Embed presentation
Download as PDF, PPTX
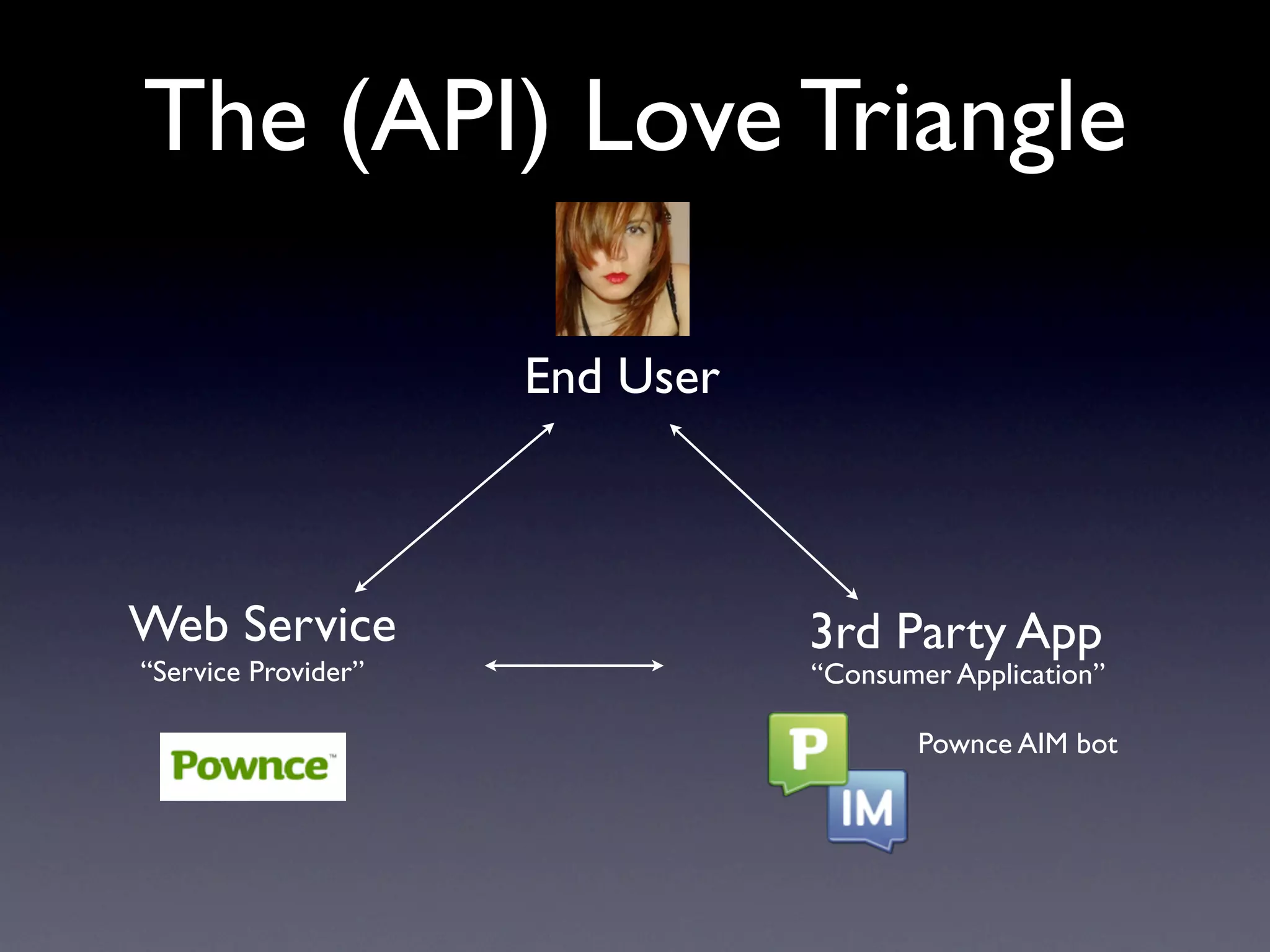

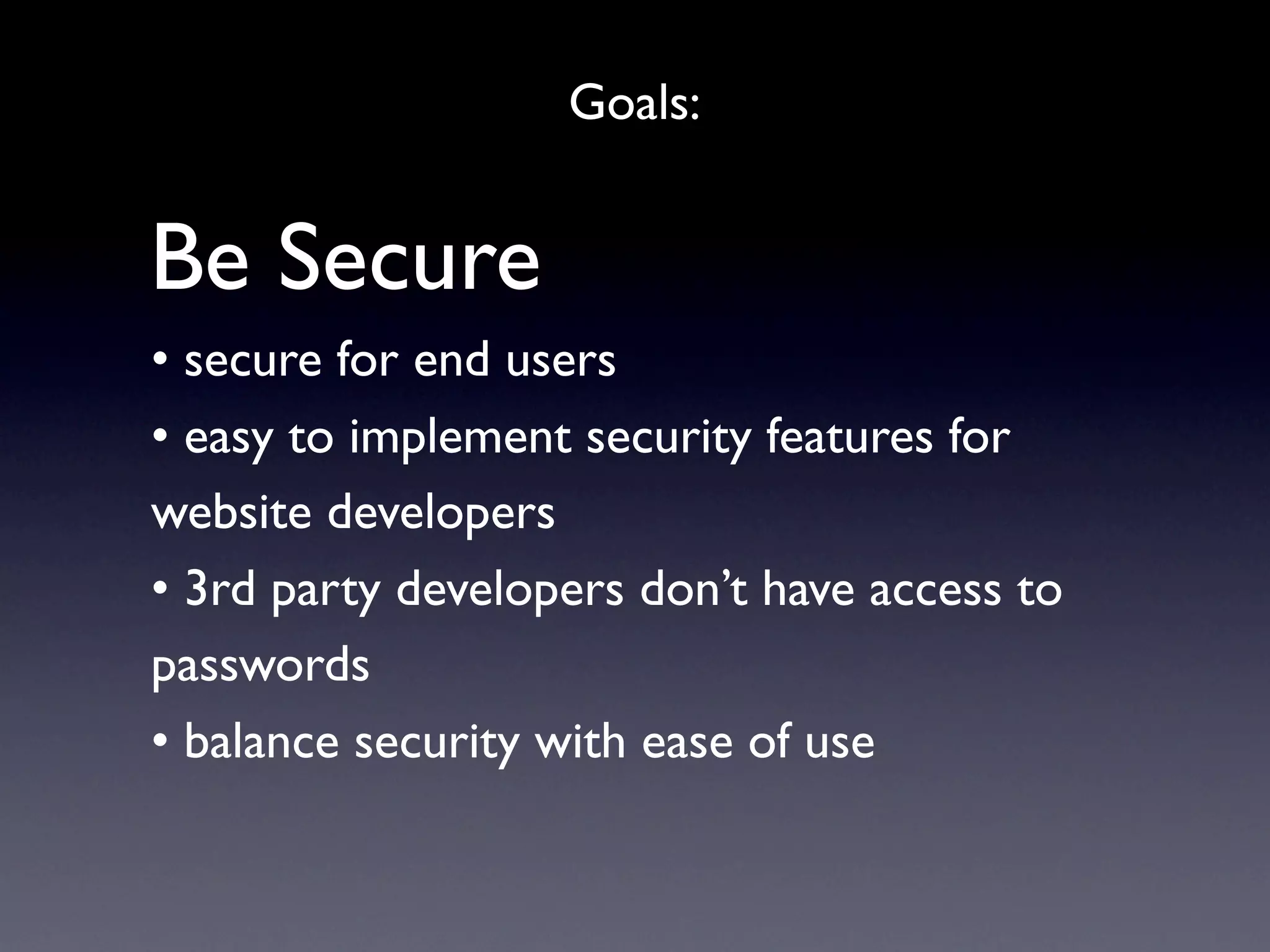
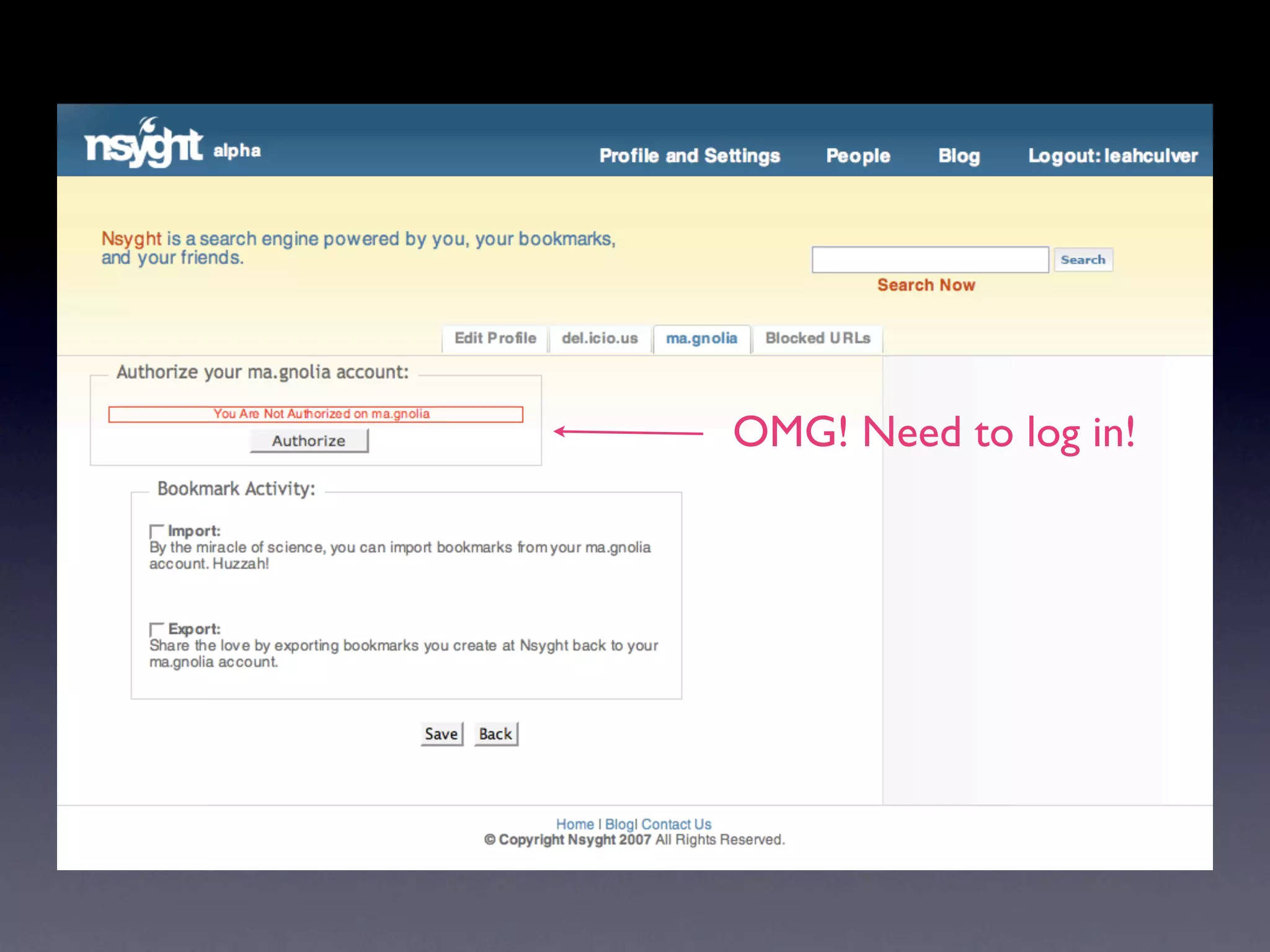


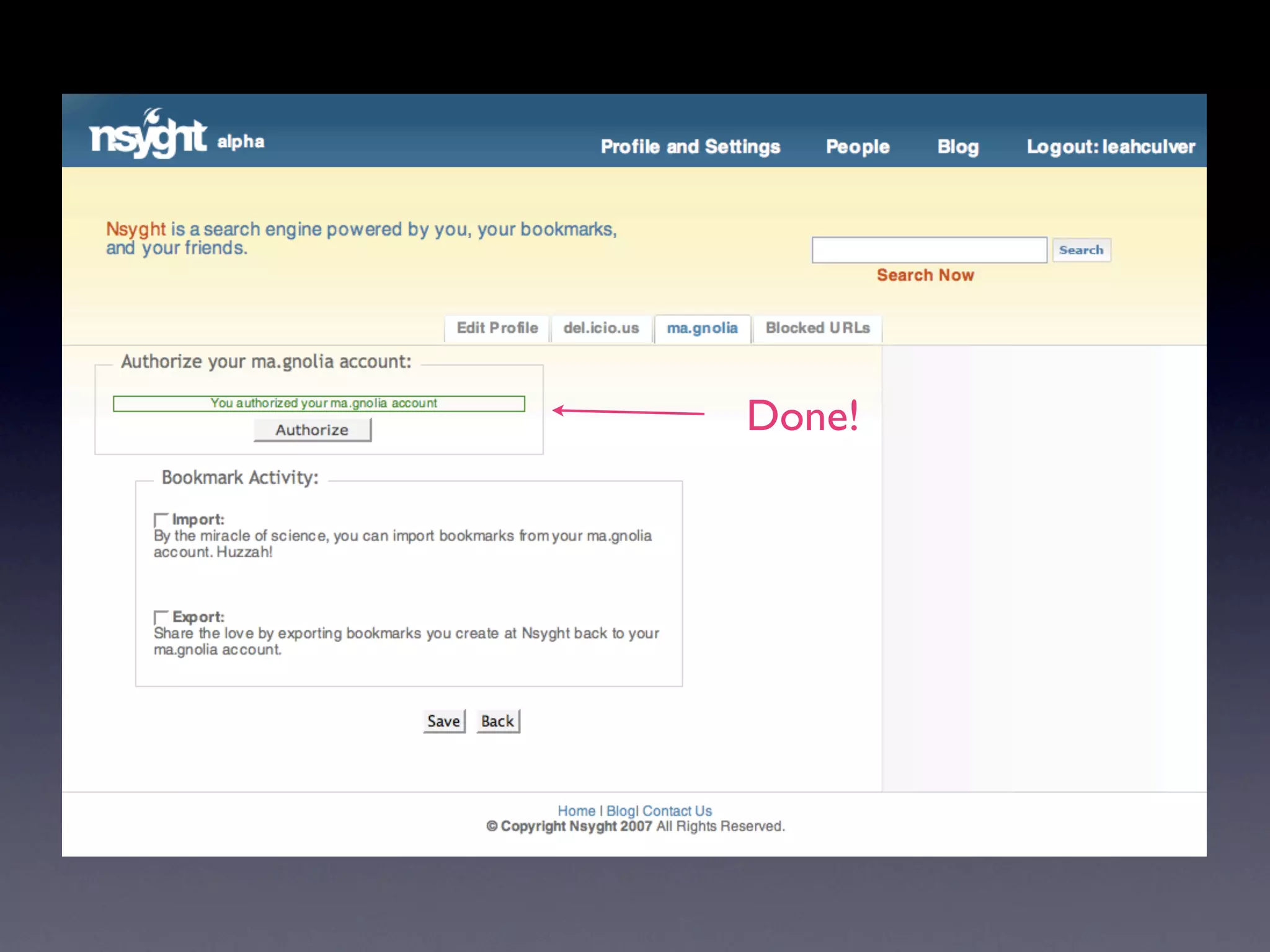
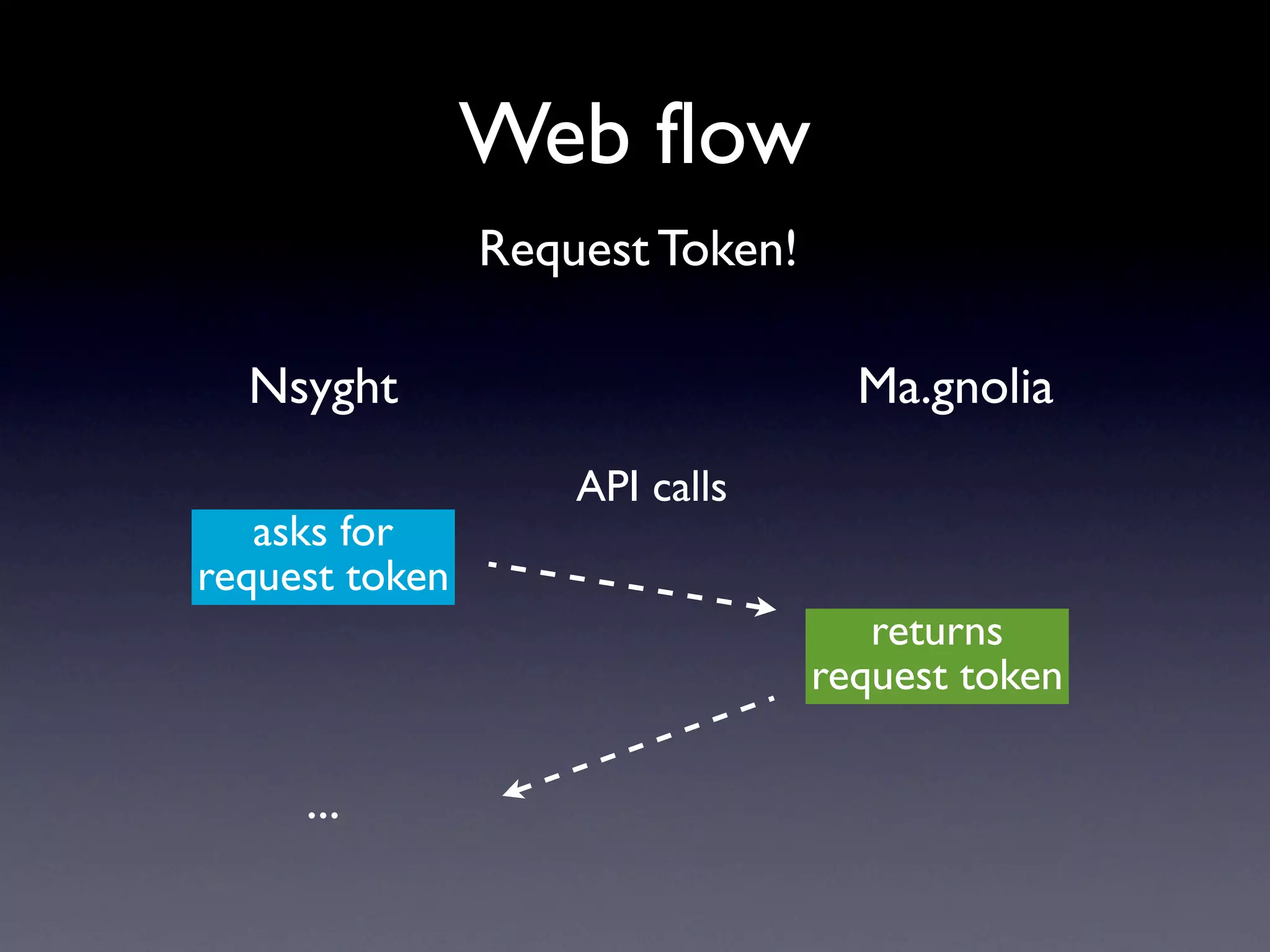
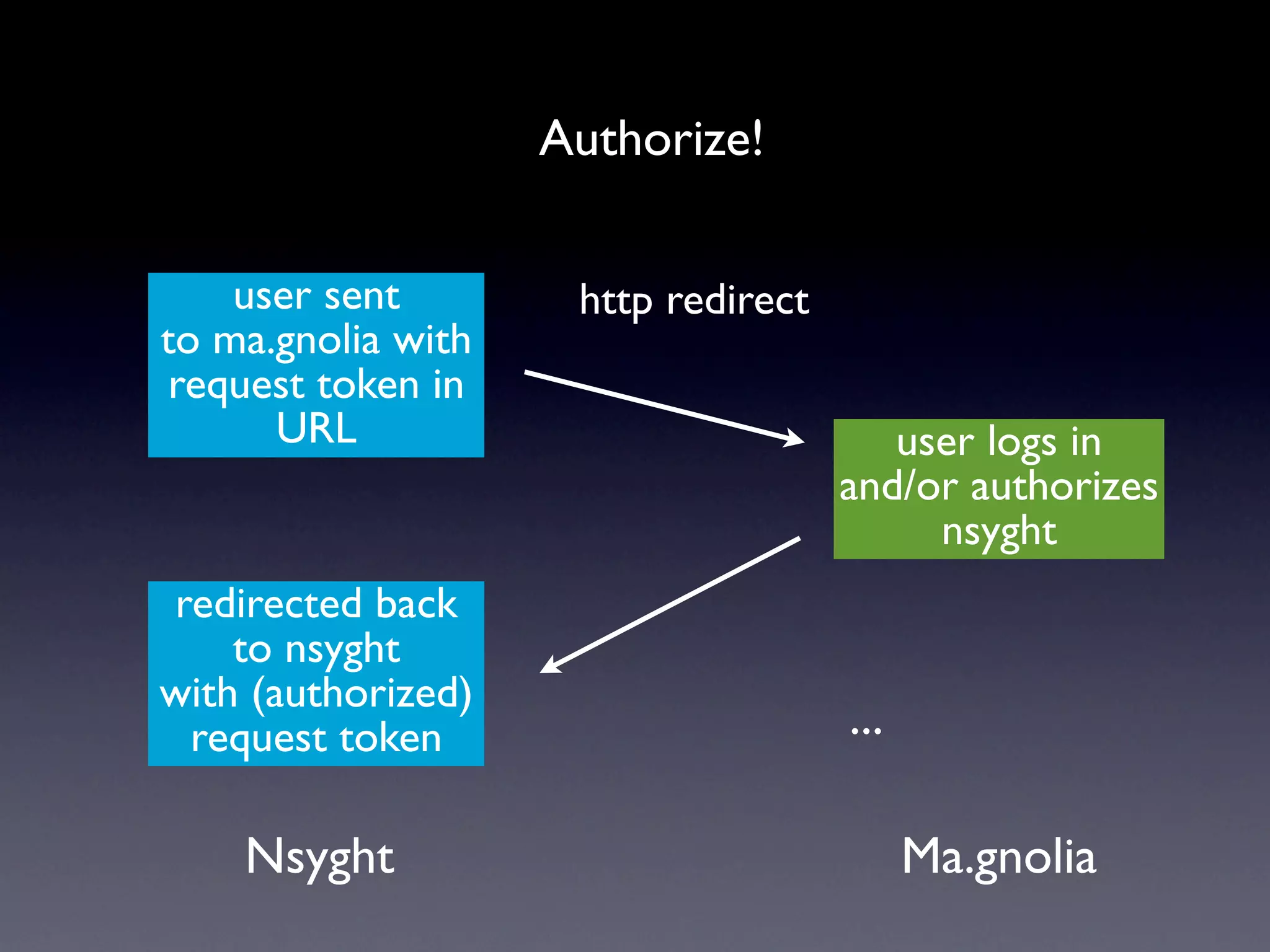
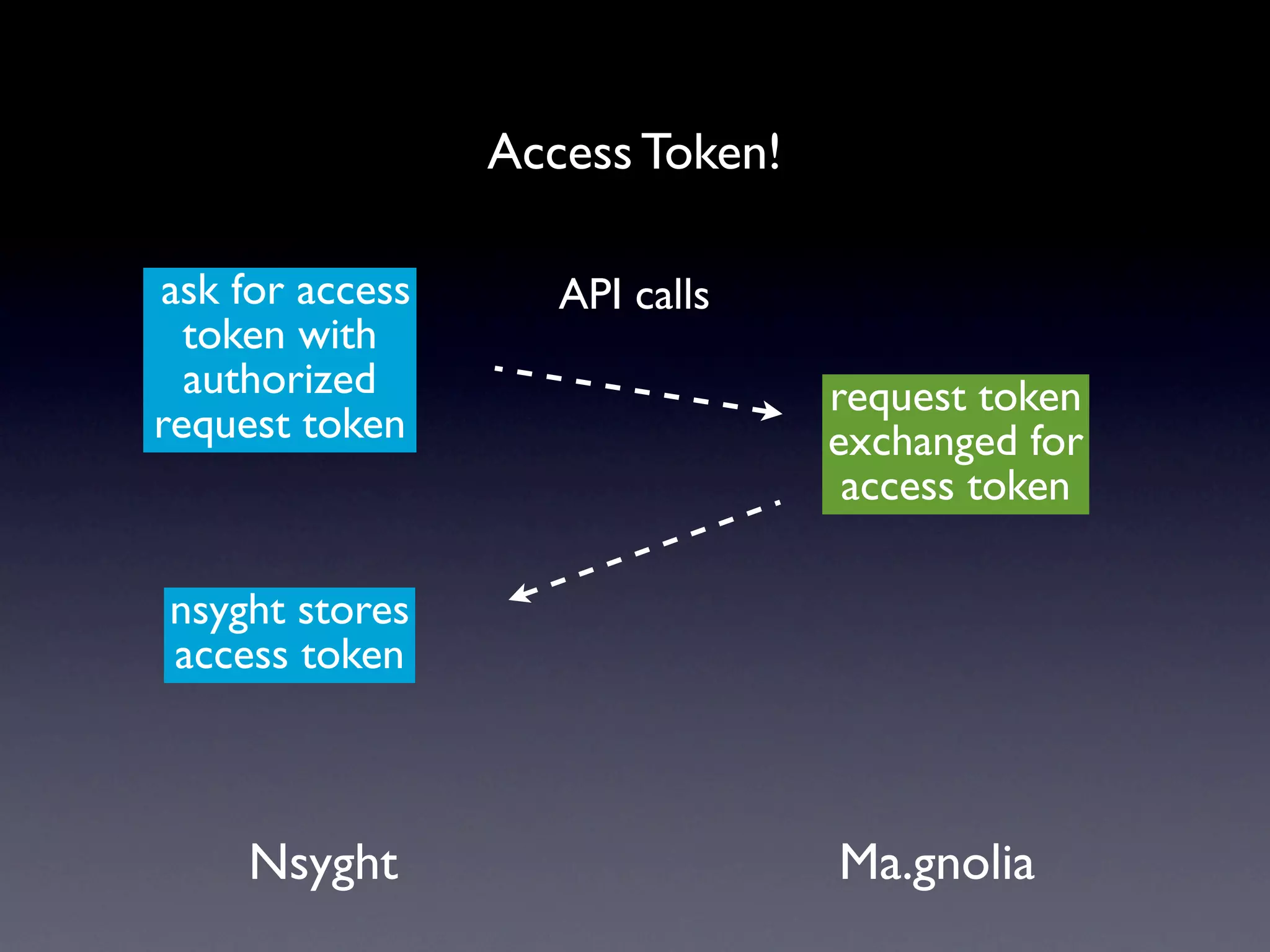
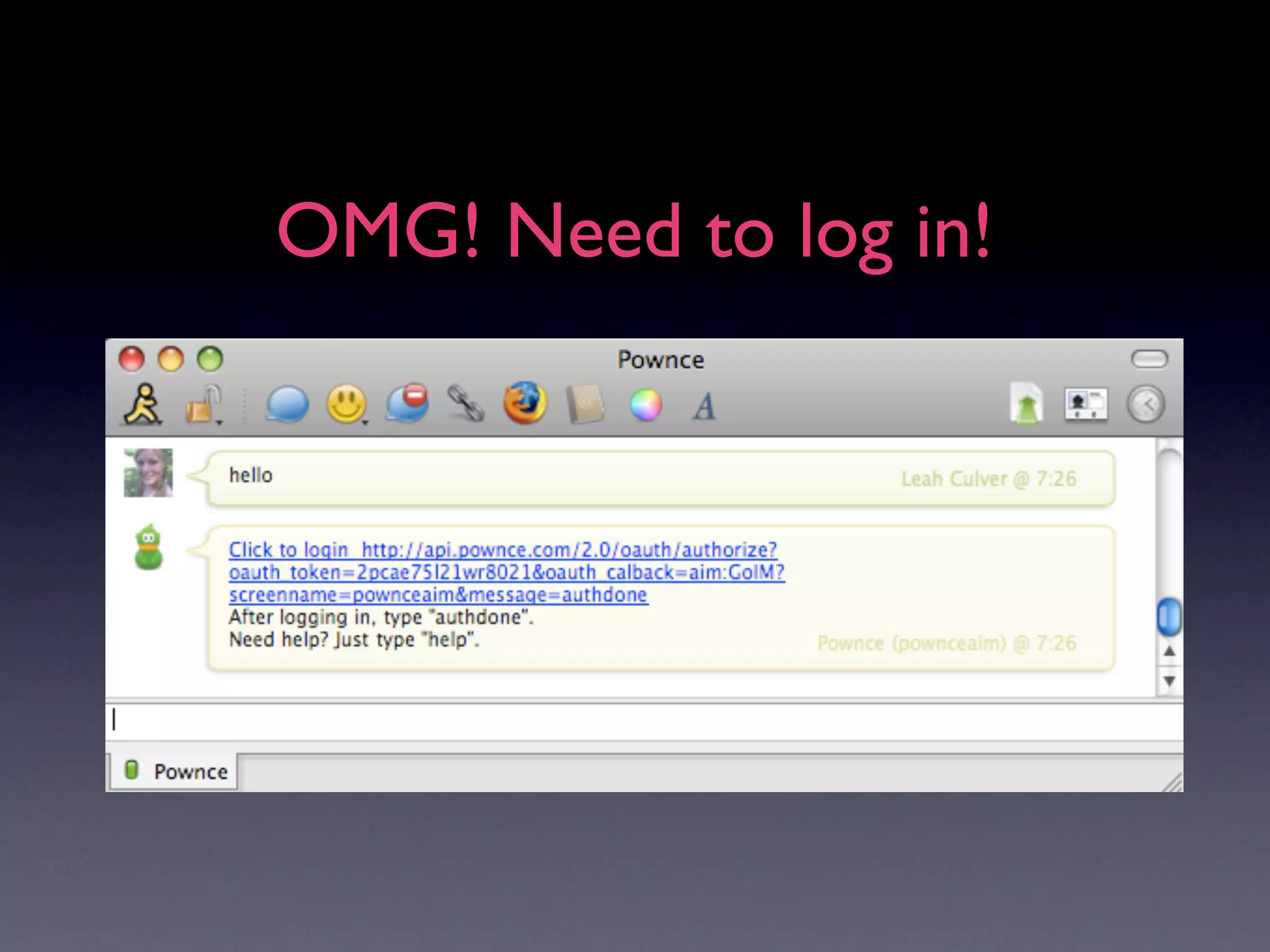
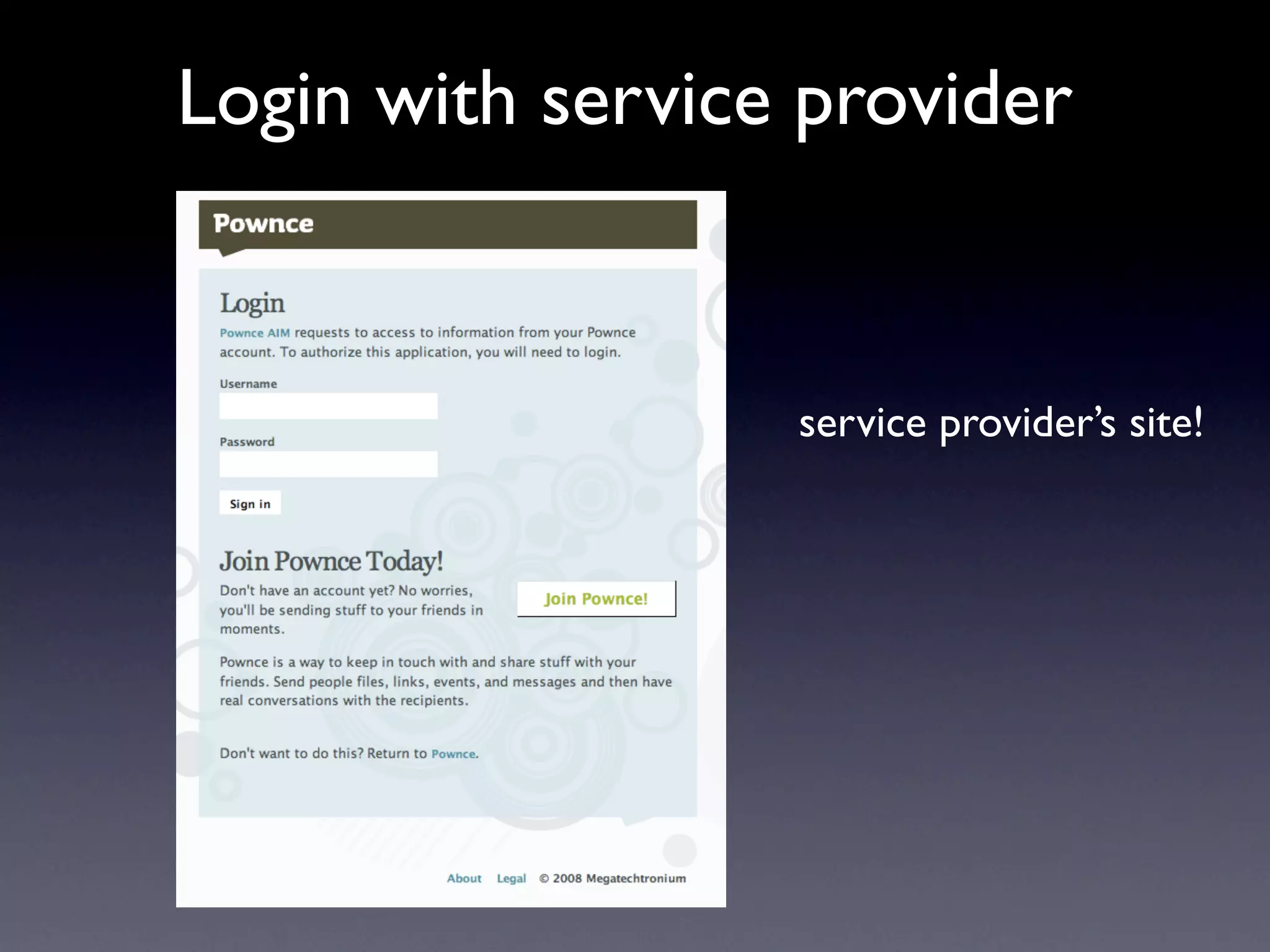
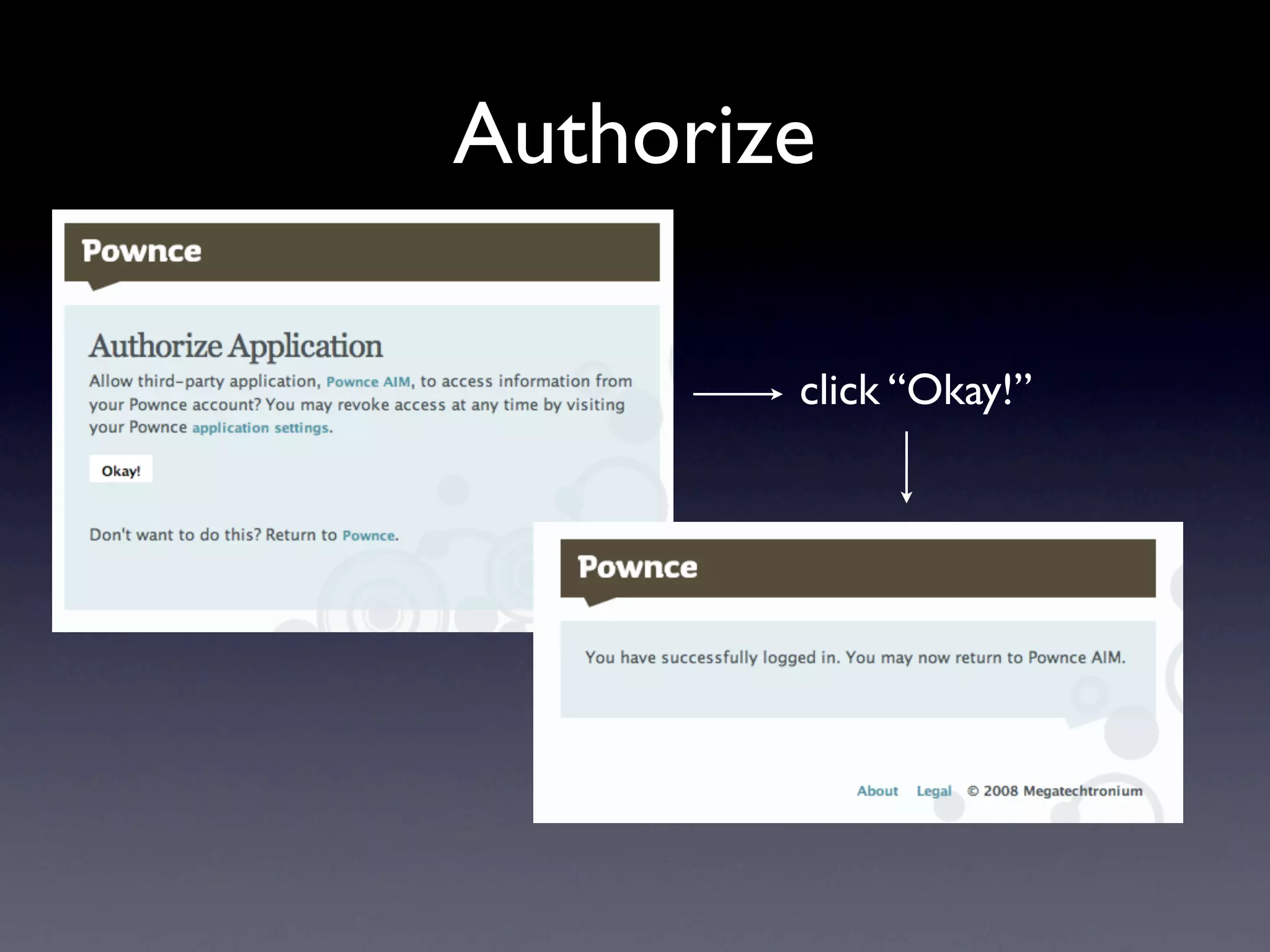
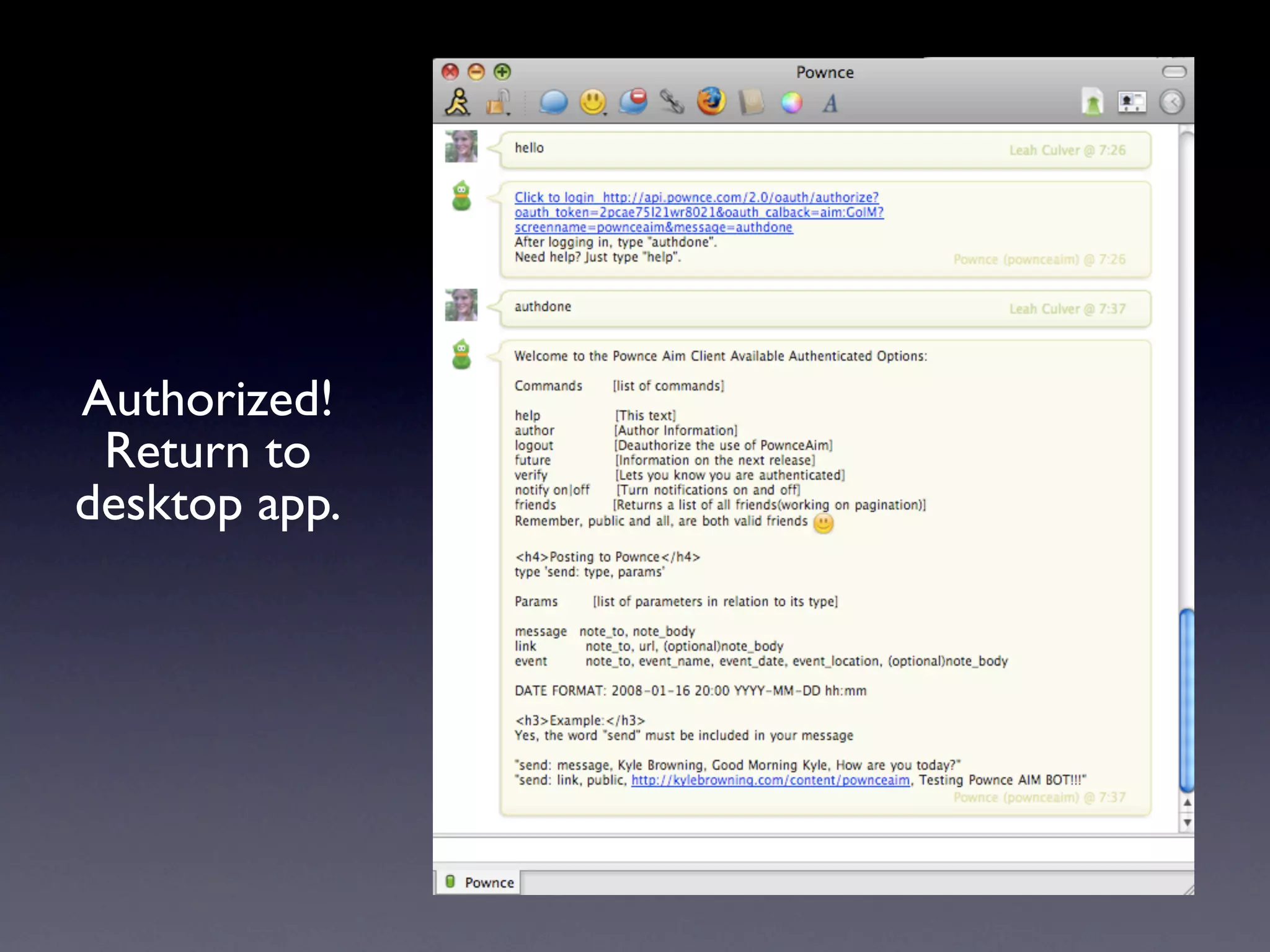
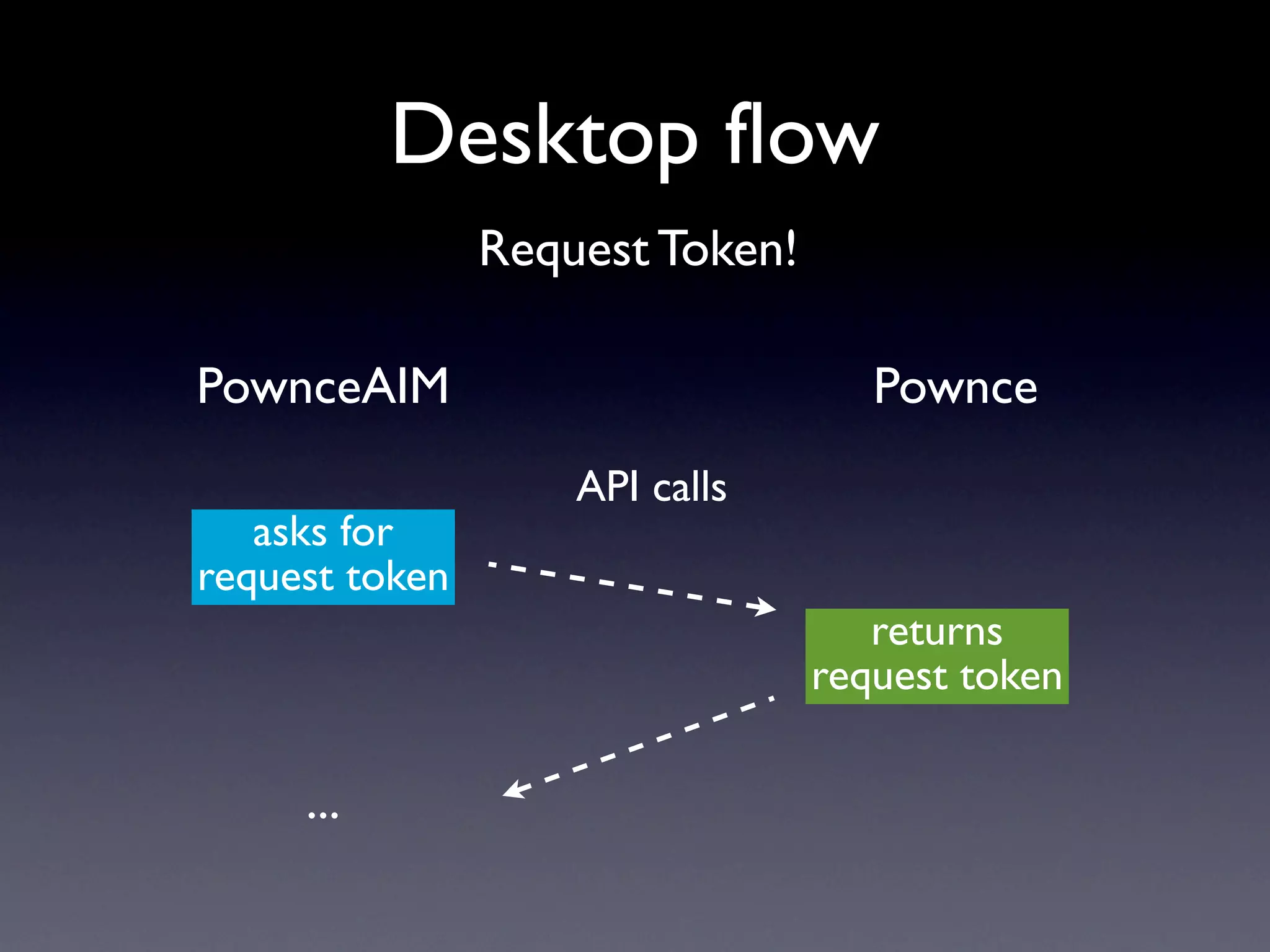
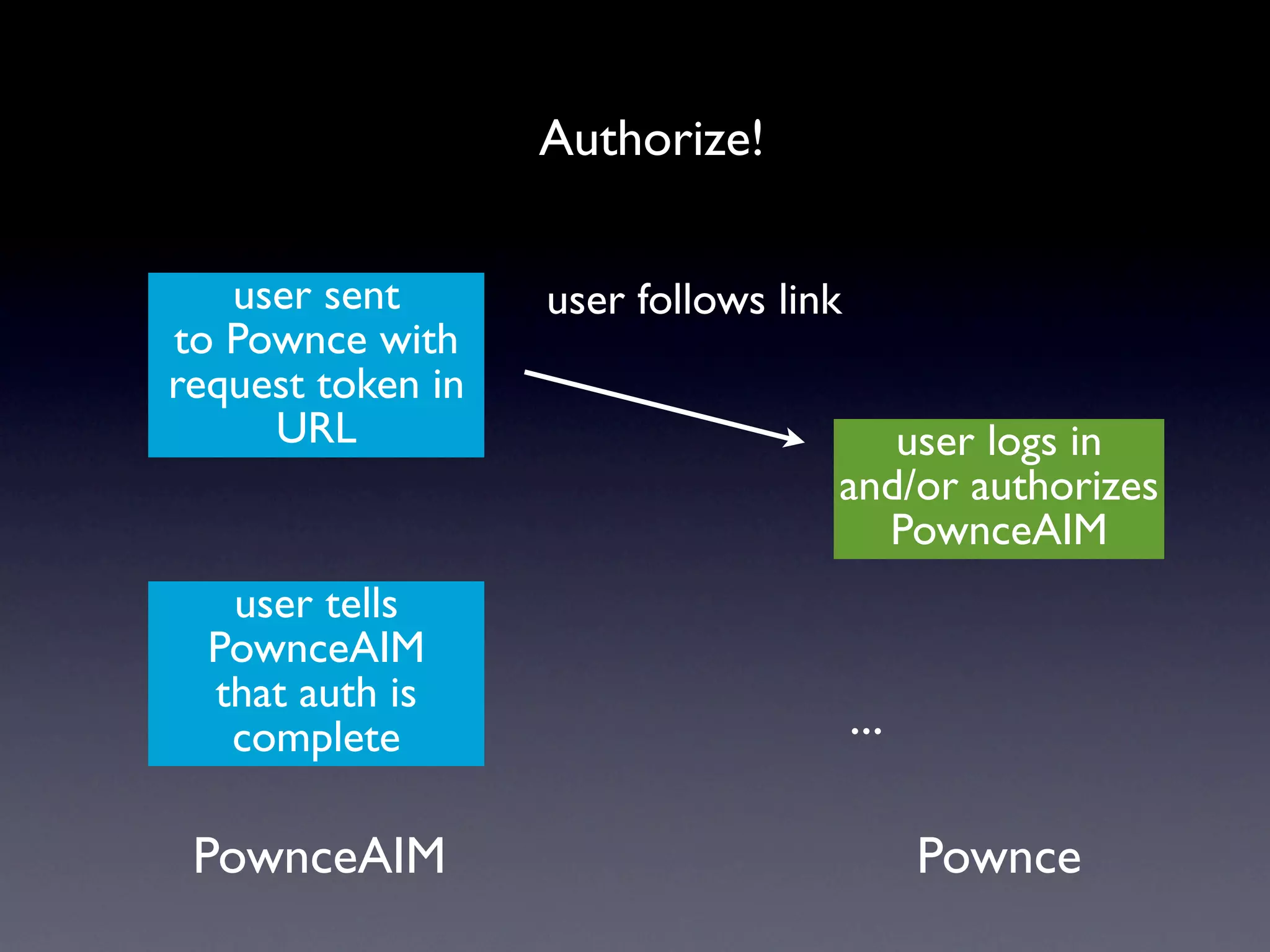
