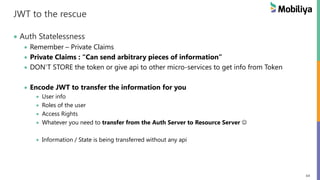
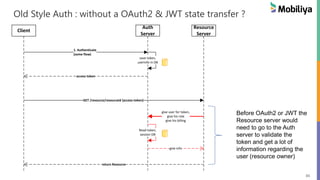
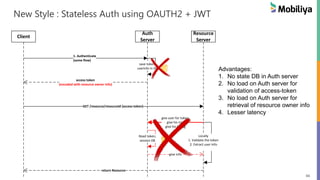
The document discusses stateless authentication using OAuth2 and JWT, explaining the concepts of authentication, authorization, and single sign-on (SSO). It provides an in-depth look at OAuth2, detailing its actors, various grant flows, and the implementation of JWT as a token standard for secure authorization. Additionally, it outlines how to implement OAuth2 services, the differences between grant types, and the necessary setup for stateless authorization.




![21
Setup of OAuth2 [one time setup]
Client (App) Registration
One time only, for every Client App.
Usually a registration form in the developer or API section of AuthServer website
Client App will provide following to Auth Server (or more)
1. App Name [shows resource owner]
2. App Website URI
3. Redirect URI
Auth Server will provide following to Client
1. Client Id [publicly exposed]
2. Client Secret [should be protected]](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-21-320.jpg)
![22
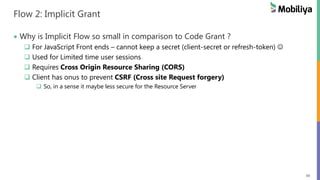
Authorization Grant Flows [daily operation]
4 Types of Grant Flows/Types Available for OAuth2 [can support one/more]
1. Authorization Code Grant
2. Implicit Grant
3. Resource Owner Credentials
4. Client Credentials](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-22-320.jpg)
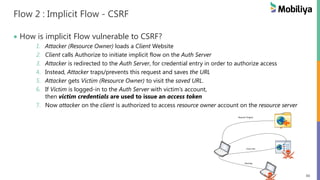
![23
OH GOD! Which Grant Flow to use When?
Cheat Sheet [guideline, not a MUST]
Auth Code Grant: 3rd Party or Web Server Apps
Implicit: 3rd Party Mobile / Web Apps (no backend)
Resource Owner Creds: Apps owned by the Auth Server company
Client Credentials: NO UI Backend - Micro-services API Access](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-23-320.jpg)

