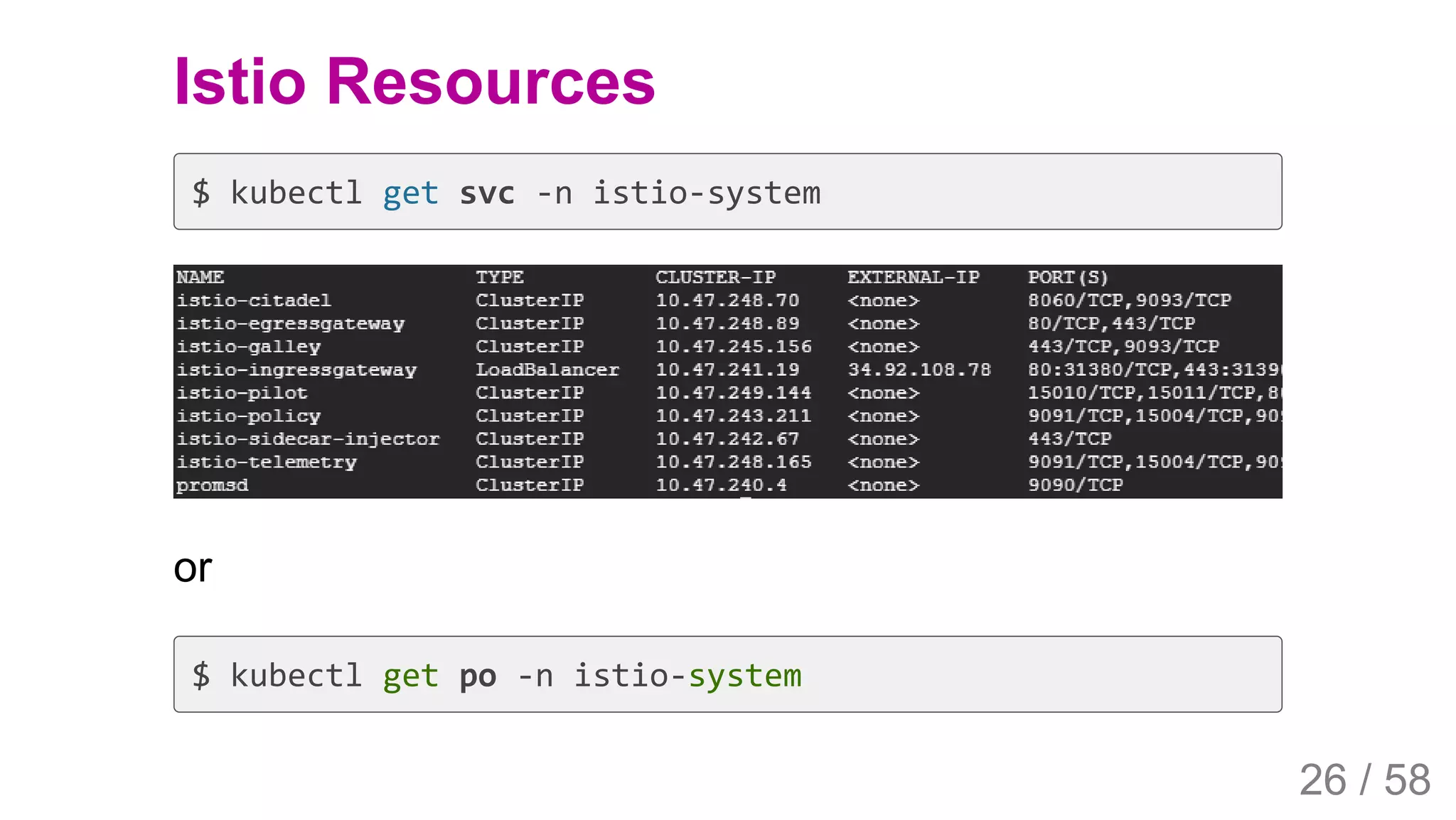
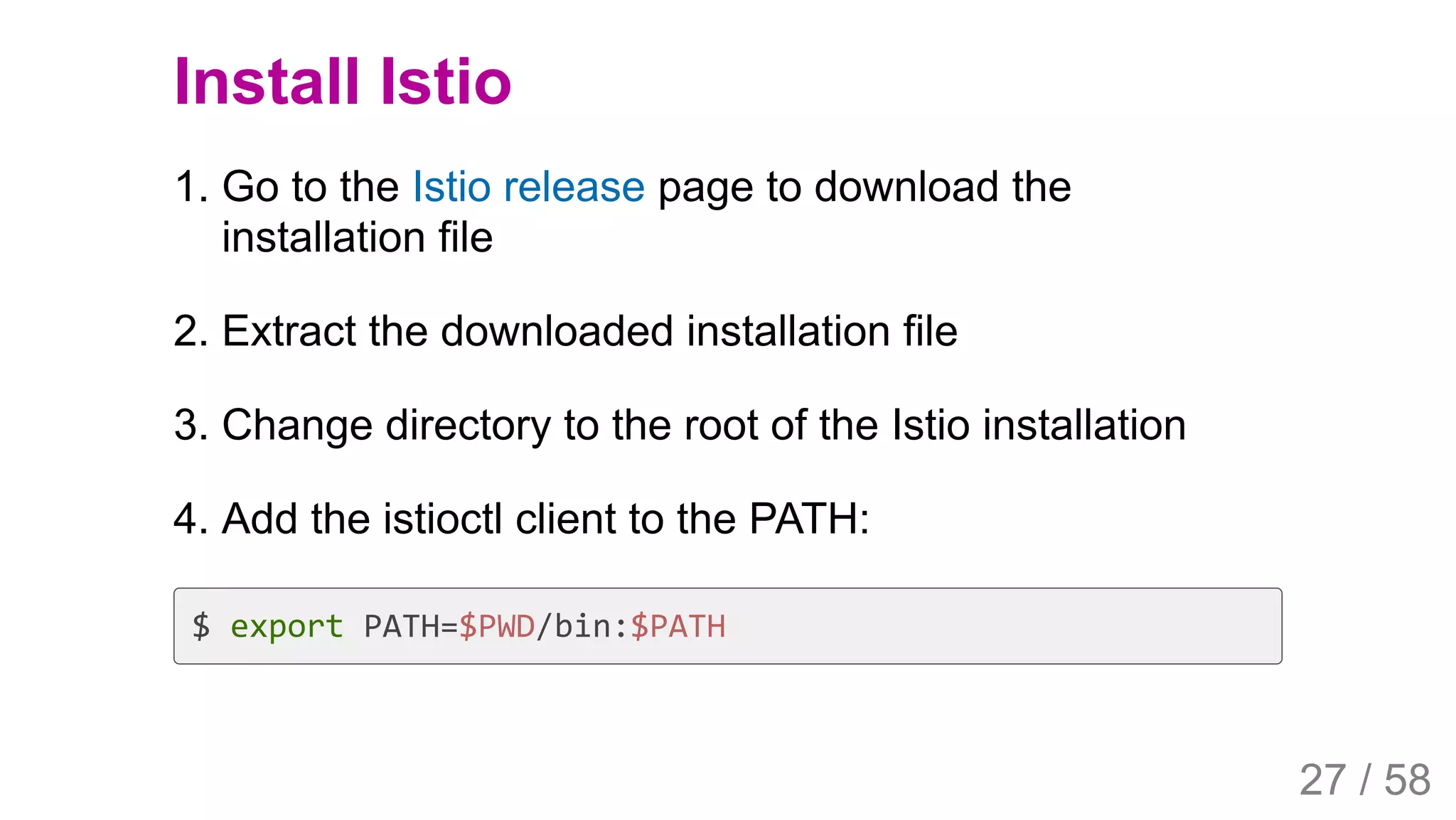
