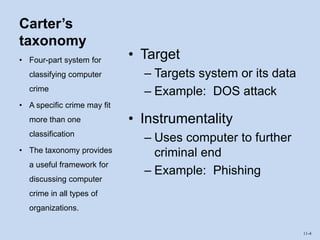
Carter's taxonomy provides a four-part system for classifying computer crimes: target crimes target systems or data, instrumentality crimes use computers to further criminal ends, incidental crimes are not computer-dependent but related to computers, and associated crimes are new versions of traditional crimes. The chapter discusses risks and threats to information systems like fraud, interruptions, and information disclosure, and controls to prevent computer crimes through physical, technical, and administrative measures. It also explains that COBIT provides a framework for IT governance and management through principles and enablers that match IT capabilities to user needs.