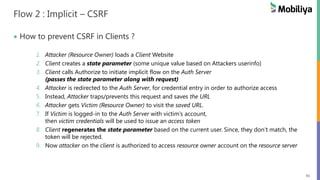
![26
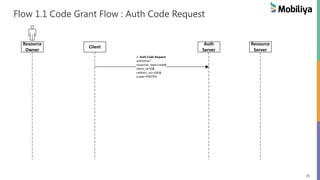
Flow 1.1 Code Grant Flow : Auth Code Request
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
response_type = code
[indicates the Auth Code Grant Flow]](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-26-320.jpg)
![27
Flow 1.1 Code Grant Flow : Auth Code Request
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
client_id = id
[which client app is initiating the flow
client id received in setup flow]](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-27-320.jpg)
![28
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
Flow 1.1 Code Grant Flow : Auth Code Request
redirect_uri = uri
[user is redirected to this uri after
authentication – success or failure]](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-28-320.jpg)
![29
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
Flow 1.1 Code Grant Flow : Auth Code Request
scope = PHOTOS
[level of access, app is trying to access]](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-29-320.jpg)
![30
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
2. SHOW Login & Consent Pages
[accept user creds]
[scope and app approval from user]
Flow 1.2 Code Grant Flow : User Consent
Auth server
1. Validates User Creds
2. Takes Consent on Client + Scope](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-30-320.jpg)
![31
Flow 1.2 : Code Grant Flow : User Consent
Deciphered
from Client ID
Deciphered
from Scope
User Consent
[will typically look like this]](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-31-320.jpg)
![32
Flow 1.3 : Code Grant Flow : Auth Code
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authserver/authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
2. SHOW Login & Consent Pages
[accept user creds]
[scope and app approval from user]
OK
3. redirect_uri/?code=AUTHORIZATION_CODE
Auth server
1. Sends “Auth Code” to the Client
(super-limited time code)
2. Contents of Code – can be anything](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-32-320.jpg)
![33
Flow 1.4 : Code Grant Flow : Access Token Request
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authserver/authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
2. SHOW Login & Consent Pages
[accept user creds]
[scope and app approval from user]
OK
3. redirect_uri/?code=AUTHORIZATION_CODE
4. Access Token Request
authserver/oauth/token?
client_id=CLIENT_ID&
client_secret=CLIENT_SECRET&
grant_type=authorization_code&
code=AUTHORIZATION_CODE&
redirect_uri=CALLBACK_URL
Access Token Request
1. Code – identifies – scope, user, client
2. Client ID/Secret – identifies the client](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-33-320.jpg)
![34
3. Get Resource (access-token)
4. Resource
Flow 1.5 : Code Grant Flow : Access Token + Refresh Token
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Code Request
authserver/authorize?
response_type=code&
client_id=ID&
redirect_uri=URL&
scope=PHOTOS
2. SHOW Login & Consent Pages
[accept user creds]
[scope and app approval from user]
OK
3. redirect_uri/?code=AUTHORIZATION_CODE
4. Access Token Request
authserver/oauth/token?
client_id=CLIENT_ID&
client_secret=CLIENT_SECRET&
grant_type=authorization_code&
code=AUTHORIZATION_CODE&
redirect_uri=CALLBACK_URL
5. token Transfer
{"access_token", "refresh_token"
,"scope":"read","
"info":{auth server defined user info}}
1. Access Token : Token to access api
2. Refresh Token : Token to refresh
access token on expiry
• Refresh token is optional and
MUST not be decode-able](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-34-320.jpg)

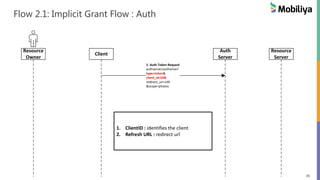
![37
Resource
Owner
Client
Auth
Server
Resource
Server
1. Auth Token Request
authserver/authorize?
type=token&
client_id=ID&
redirect_uri=URI
&scope=photos2. SHOW Login & Consent Pages
[accept user creds]
[scope and app approval from user]
OK
3. token Transfer
{"access_token"}
3. Get Resource (access-token)
4. Resource
Flow 2.2 & 2.3: Implicit Grant Flow : Auth
1. Access token is transferred](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-37-320.jpg)

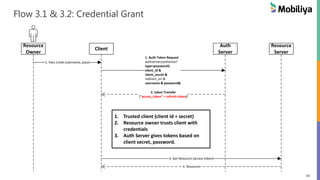
![43
Flow #3: Resource Owner Credentials
Only for really trusted clients [owned by Auth/Resource server]
For eq: Mobile Apps of a web service](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-43-320.jpg)
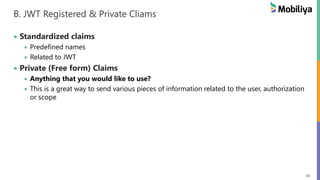
![55
B. JWT Claims / Payload
{ "iss":“oauth2.mobiliya.com",
“sub” : ”Roy’s Access-token”,
"exp":1300819380,
“iat” : 1300803380,
“nbf” : 1300803380,
“jti” : “8973-r38893-288346834”,
========================
“email” : roy@mobiliya.com,
“name” : “Gauav Roy”,
“access” : [ “photos”, “videos” ]
}
Registered Claims (predefined by JWT)
1. iss – Issuer?
2. sub – what is in this token?
3. exp – expires at?
4. iat – issued at
5. nbf – token not valid before
6. jti – jwt unique id
========================
Private claims
- Anything that the client, resource
server or auth server requires.
- Keep information regarding the user,
scope of the token, user attributes etc.](https://image.slidesharecdn.com/gauravroy-stateless-auth-using-oauth-and-jwt-170324063931/85/Stateless-Auth-using-OAUTH2-JWT-55-320.jpg)