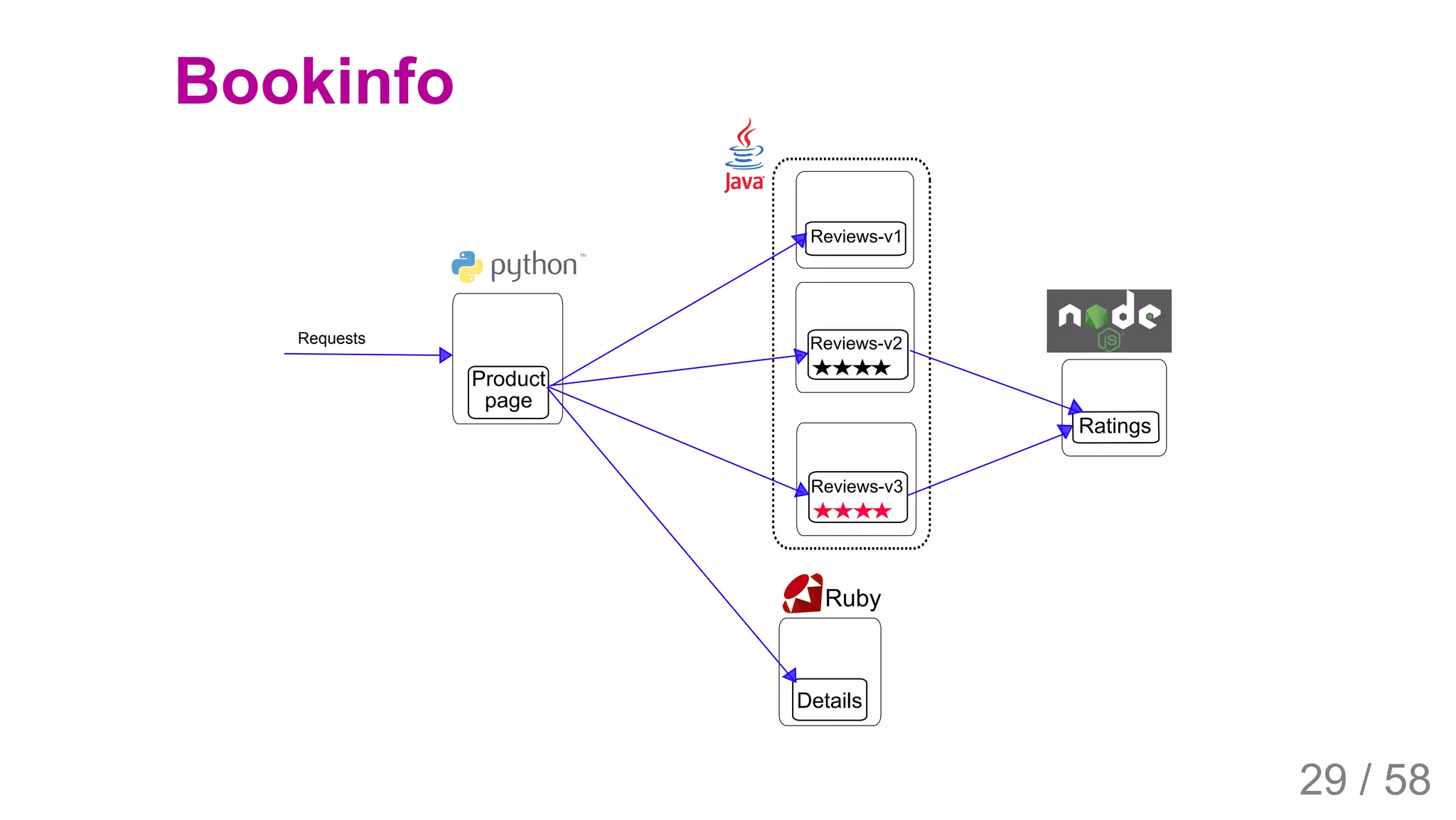
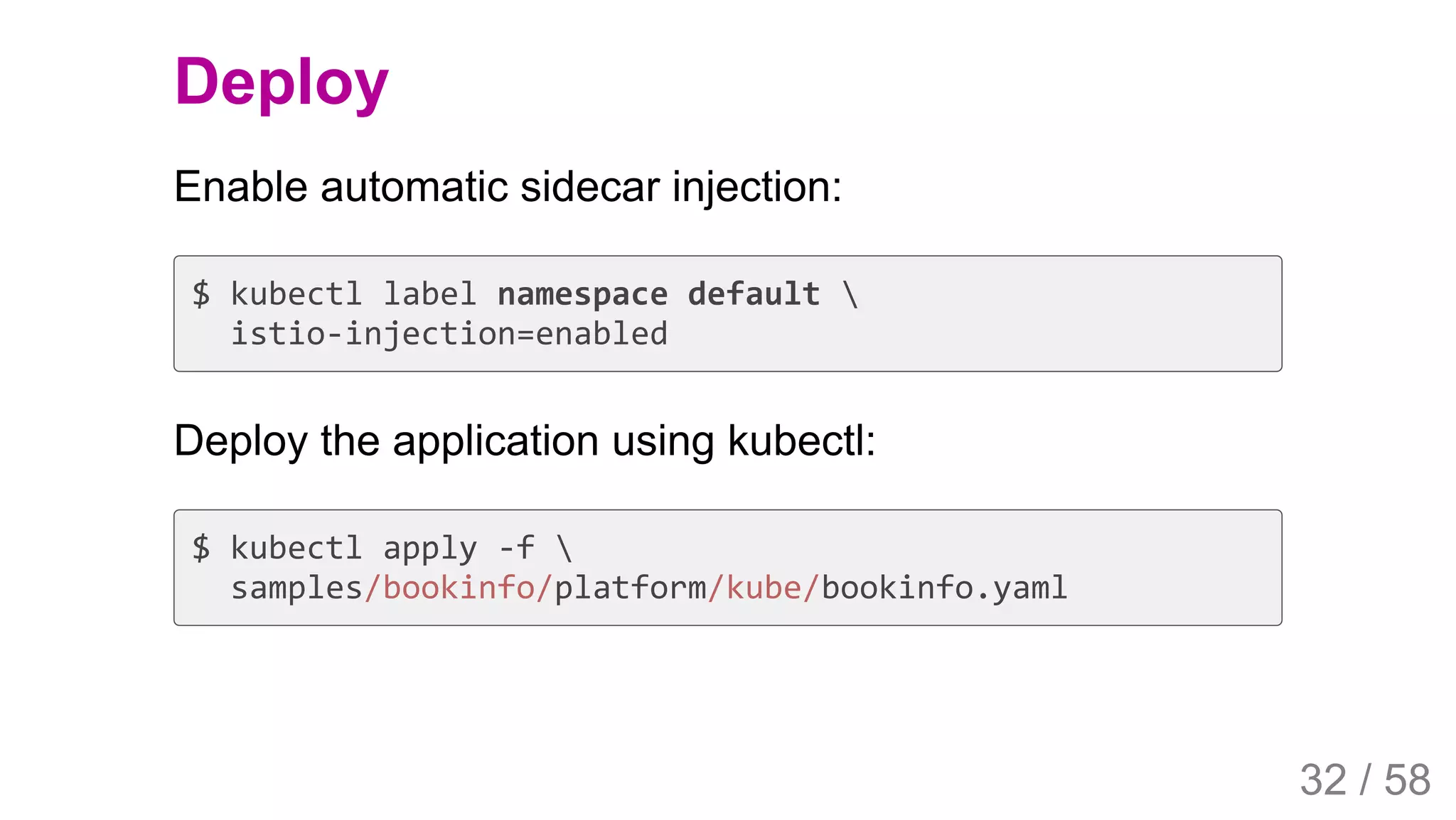
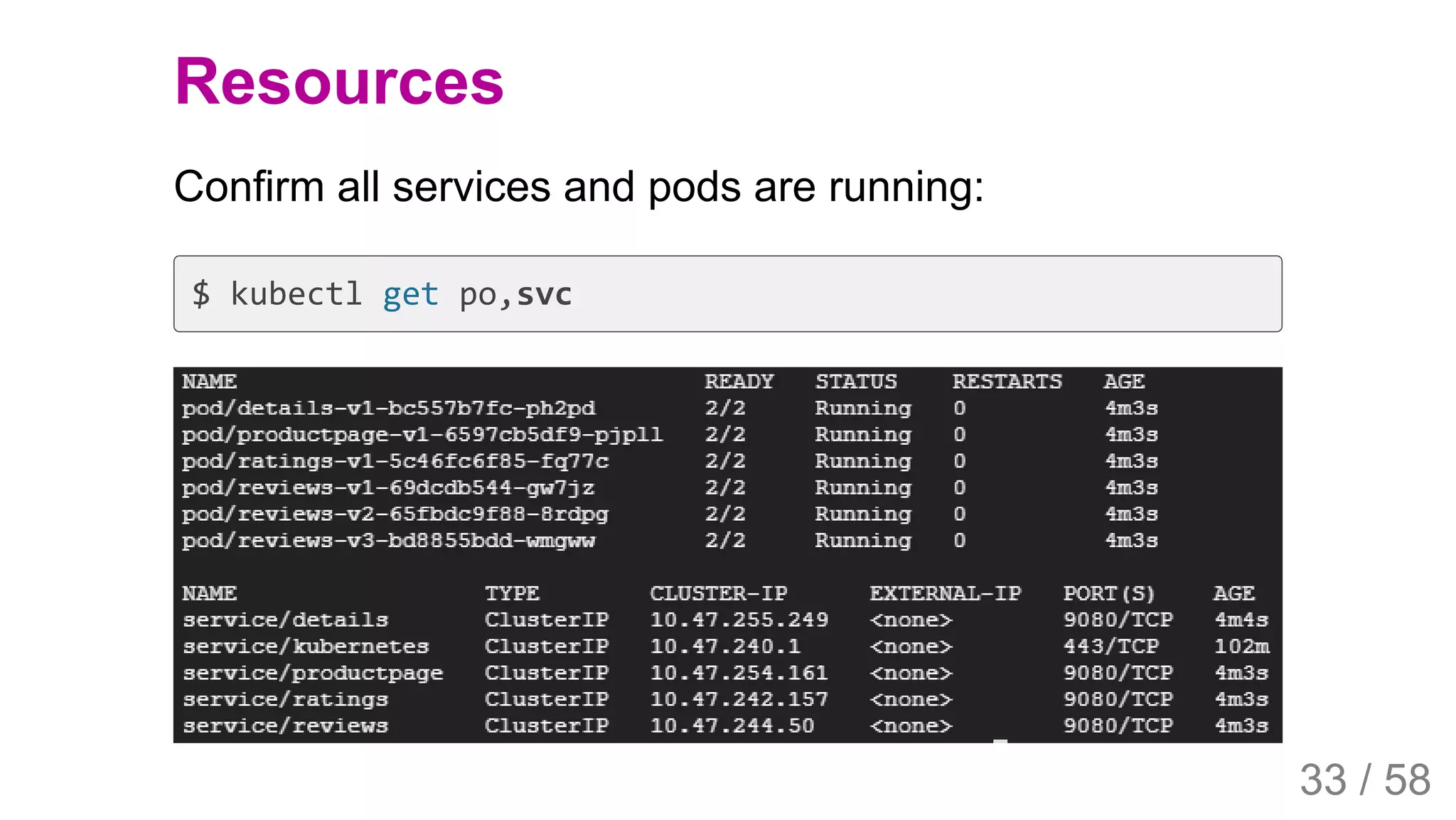