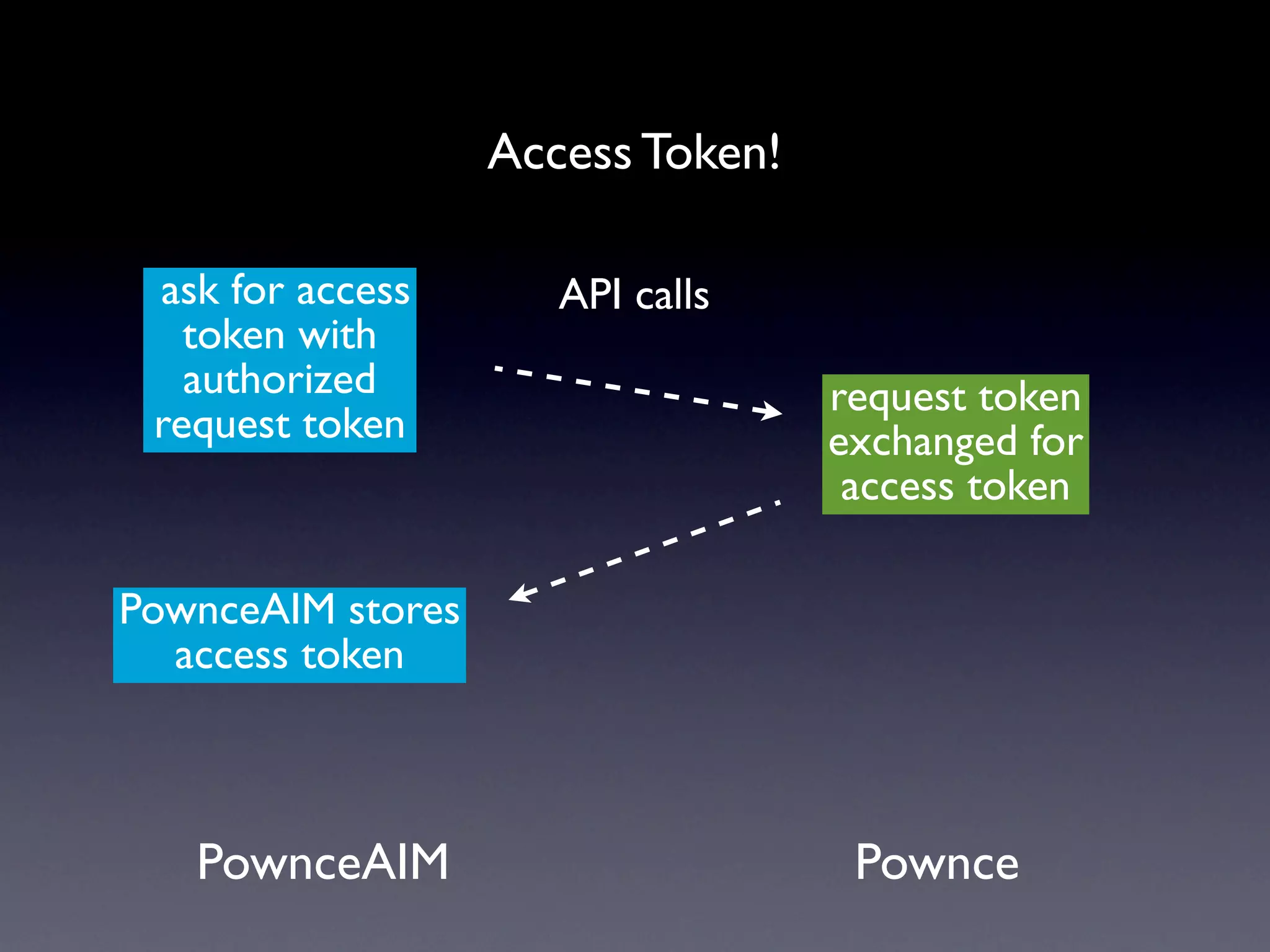
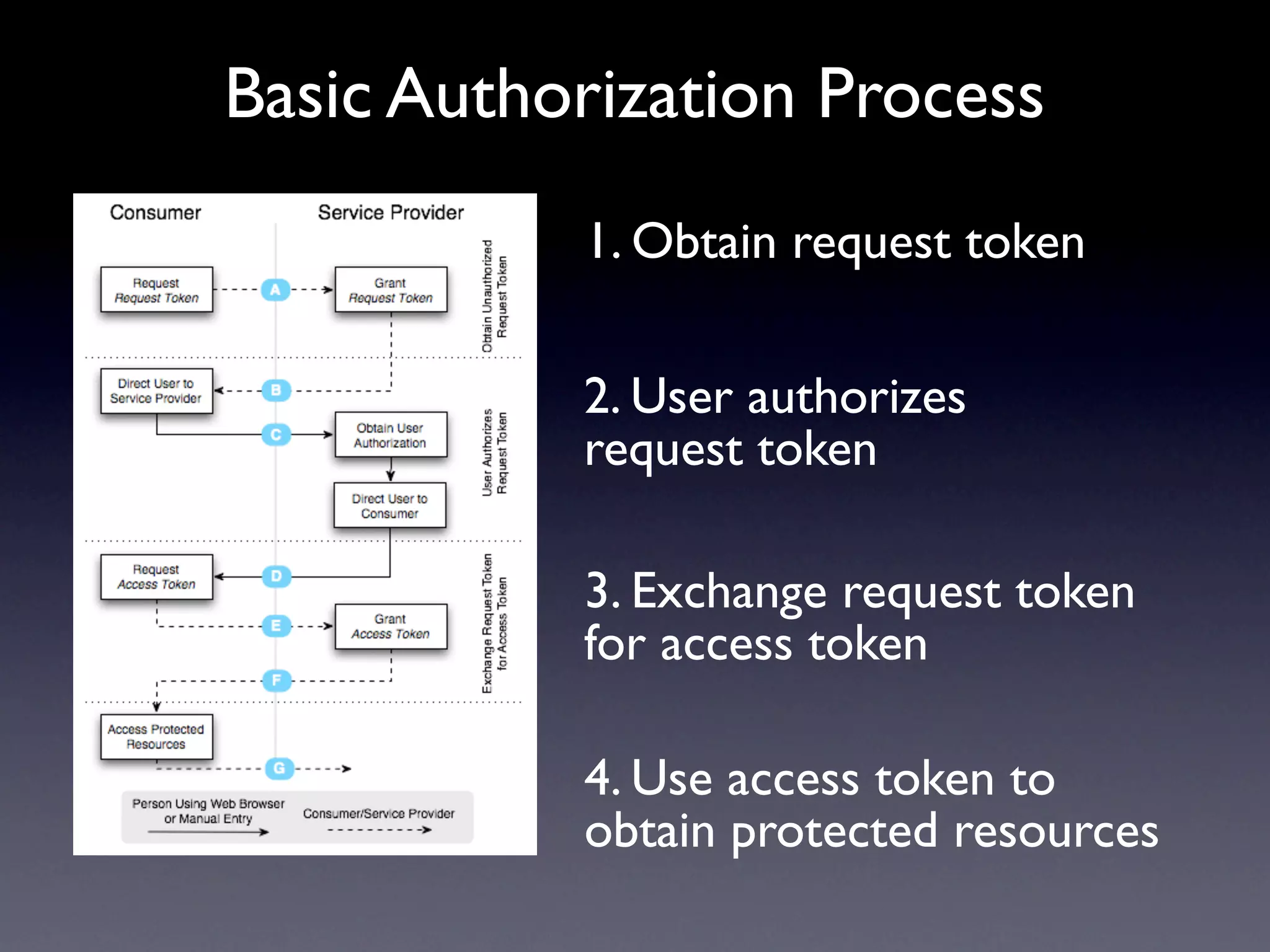
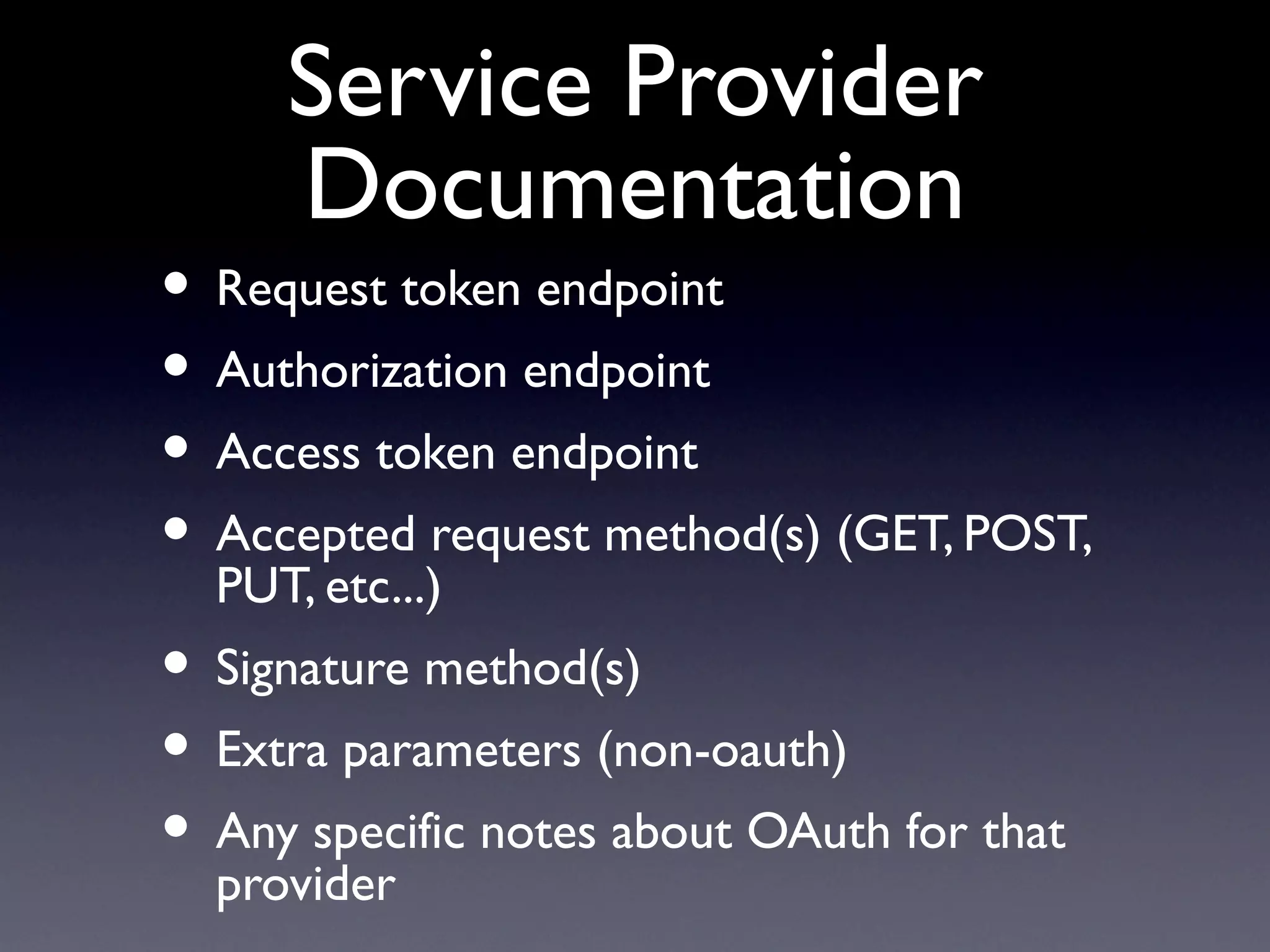
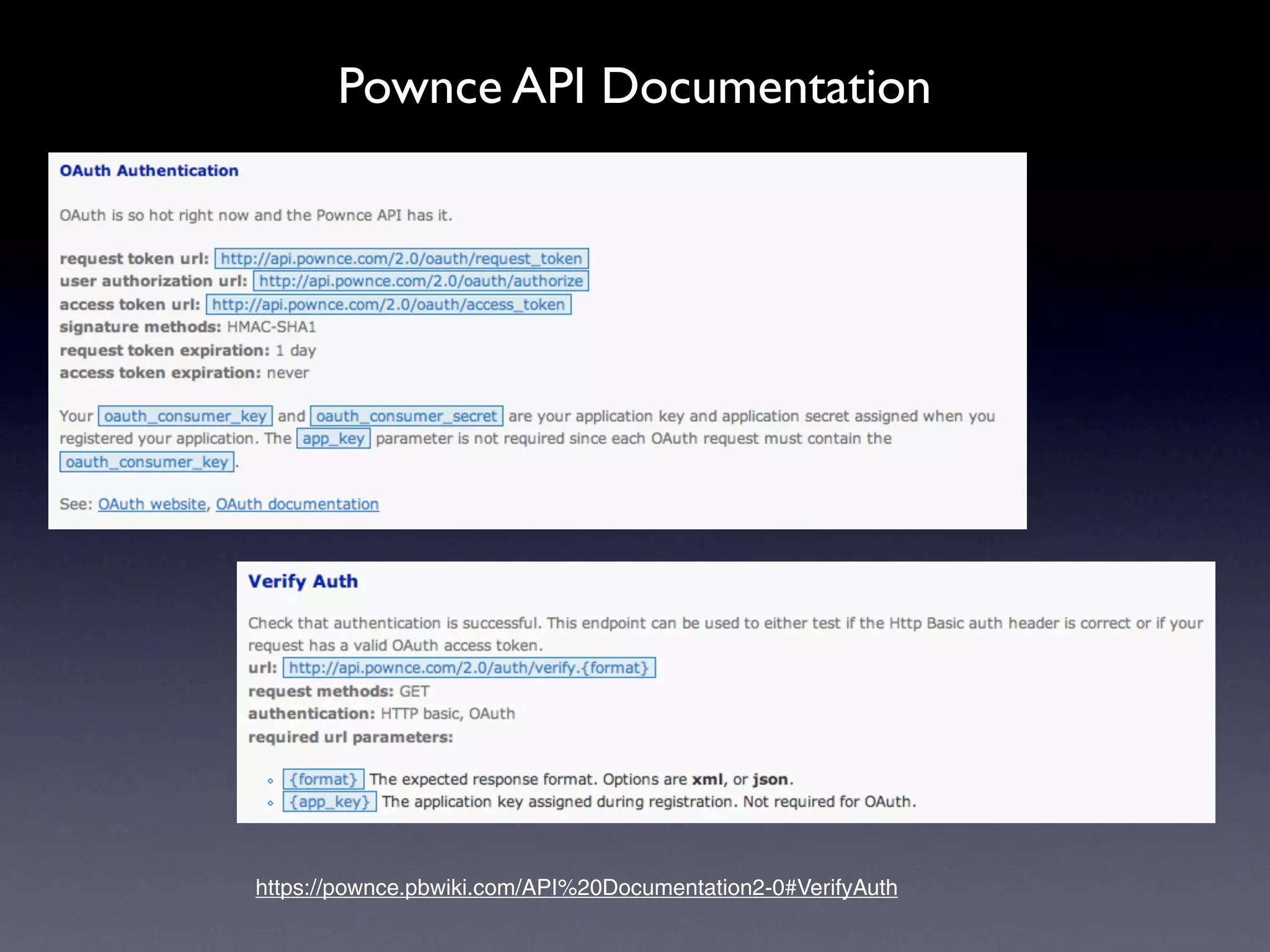
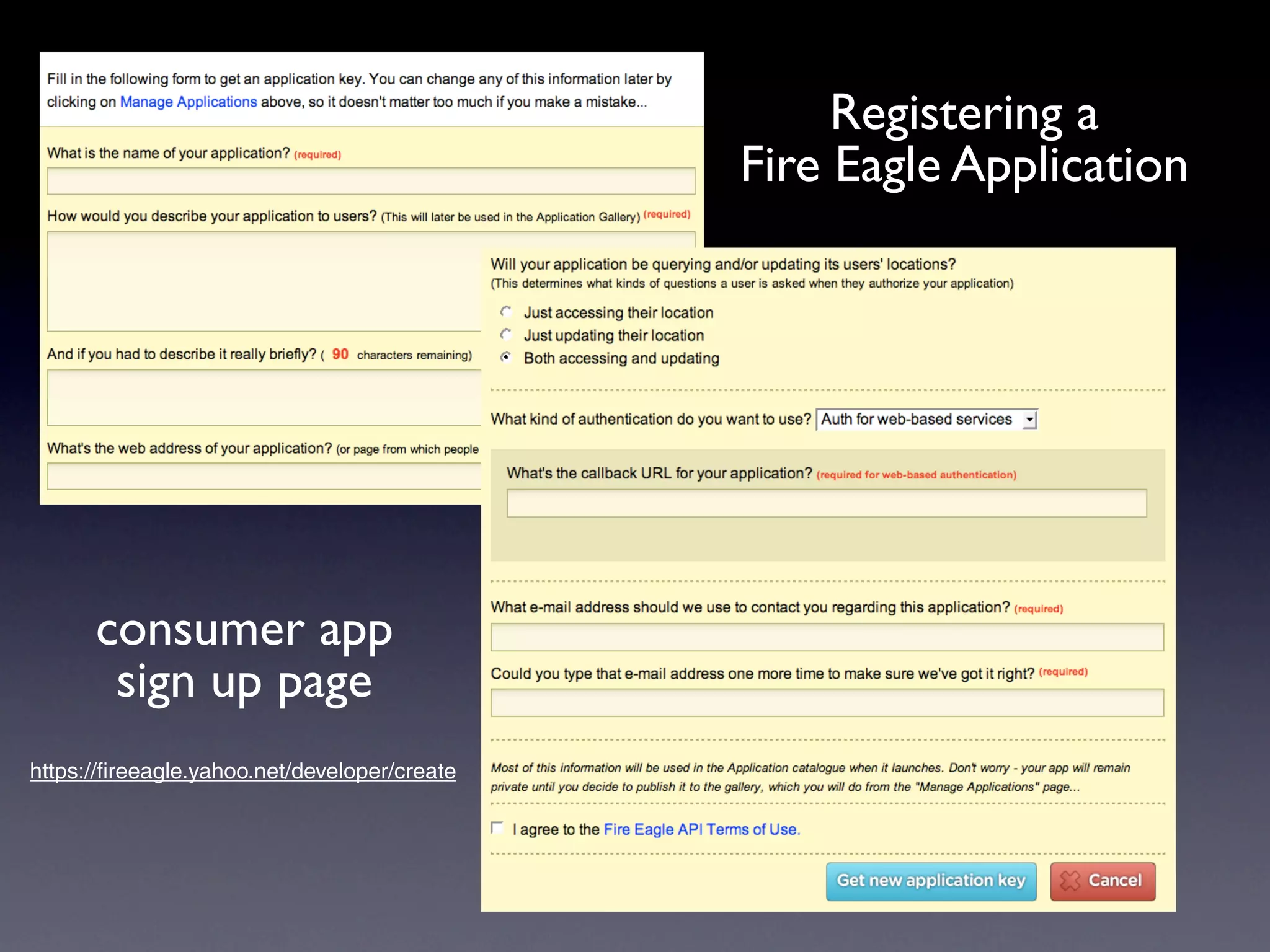
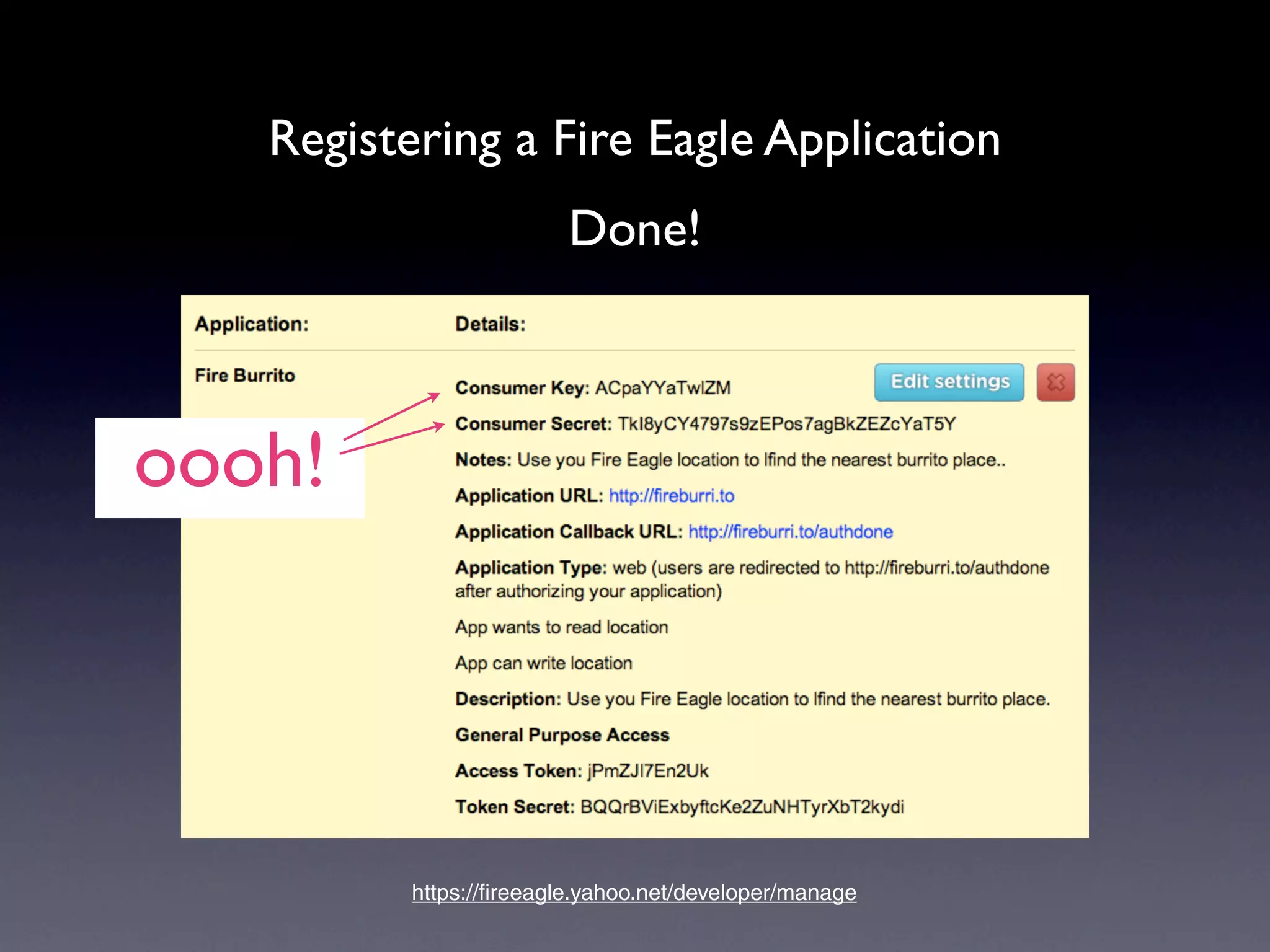
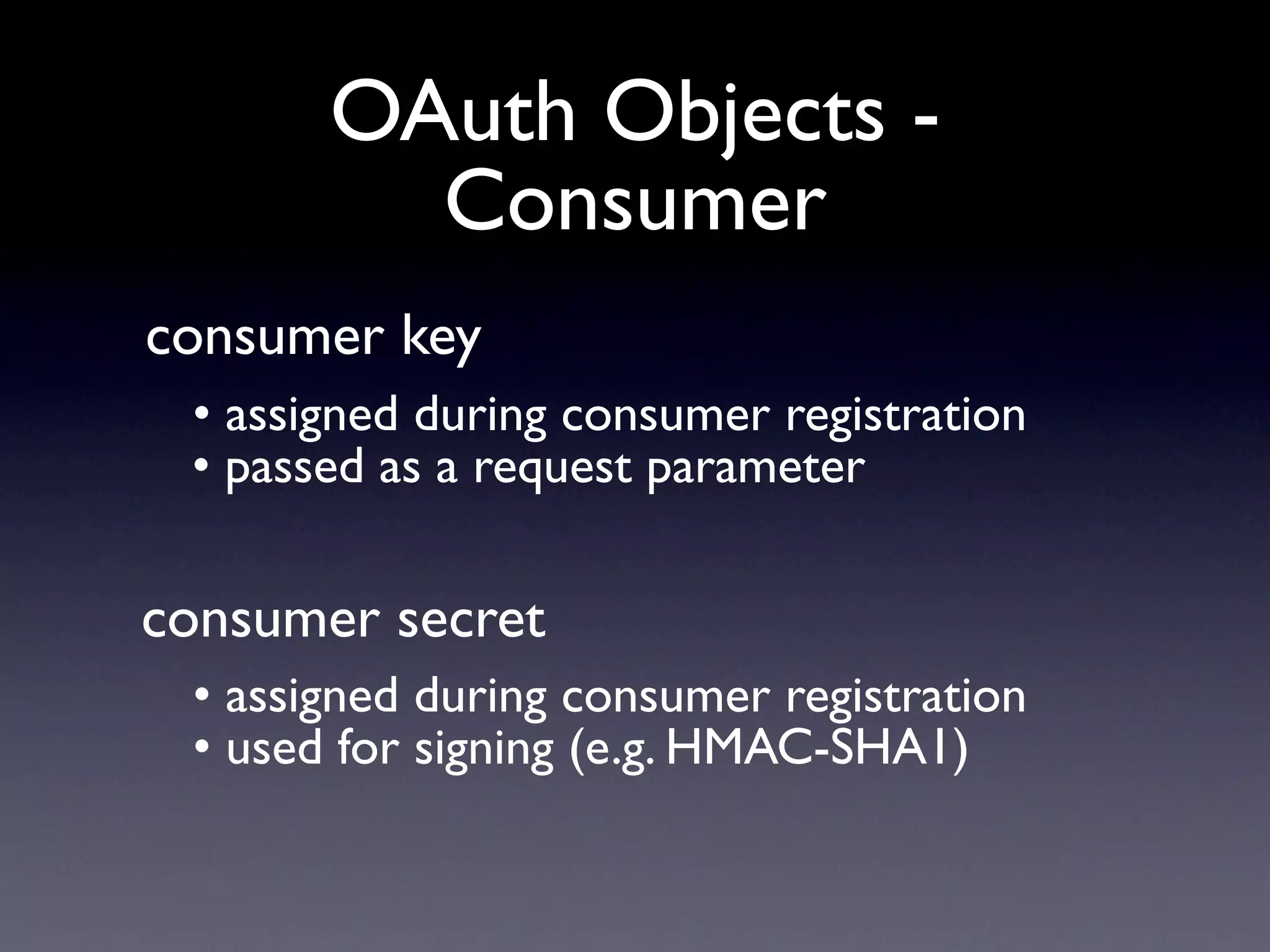
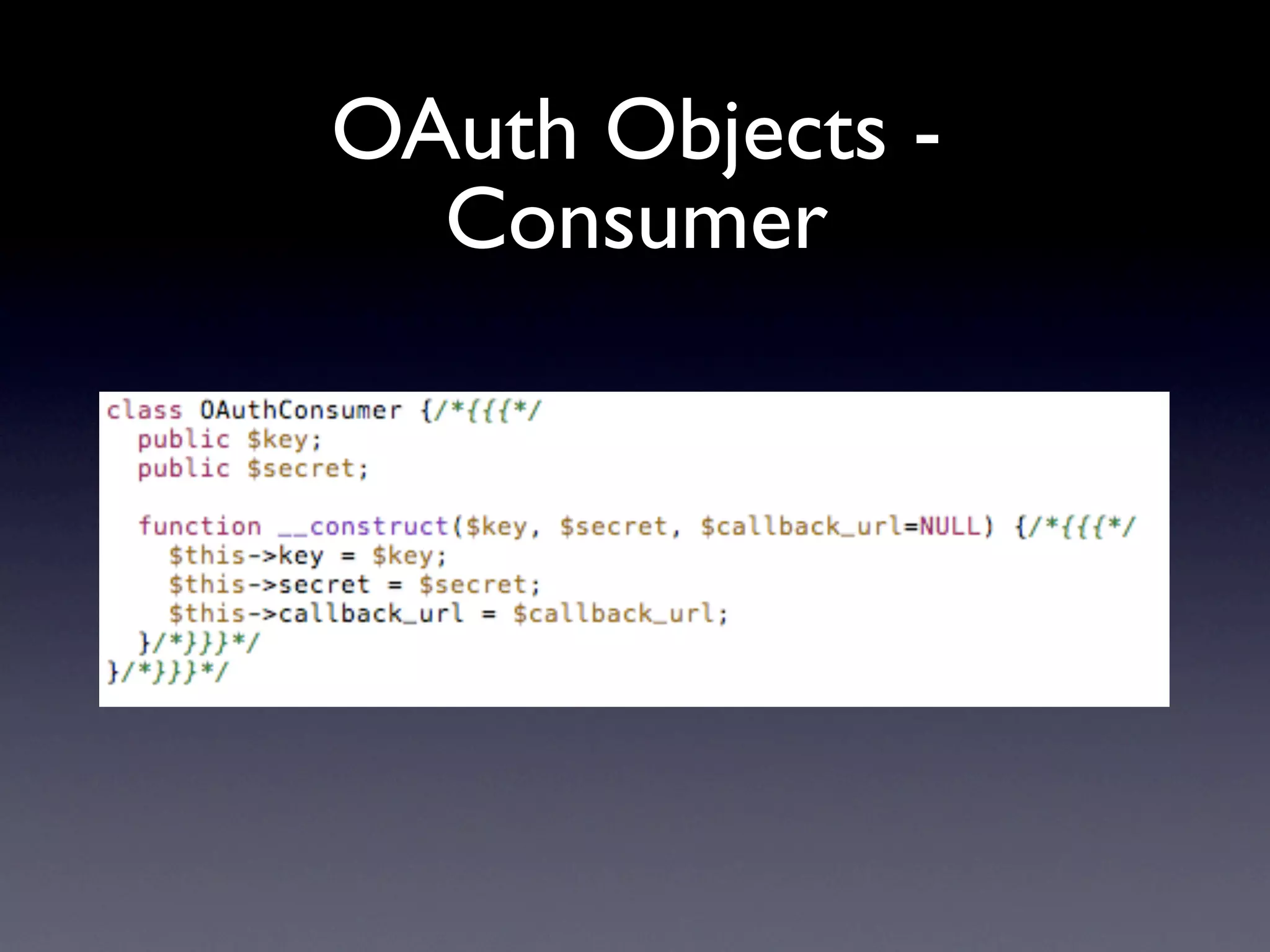
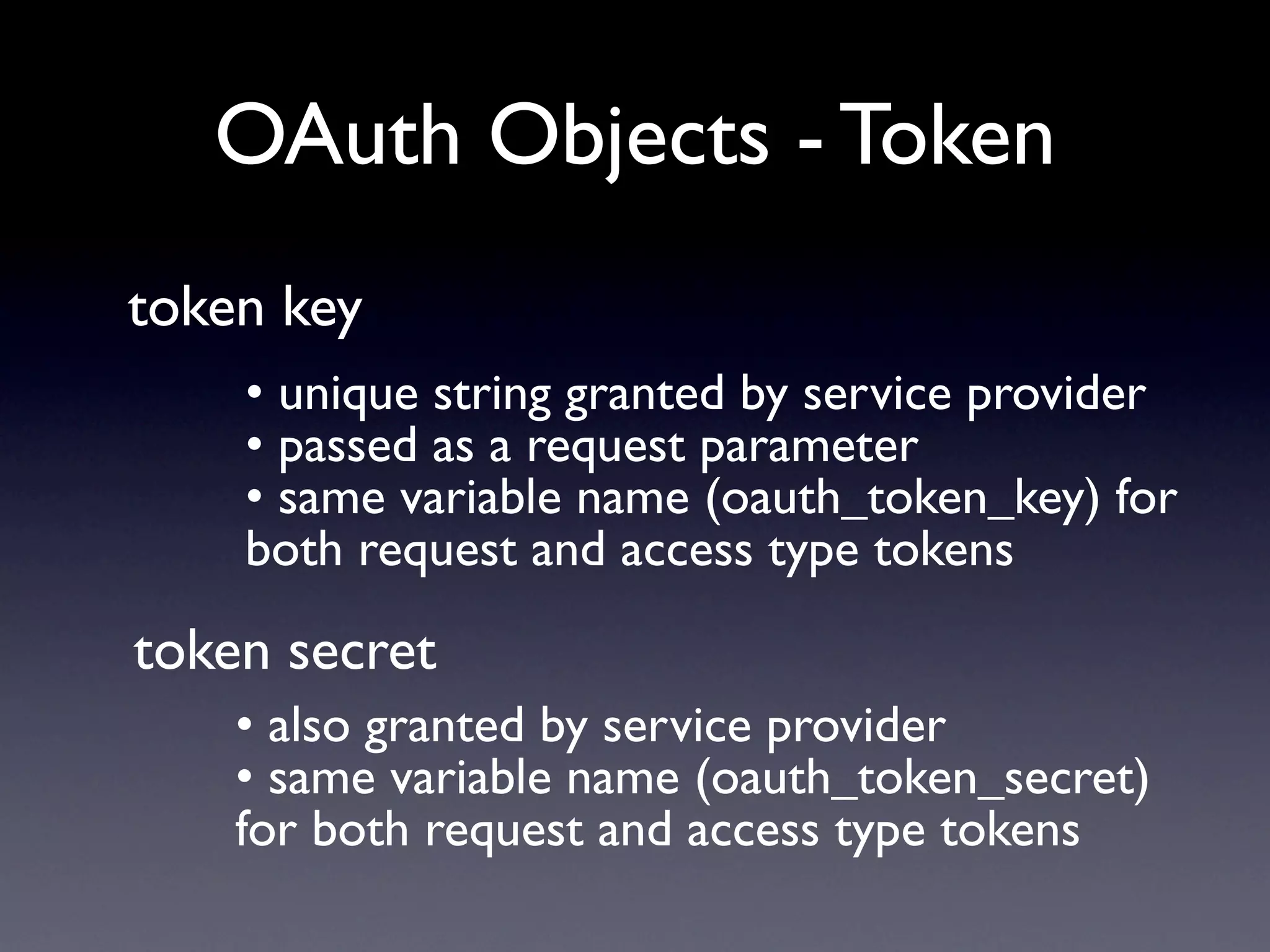
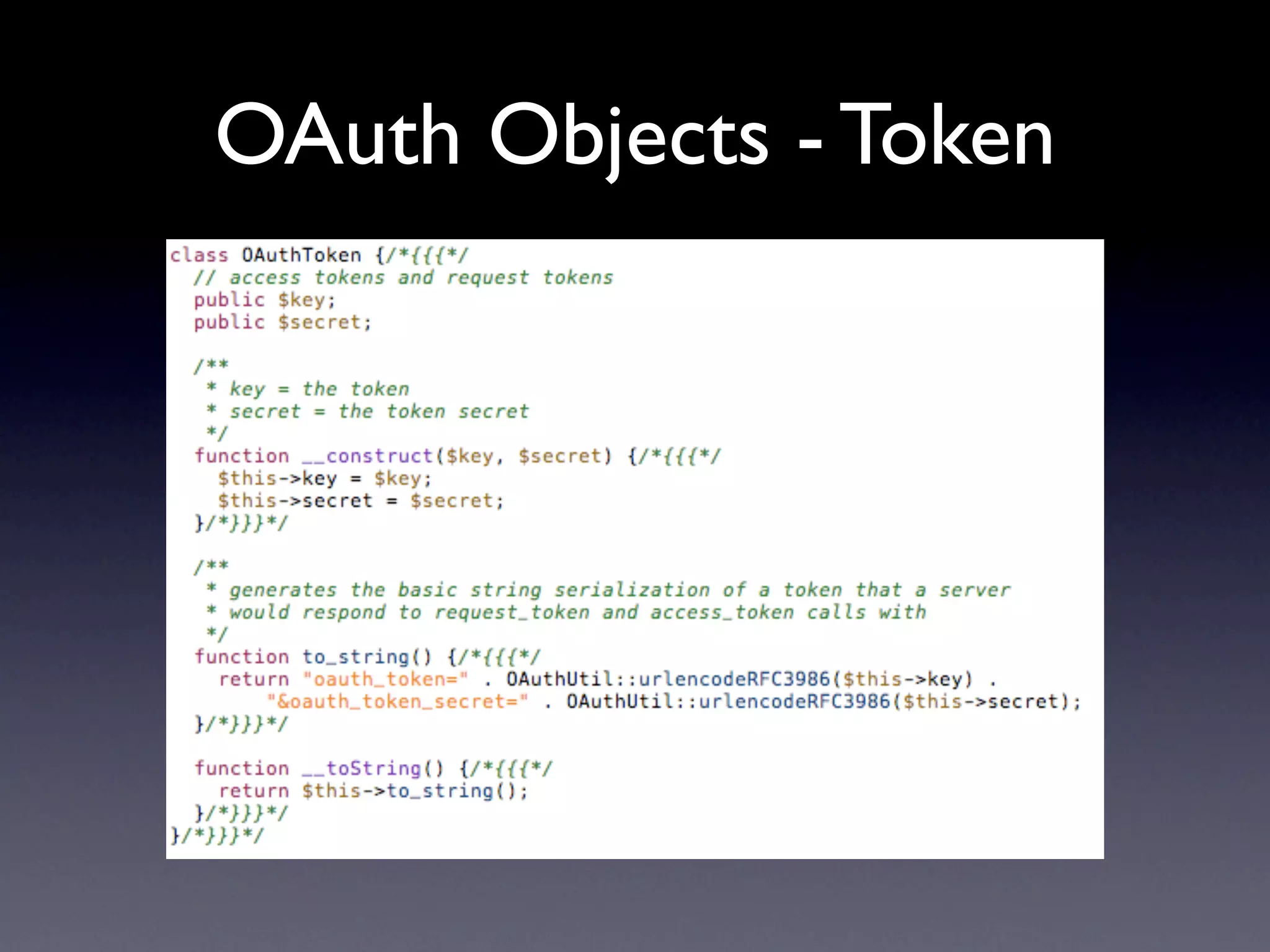
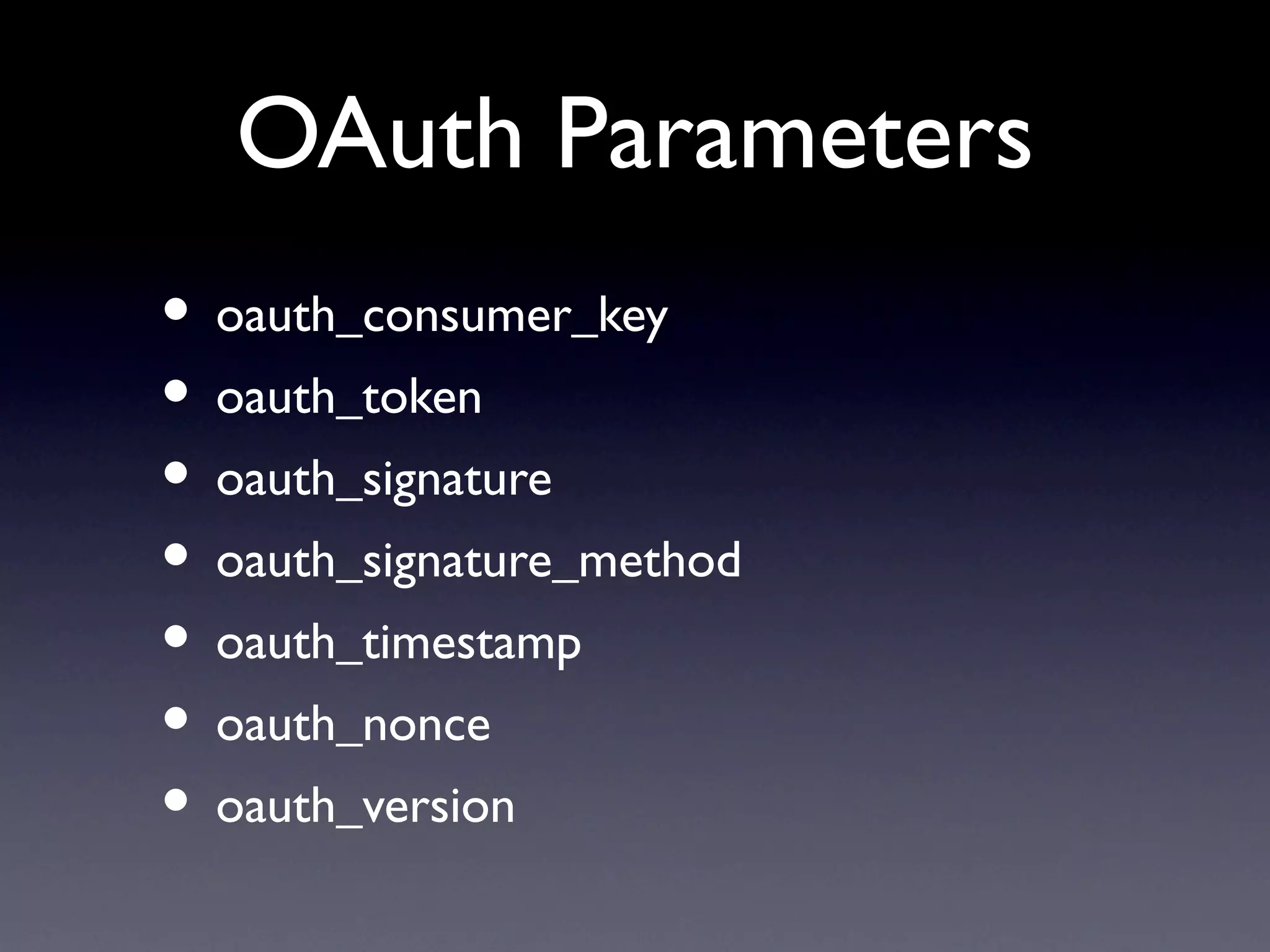
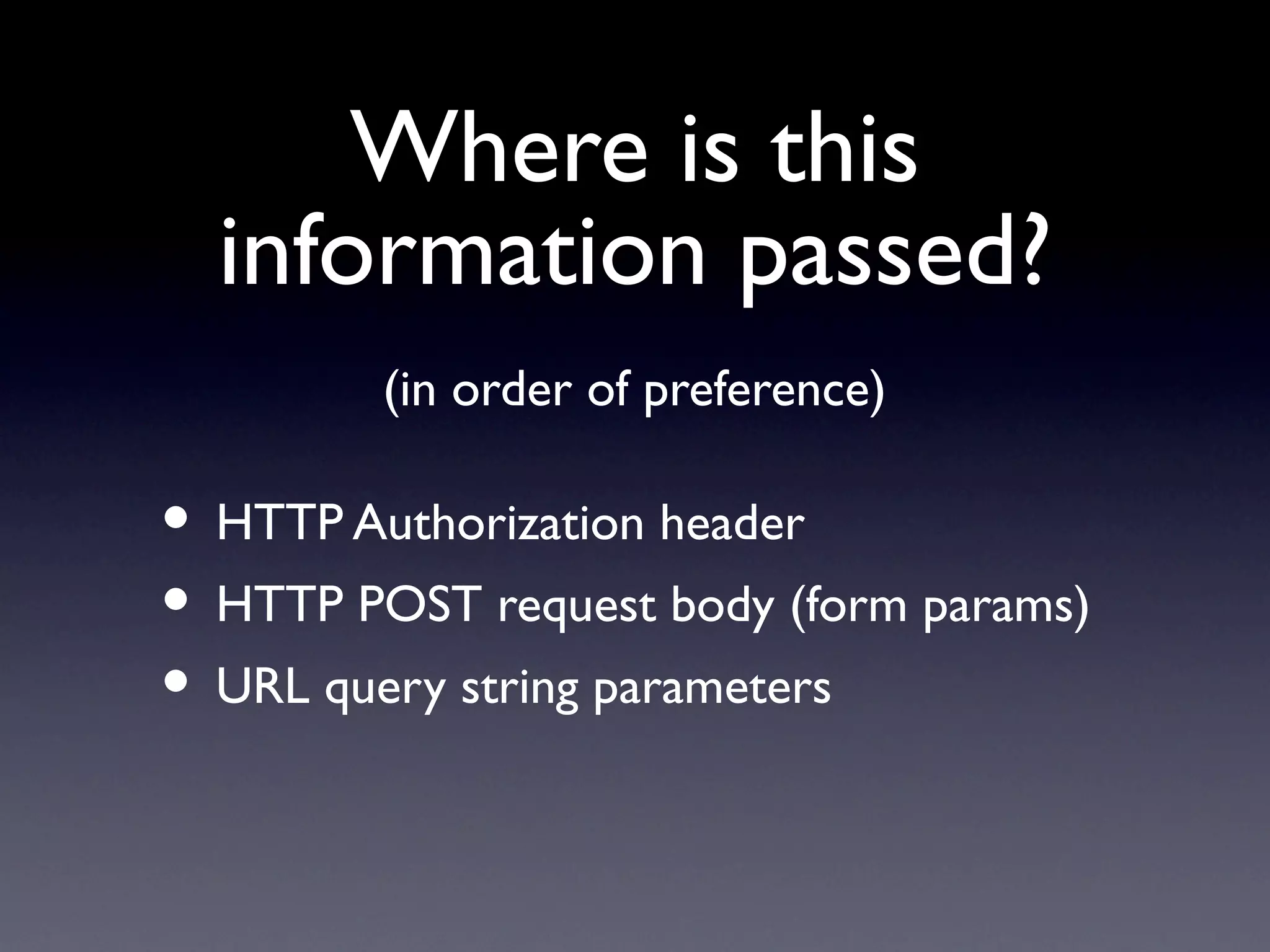
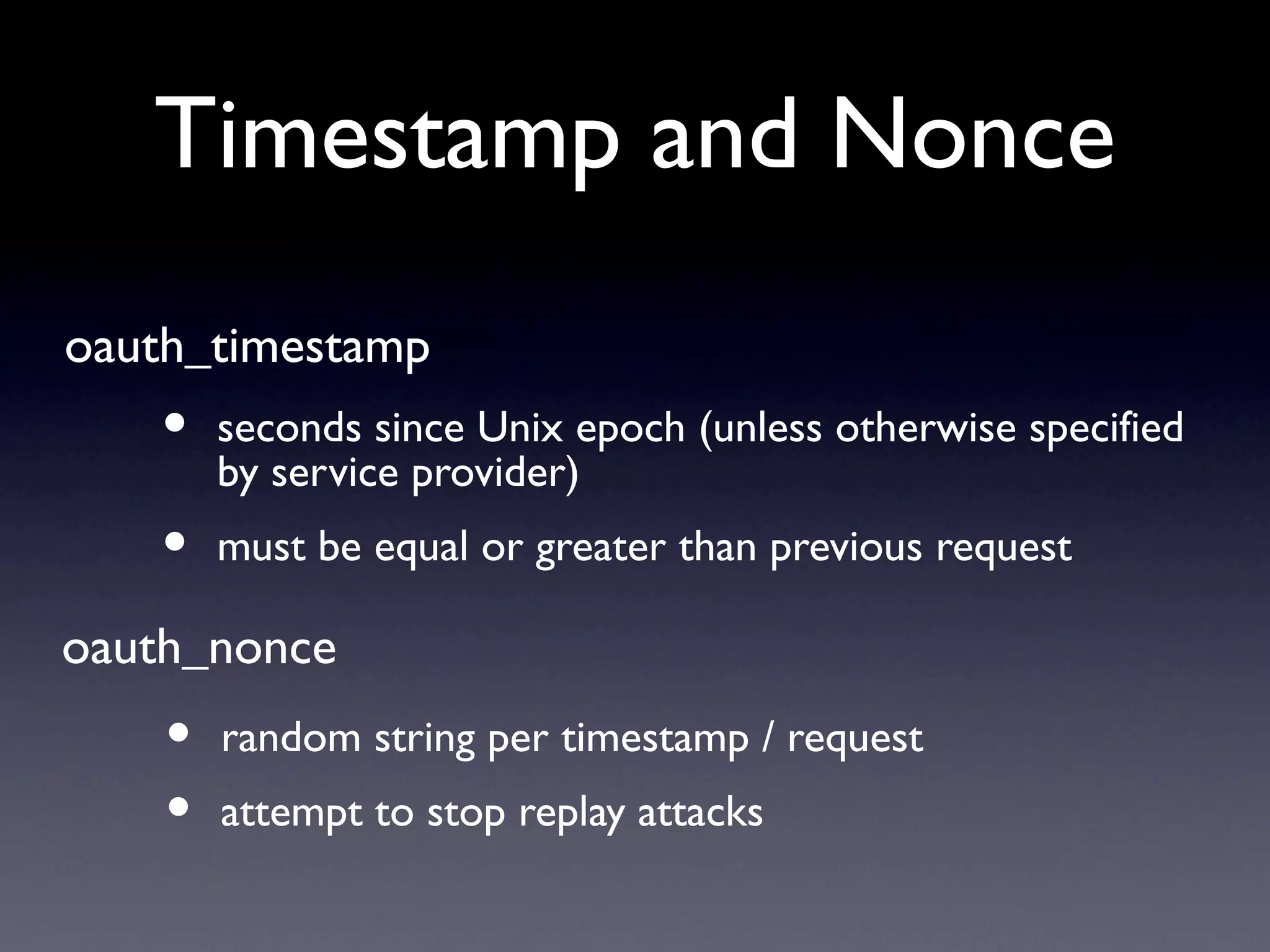
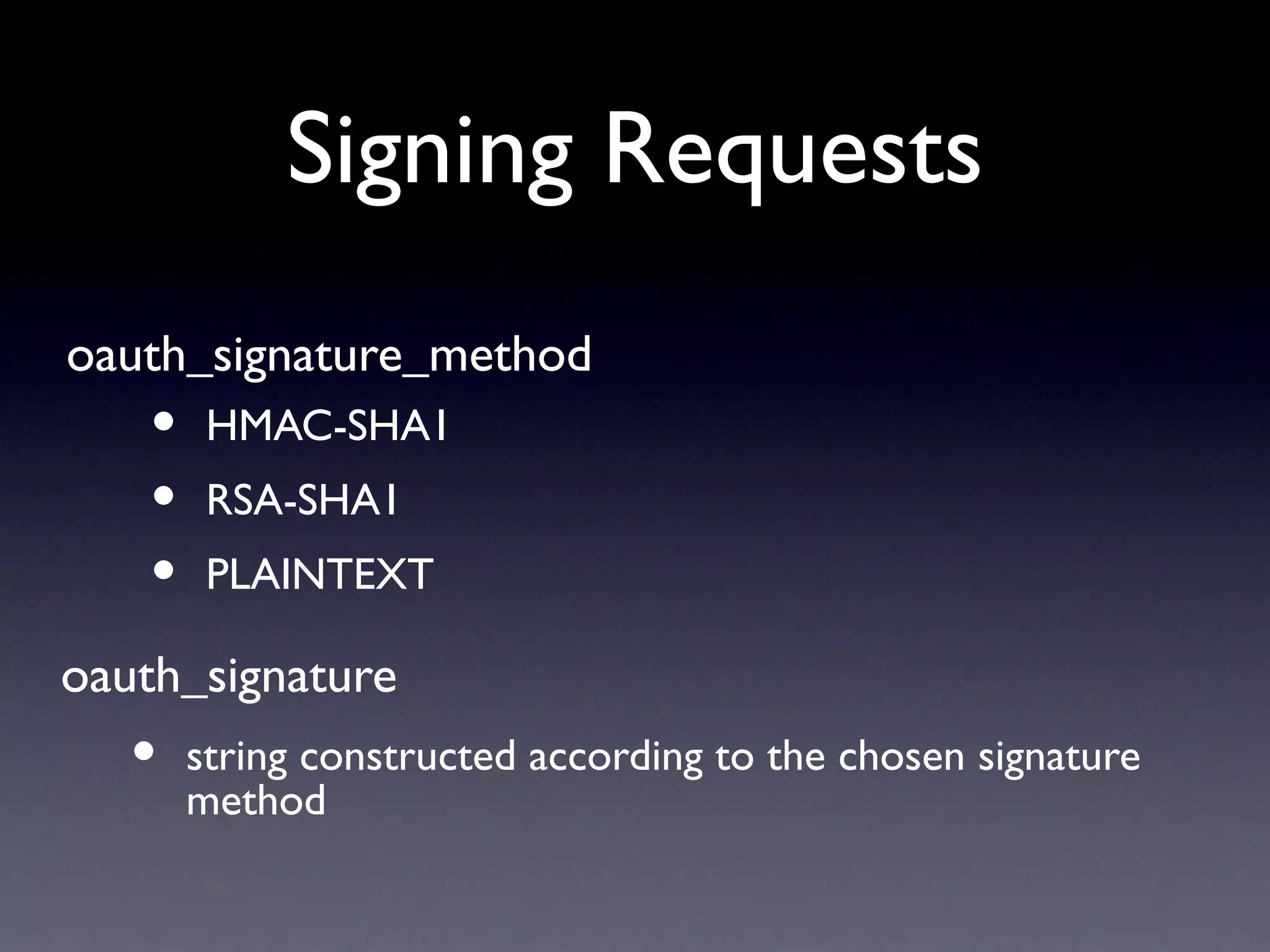
