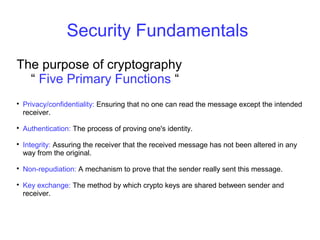
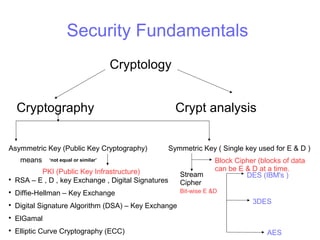
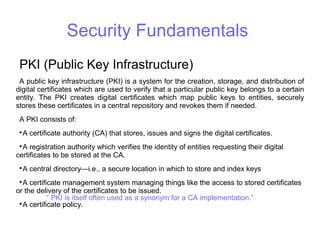
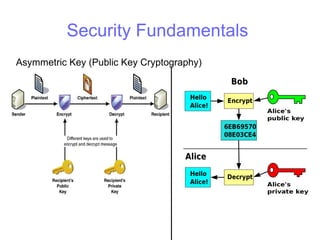
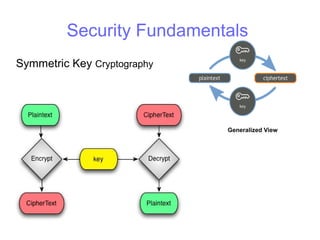
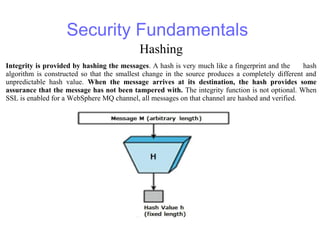
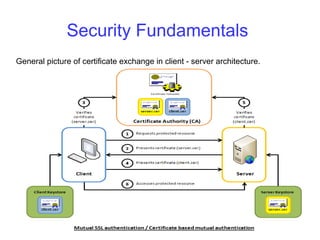
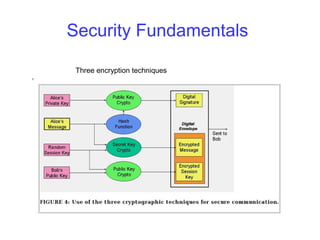
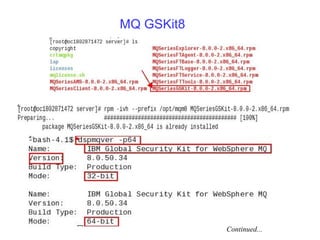
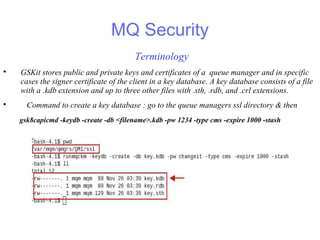
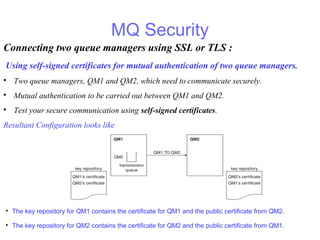
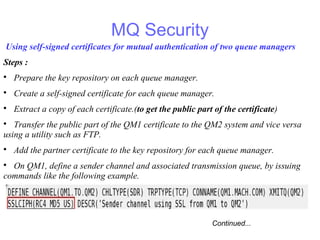
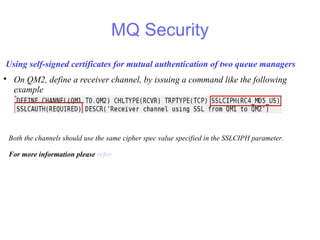
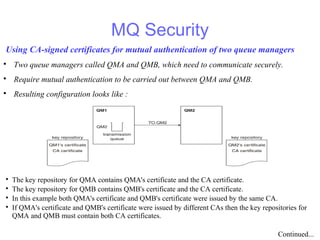
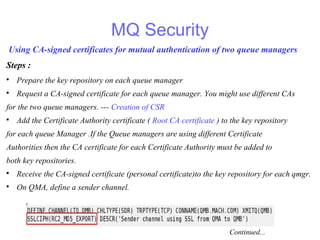
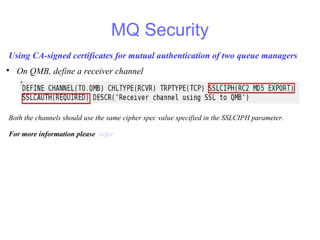
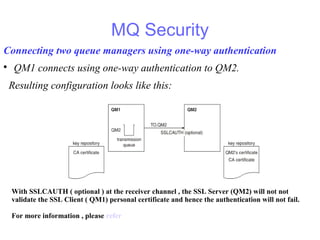
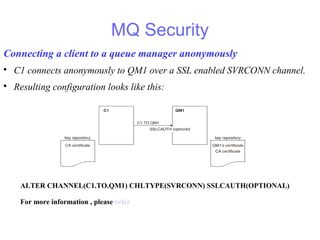
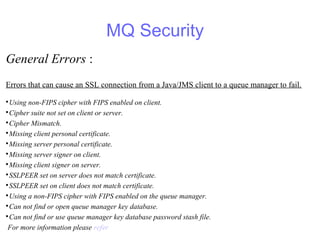