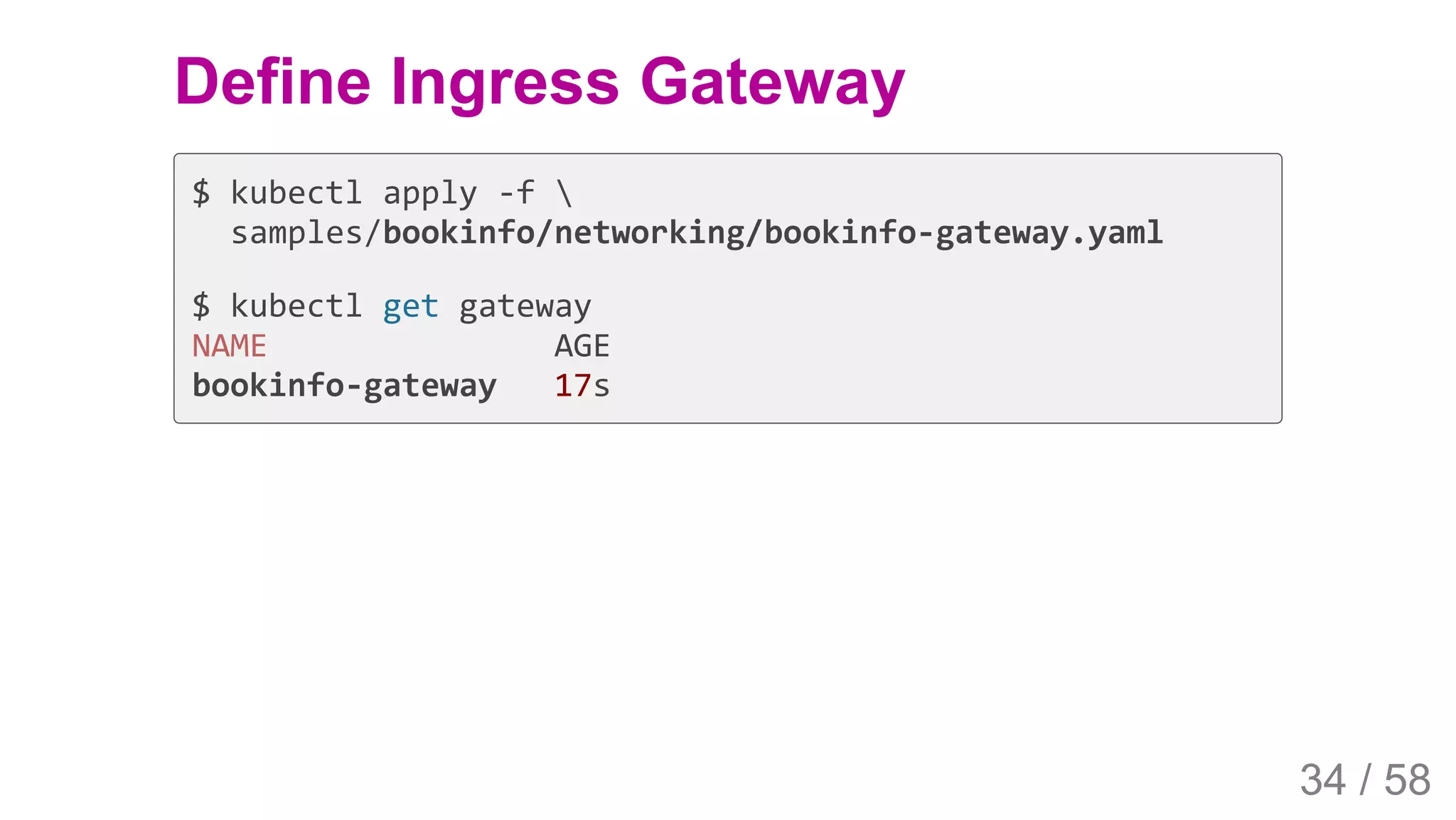
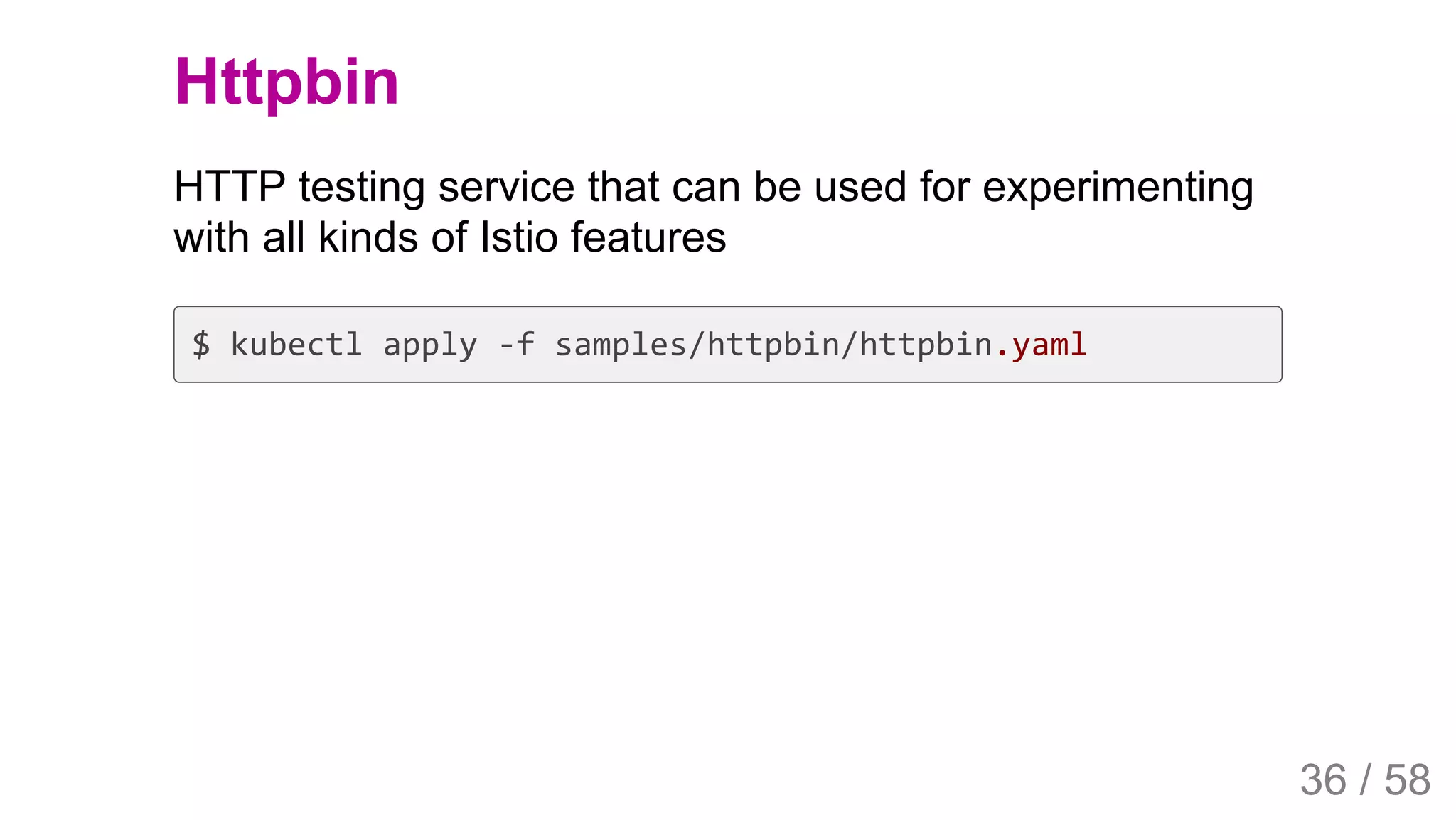
The document discusses Istio, an open source service mesh that provides traffic management, service migration and monitoring for microservices. It provides an overview of key Istio concepts like the control plane, data plane and components like Envoy, Pilot and Mixer. It also includes steps to install Istio on GKE and deploy a sample Bookinfo application to demonstrate traffic routing and load balancing capabilities.