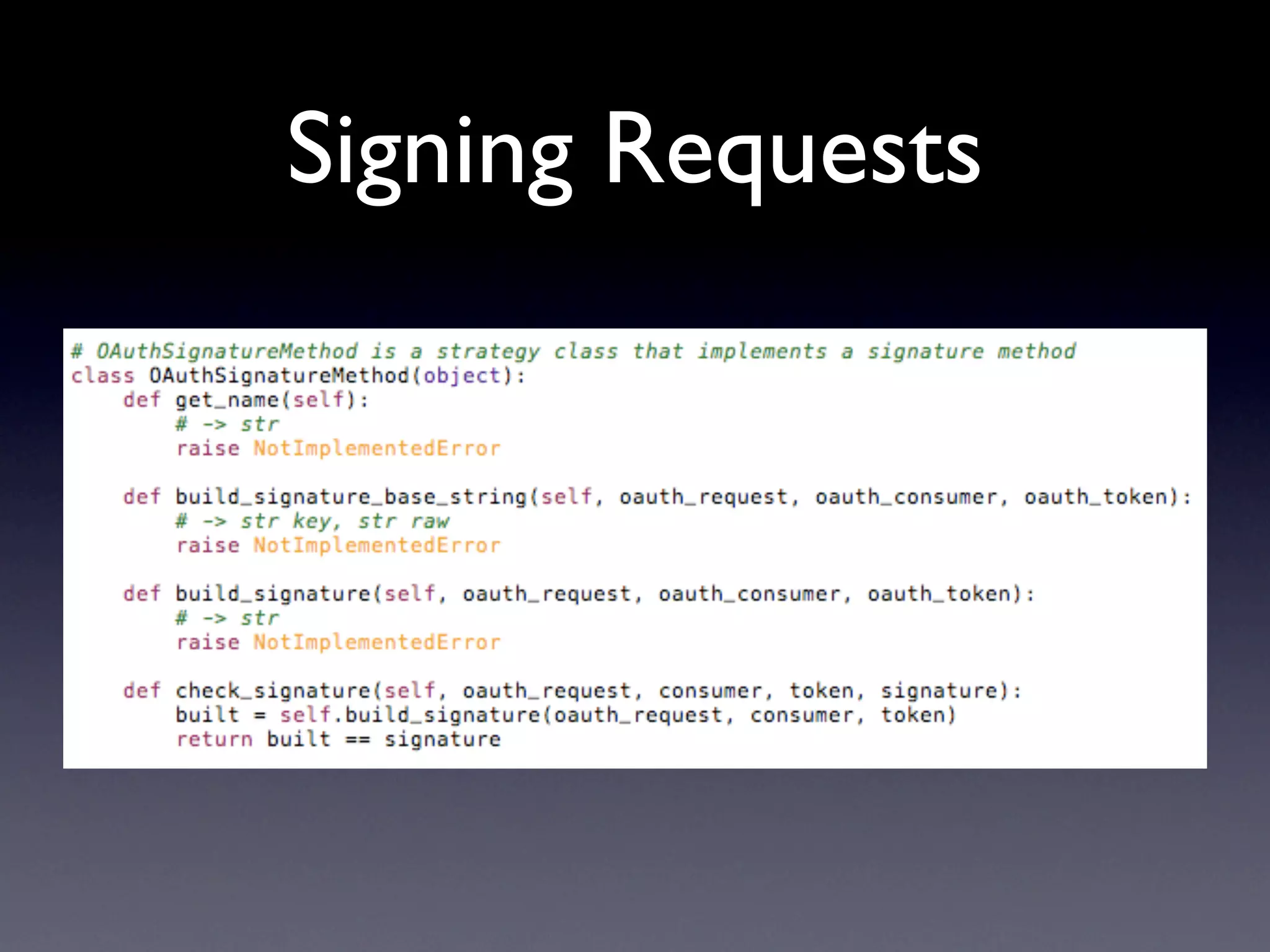
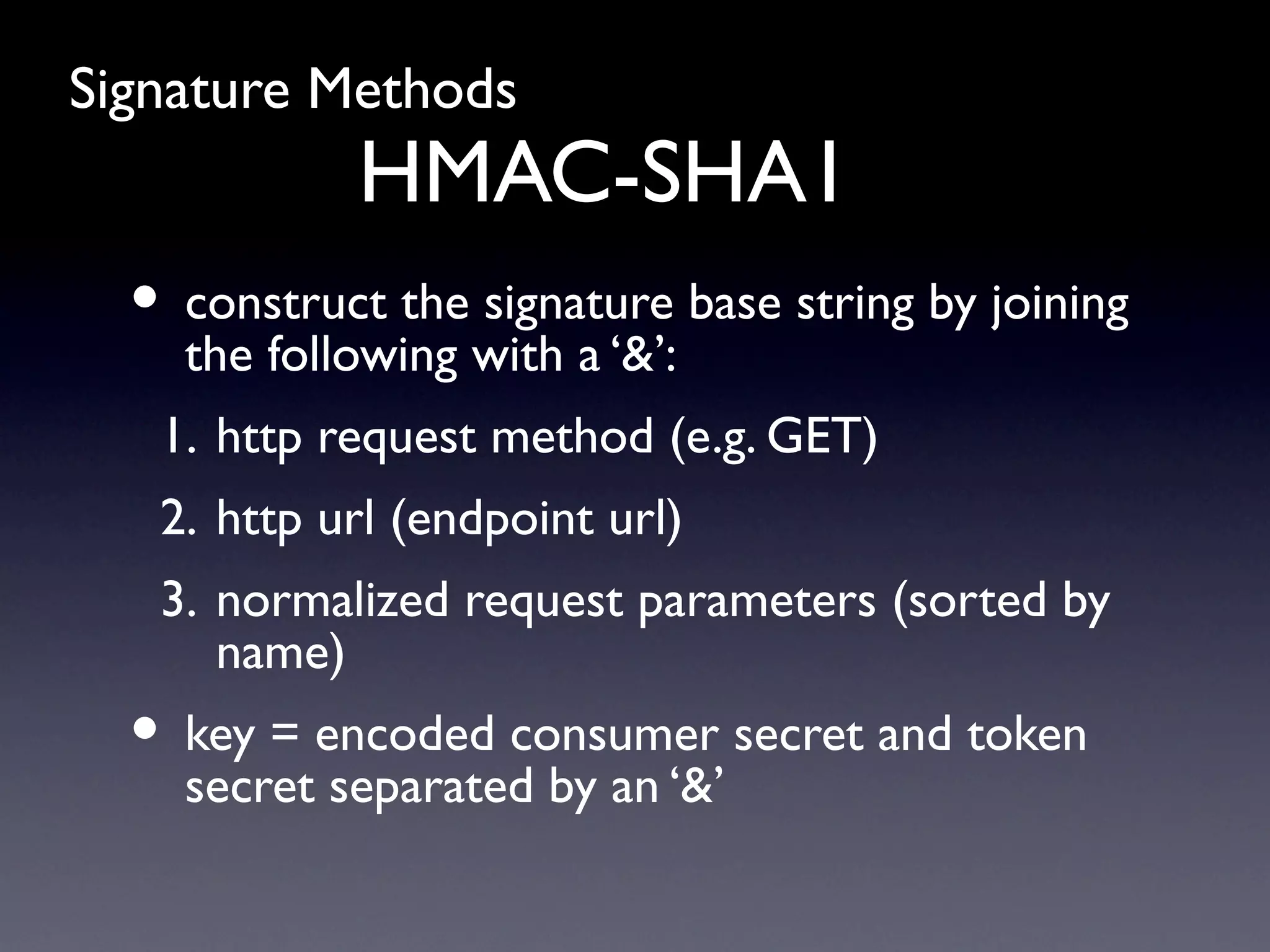
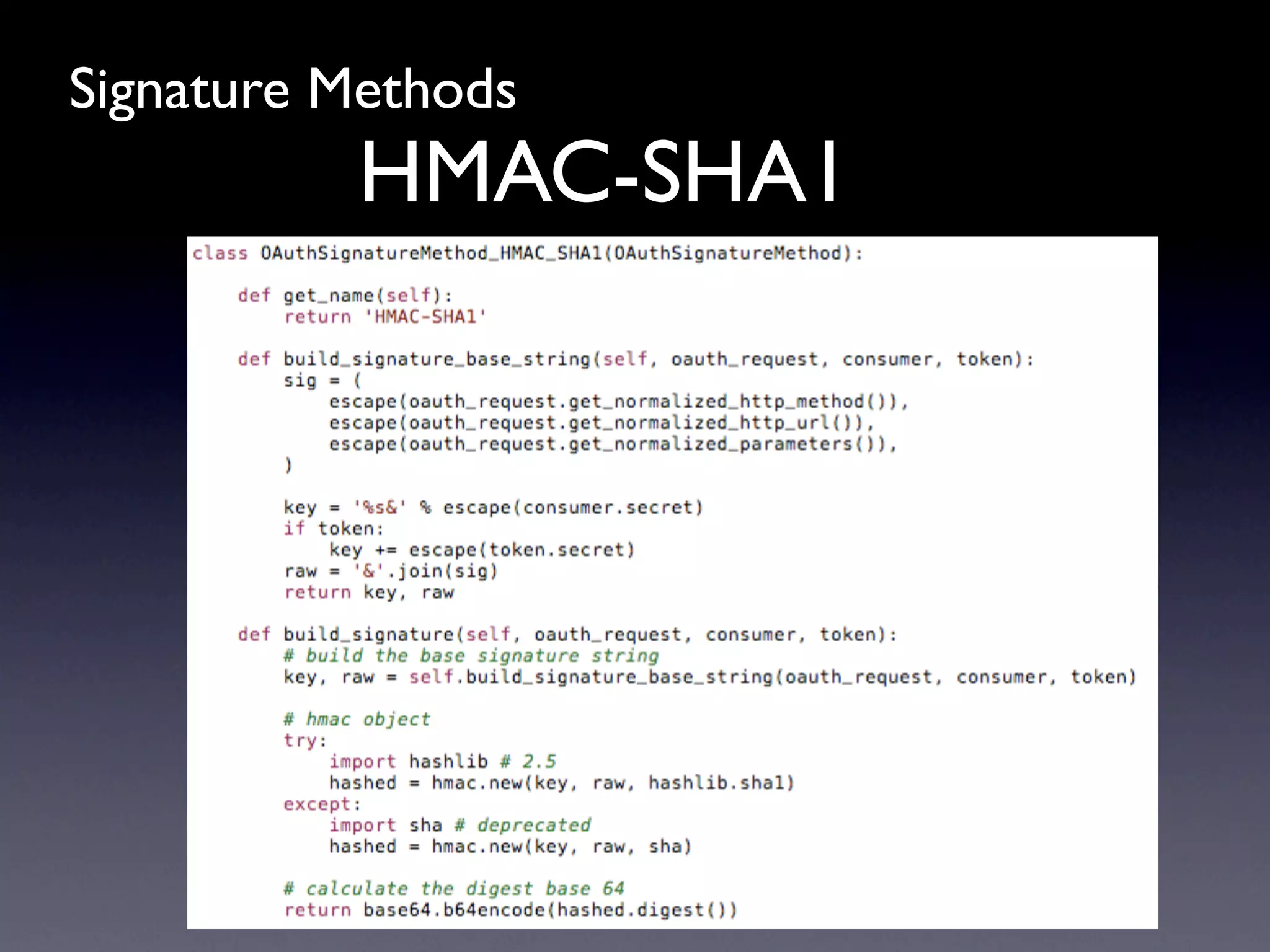
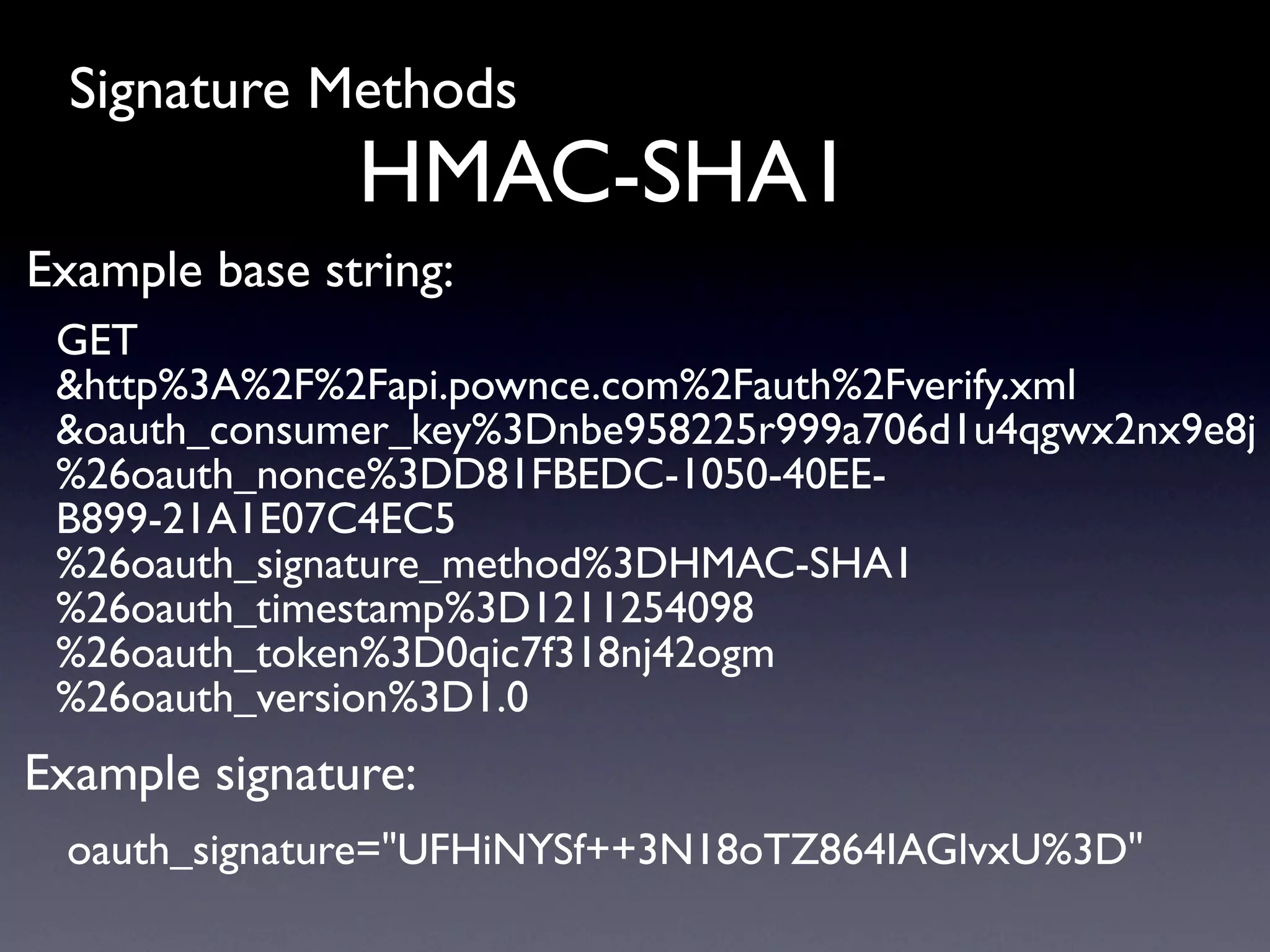
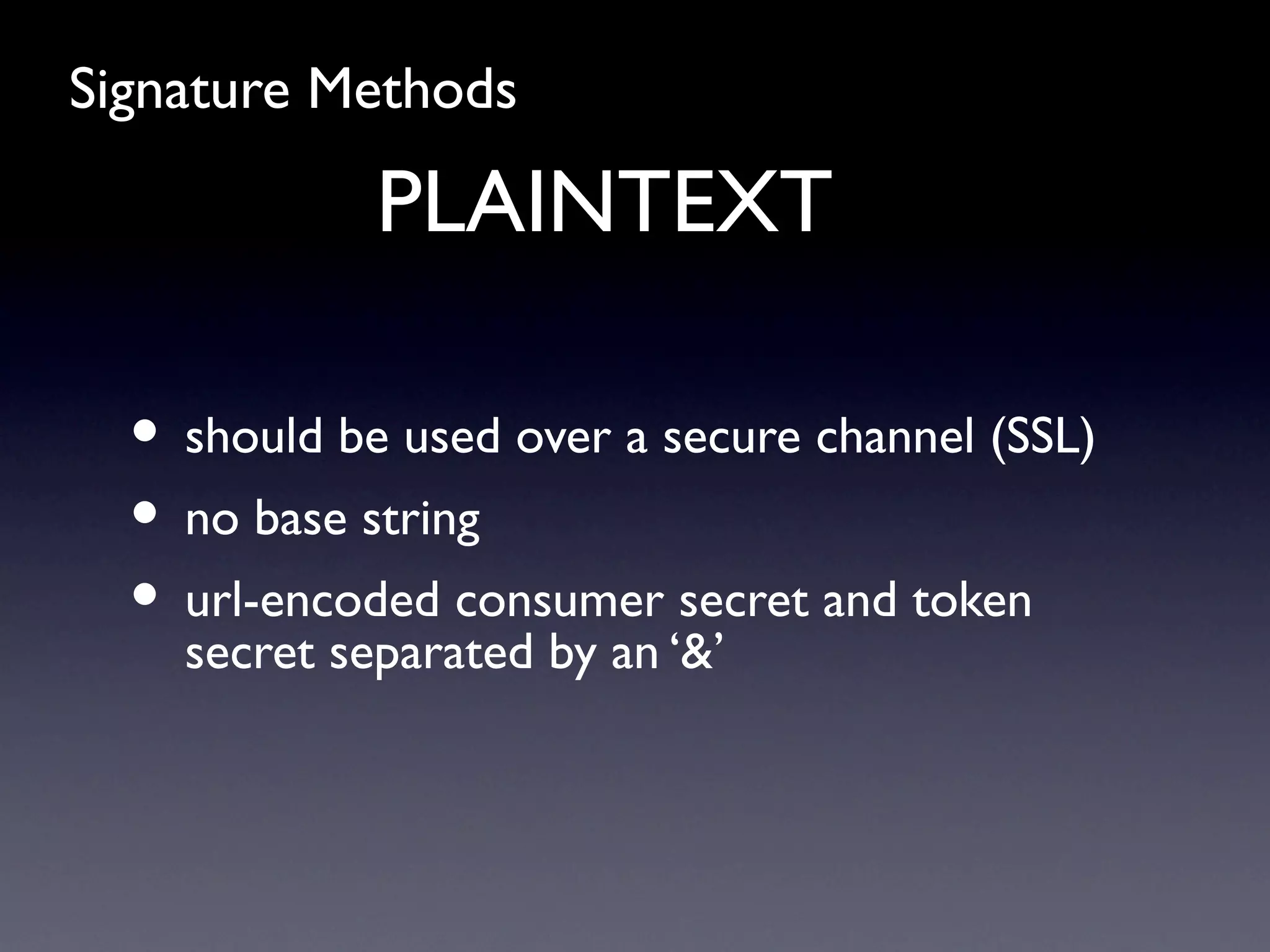
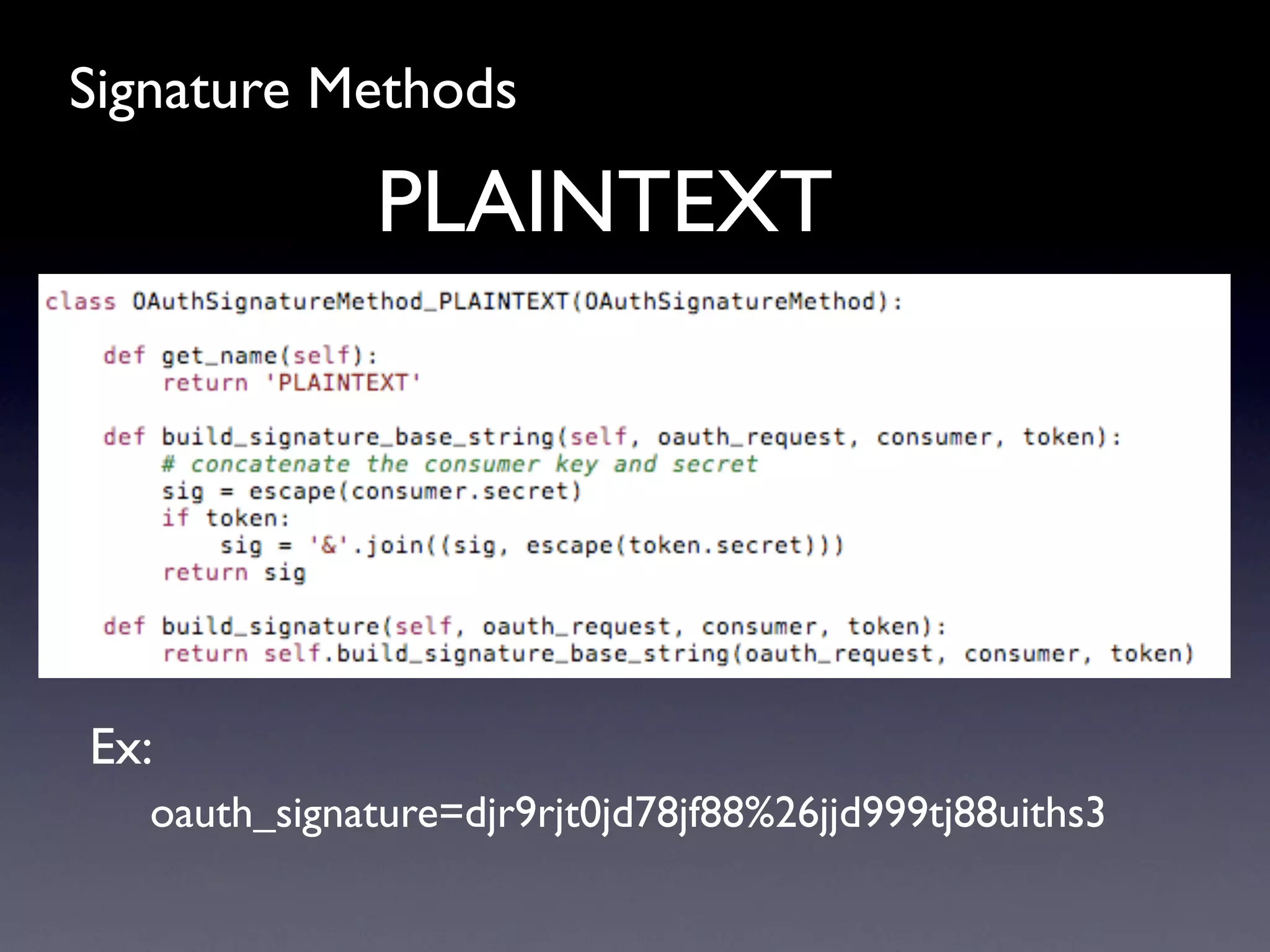
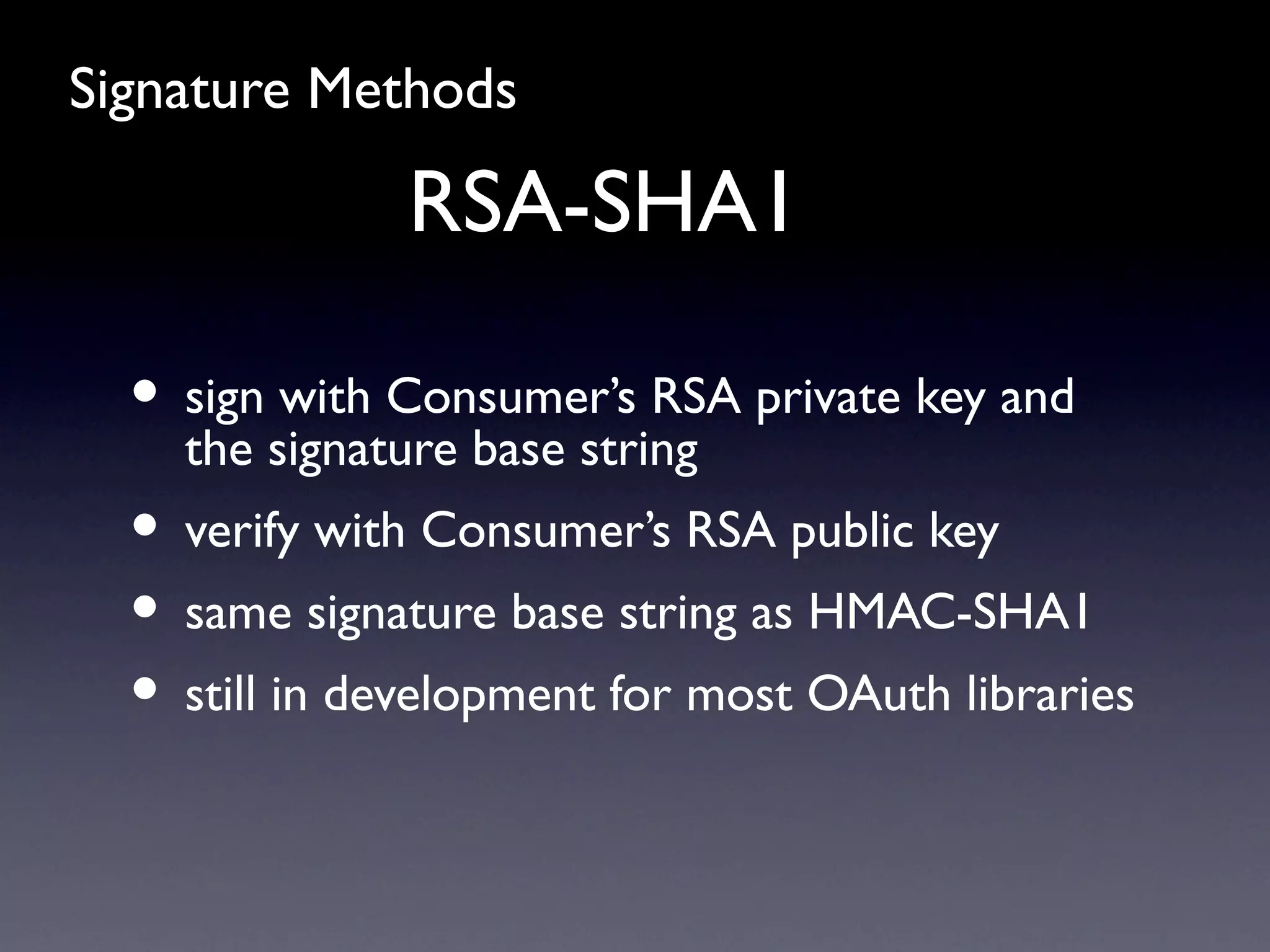
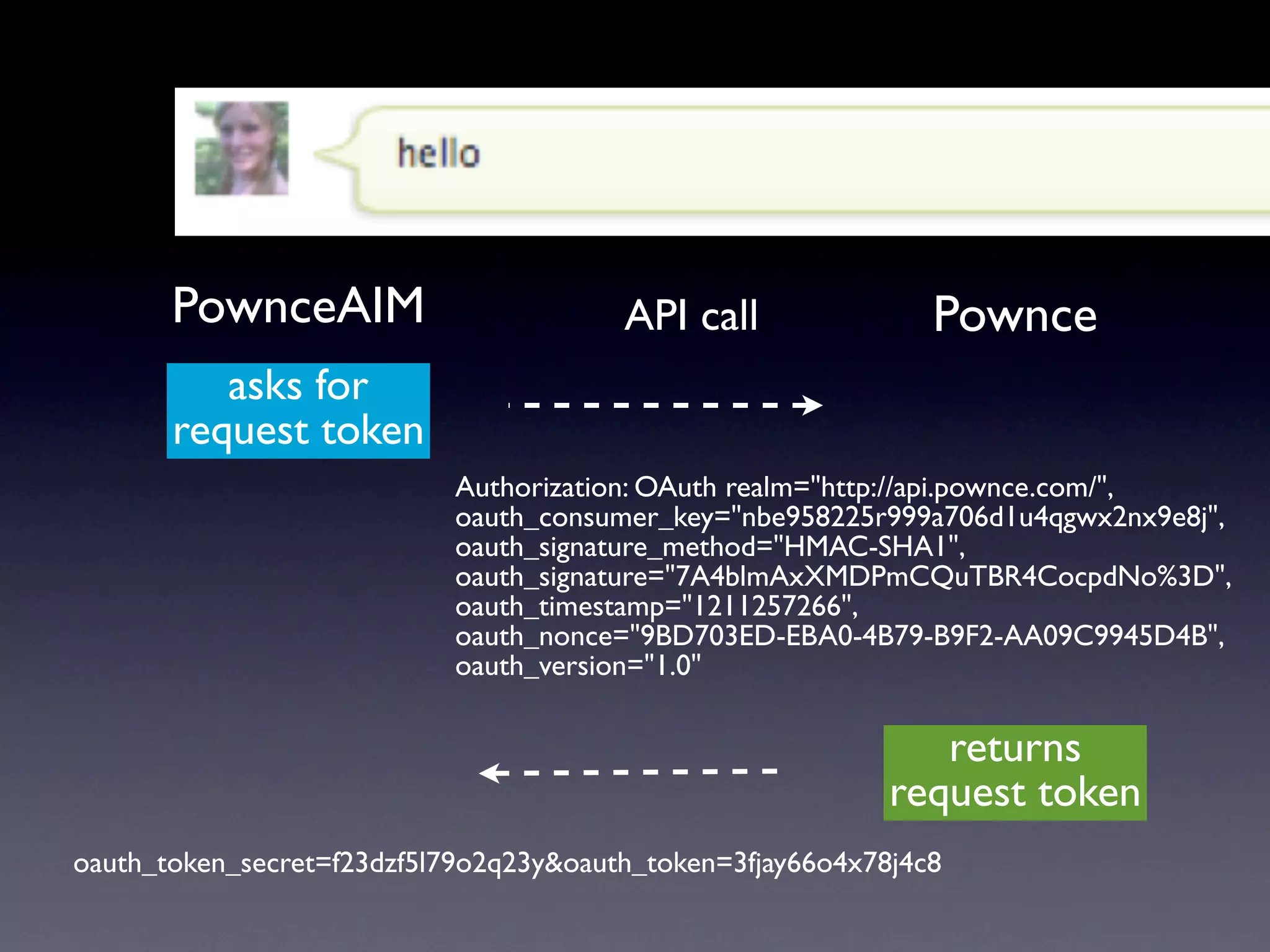
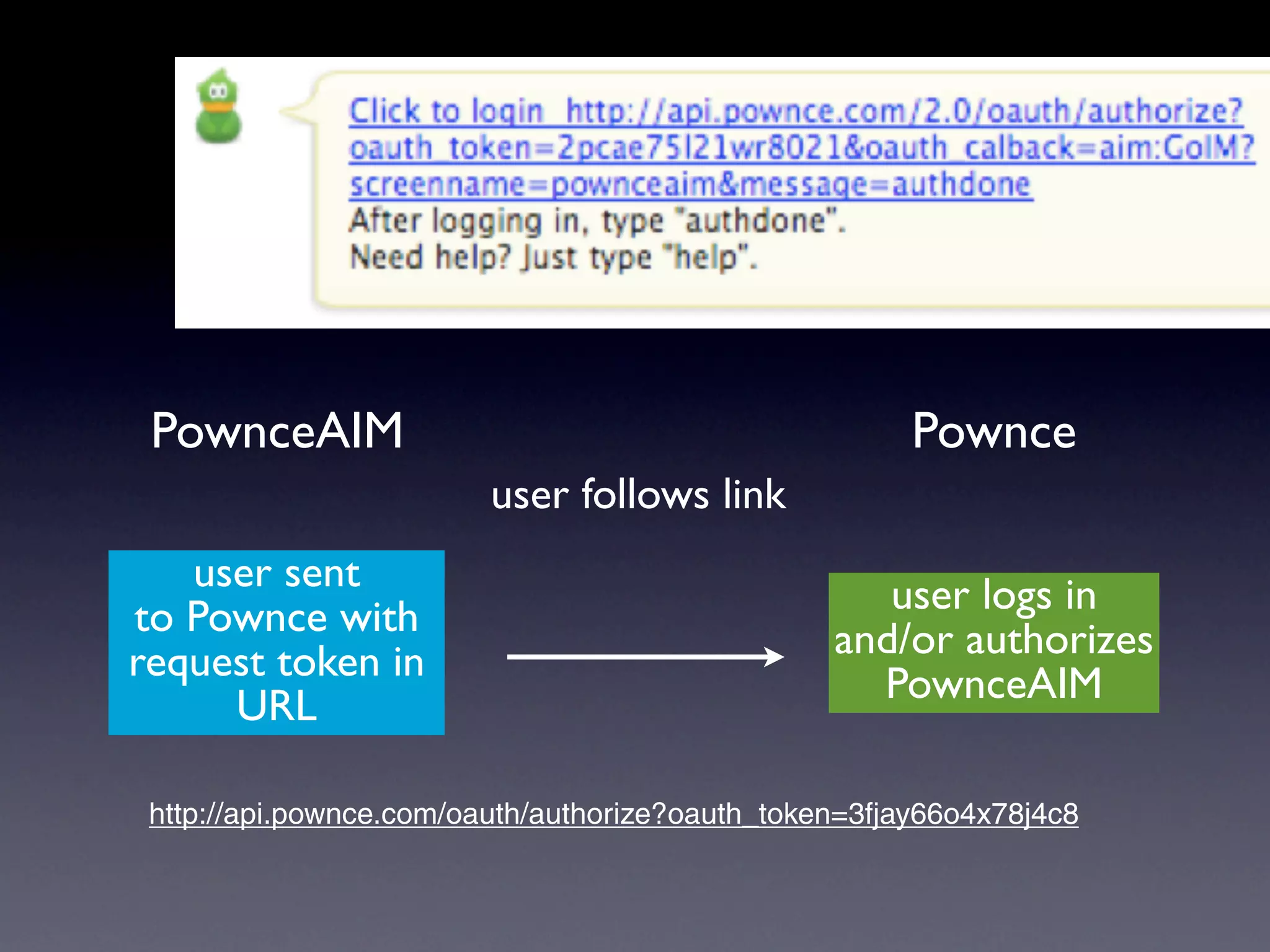
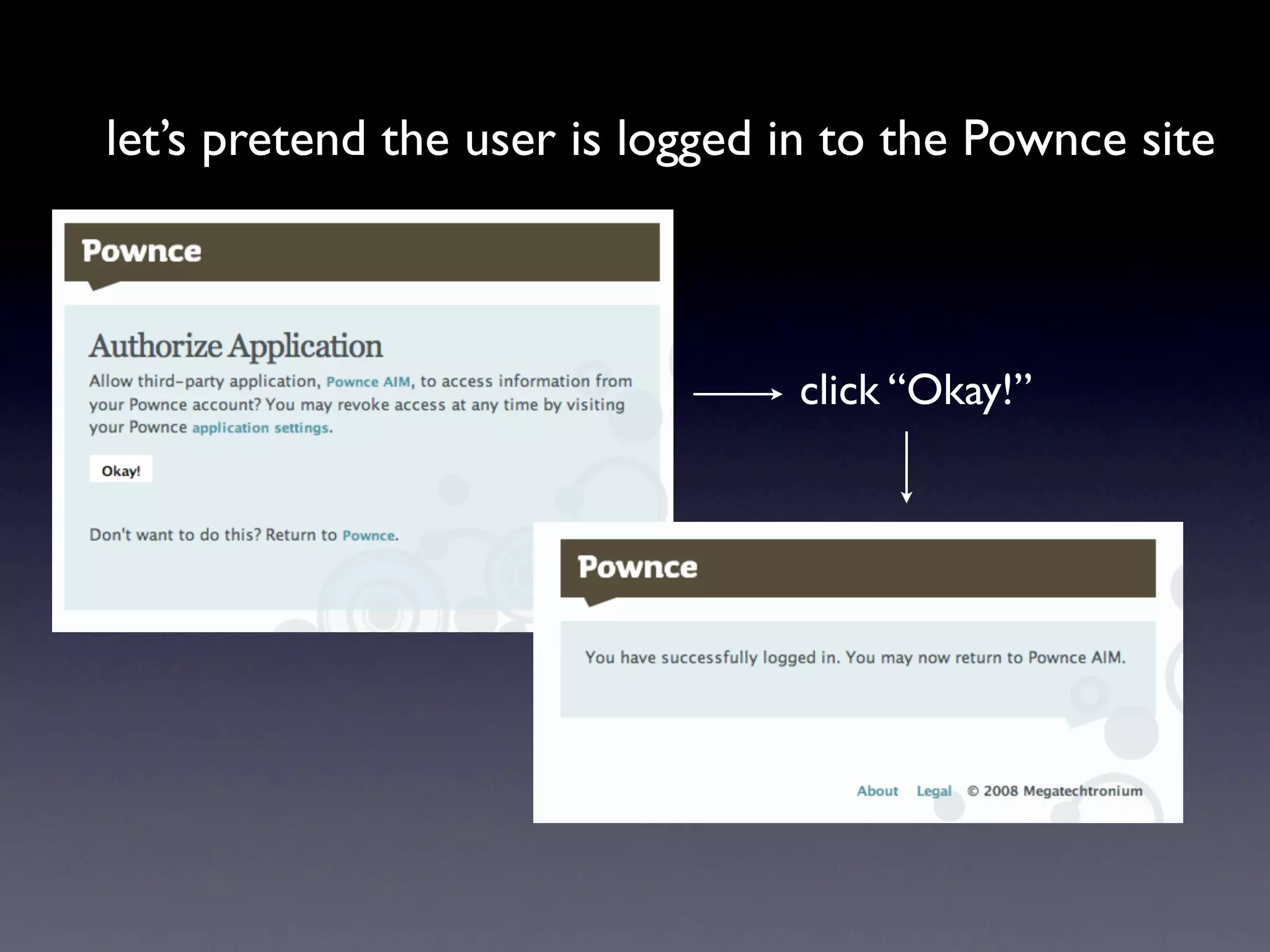
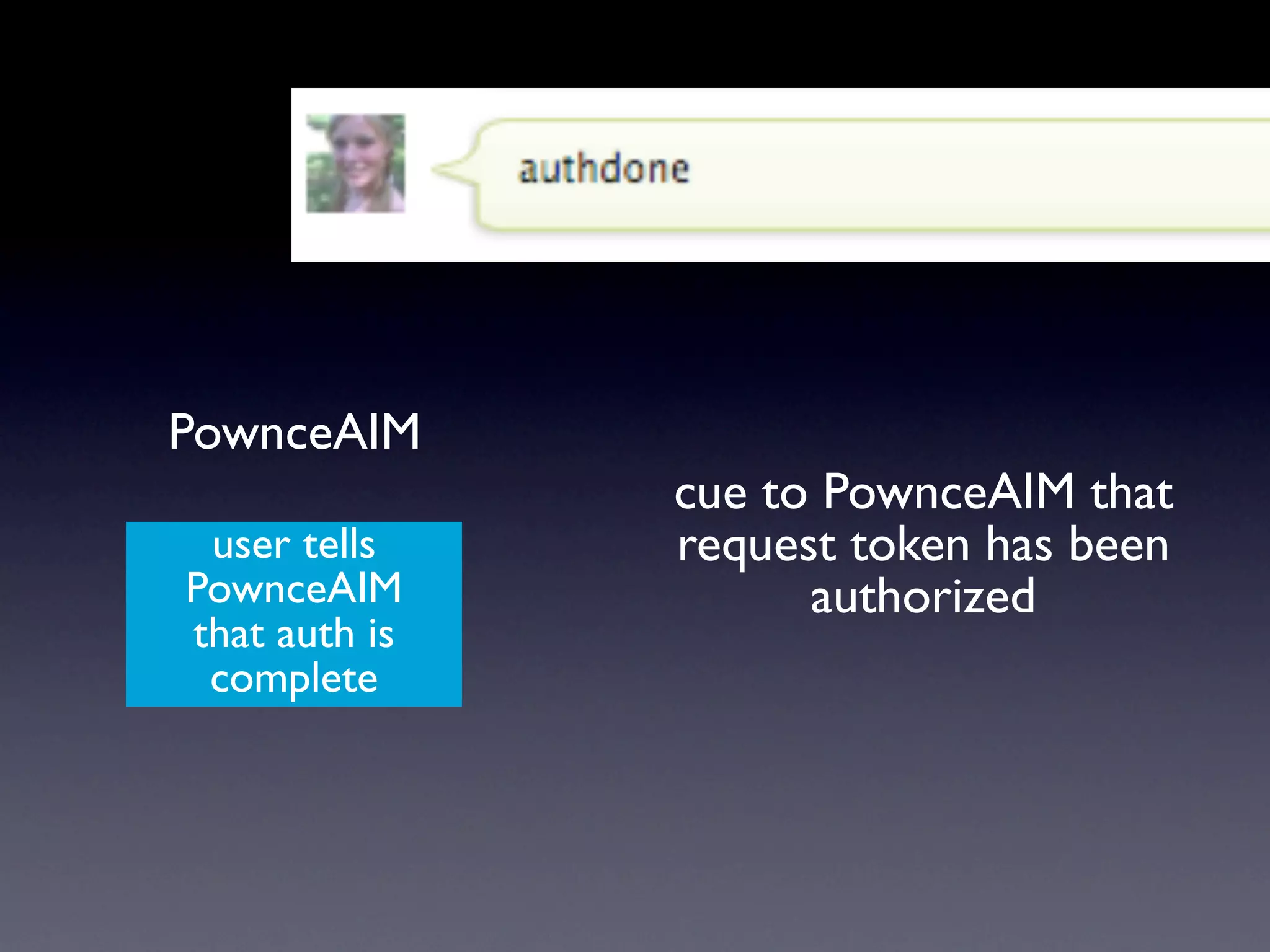
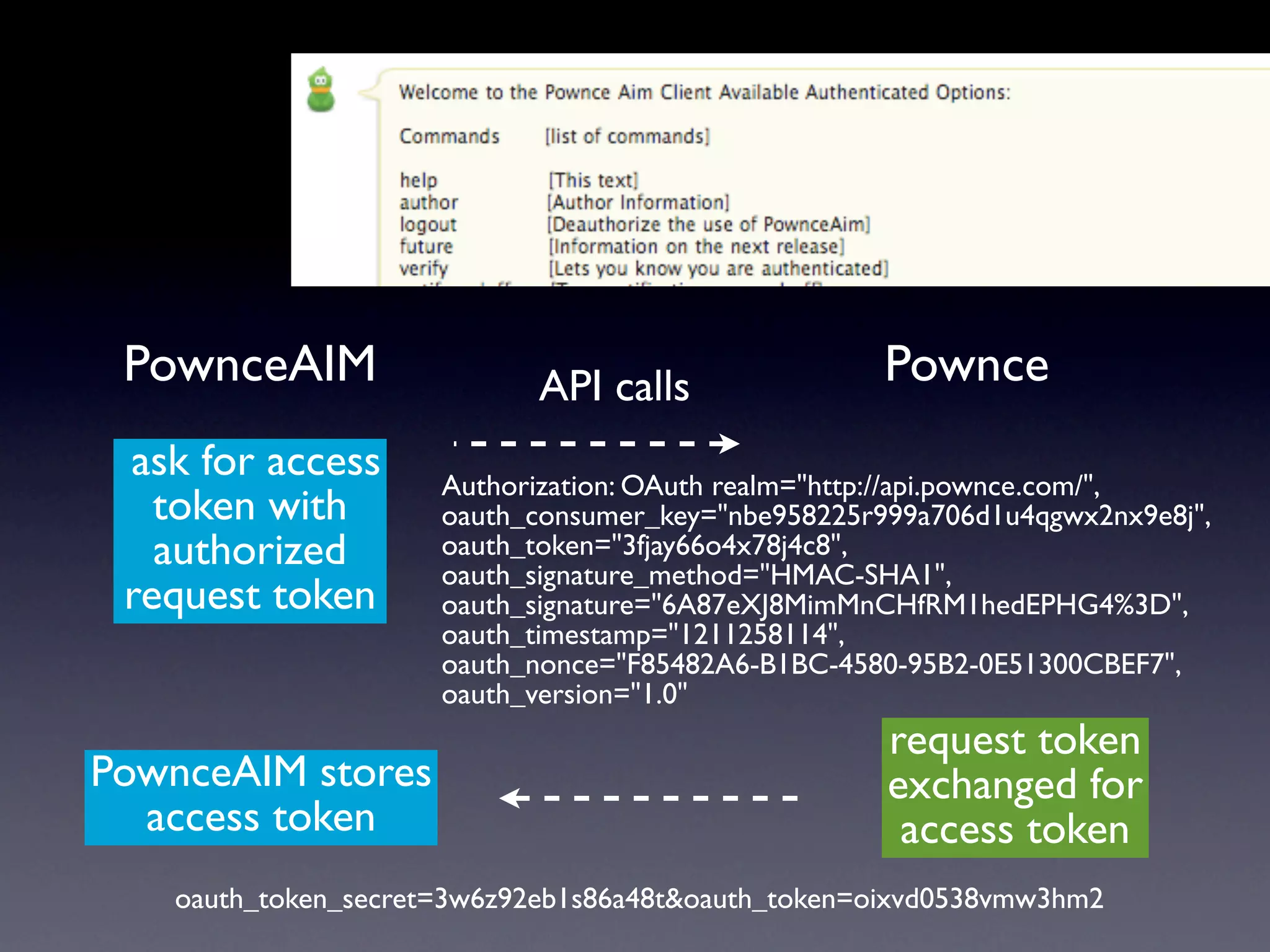
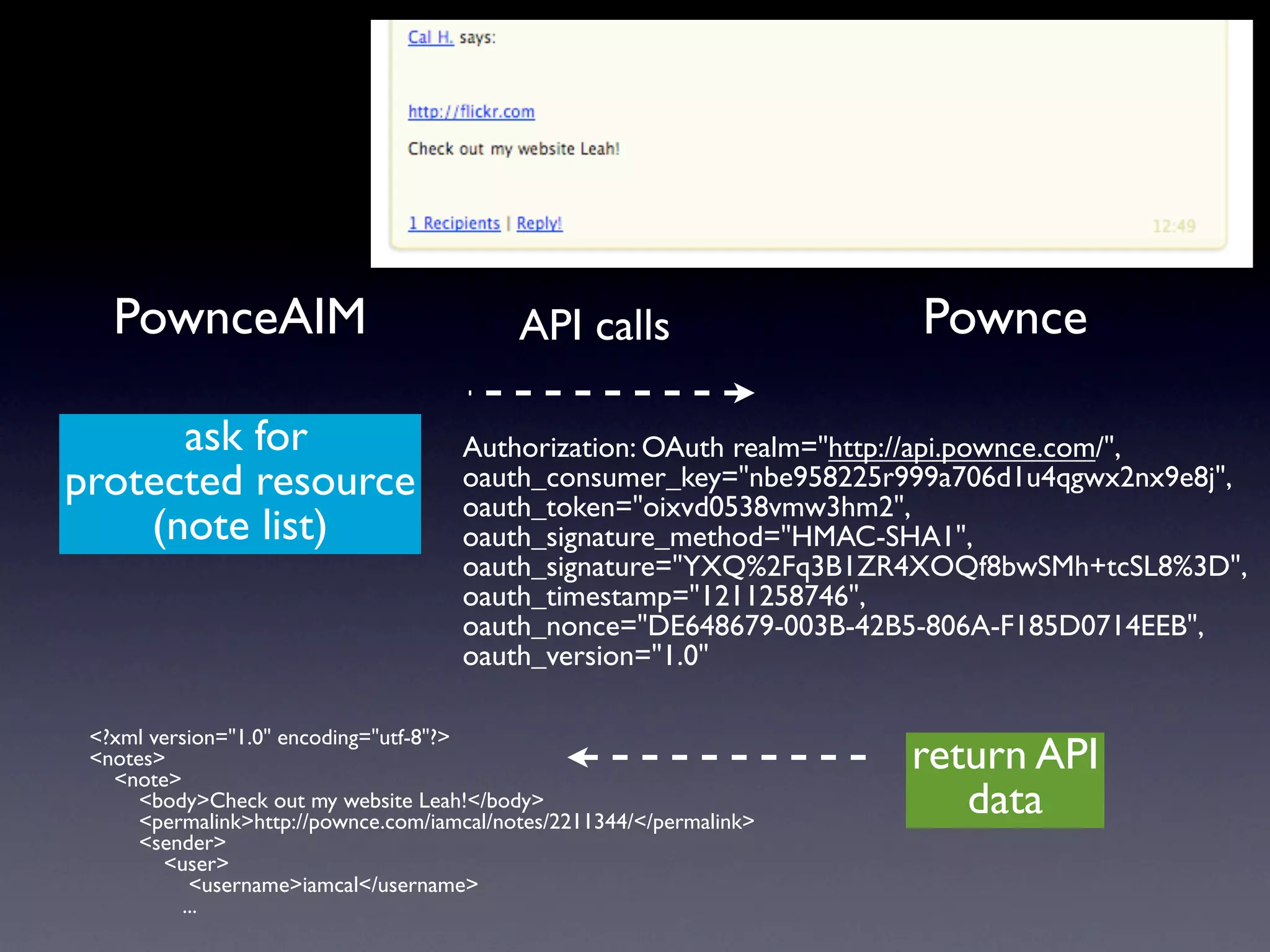

