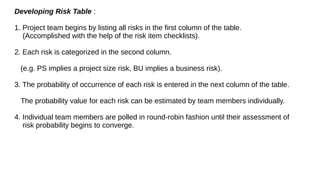
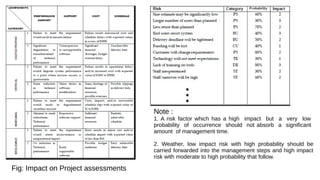
The document discusses software risk management and types of risks in software development projects. It identifies five main types of risks: schedule risks, budget risks, operational risks, technical risks, and programmatic risks. It then describes various tools and techniques for risk identification, assessment, and management, including documentation reviews, brainstorming, risk tables, and risk monitoring. Effective communication is also highlighted as important for coordinating the project team and managing risks.