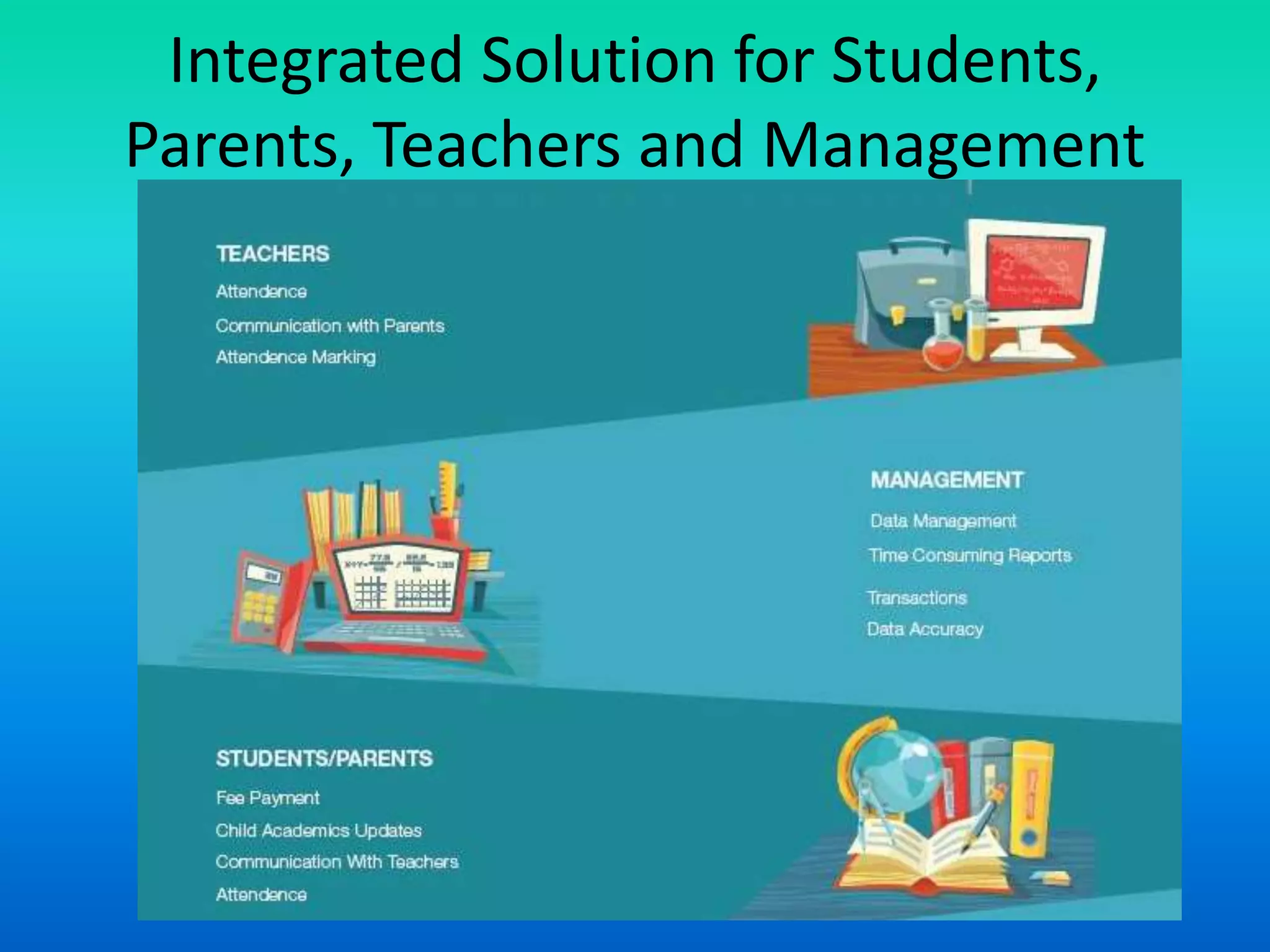
The document provides an overview of systems concepts in software design, emphasizing that a system is a collection of interrelated elements that transforms inputs into outputs with the aim of achieving specific objectives. It outlines key components such as subsystems, suprasystems, and the importance of feedback in the process. Additionally, it discusses integrated solutions for fee management in educational systems, highlighting features like online fee collection and automated tracking.