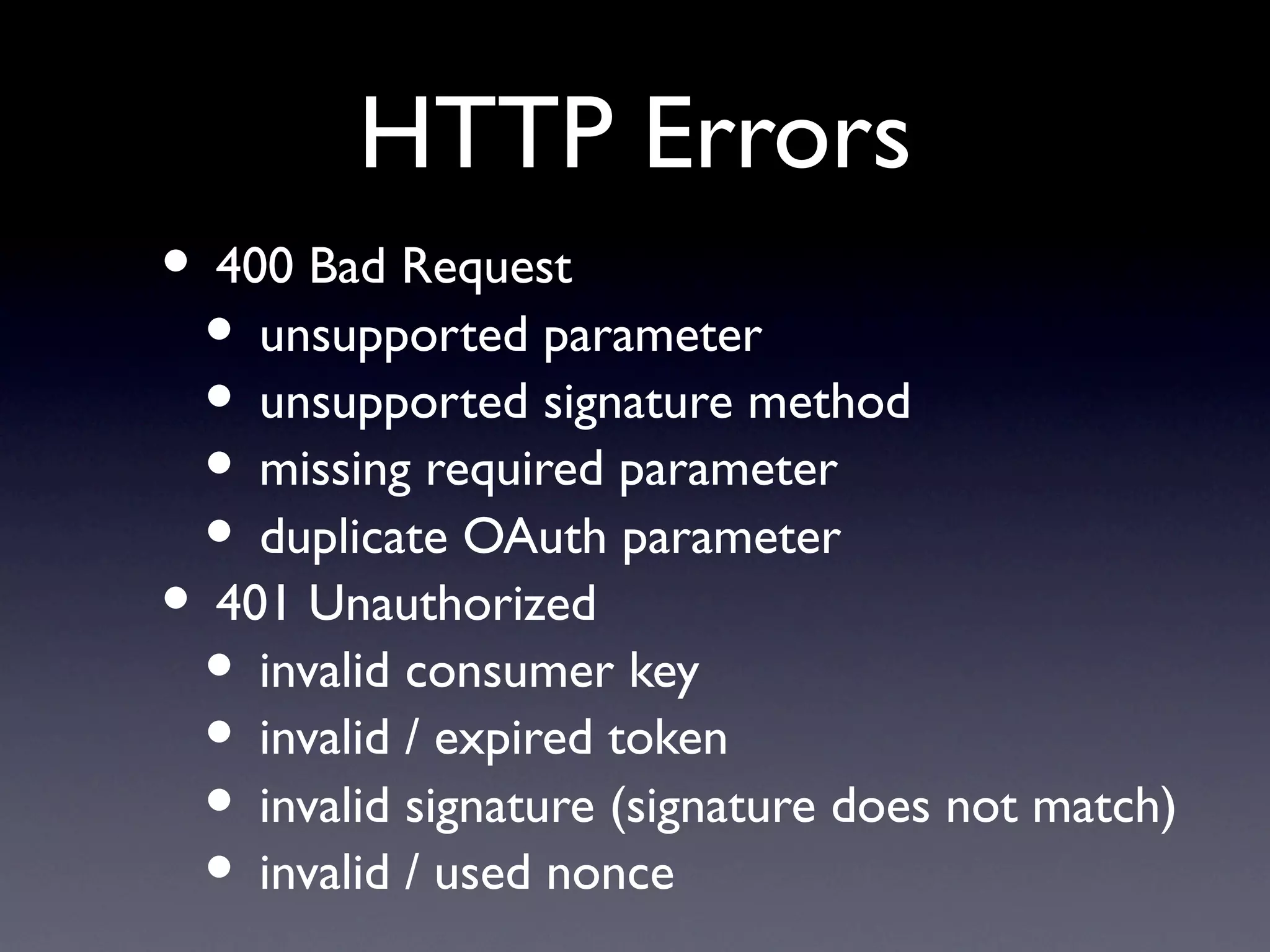
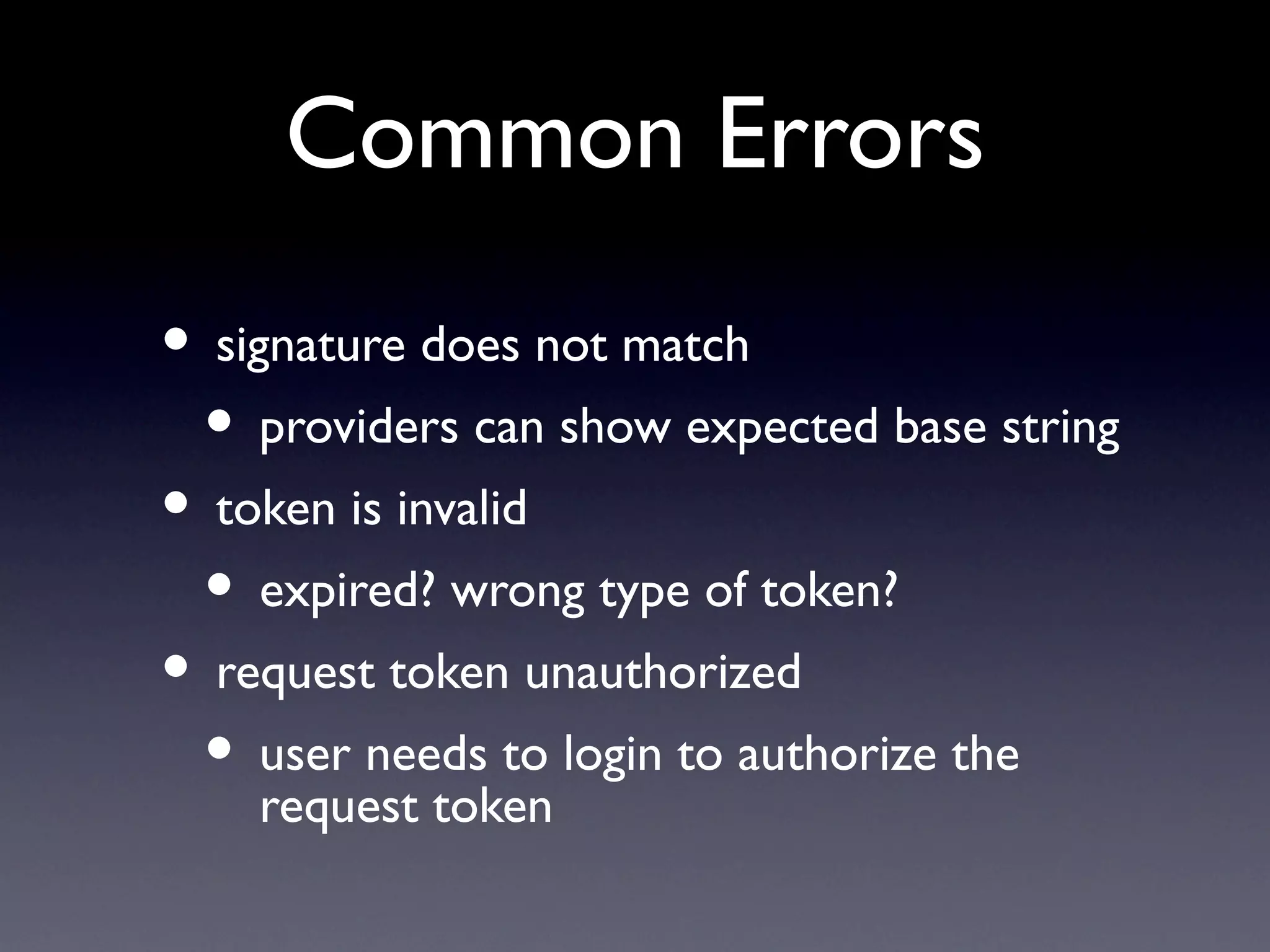
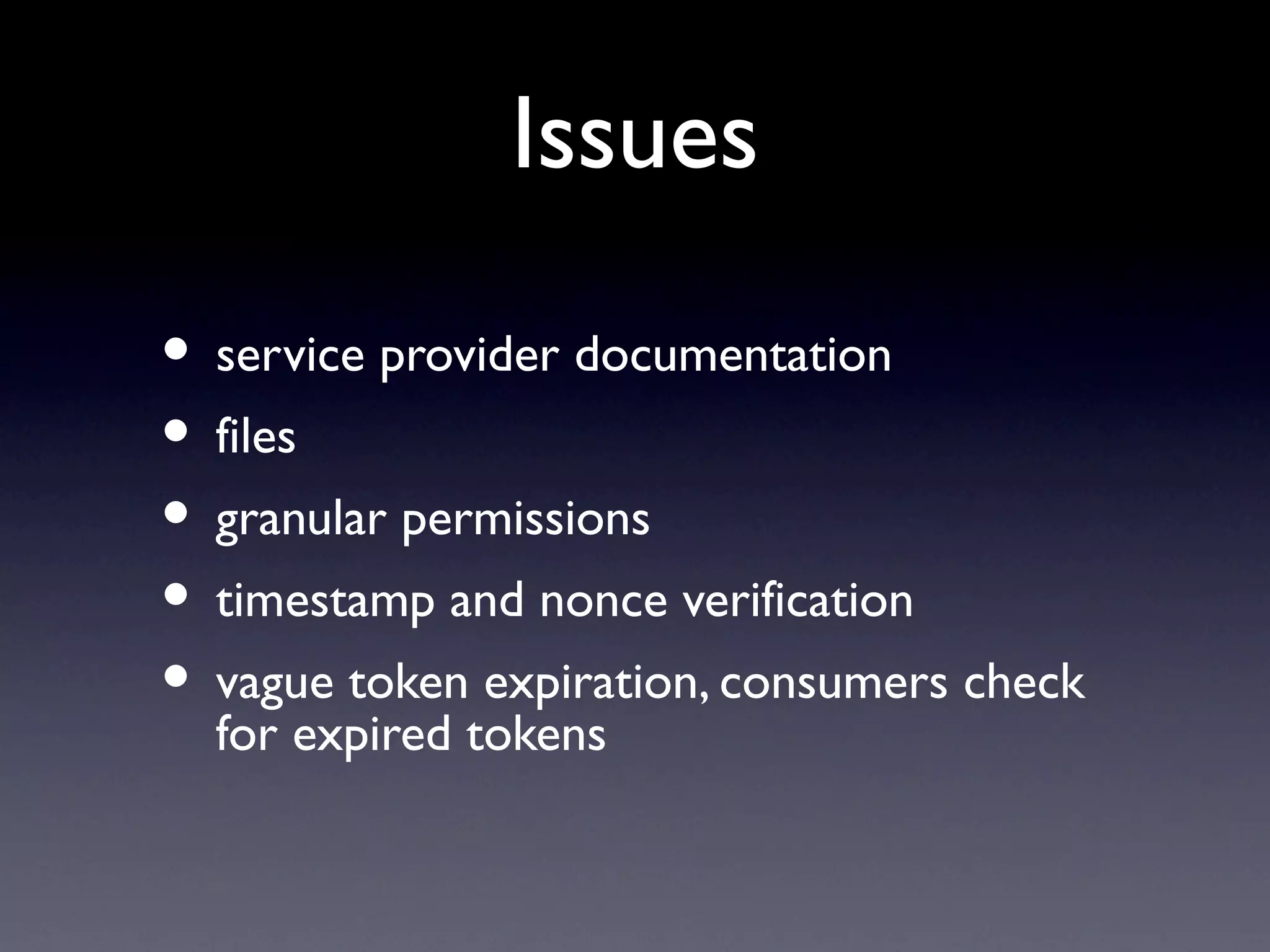
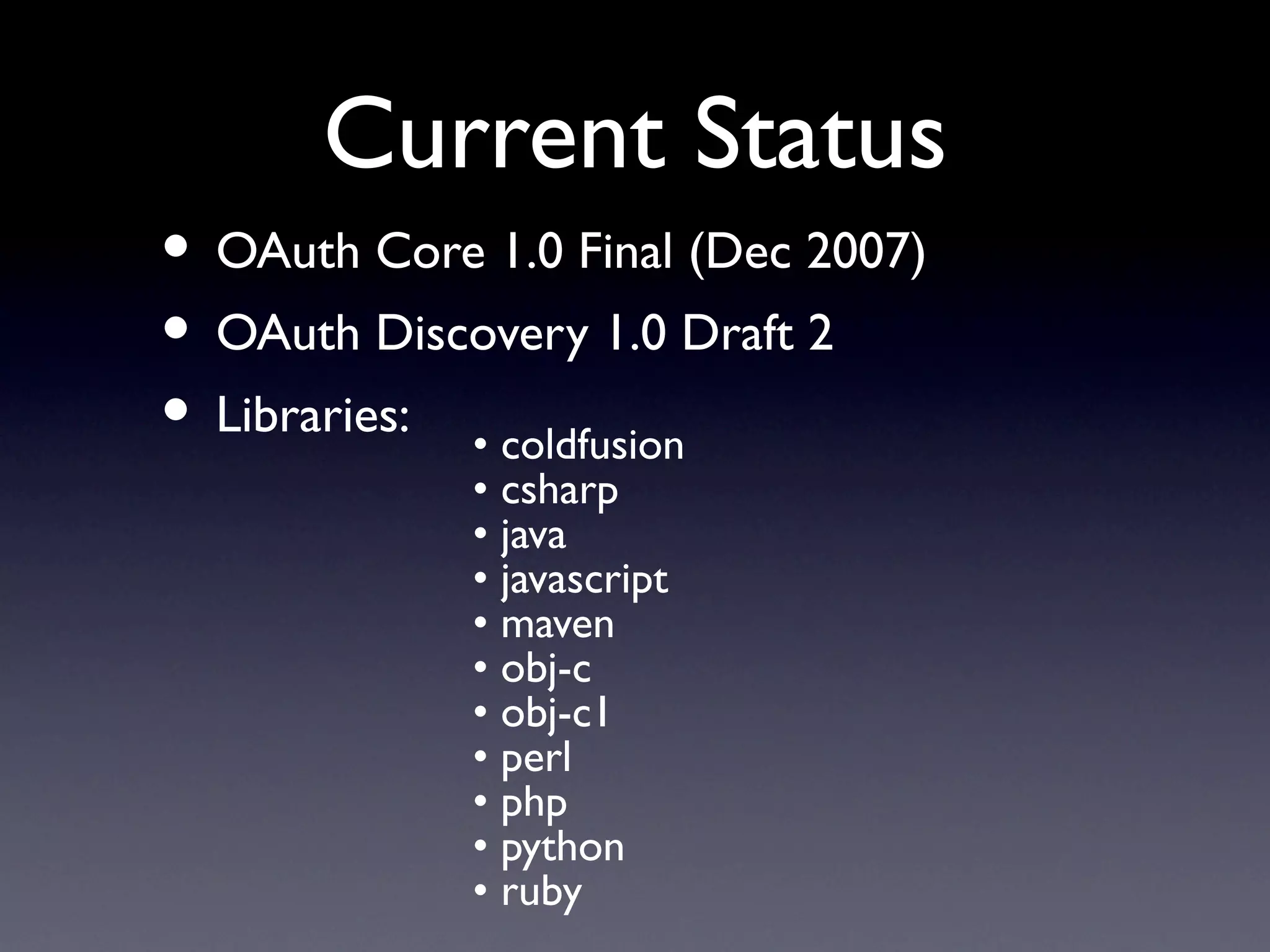
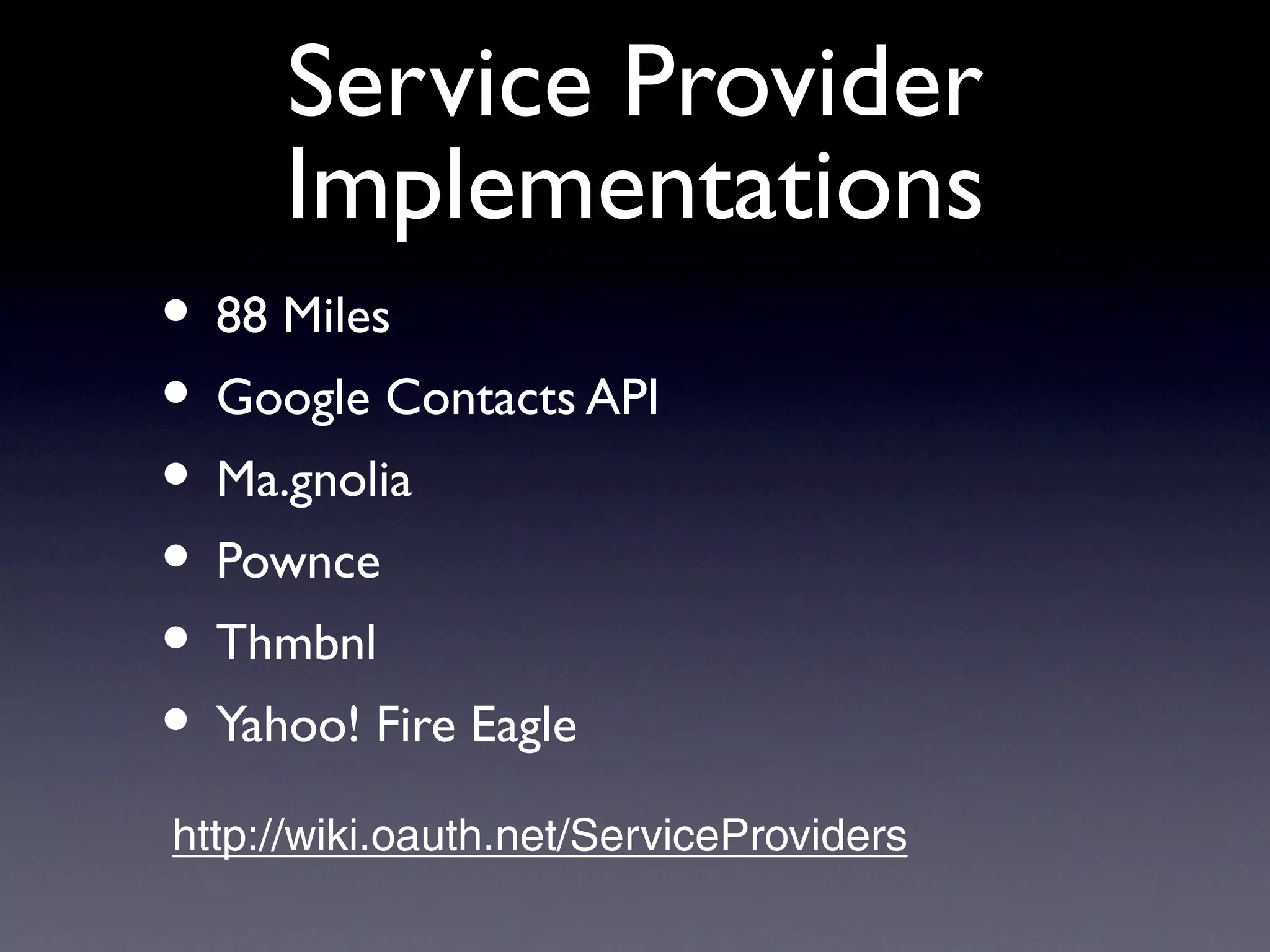
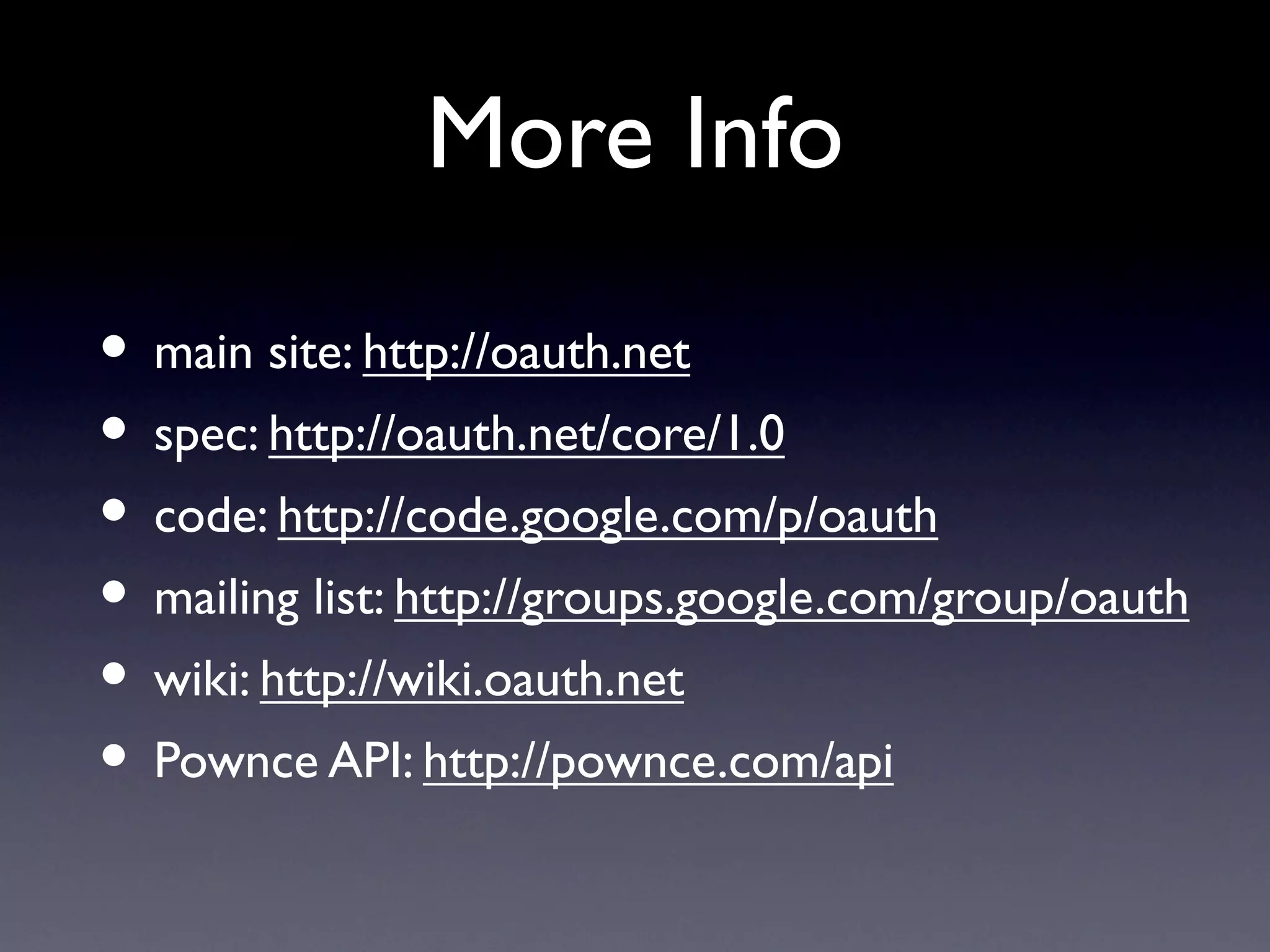

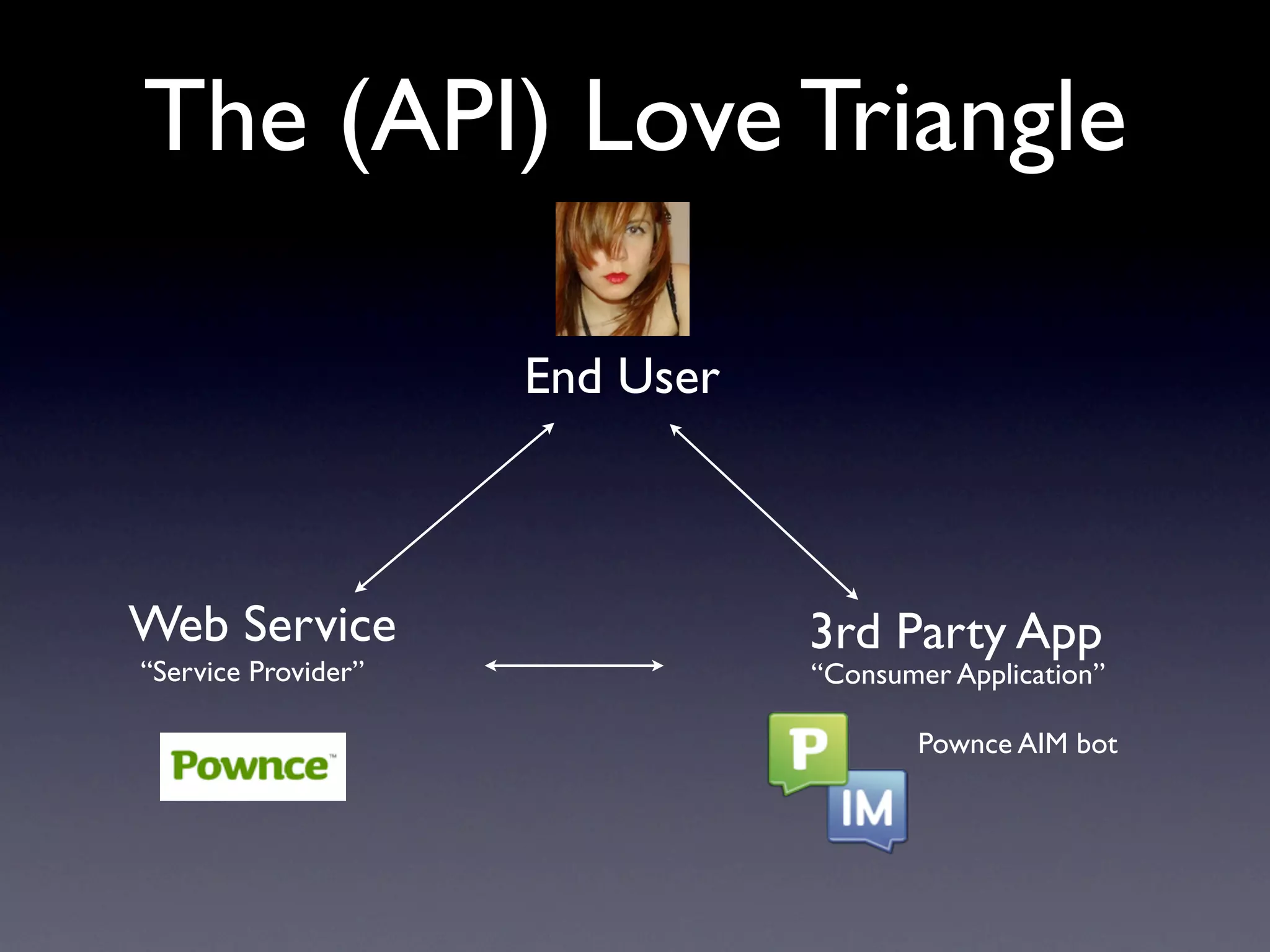
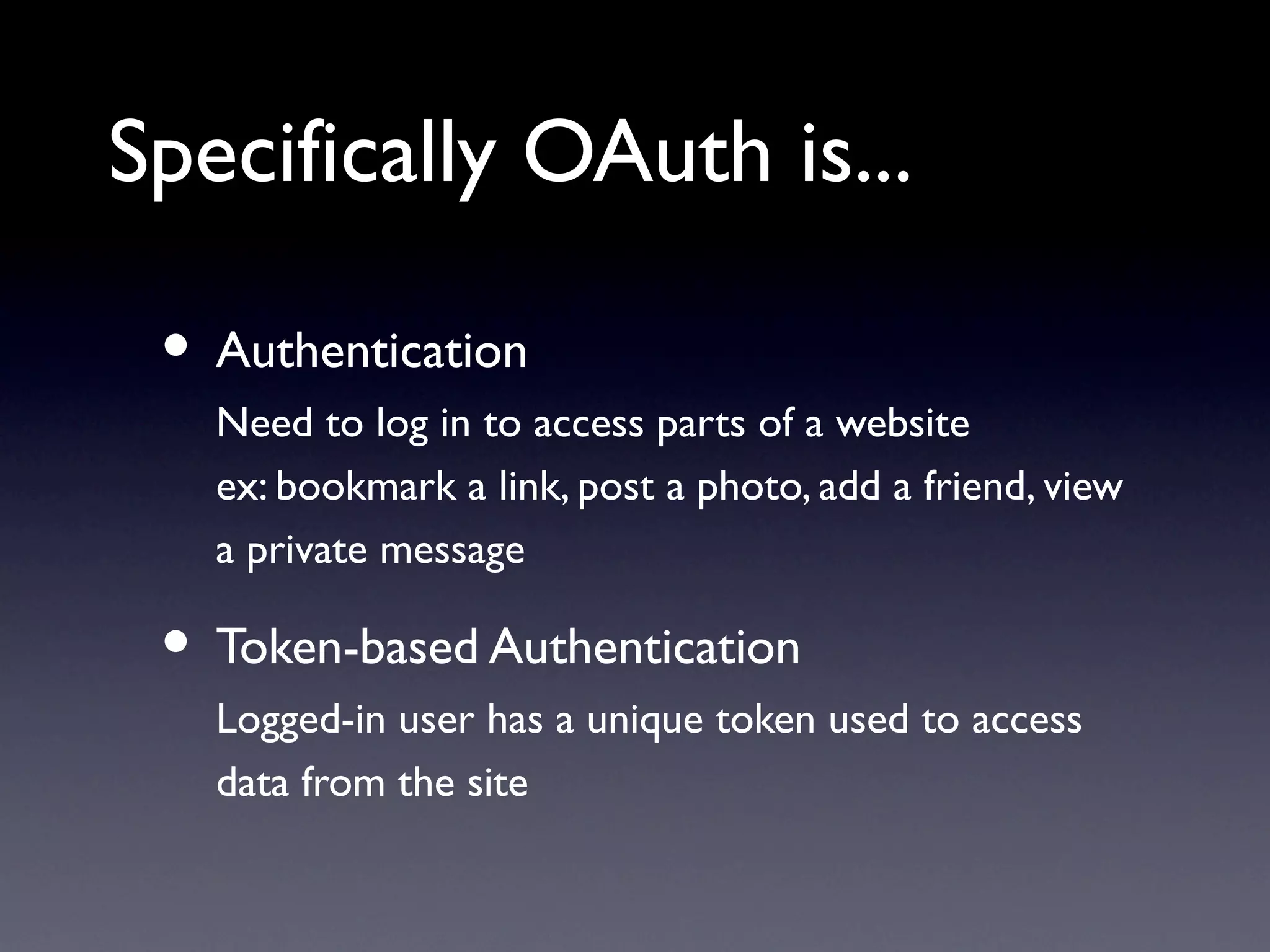
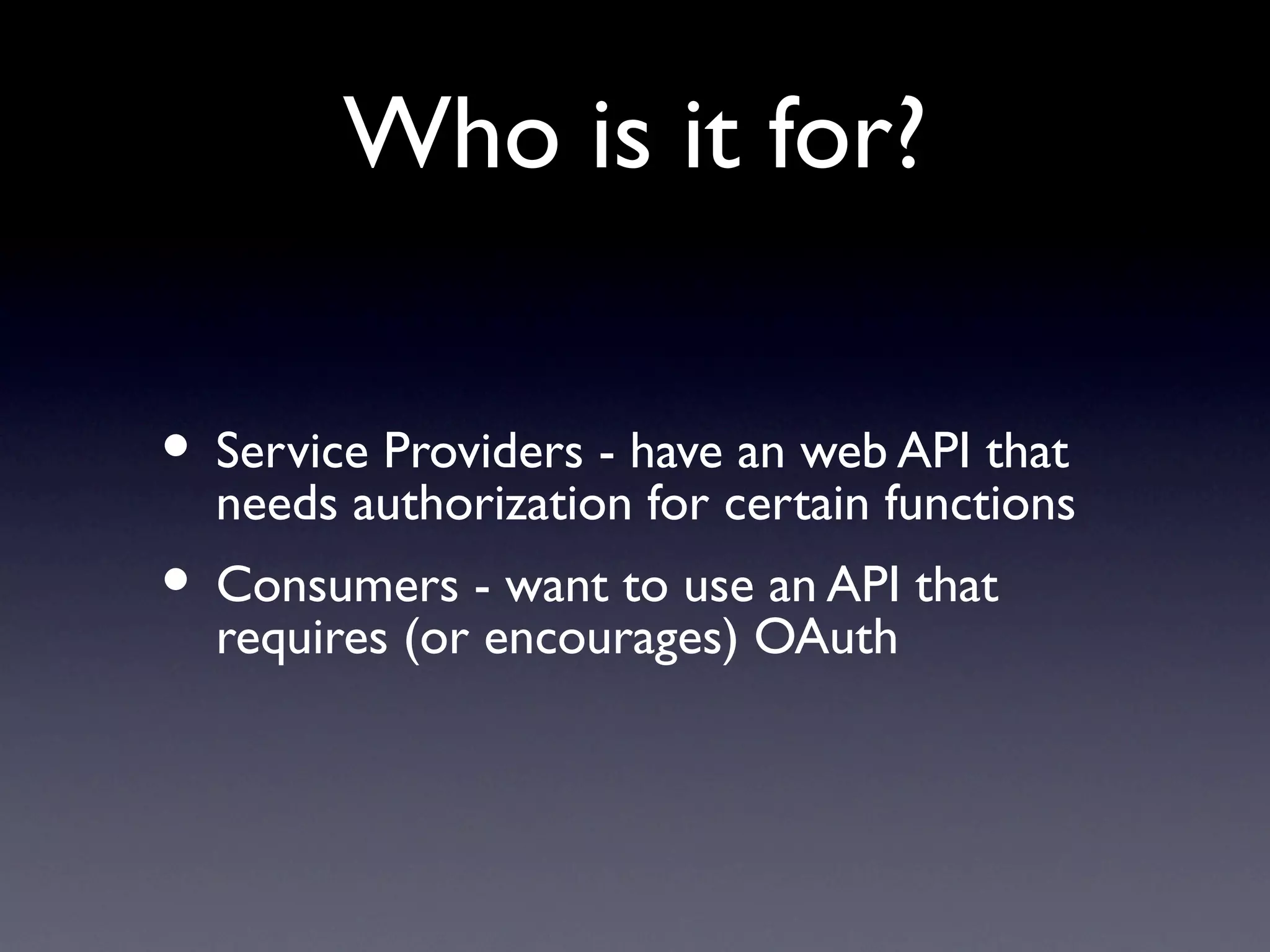
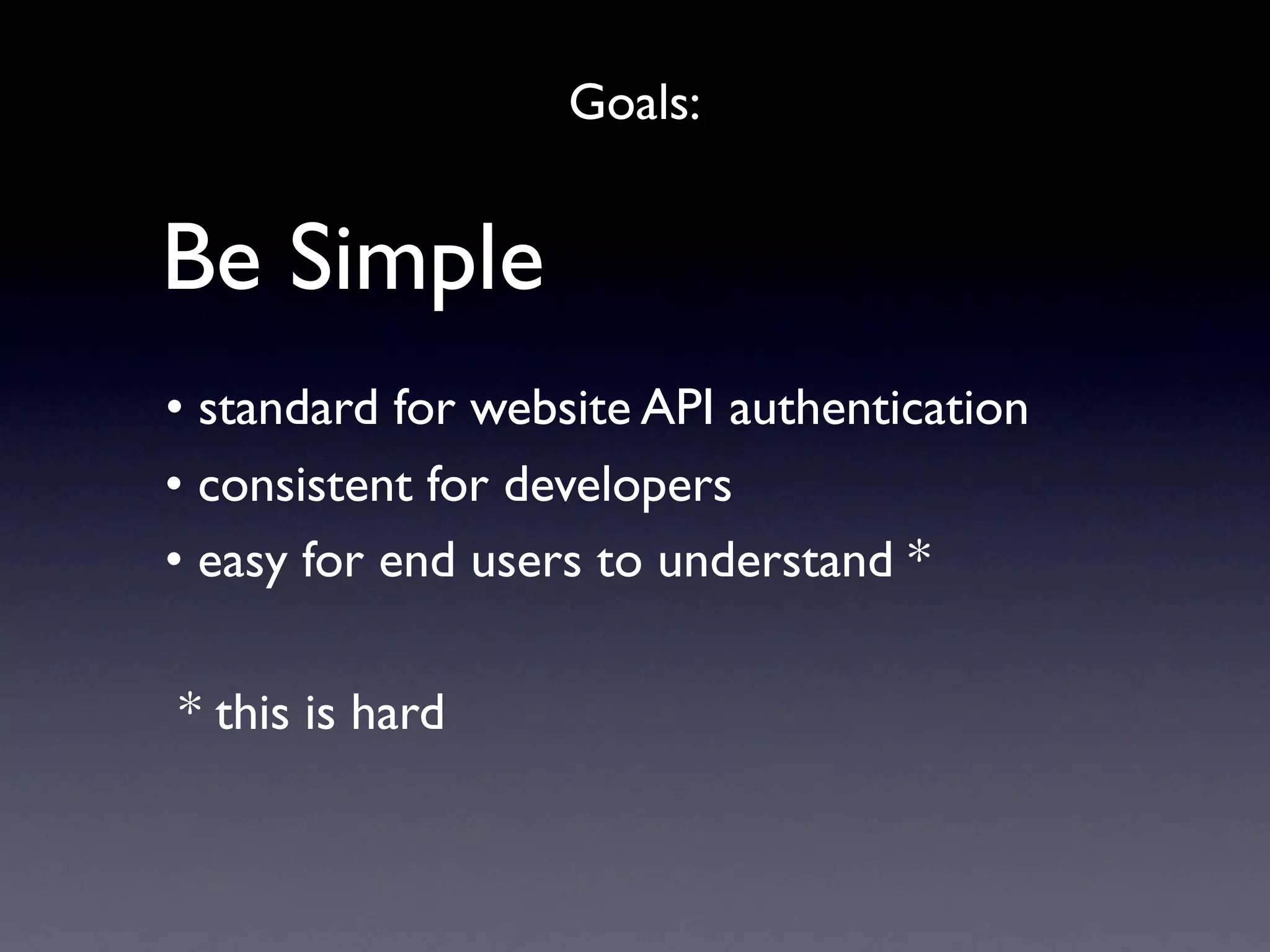
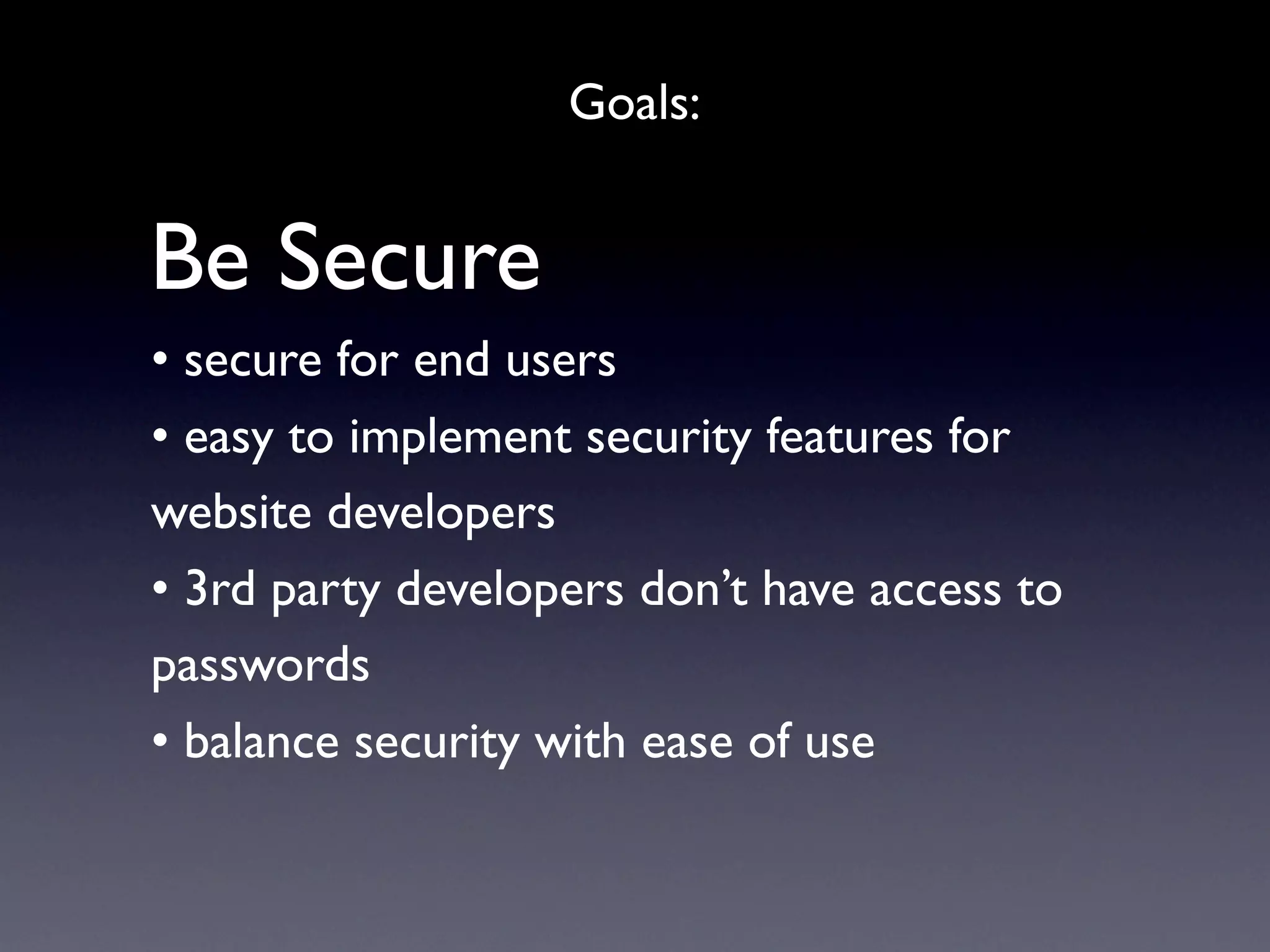
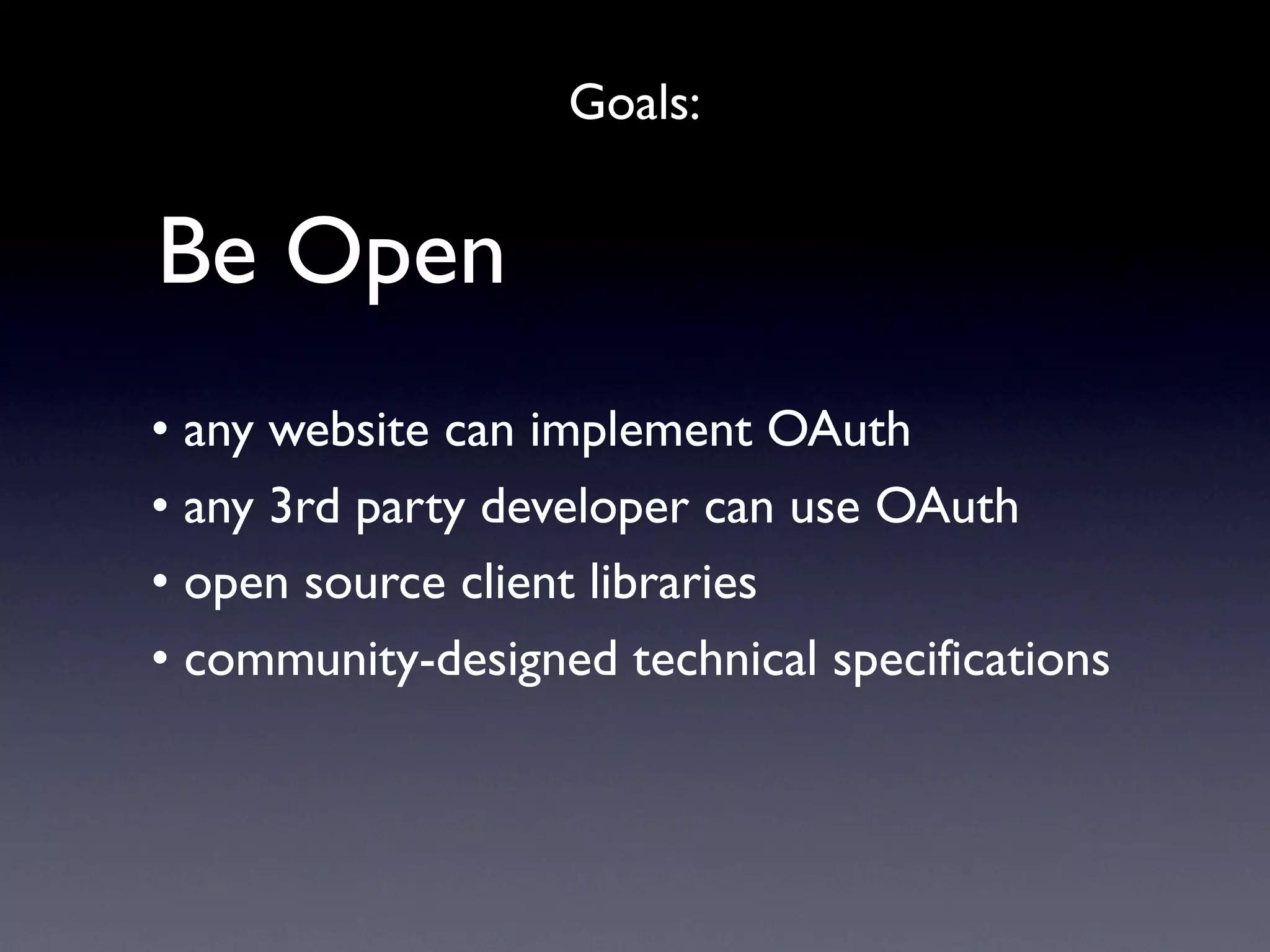
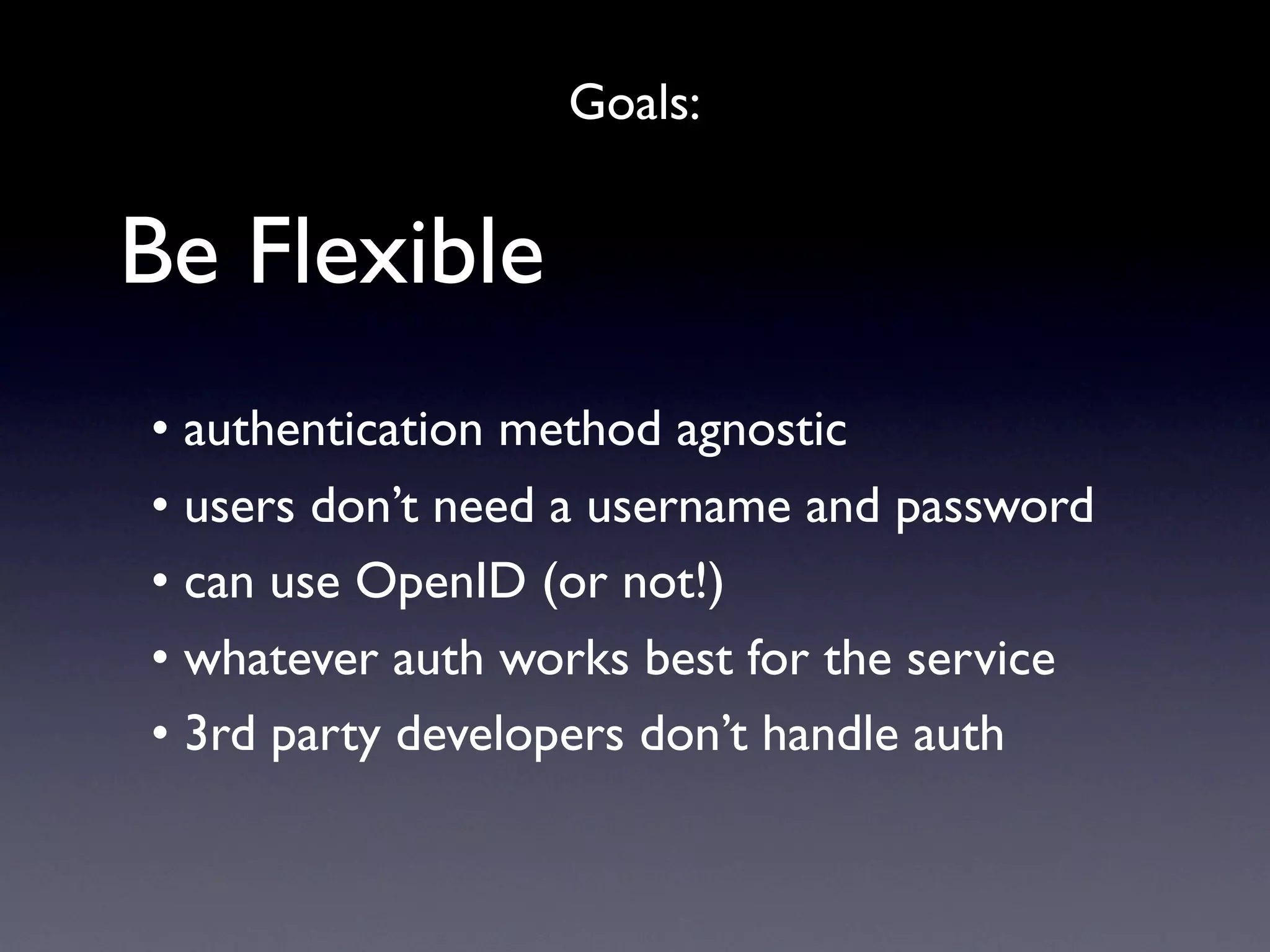
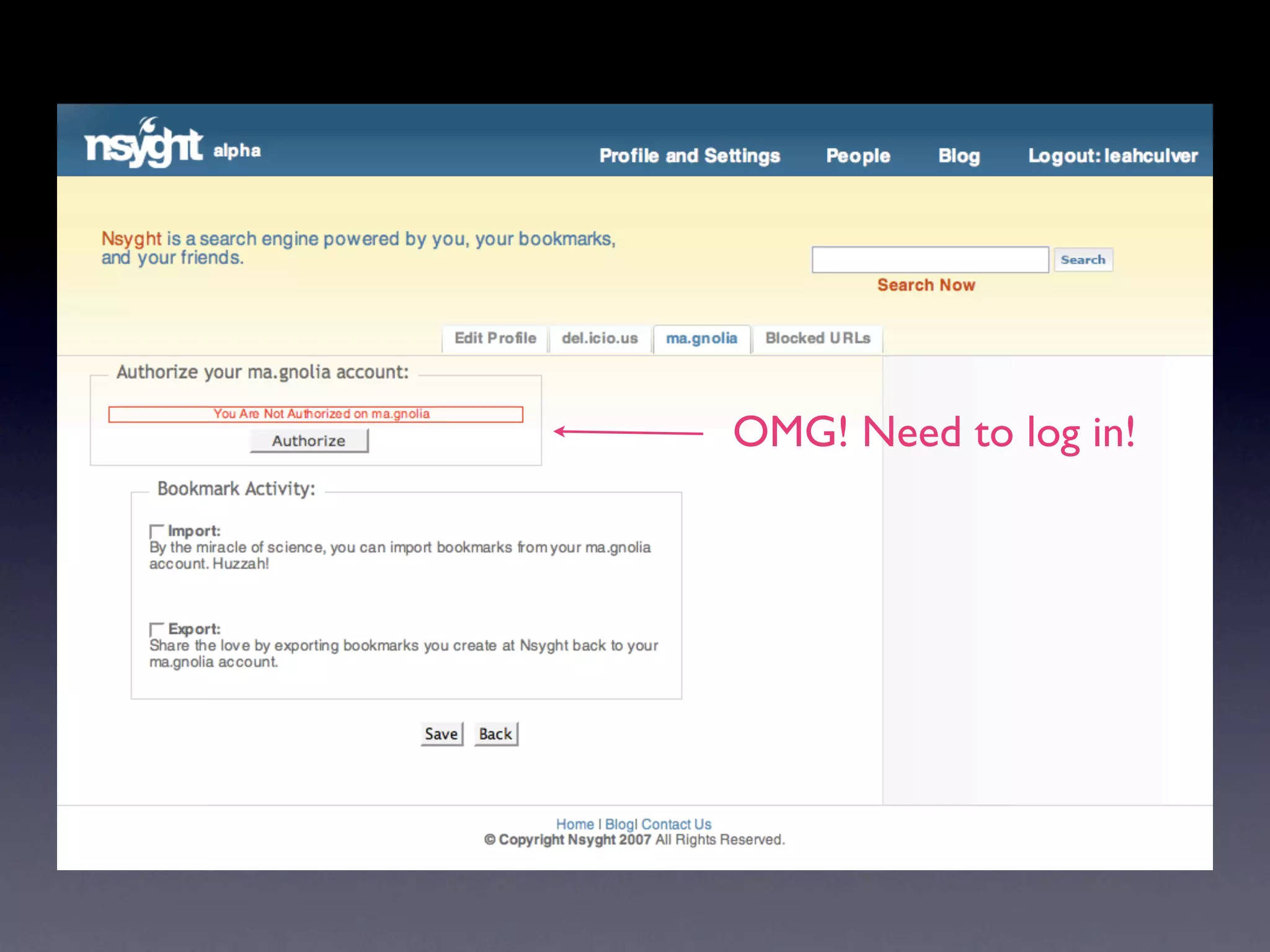