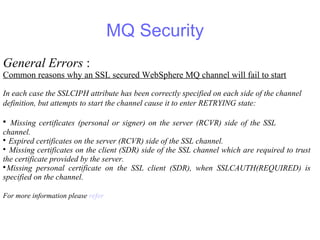
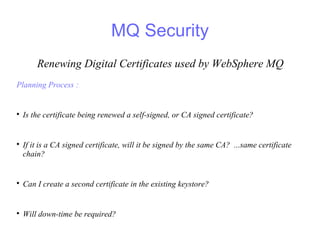
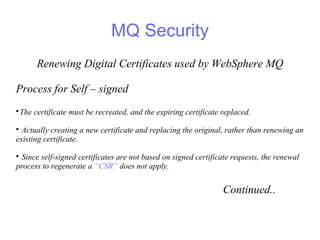
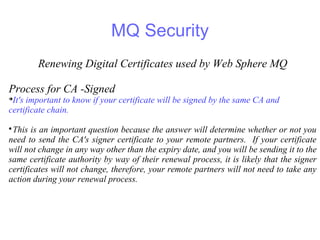
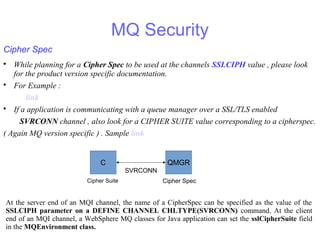
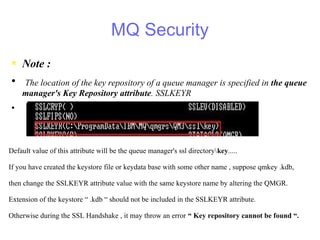
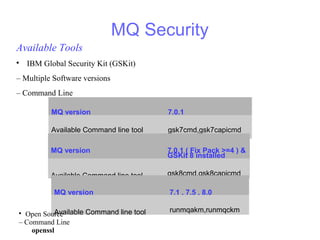
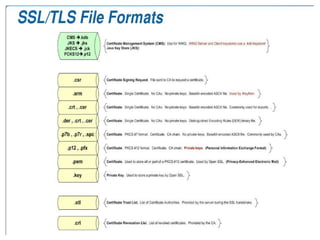
The document provides an overview of MQ security fundamentals, focusing on cryptography, digital certificates, and the Public Key Infrastructure (PKI). It details the roles of SSL/TLS in securing communications and describes the processes for mutual authentication between queue managers using self-signed and CA-signed certificates. Additionally, it outlines the management of digital certificates, including renewal procedures and common errors encountered in SSL connections.