![2019/4/4 Istio Service Mesh Introduction
127.0.0.1:5500/#54 37/58
Set variables
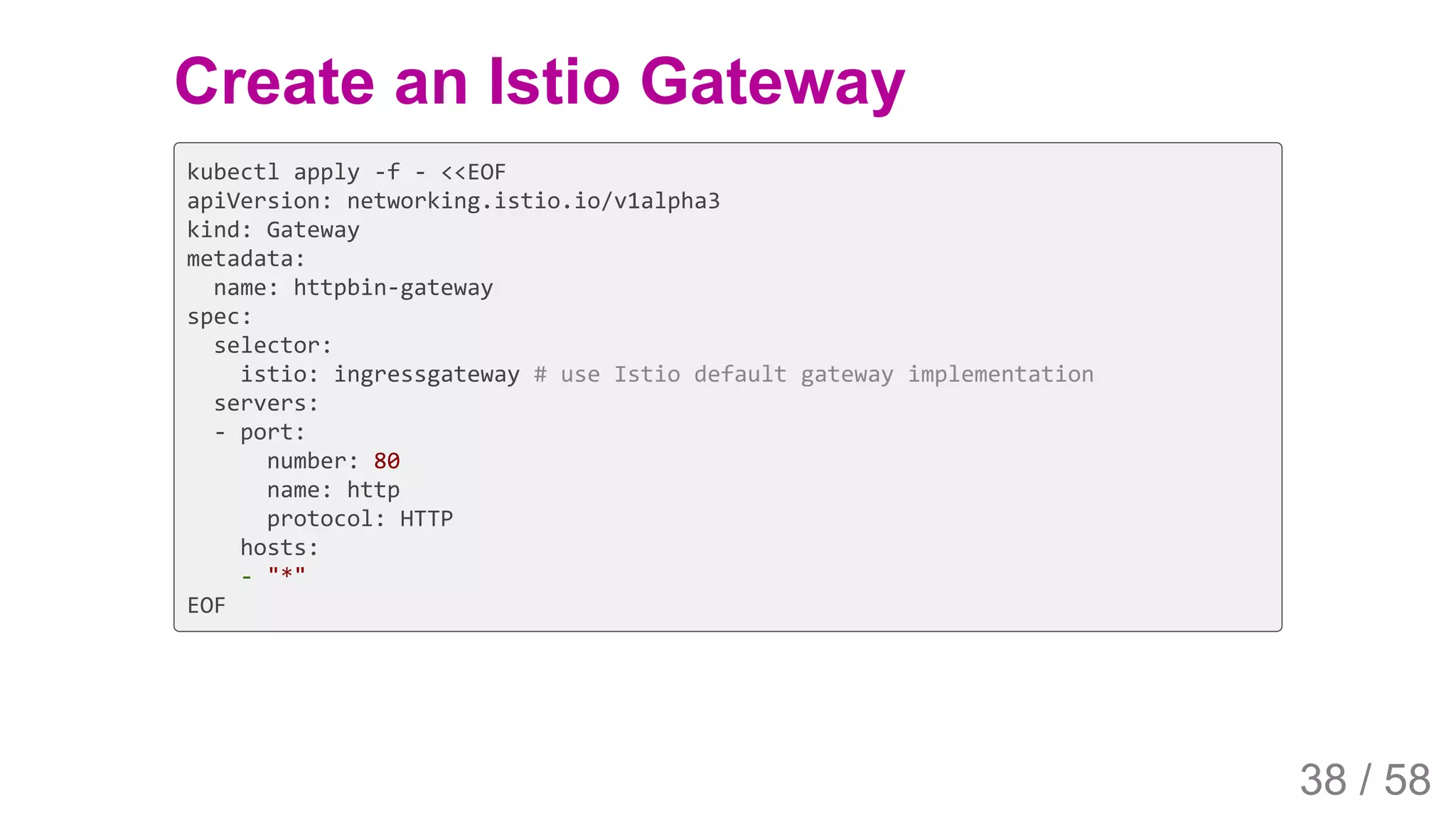
Set the ingress IP and ports:
$ export INGRESS_HOST=$(kubectl -n istio-system get service istio-ingressgateway
-o jsonpath='{.status.loadBalancer.ingress[0].ip}')
$ export INGRESS_PORT=$(kubectl -n istio-system get service istio-ingressgateway
-o jsonpath='{.spec.ports[?(@.name=="http2")].port}')
$ export SECURE_INGRESS_PORT=$(kubectl -n istio-system get service
istio-ingressgateway -o jsonpath='{.spec.ports[?(@.name=="https")].port}')
37 / 58](https://image.slidesharecdn.com/istioservicemeshintroduction-190513084053/75/Istio-service-mesh-introduction-37-2048.jpg)