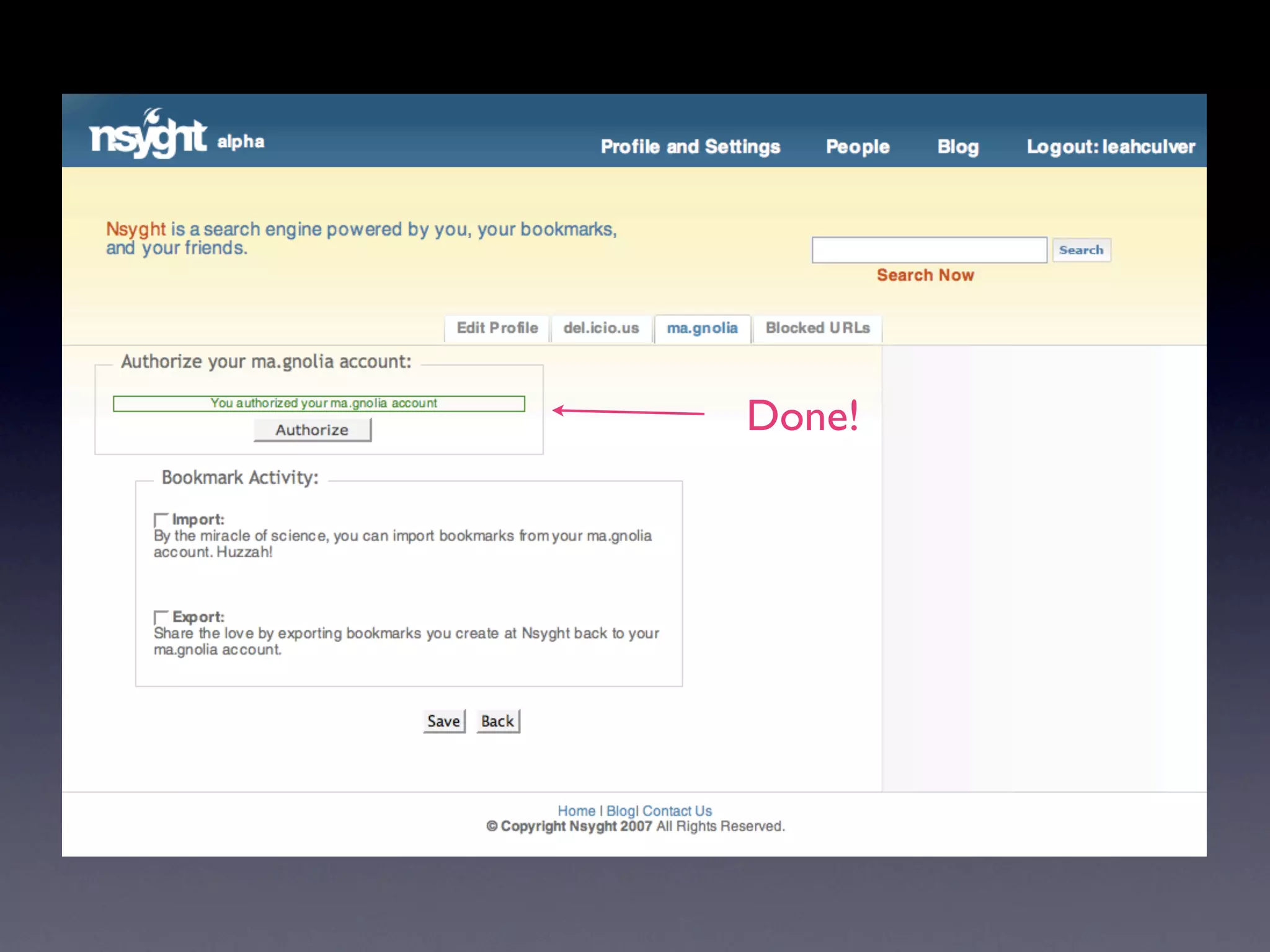
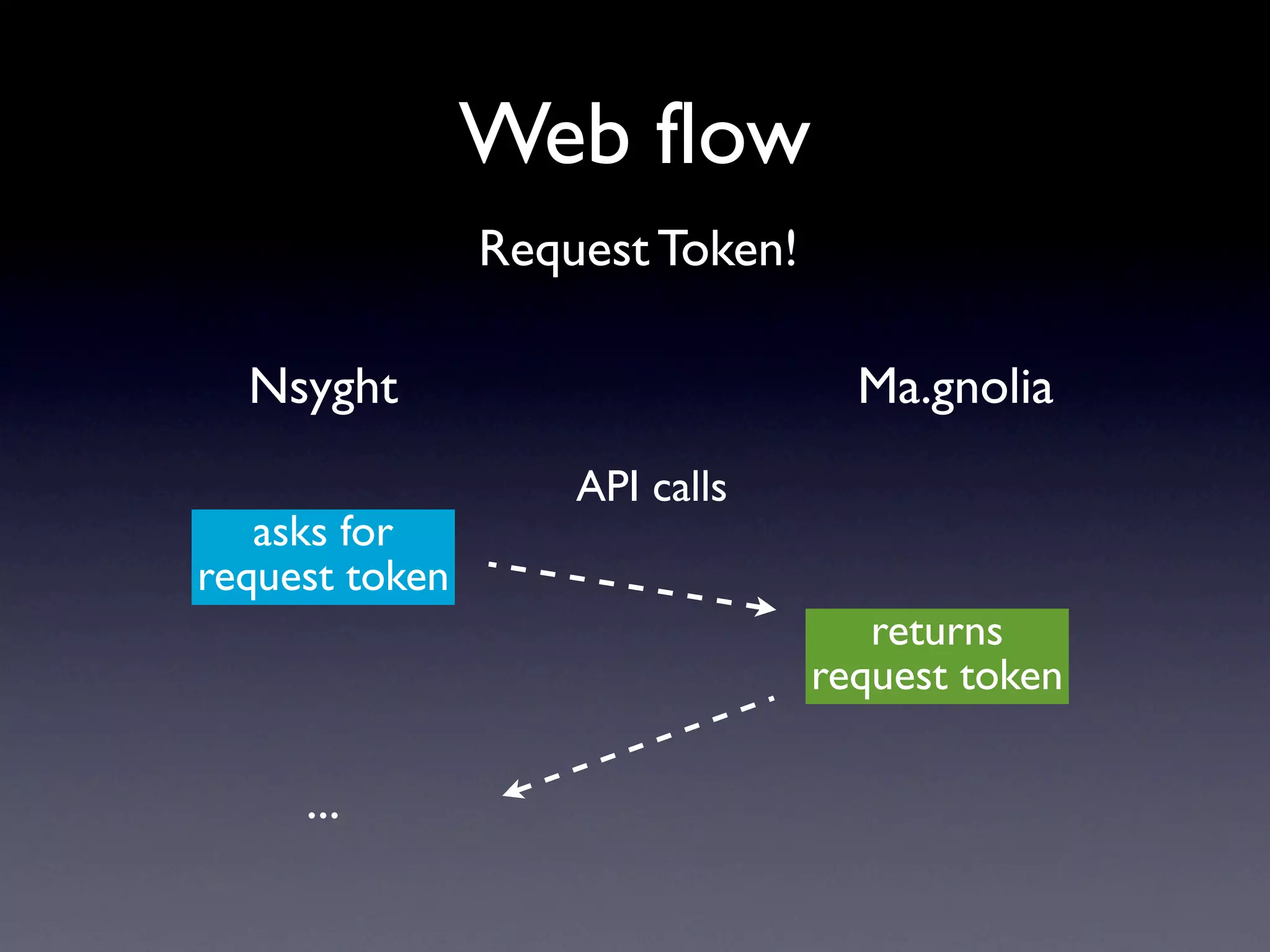
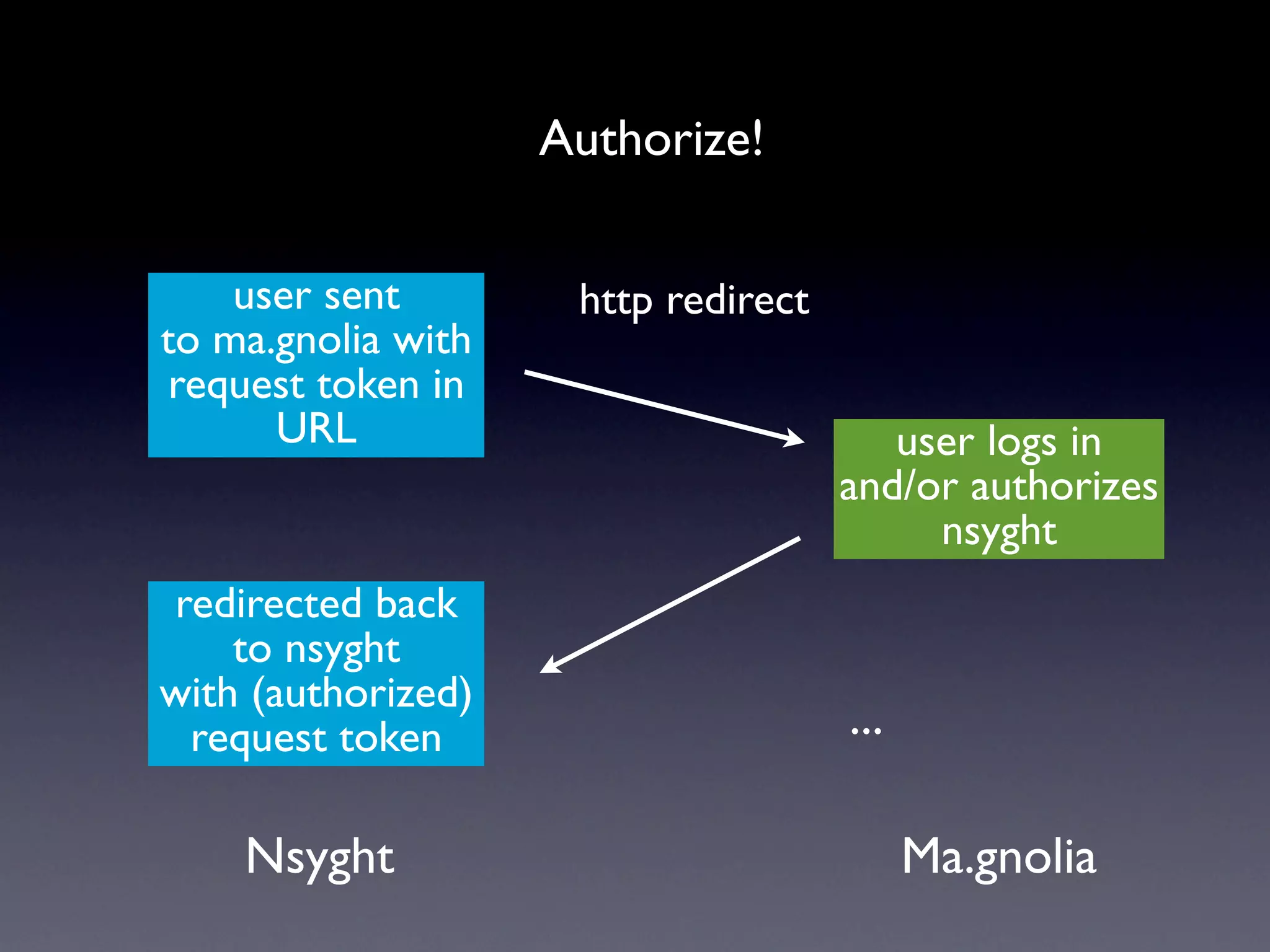
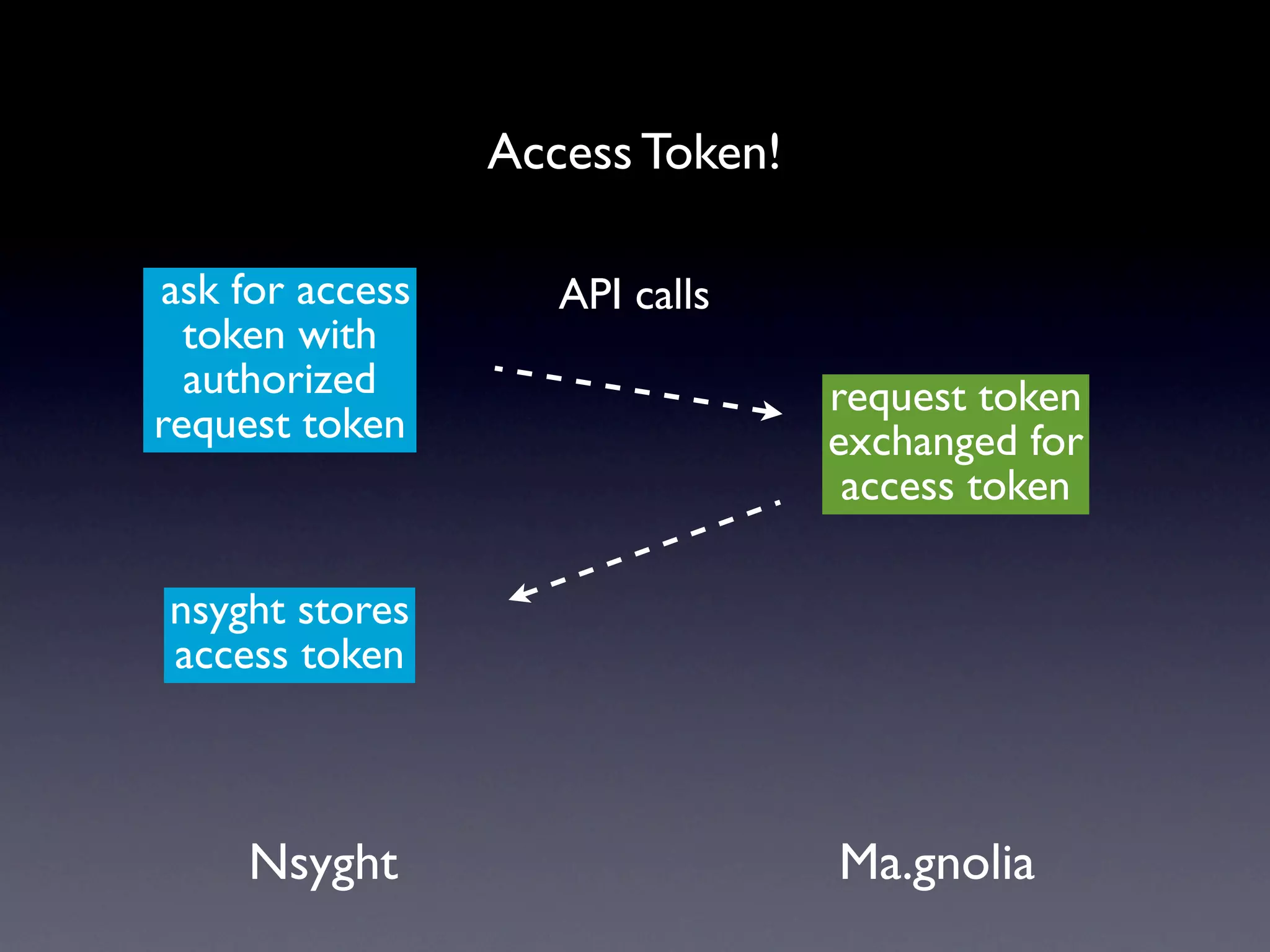
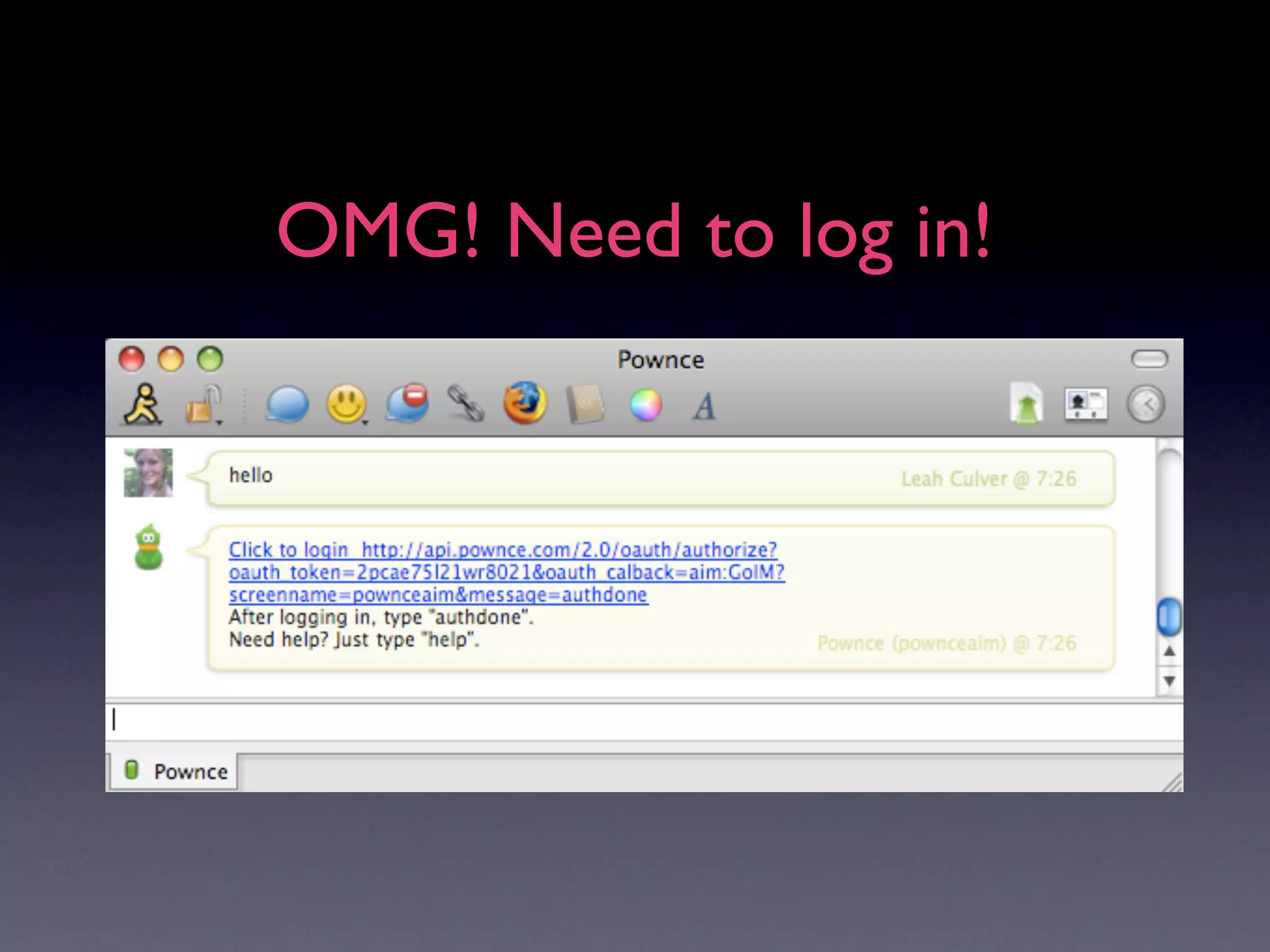
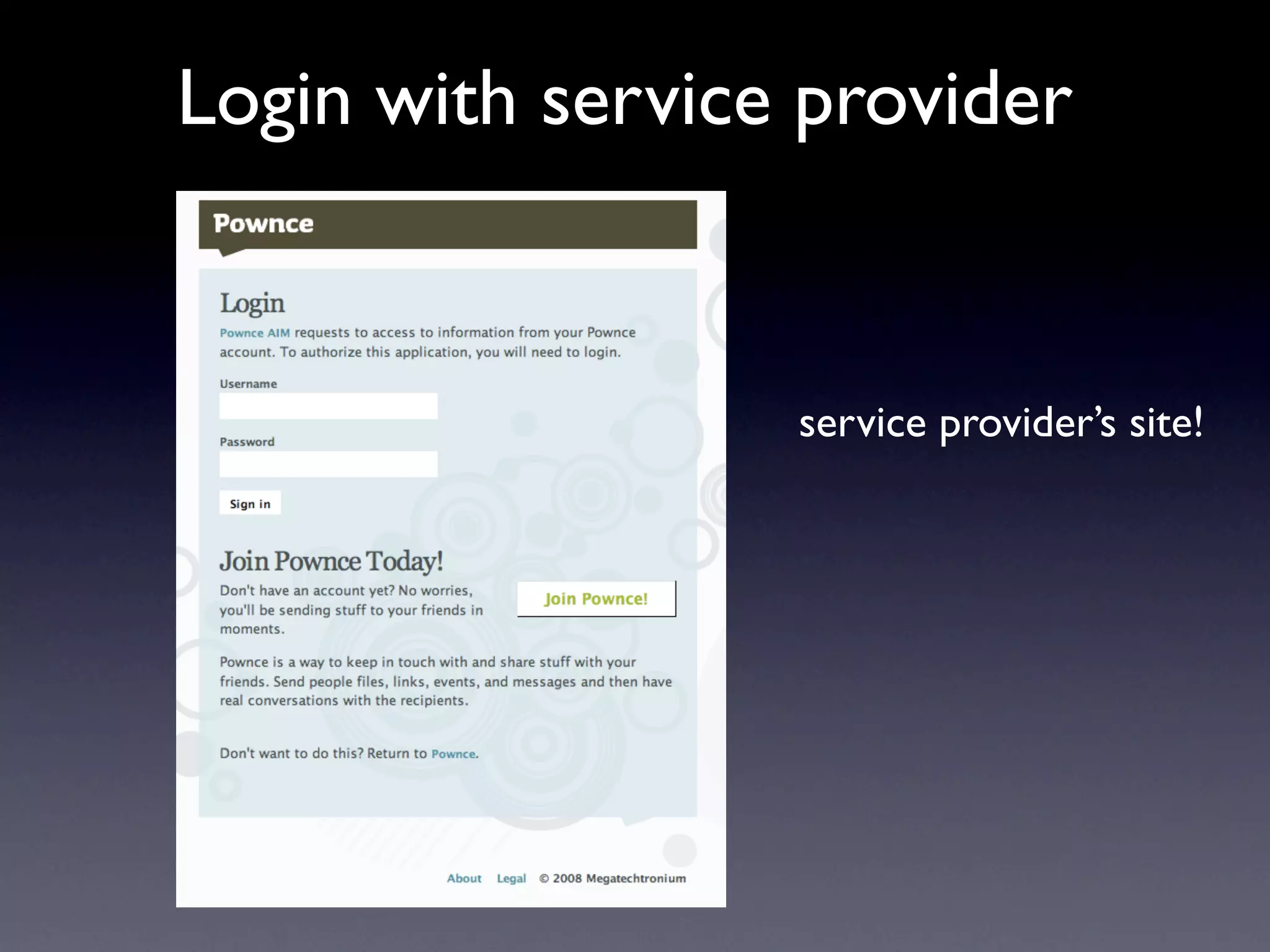
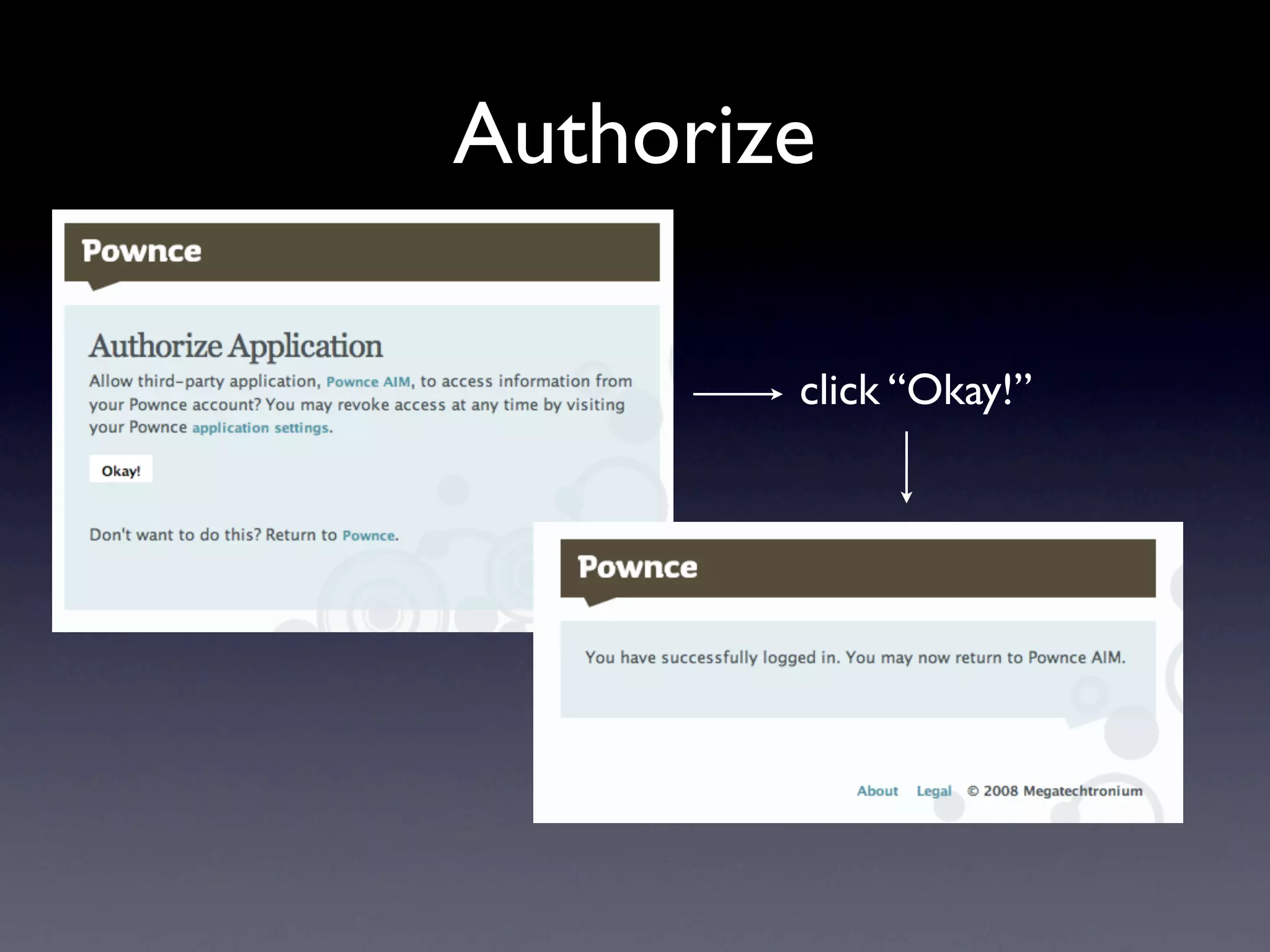
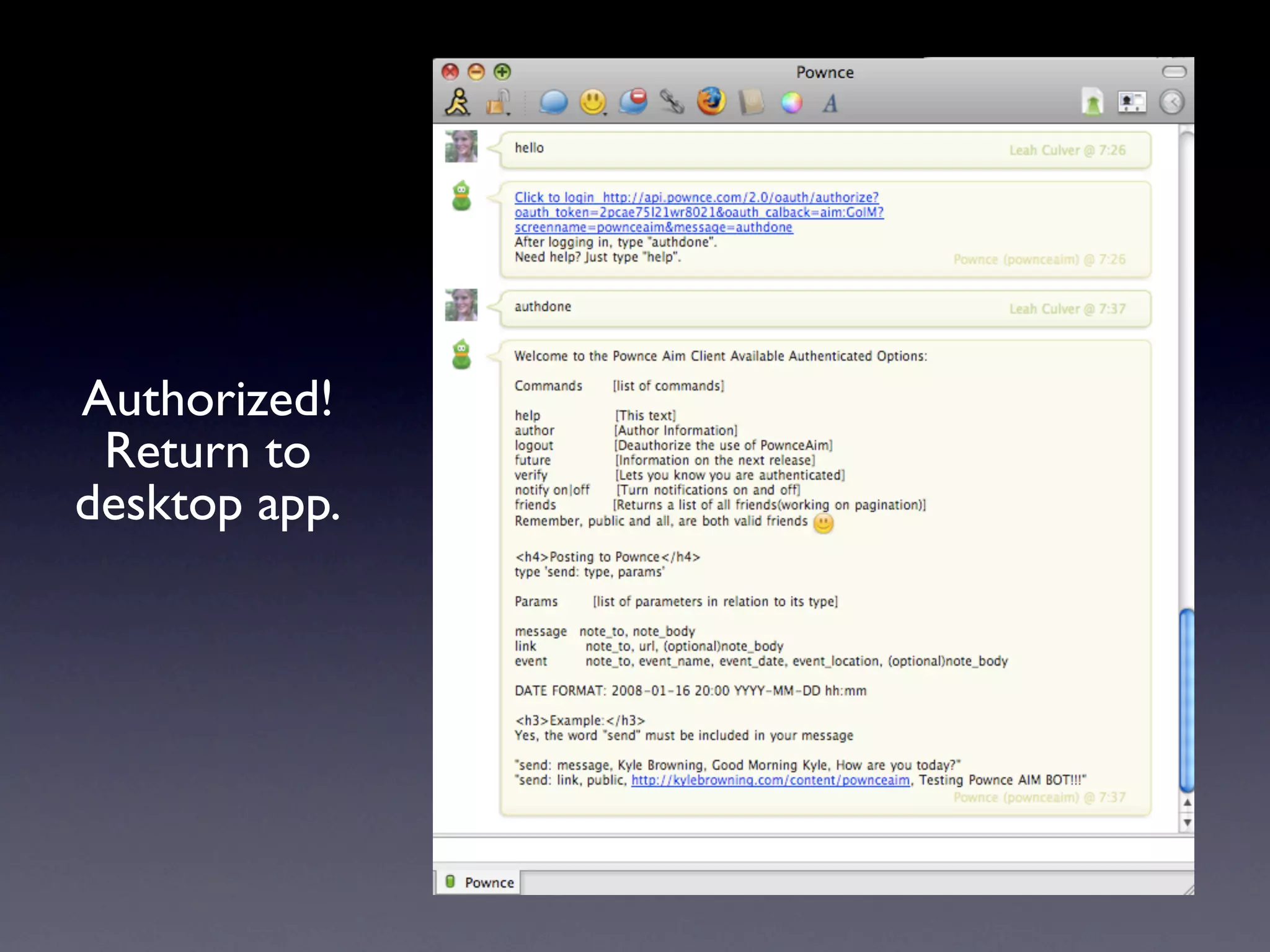
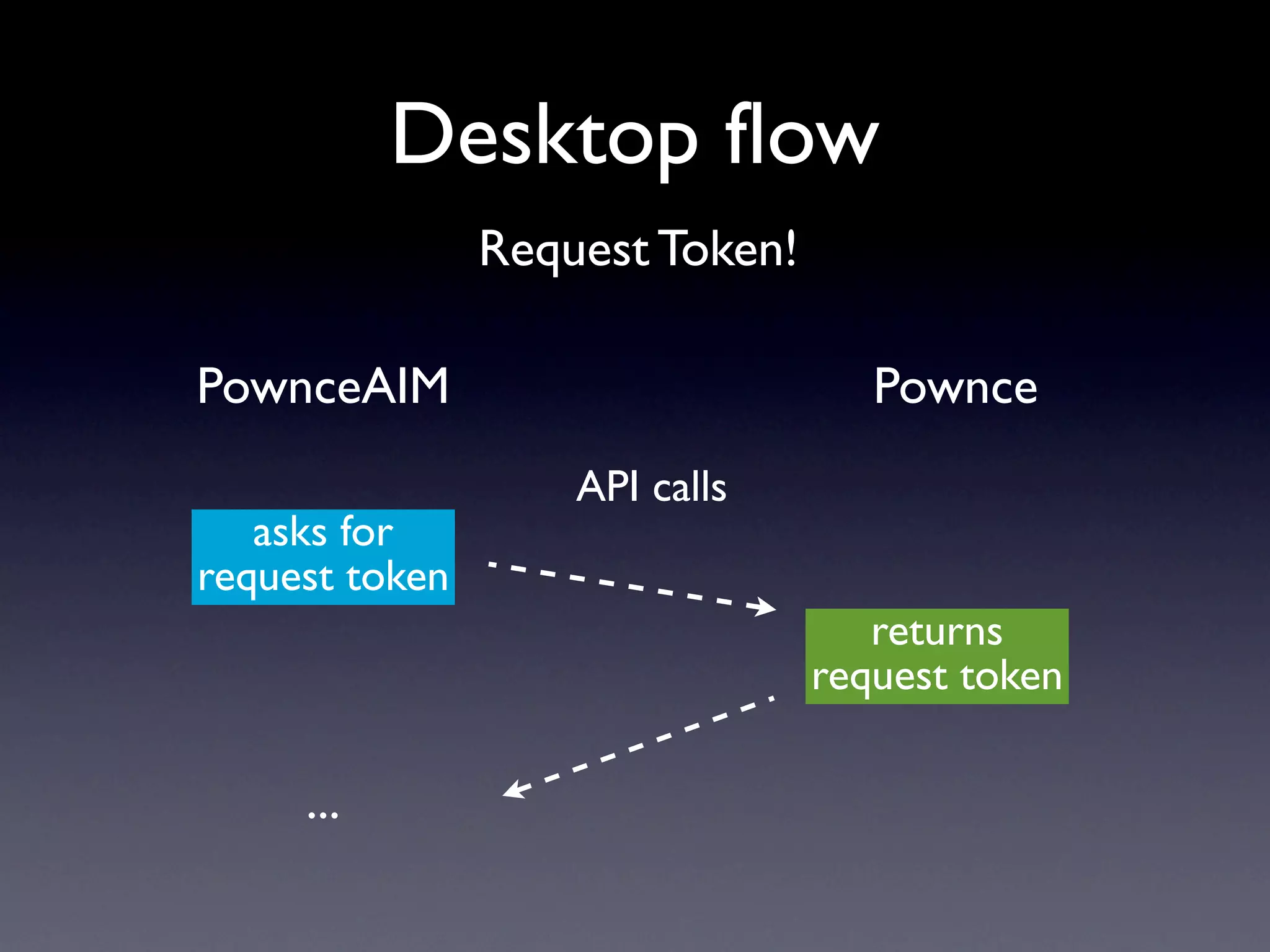
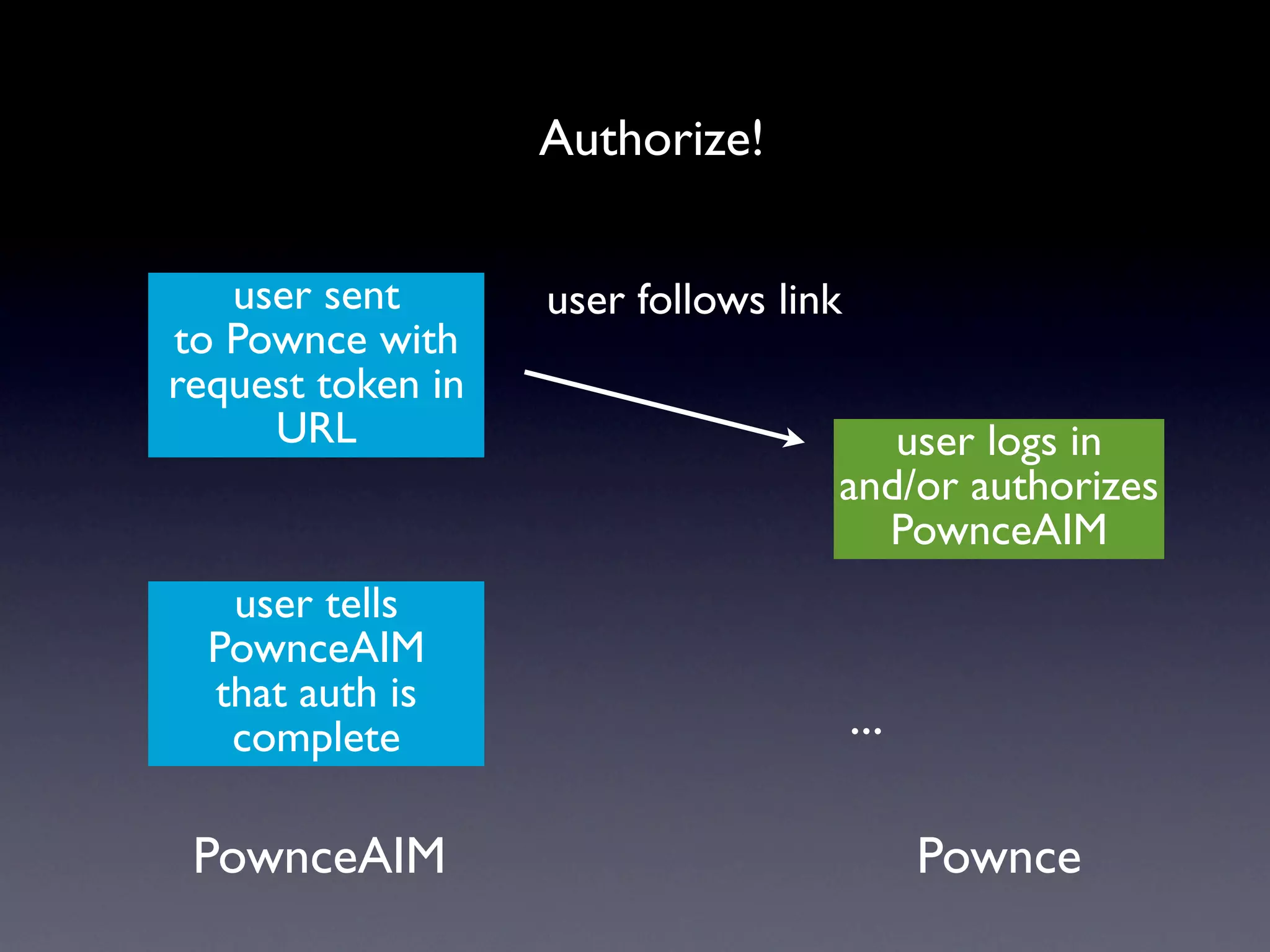
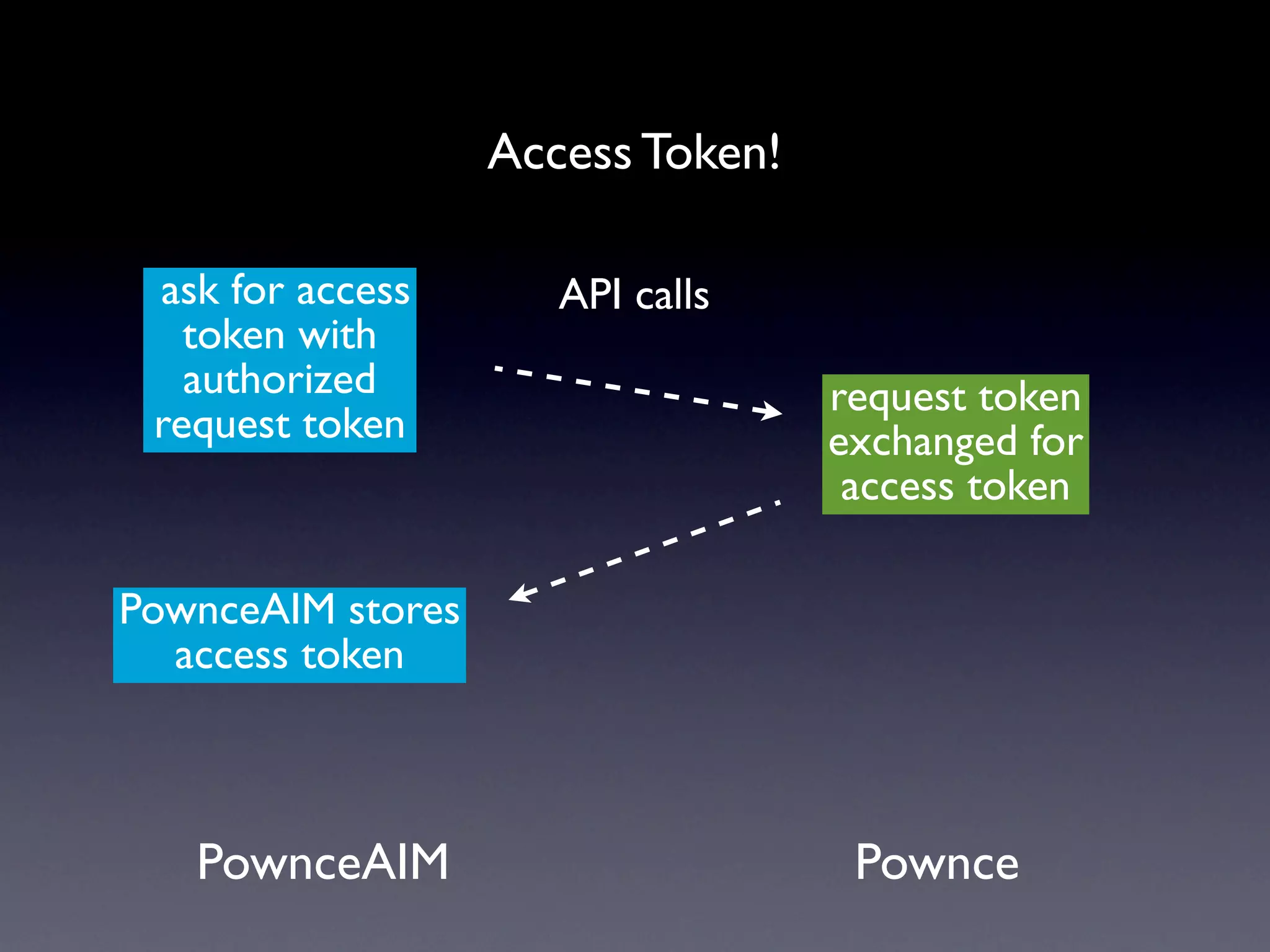
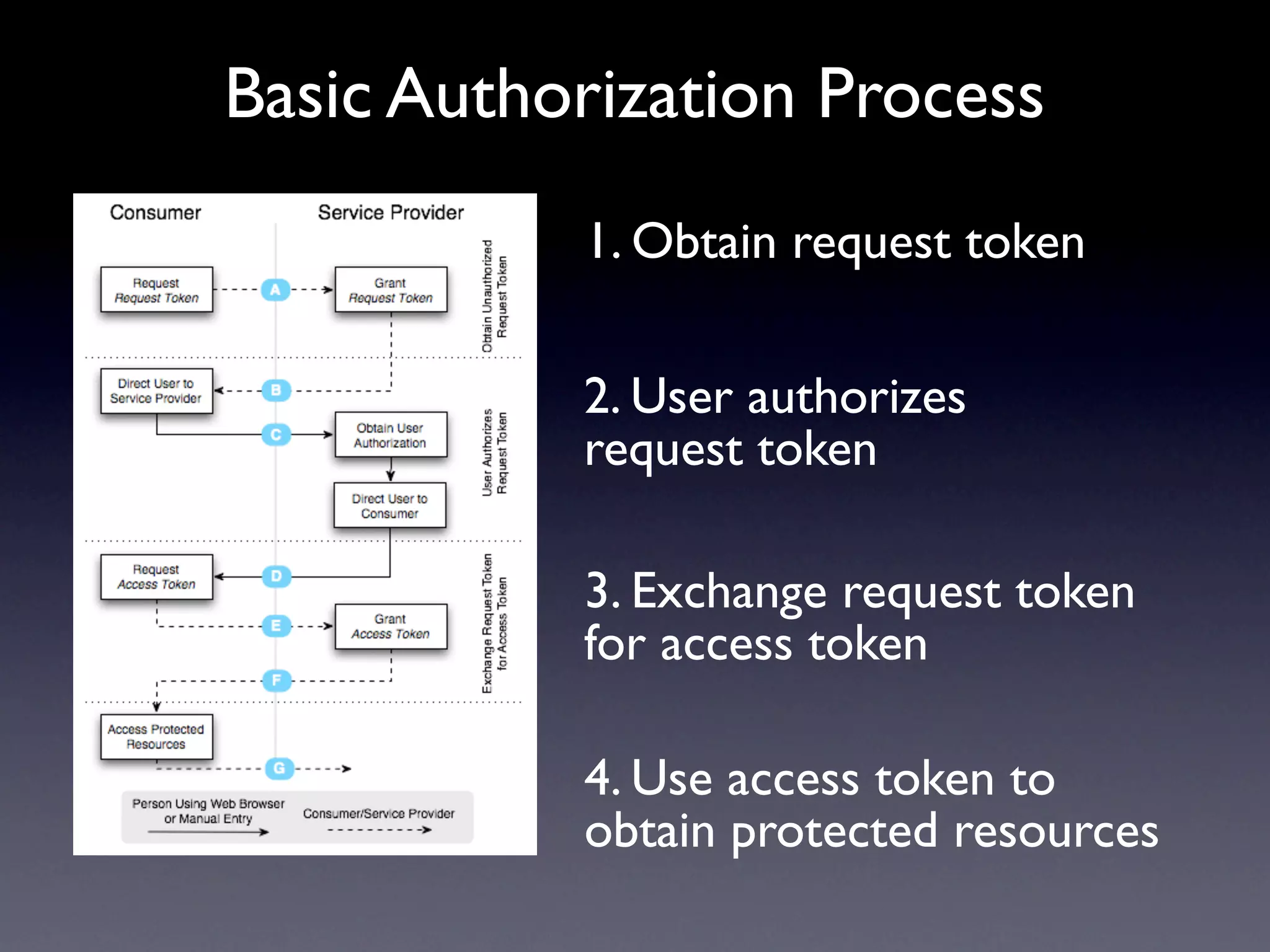
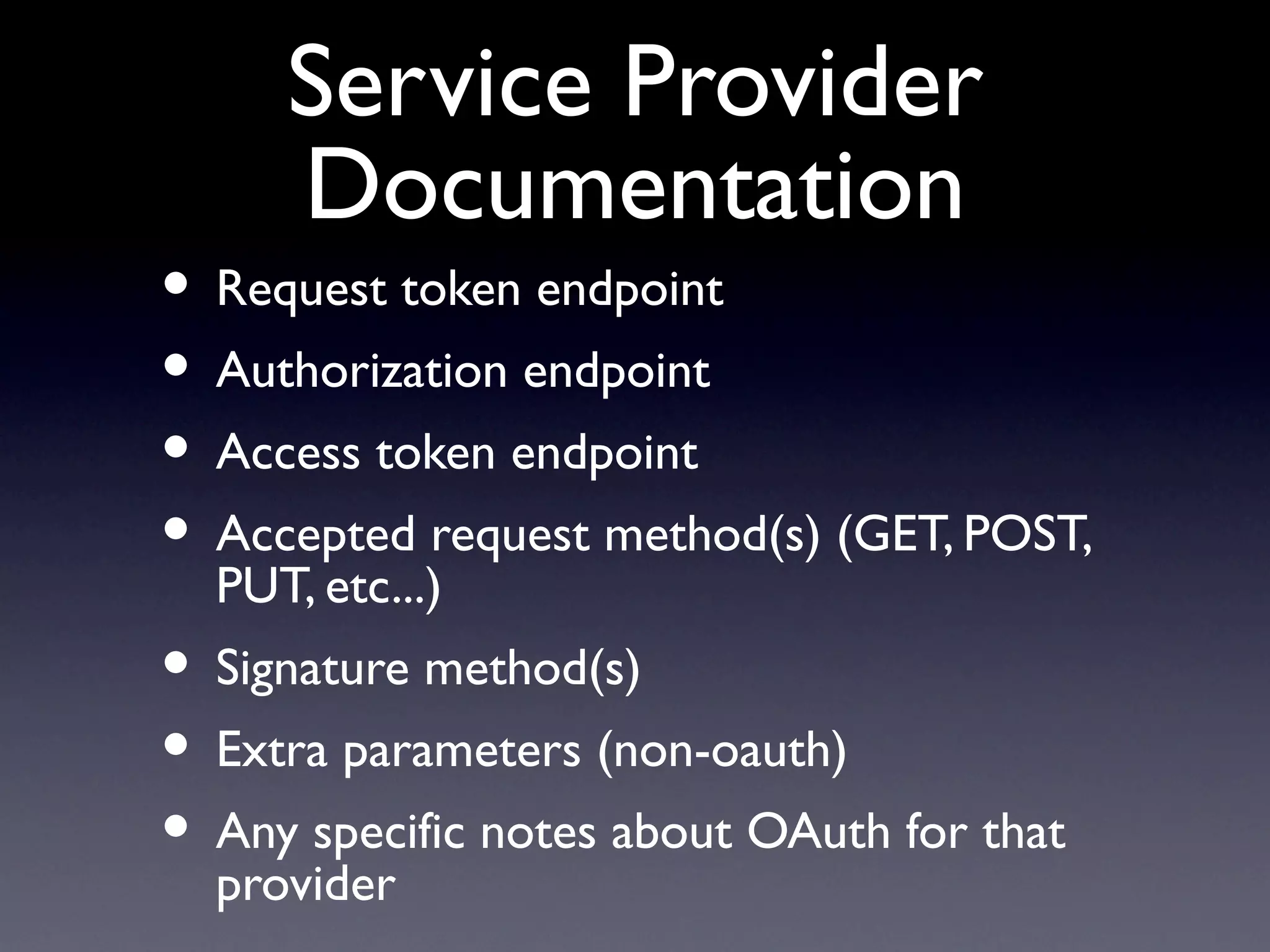
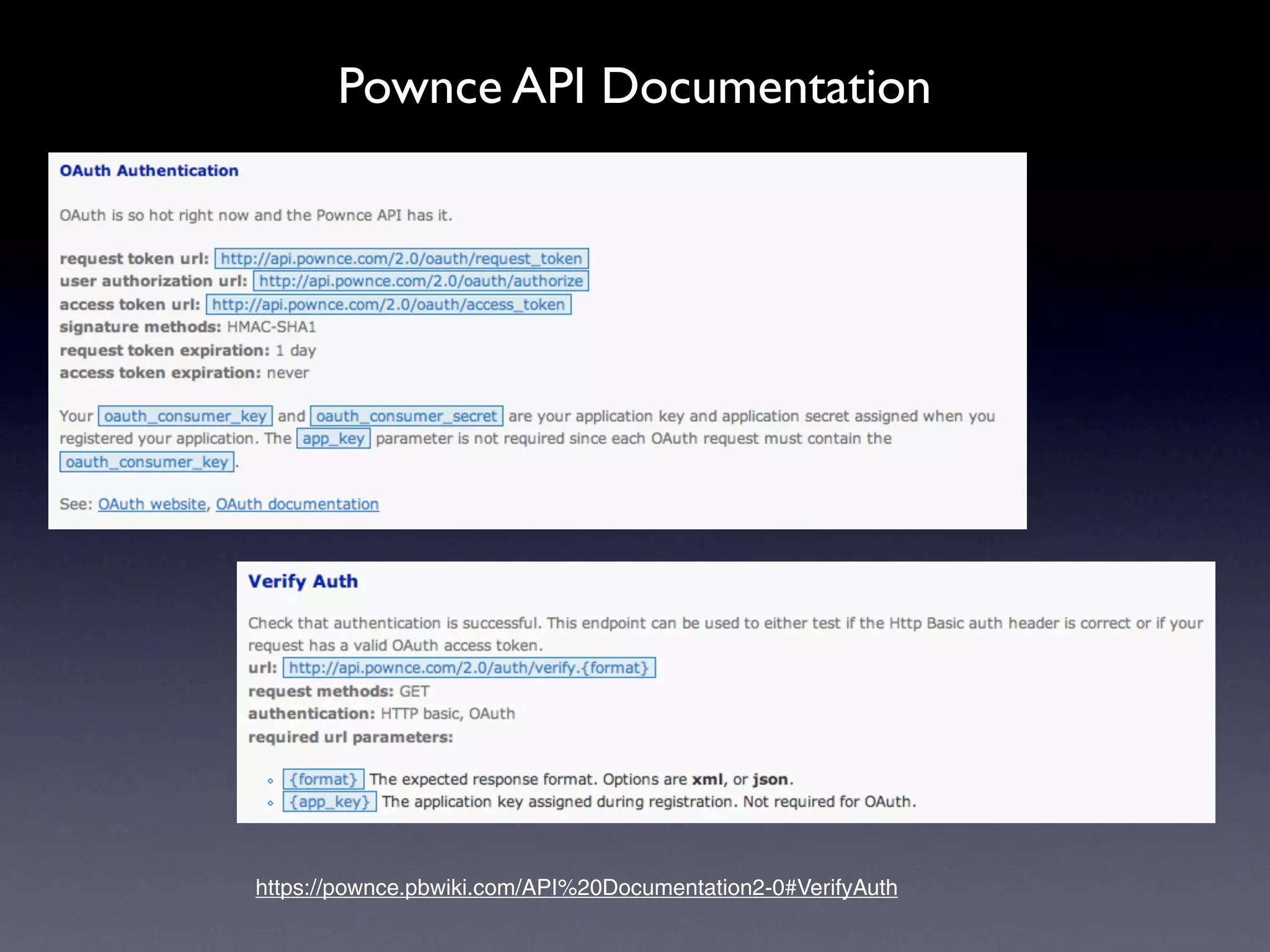
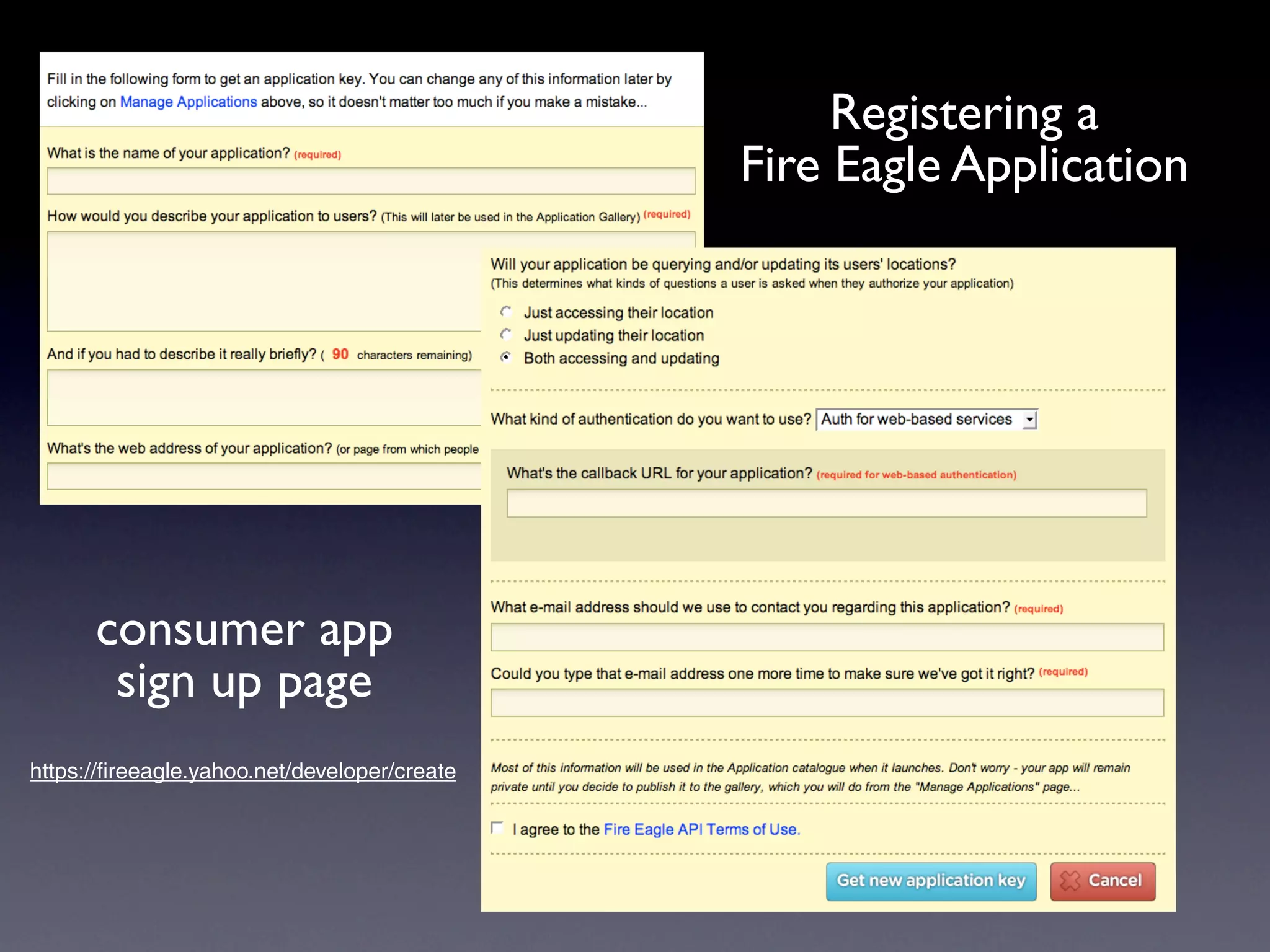
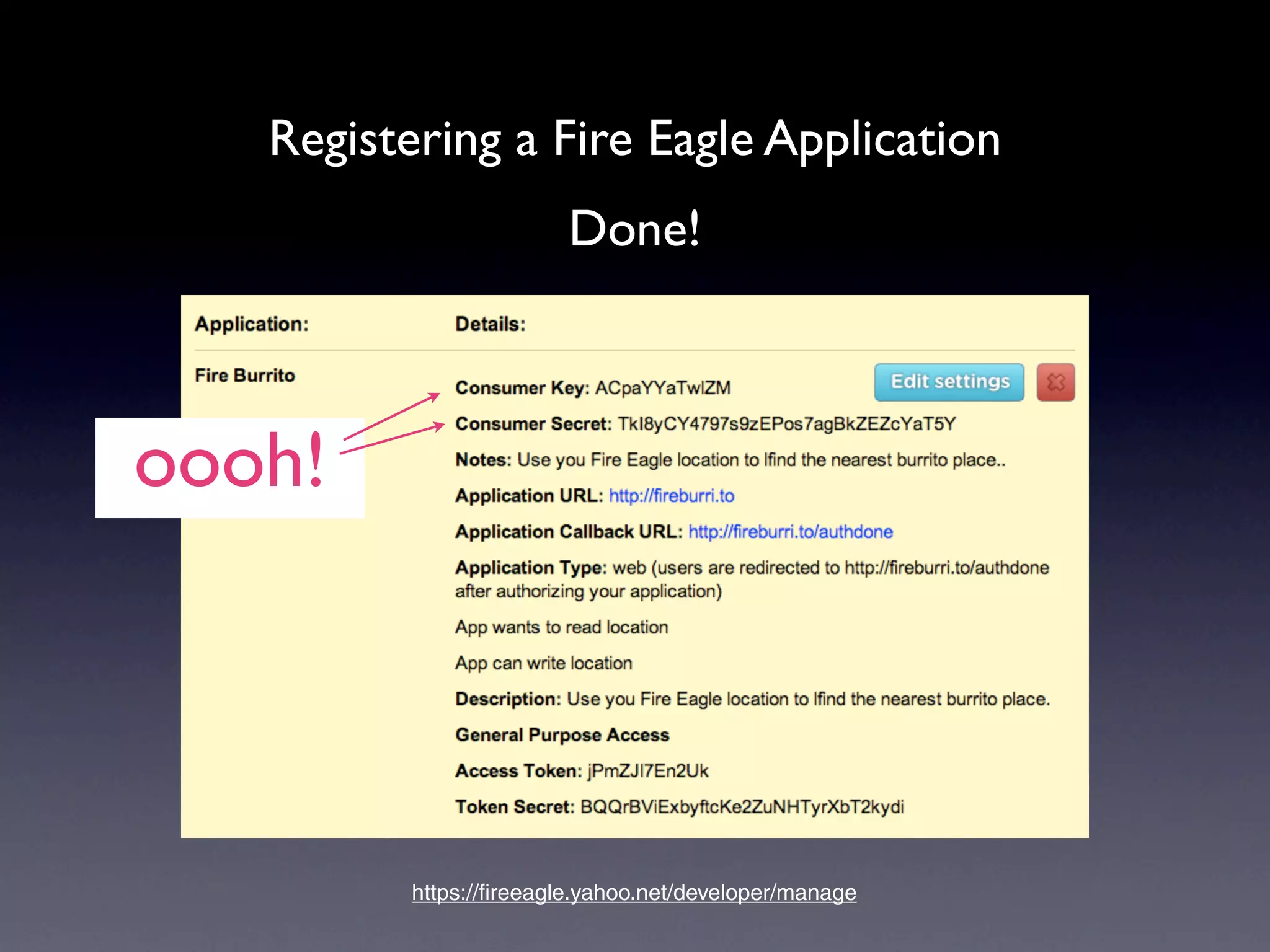
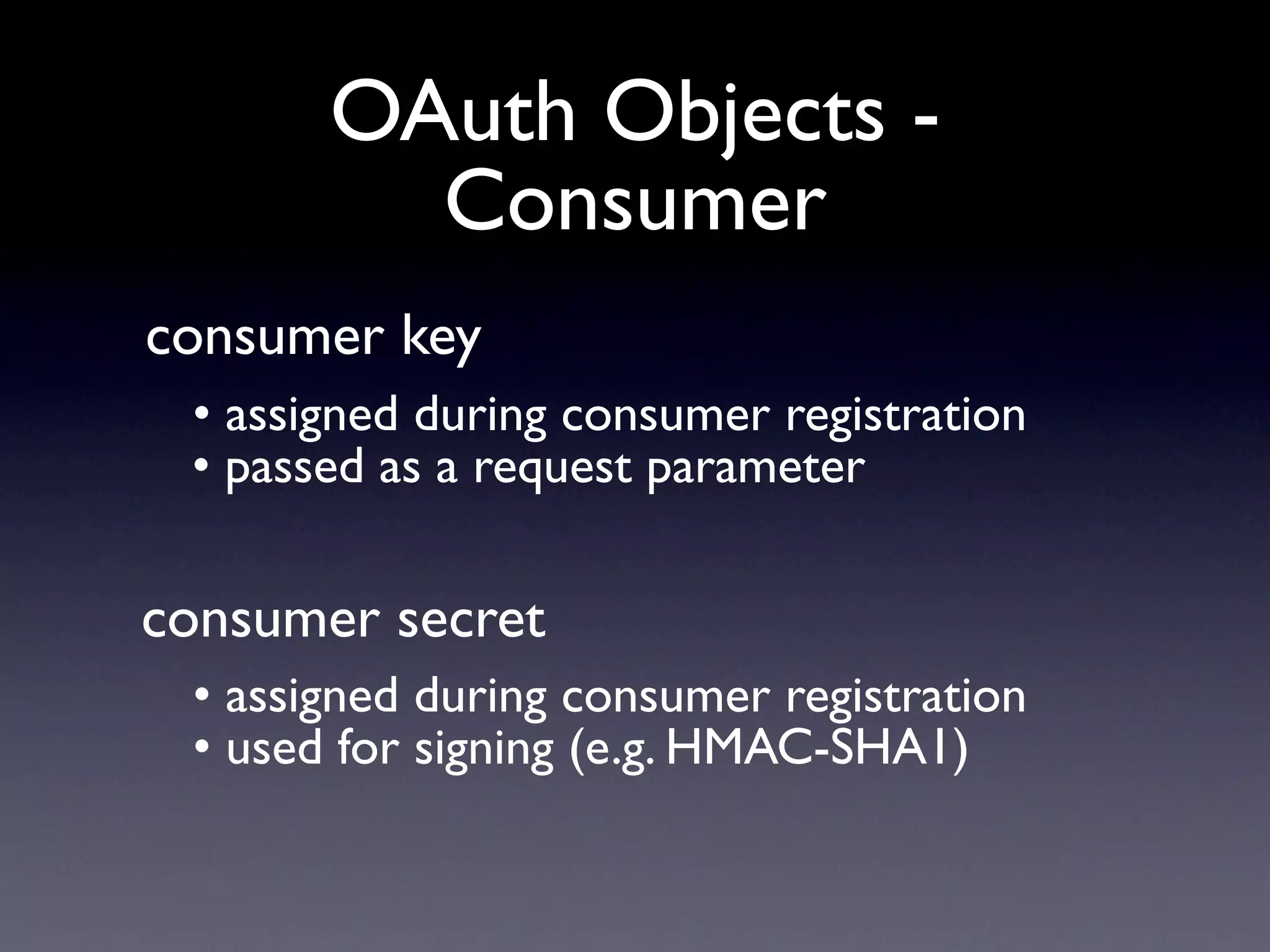
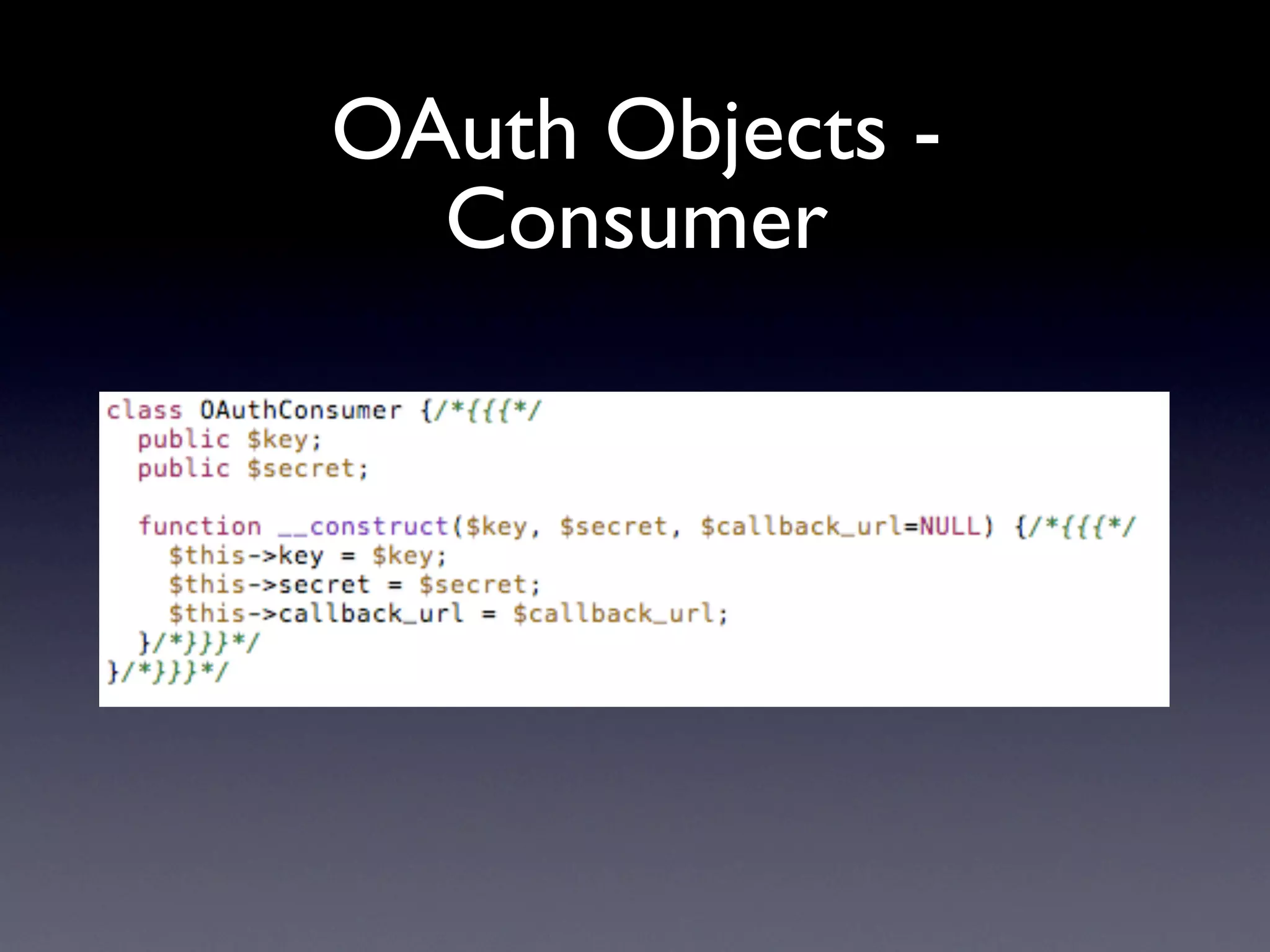
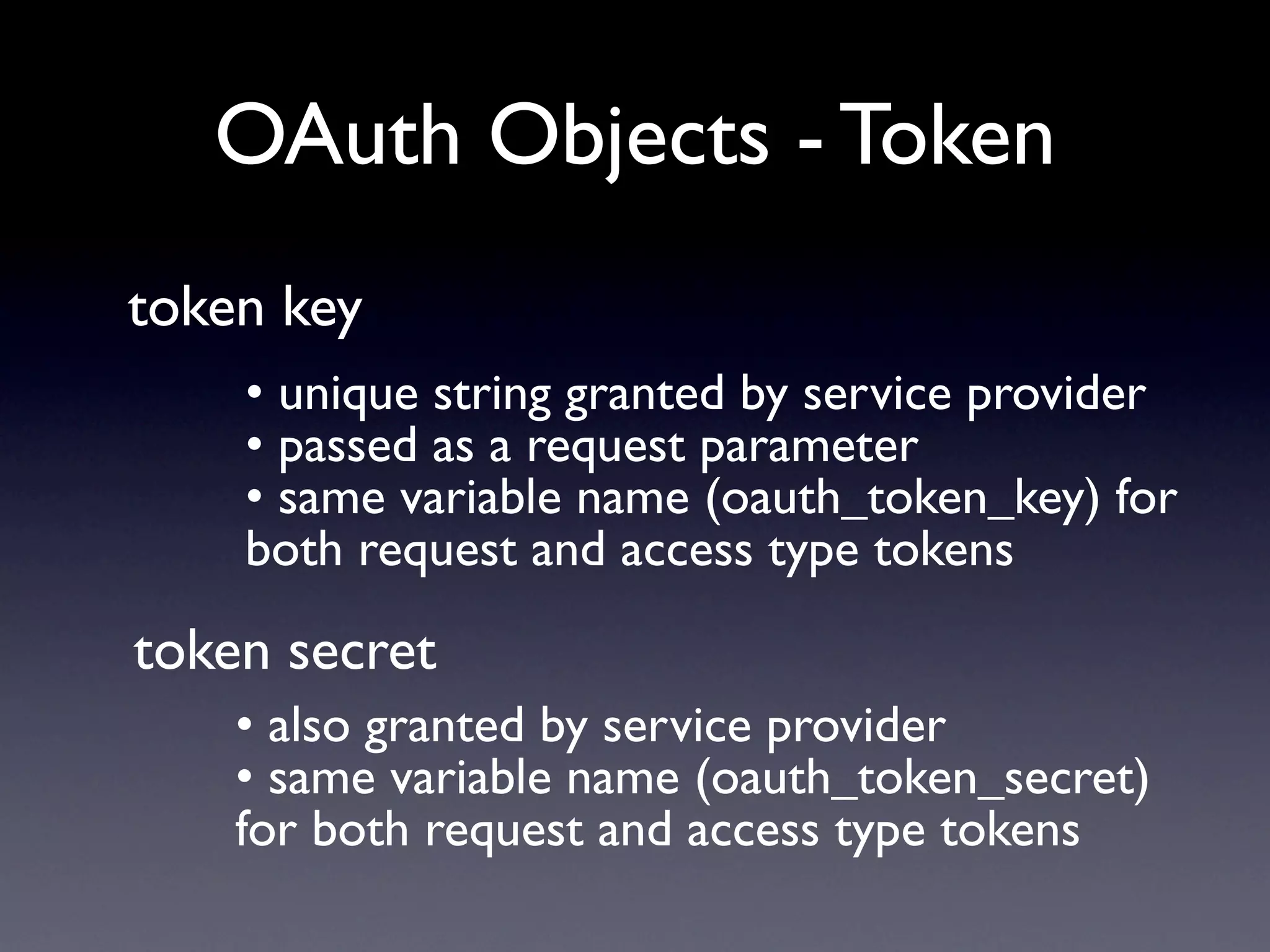
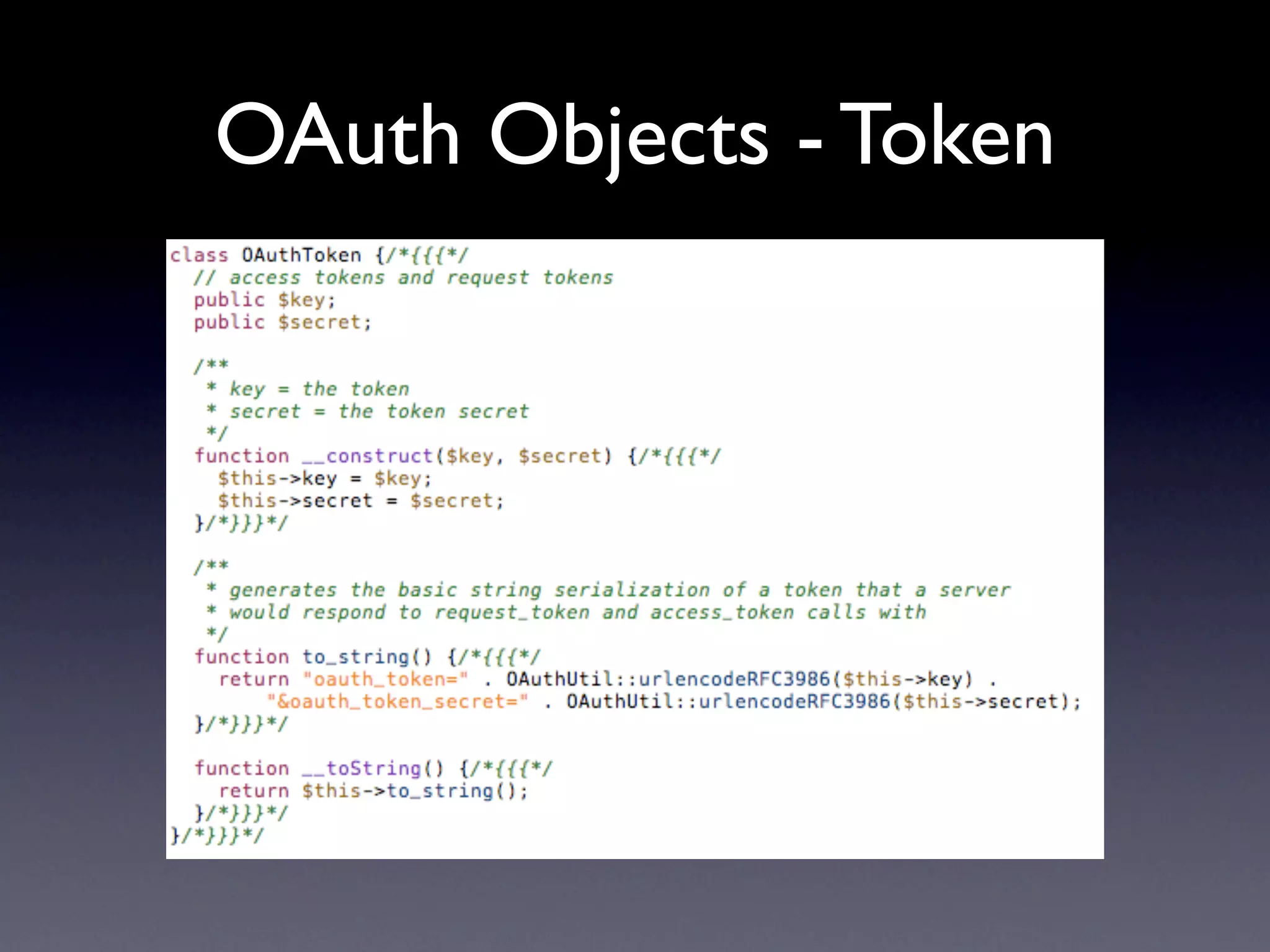
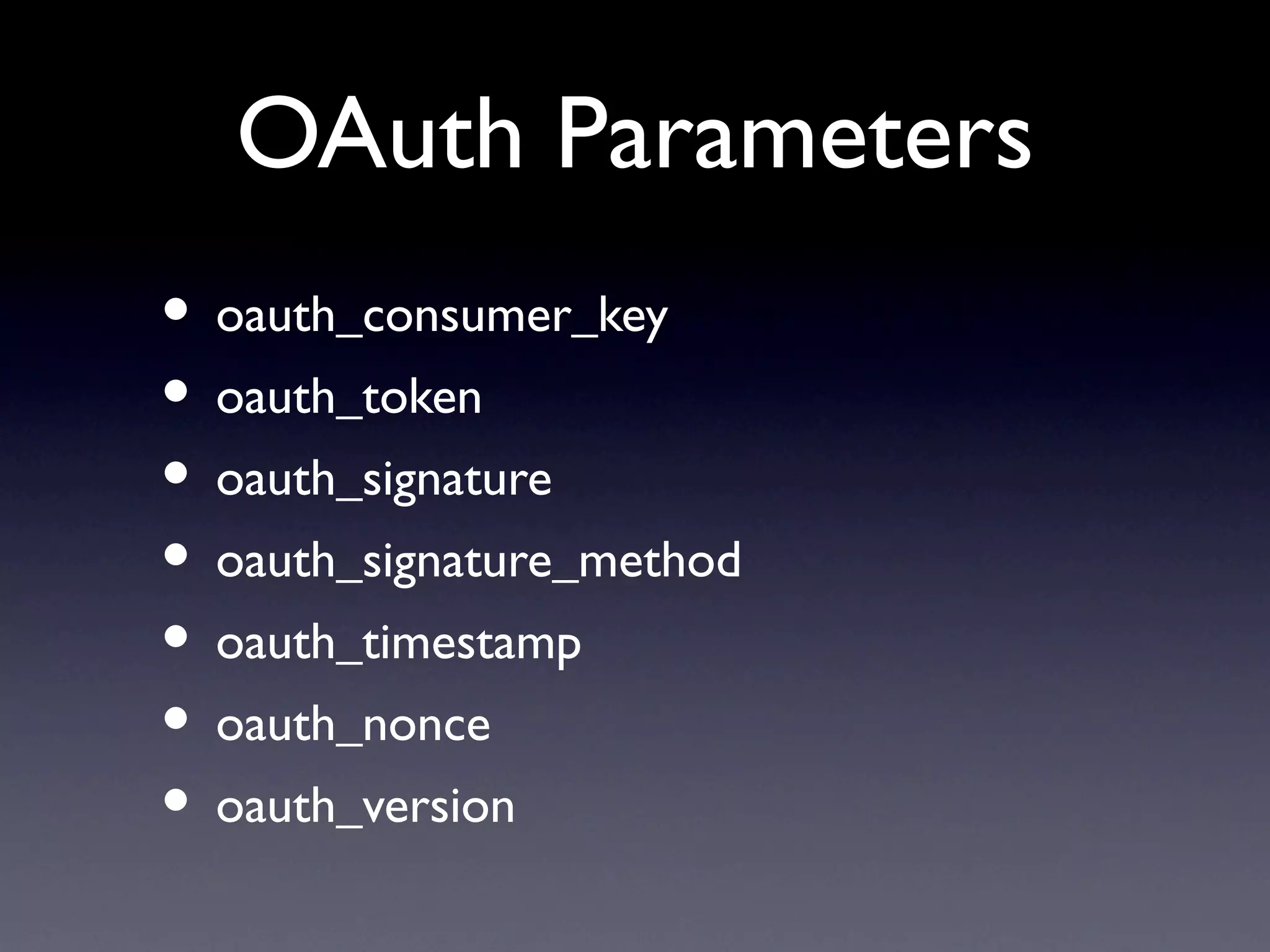
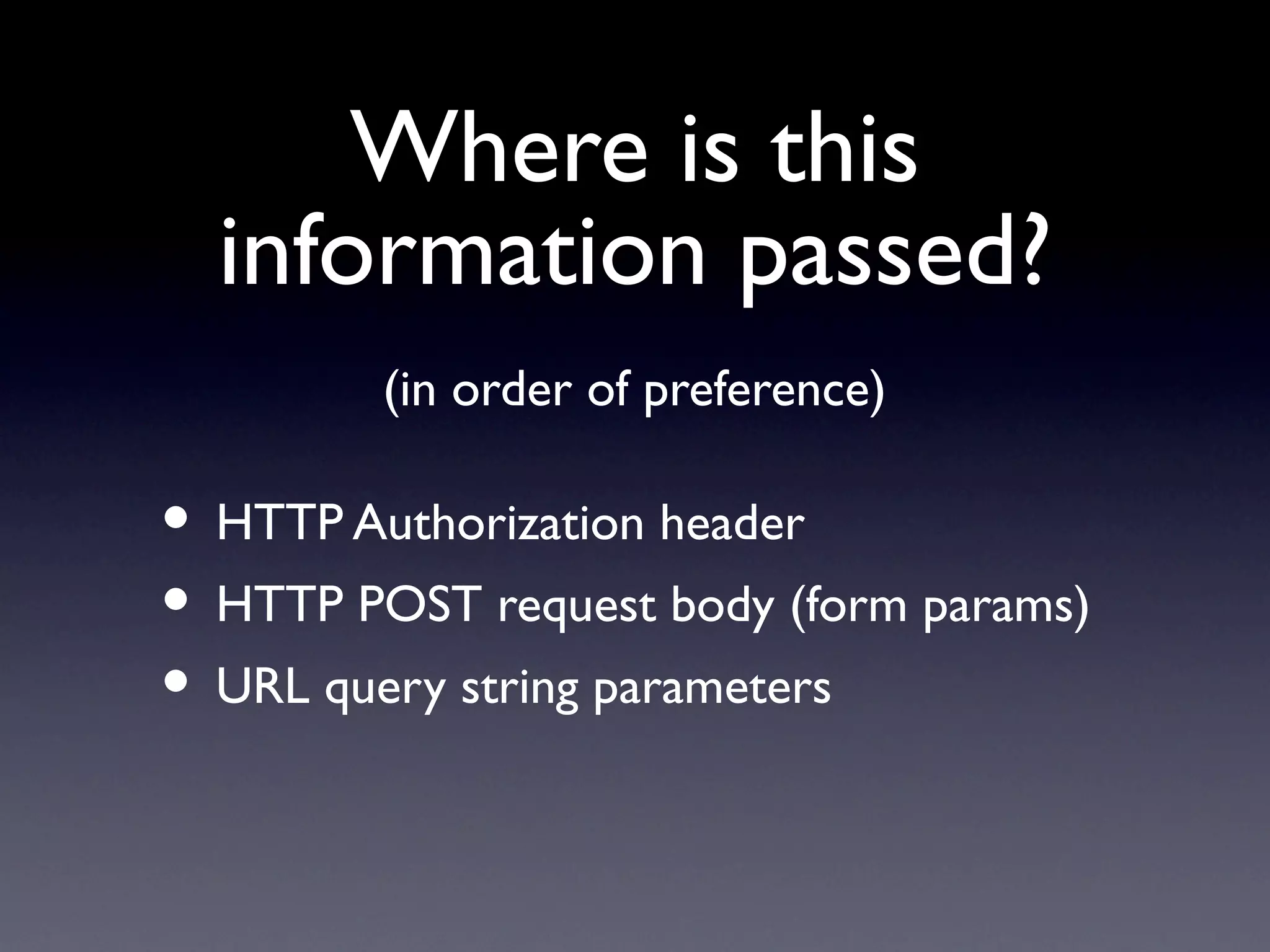
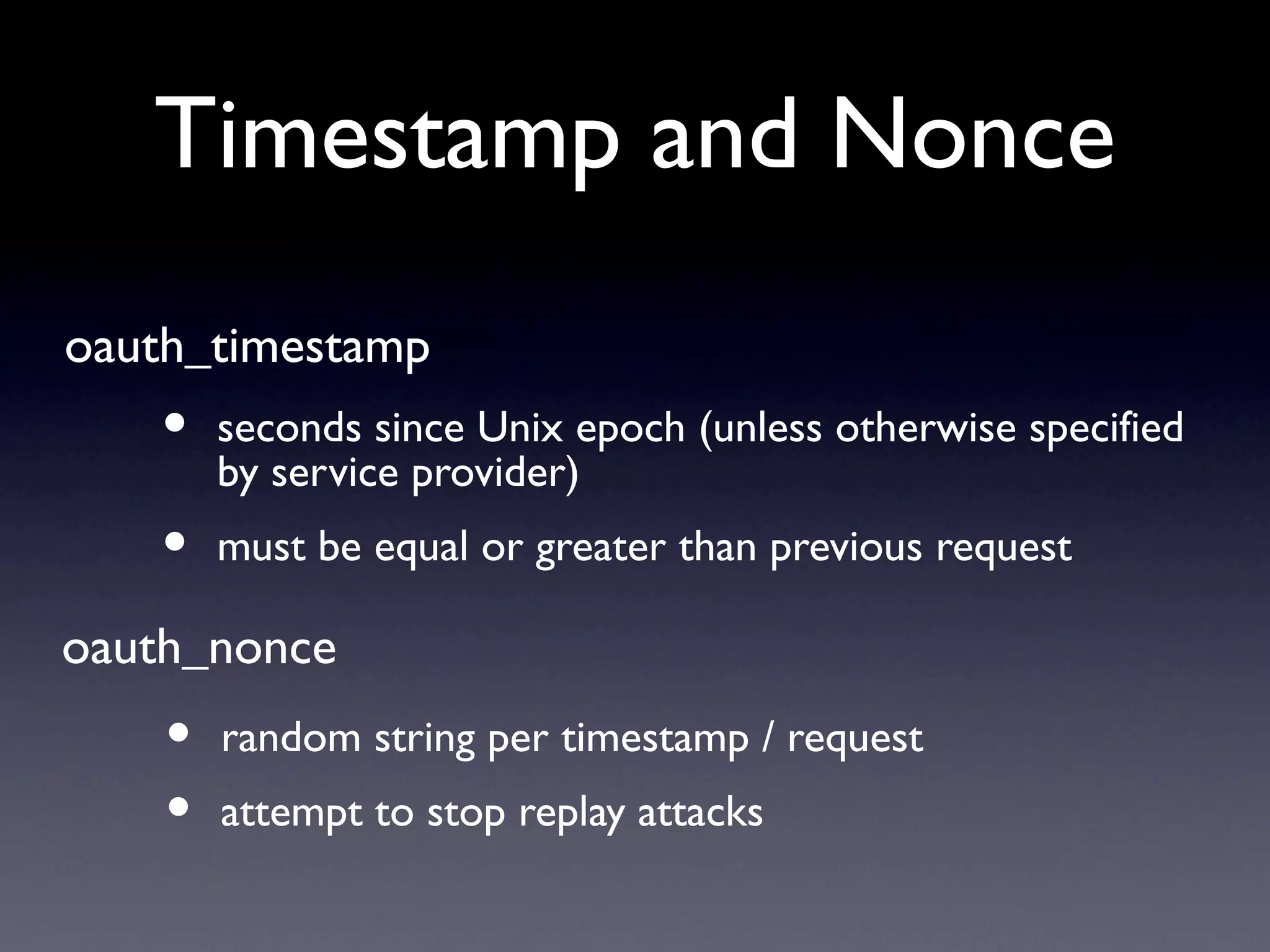
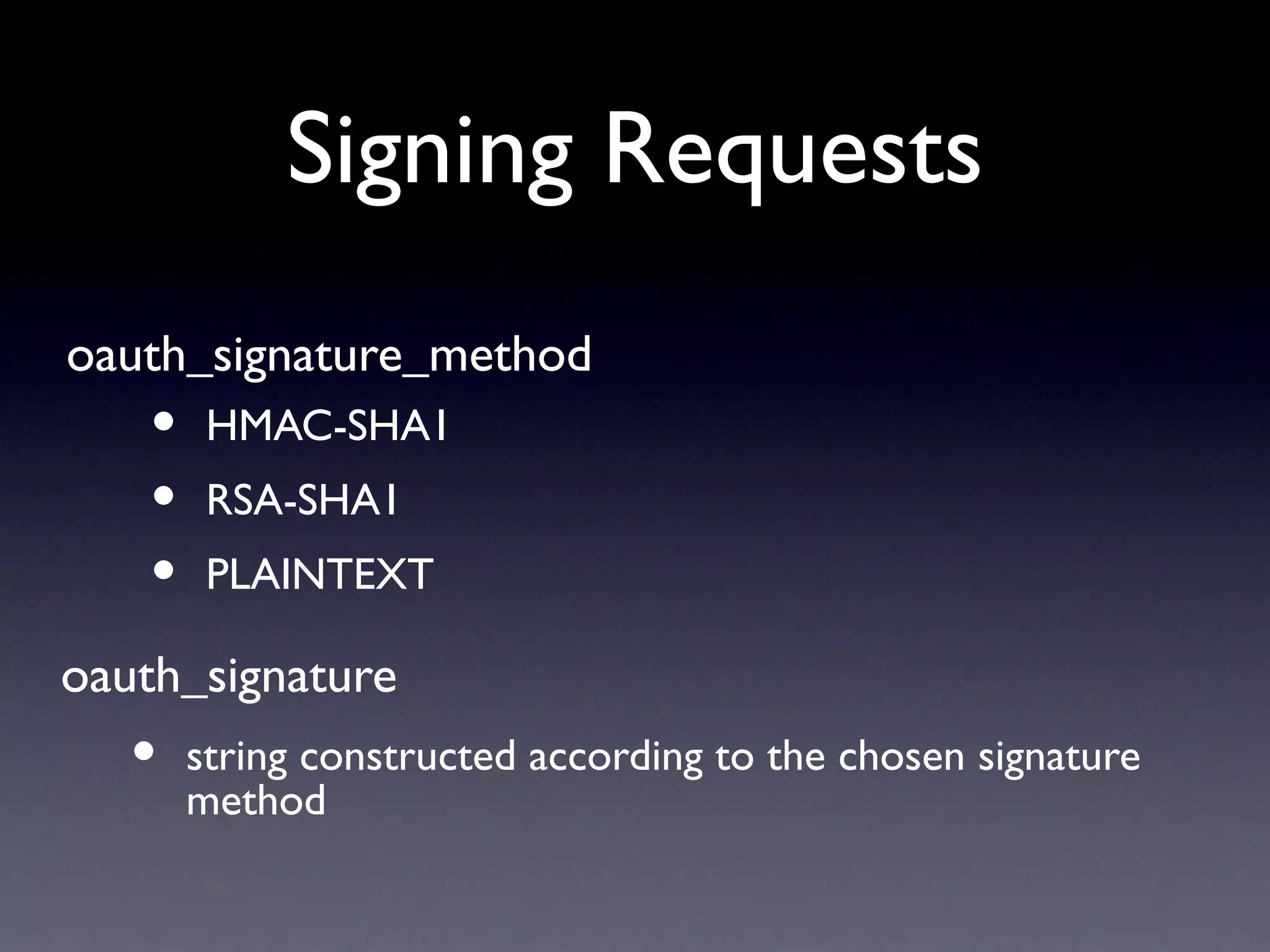
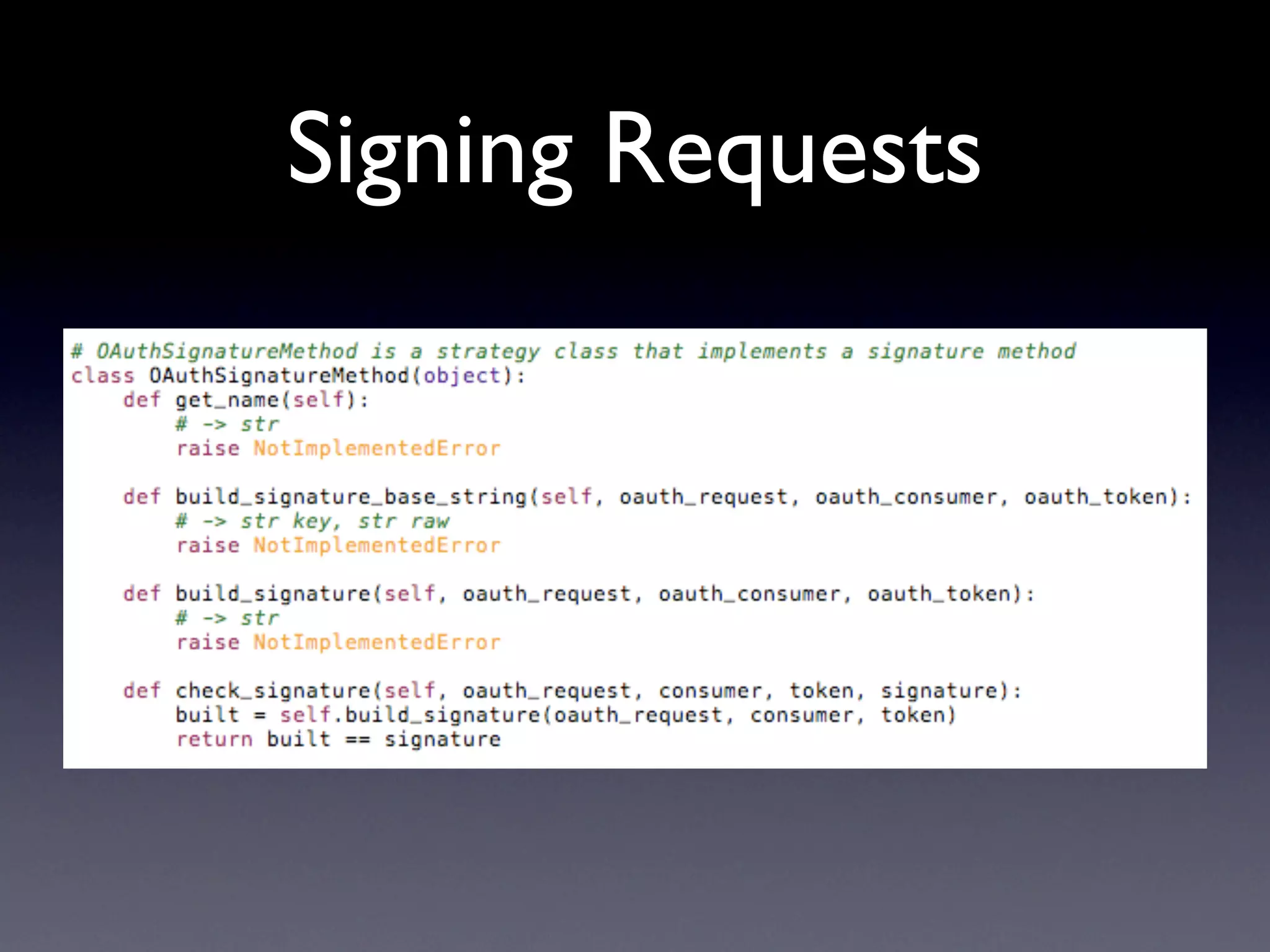
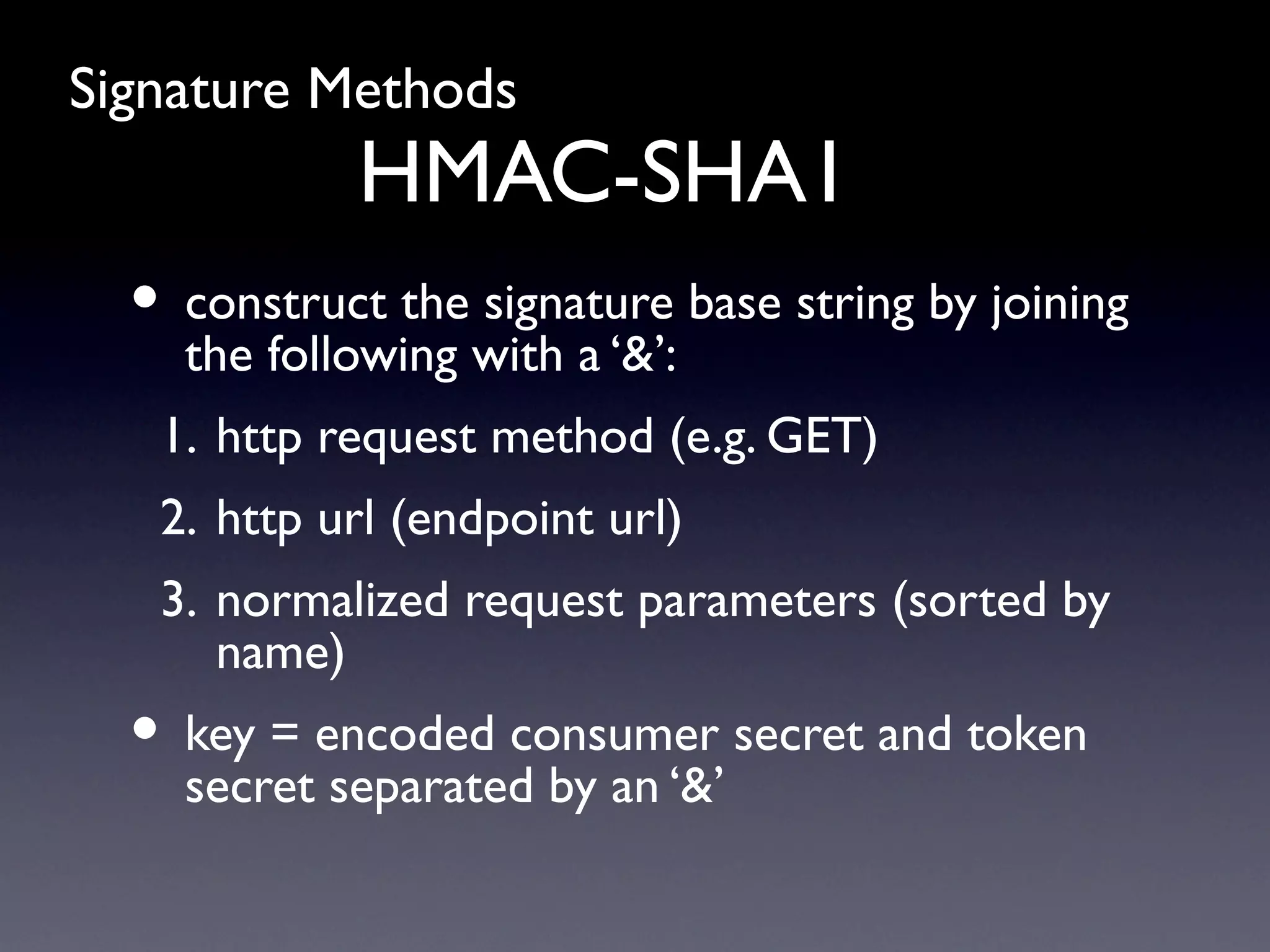
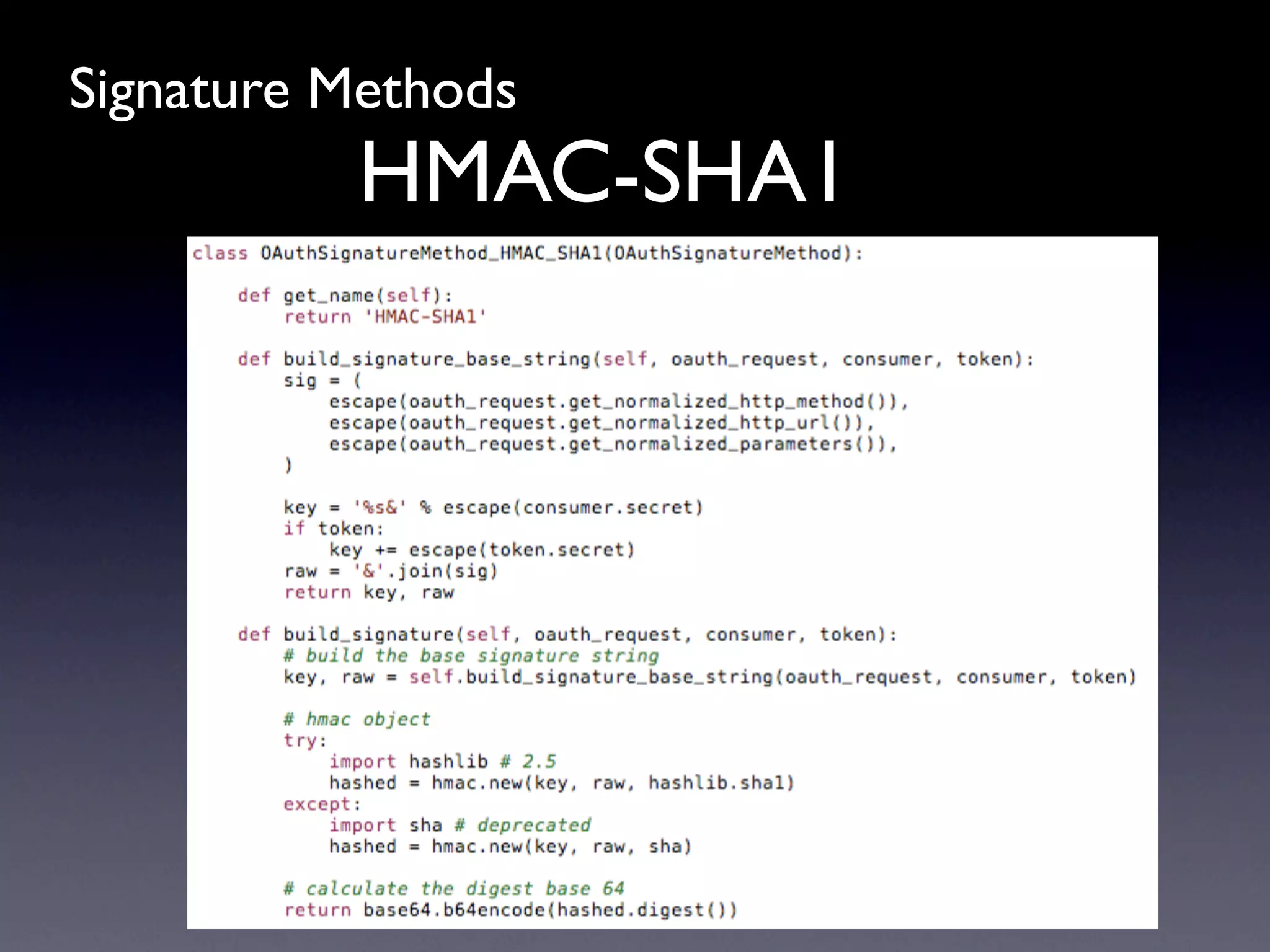
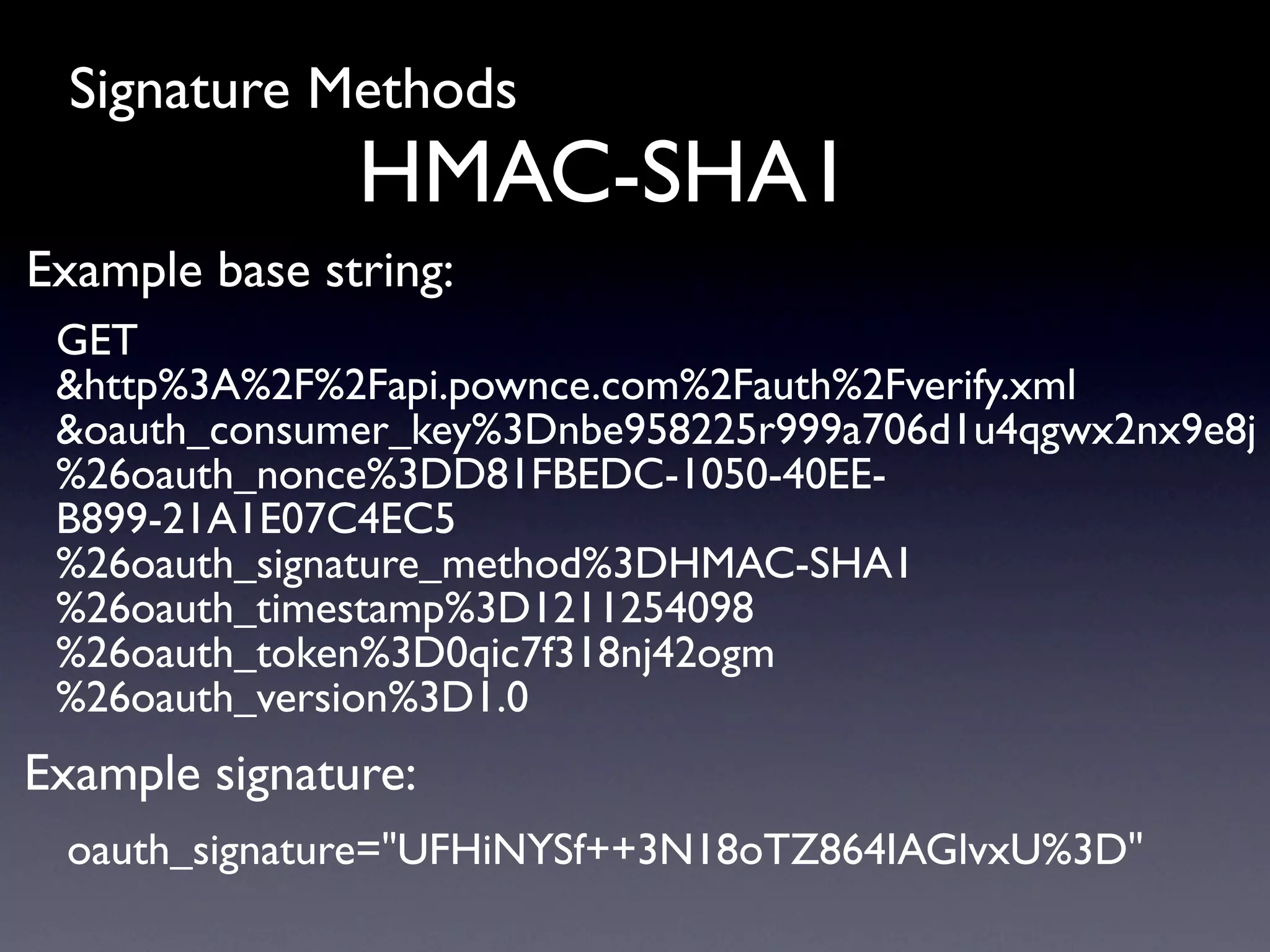
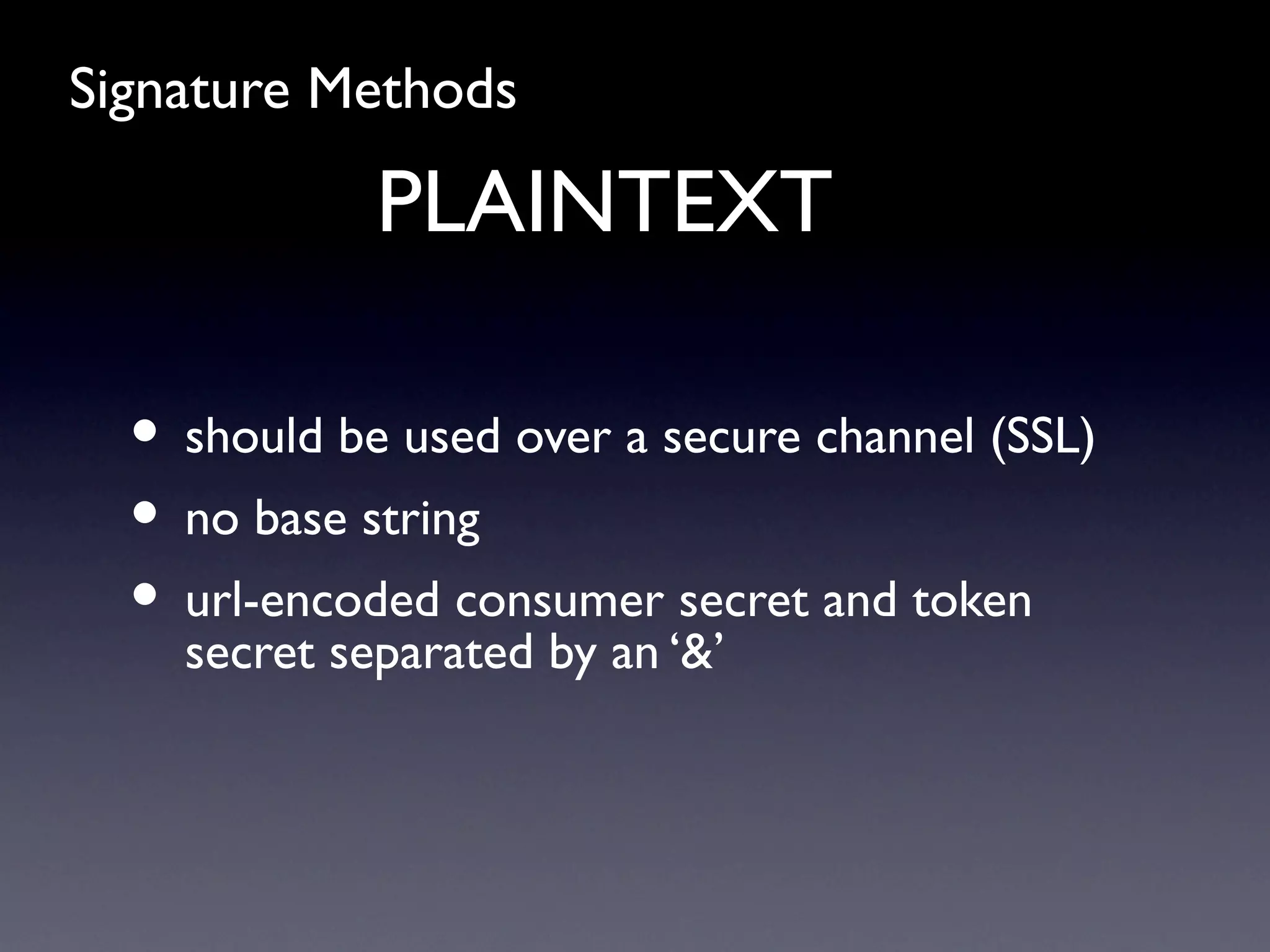
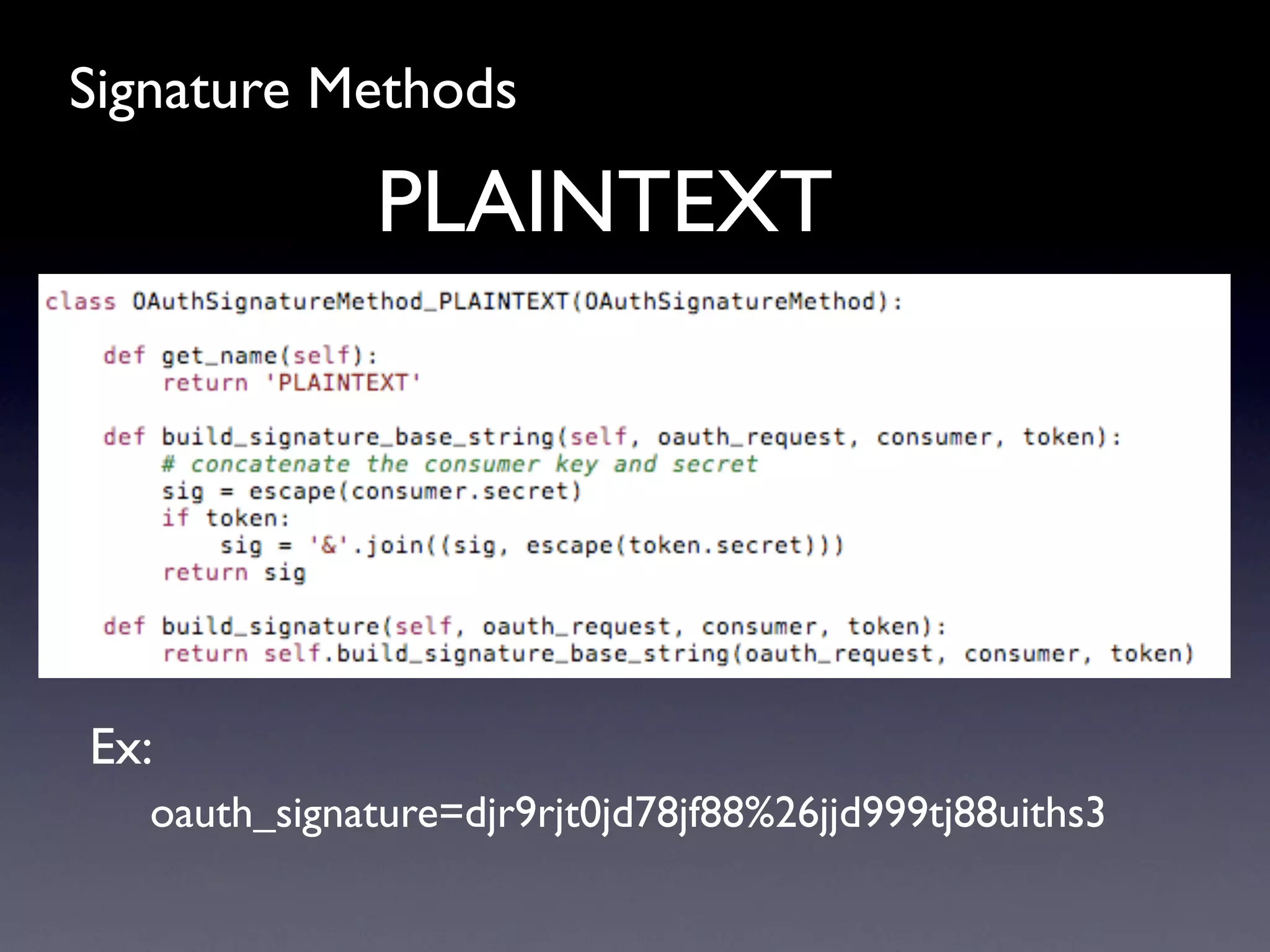
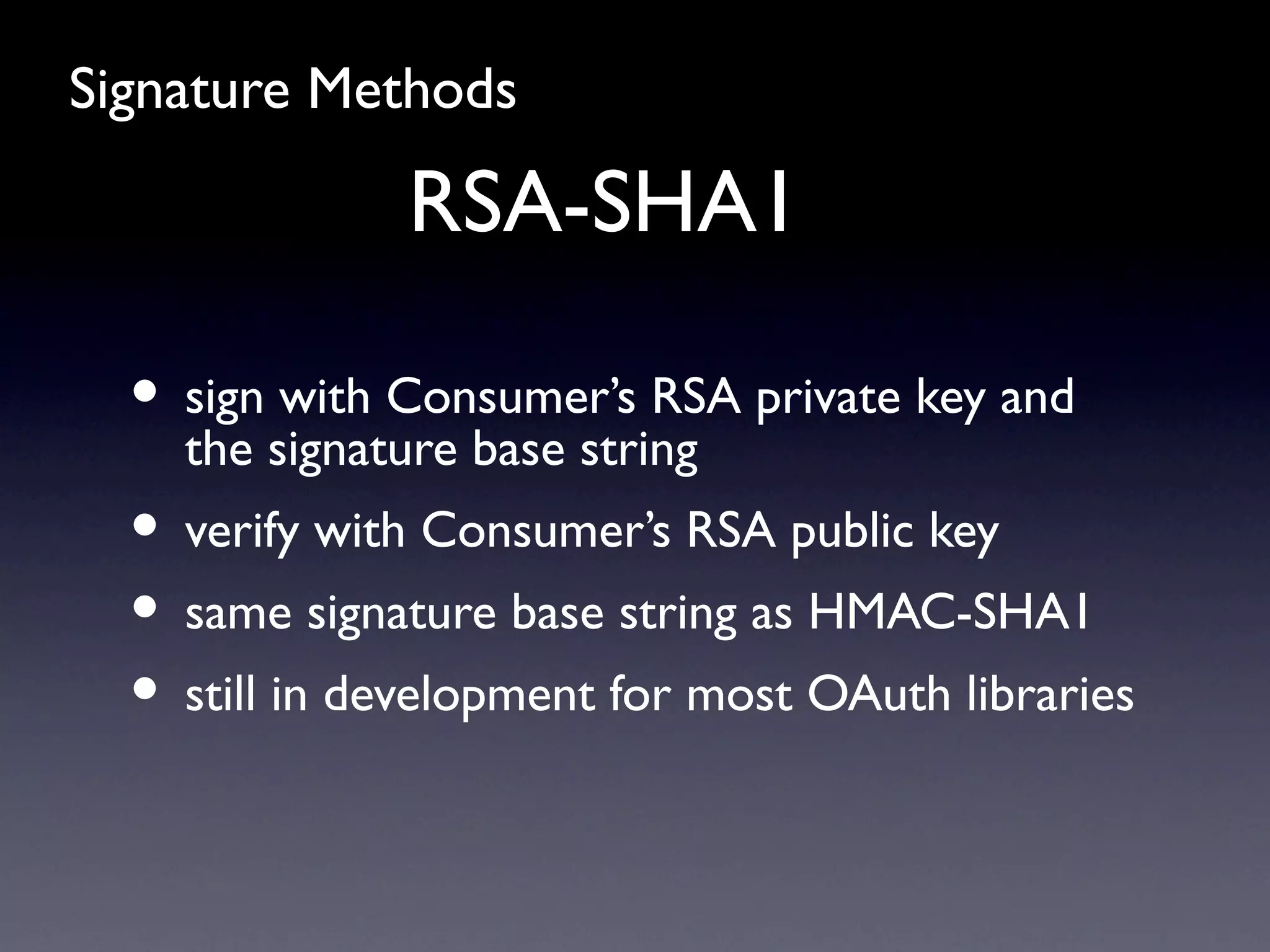
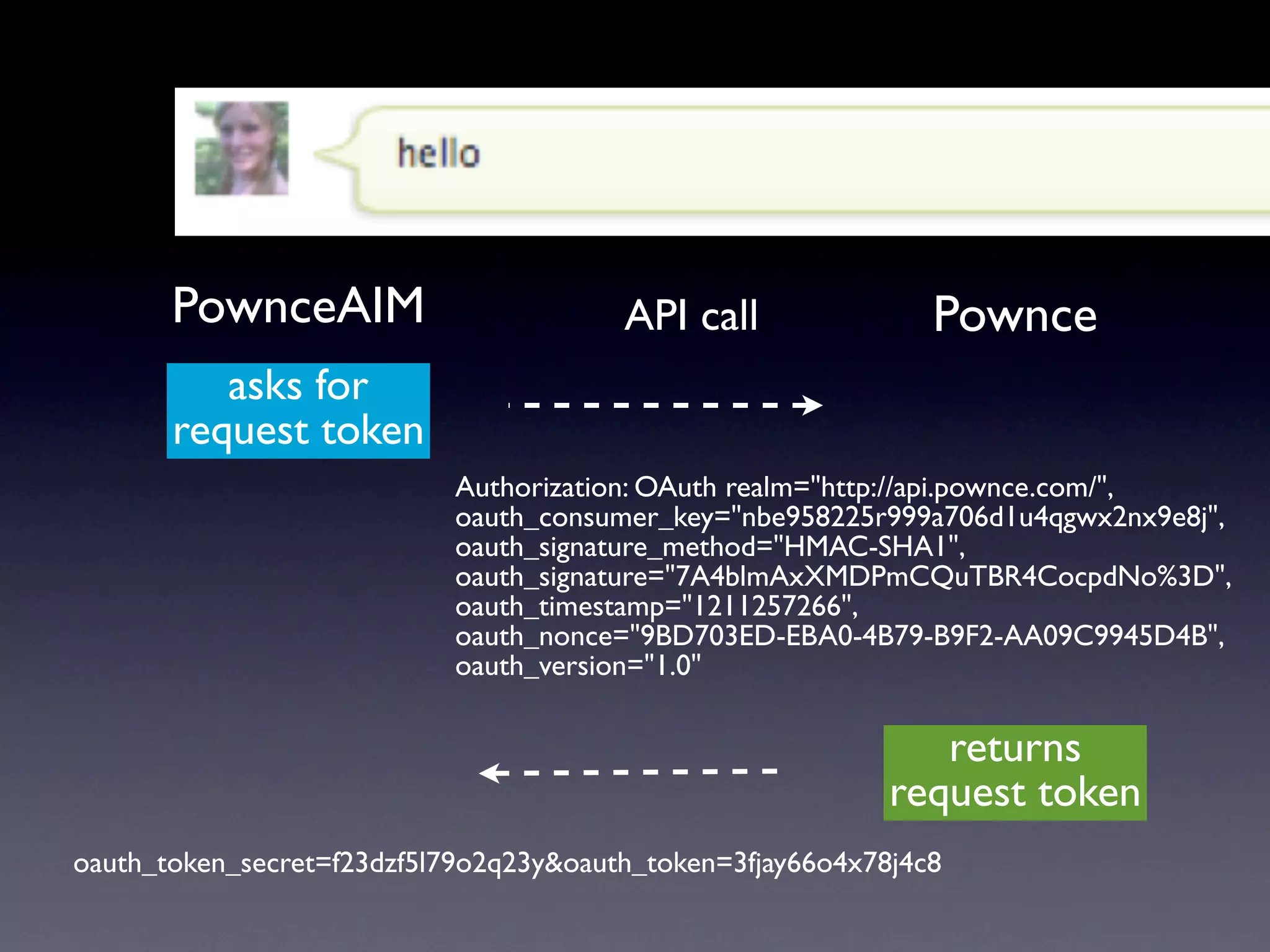
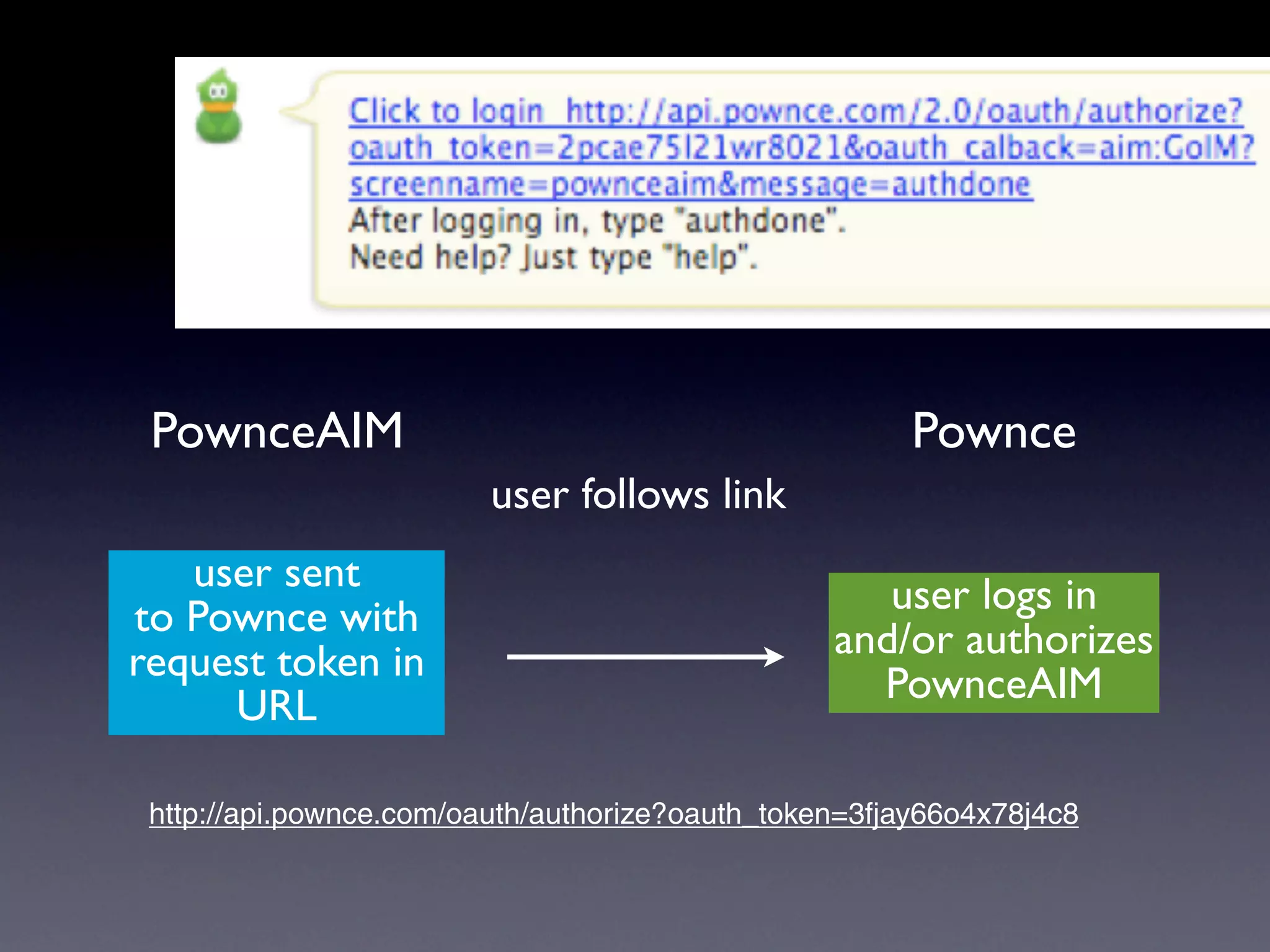
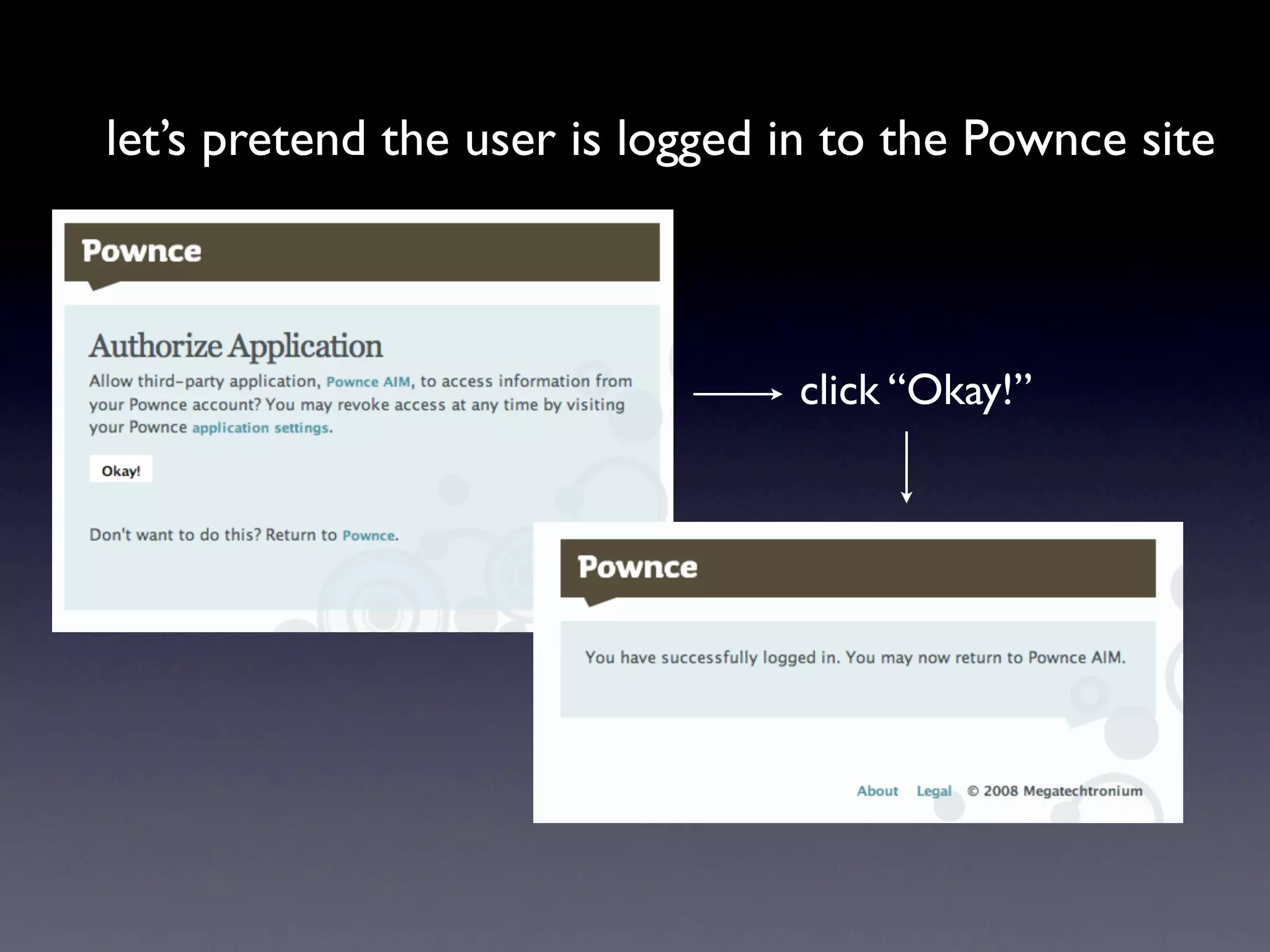
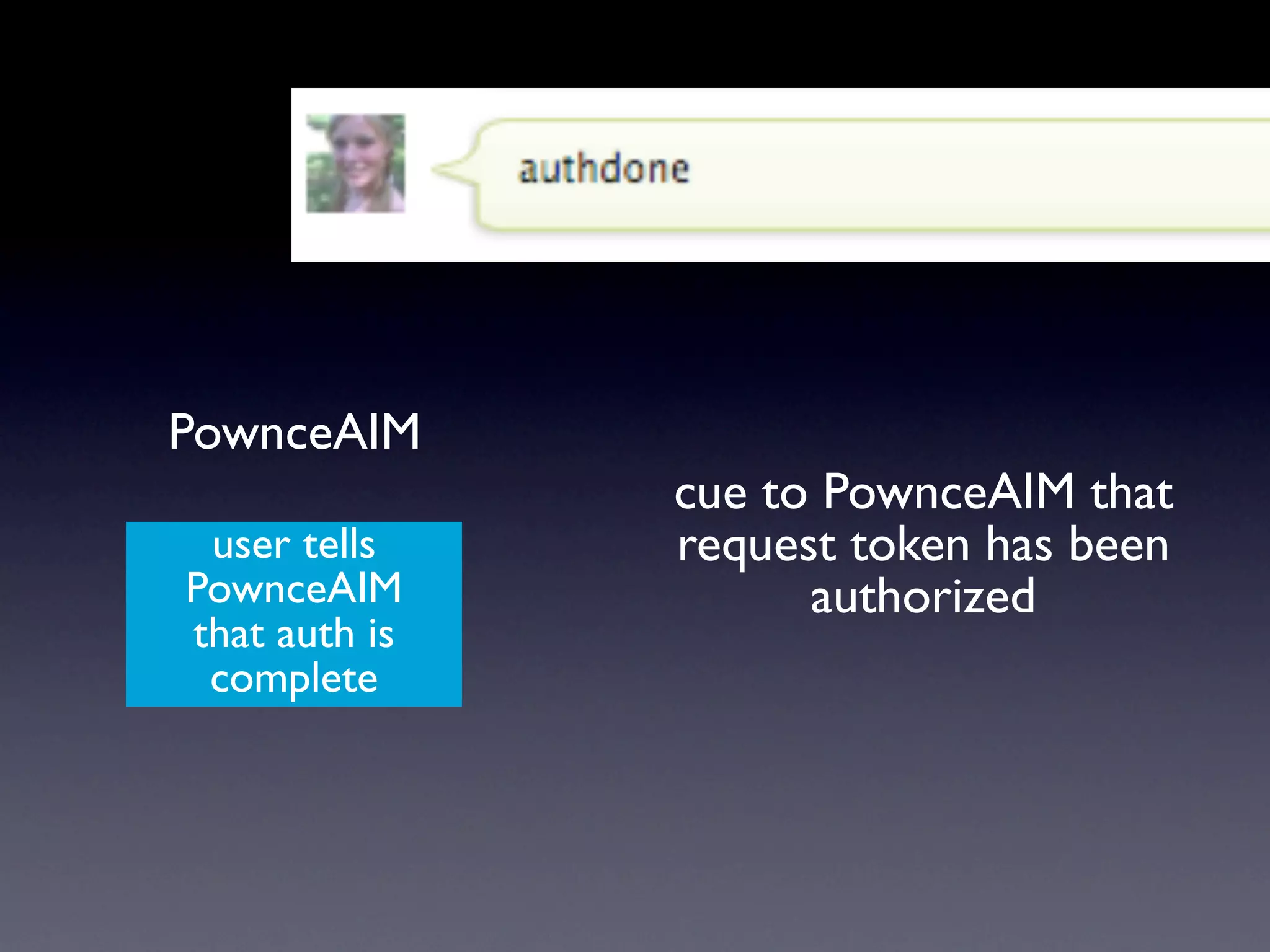
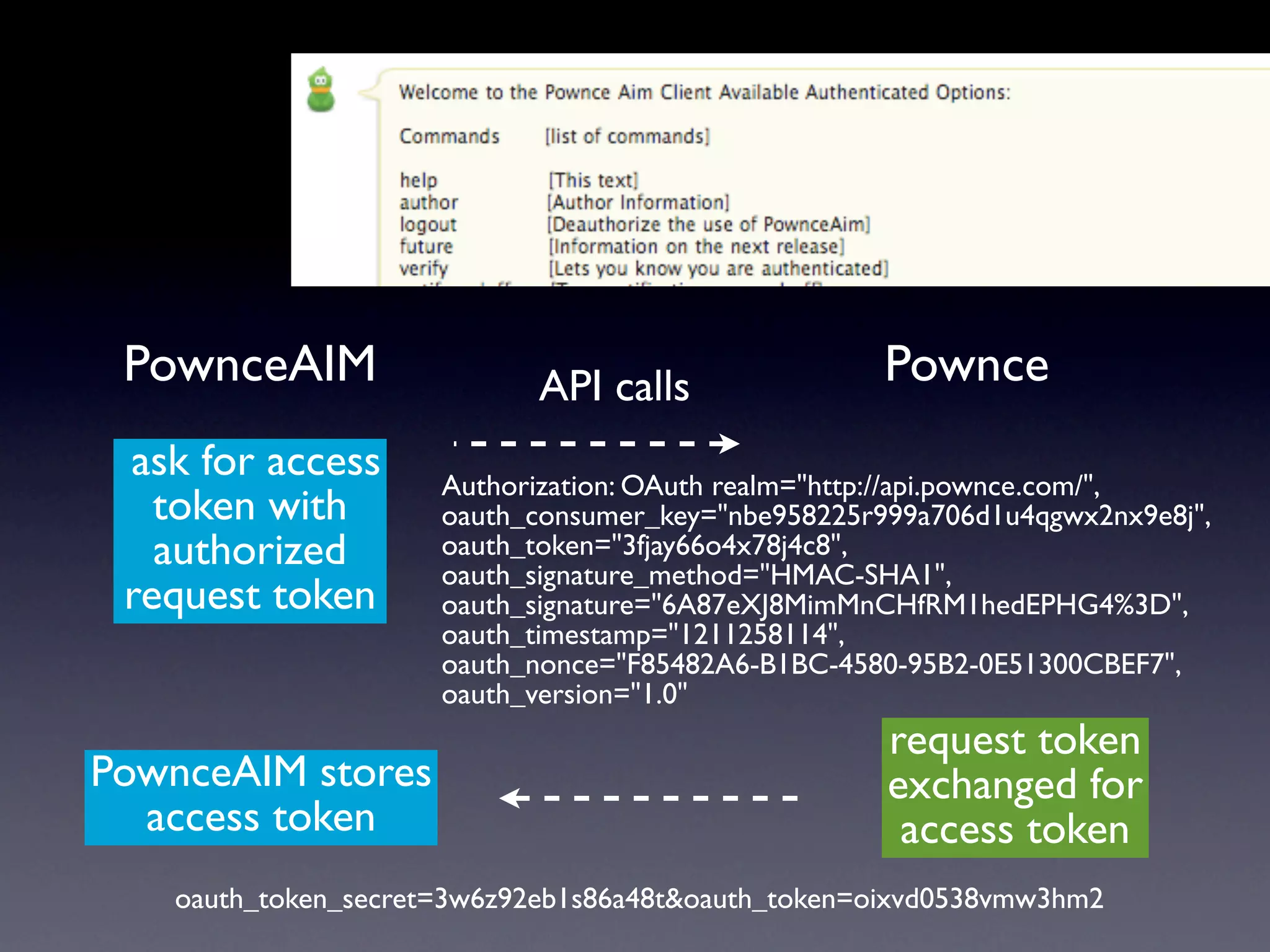
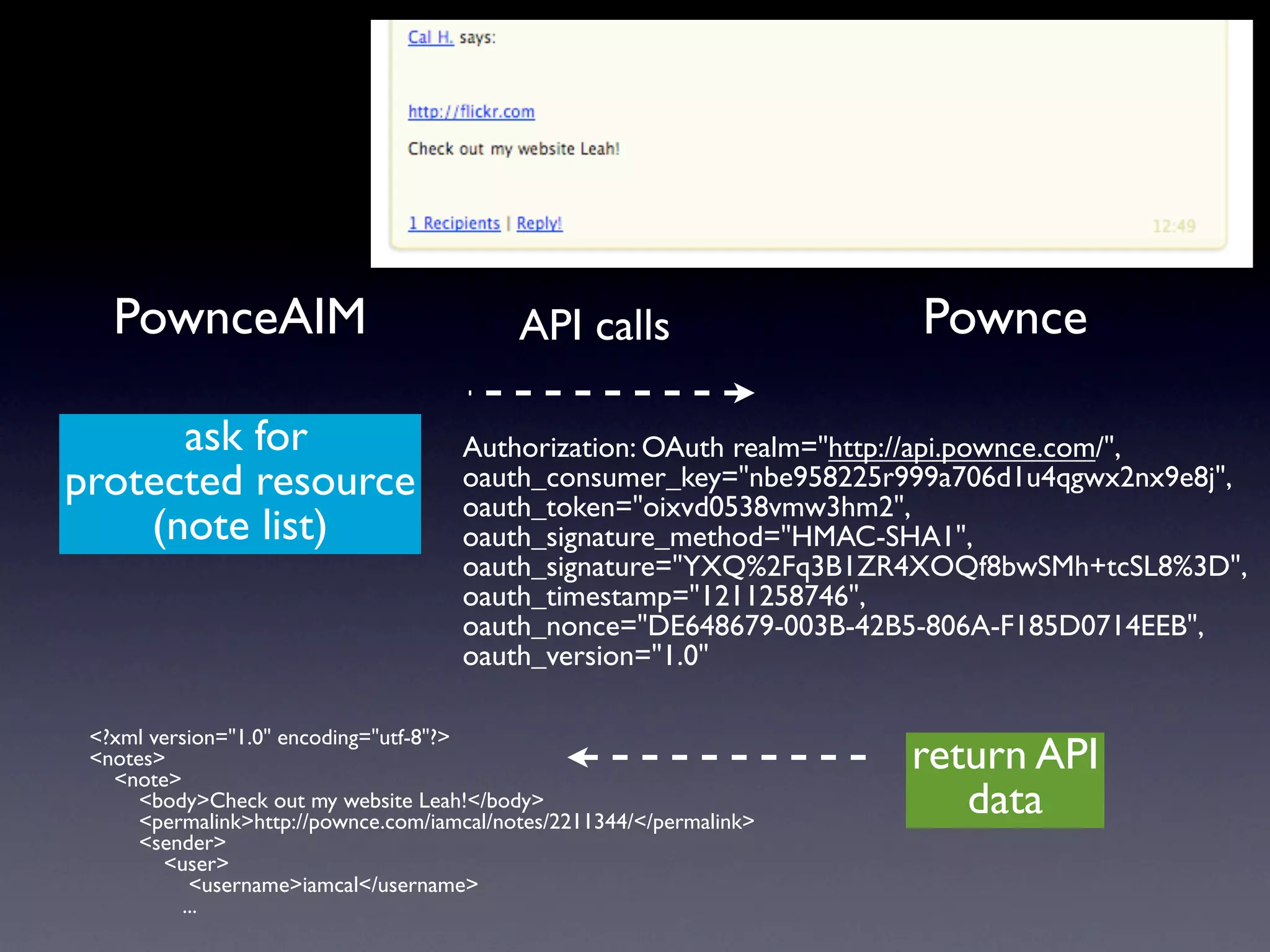
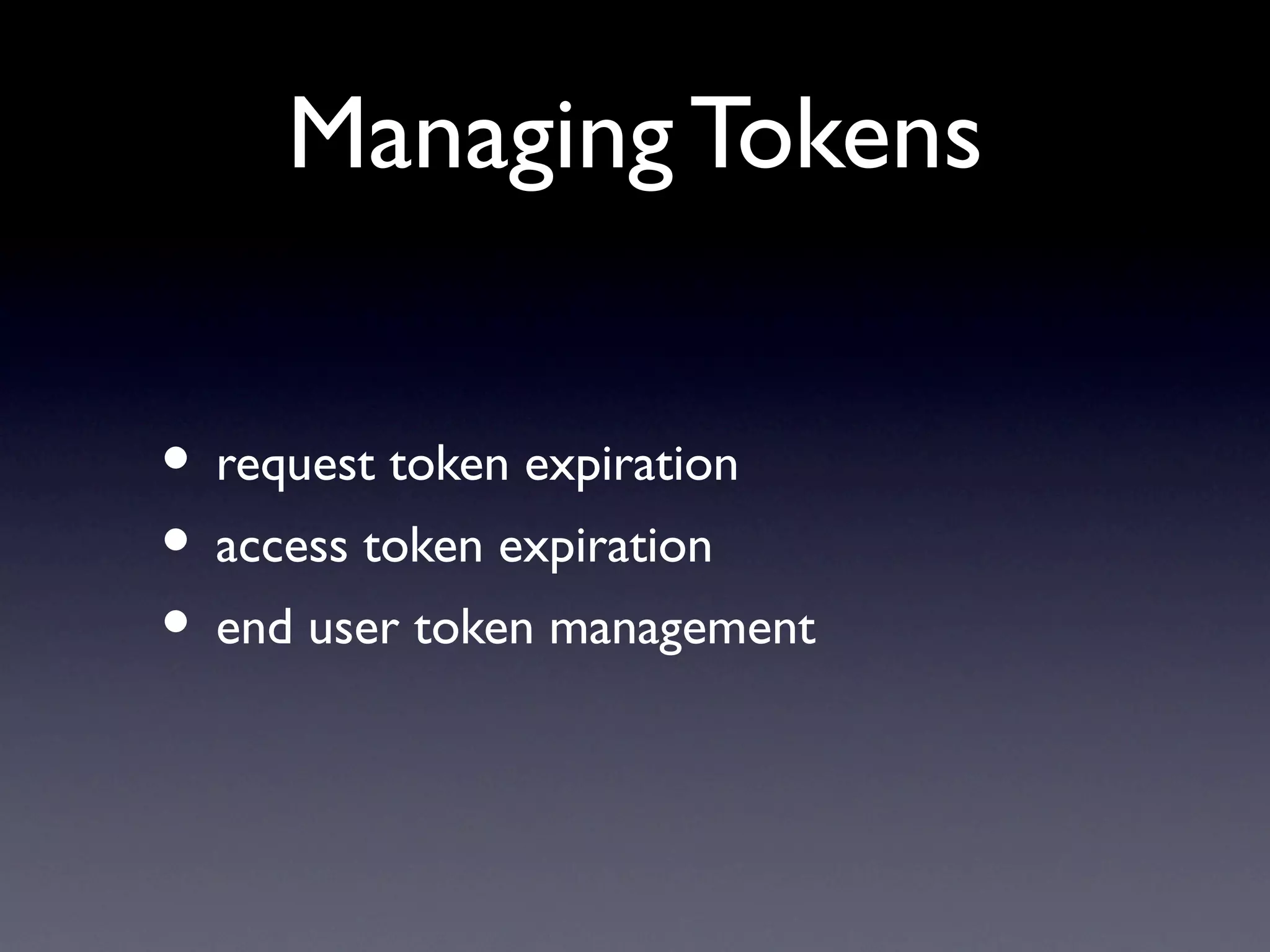
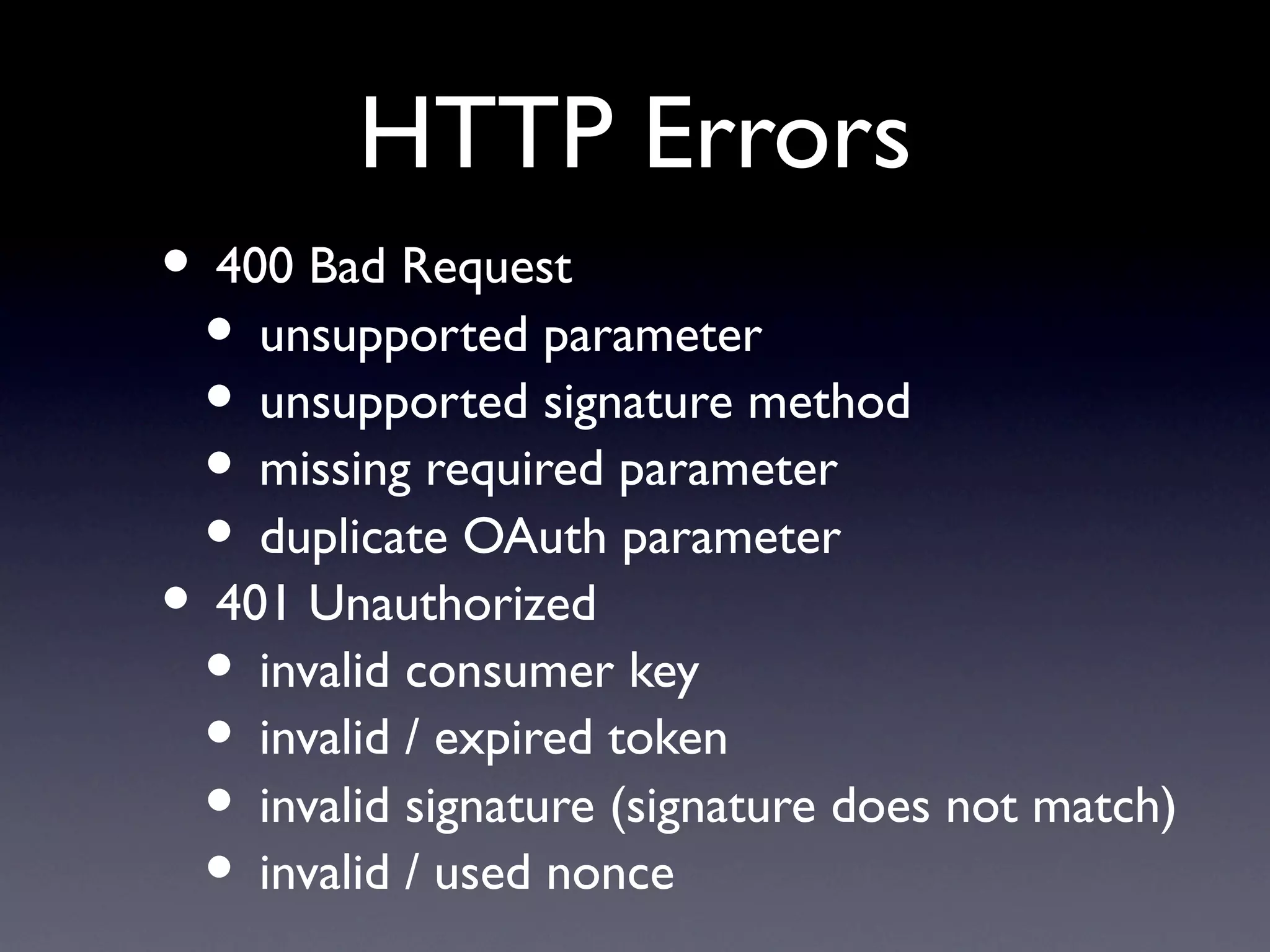
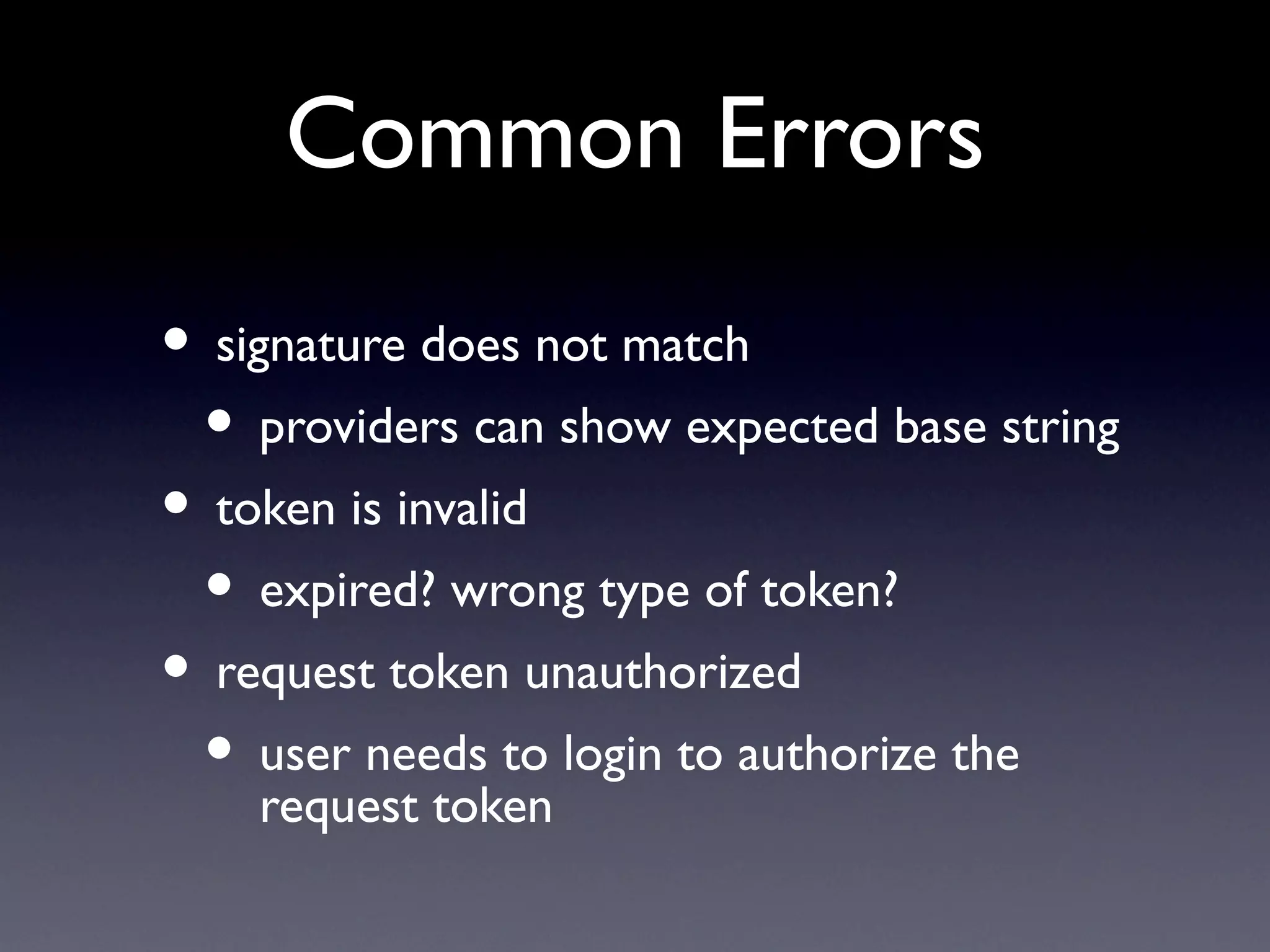
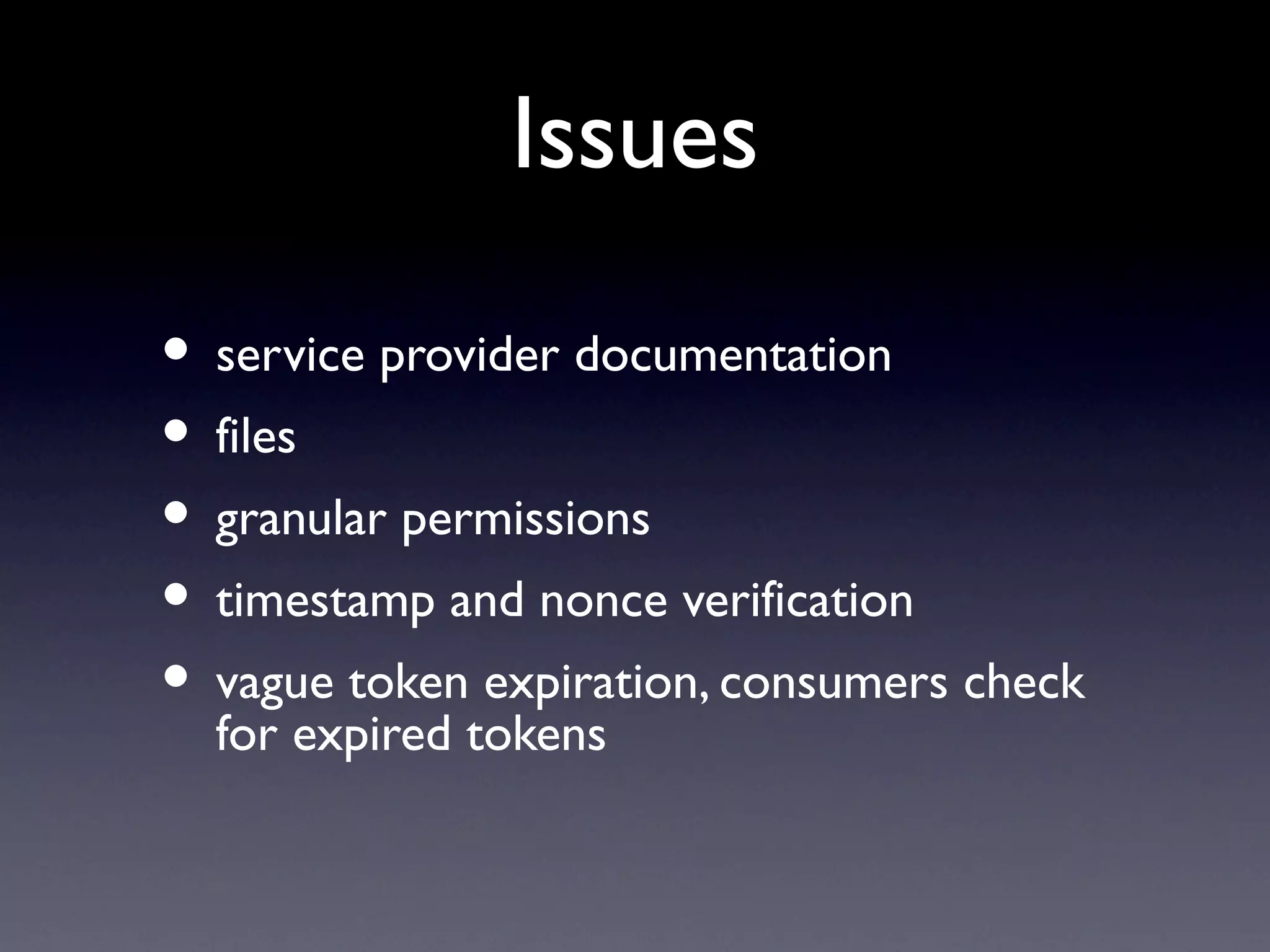
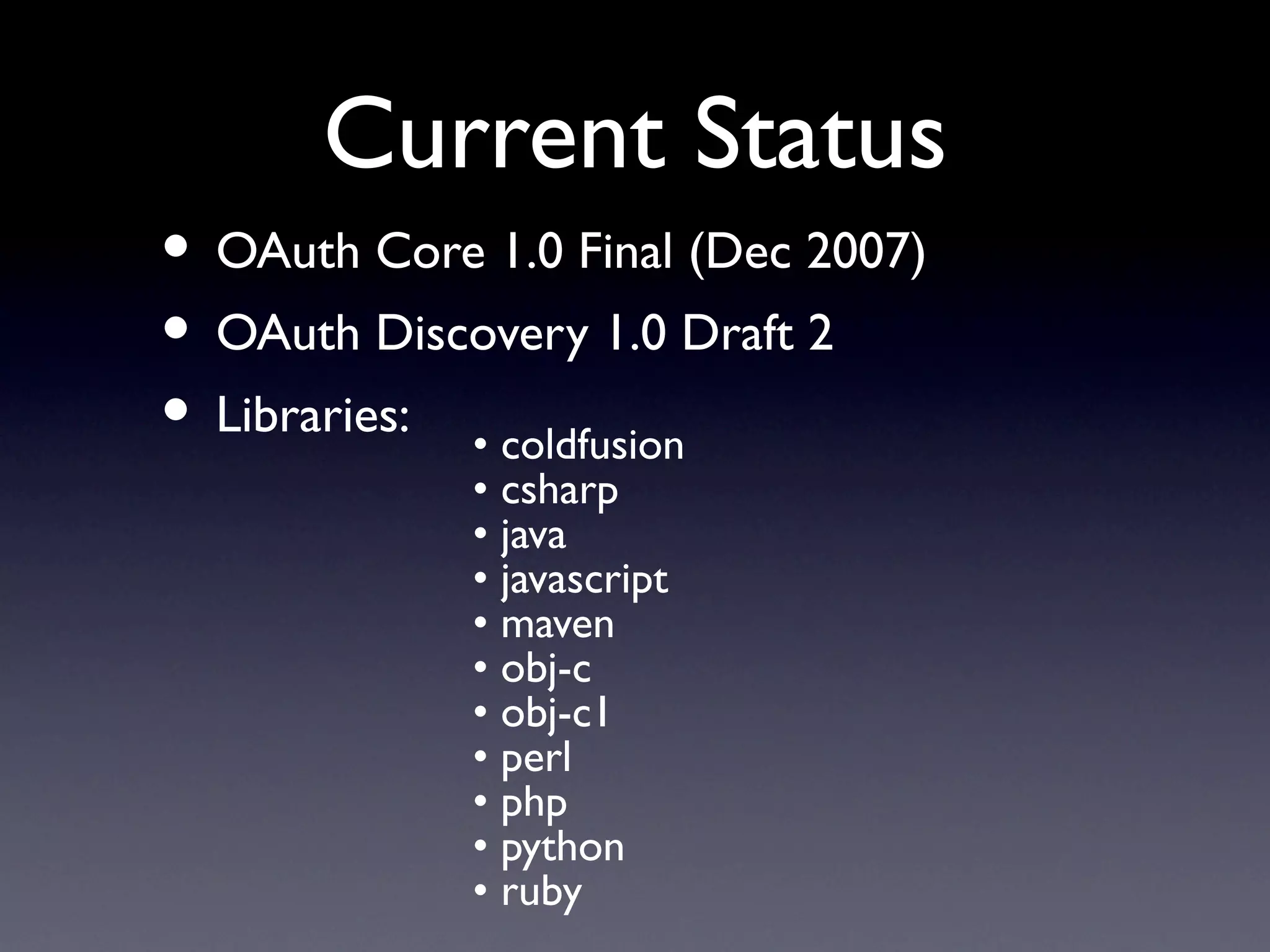
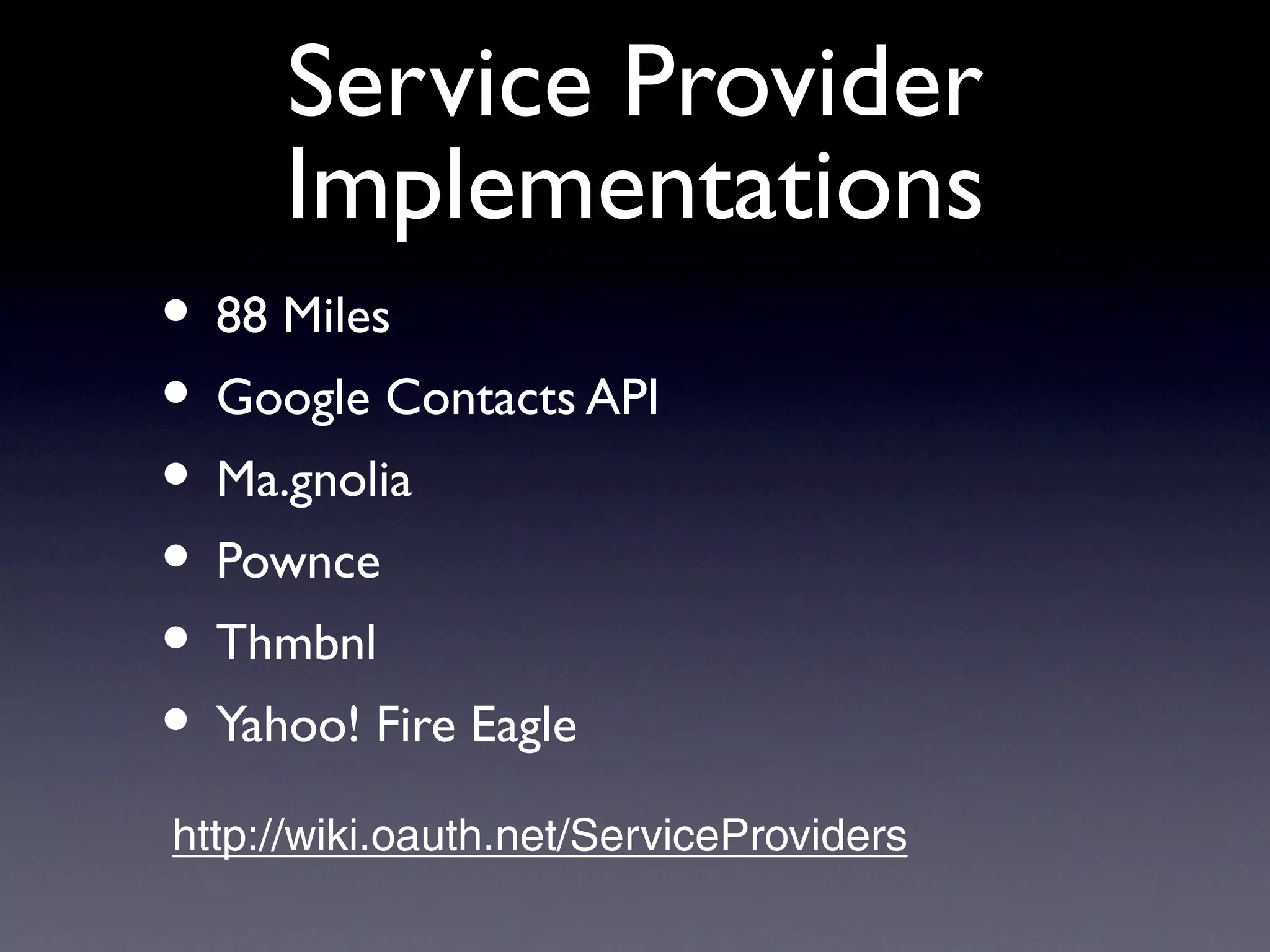
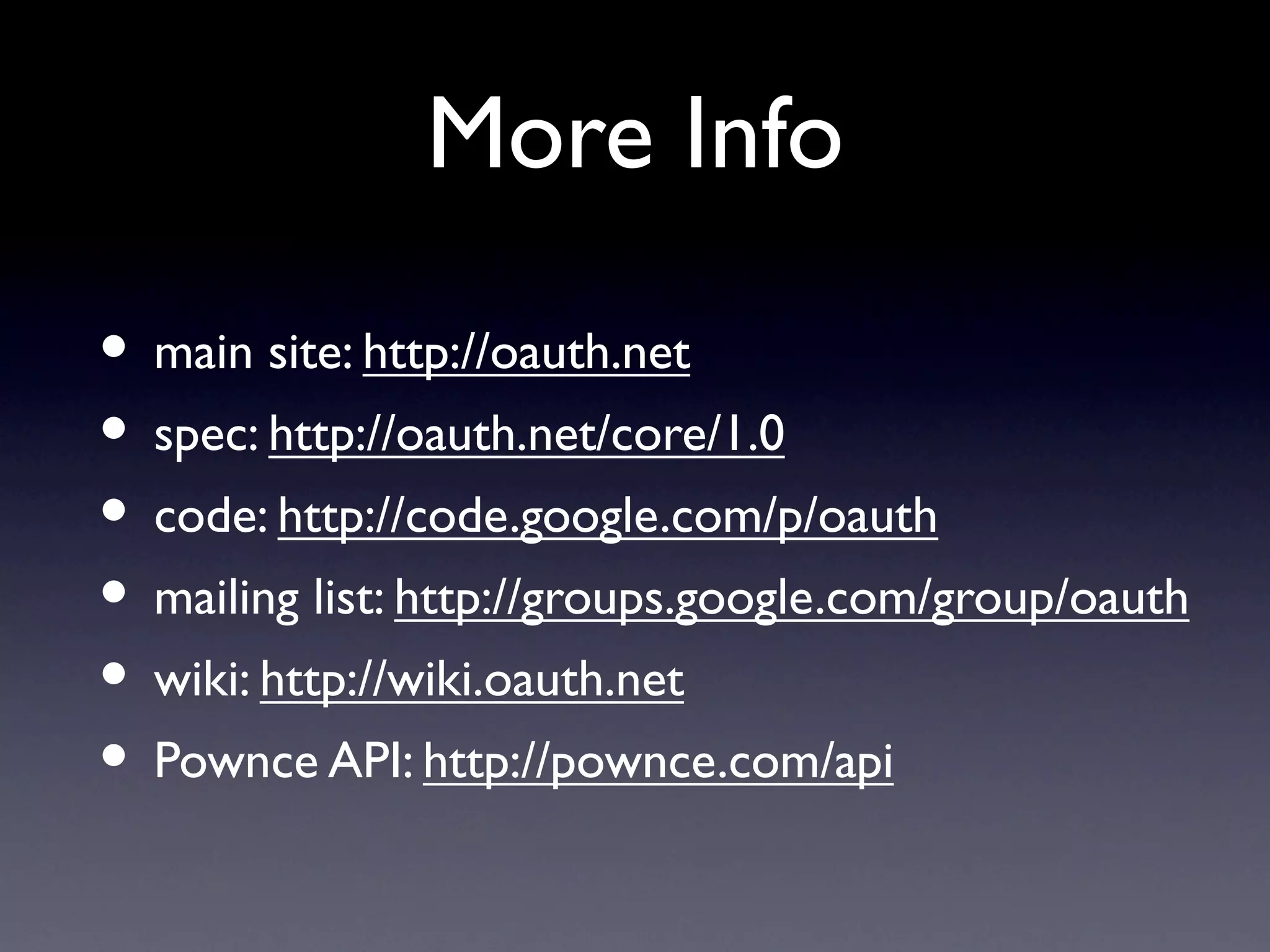
The document provides an overview of OAuth, a standard for secure API authentication, highlighting its implementation in the Pownce API from its launch in 2007. It details the authentication process, the roles of service providers and consumers, and the technical requirements for using OAuth, including token management and signing requests. Additionally, it contrasts OAuth with OpenID, illustrating their differing purposes in user identification and API authorization.