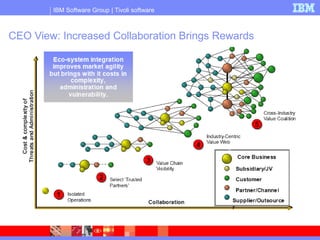
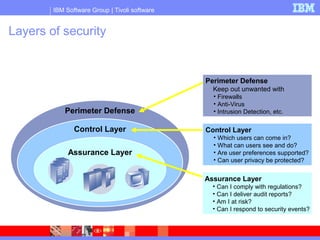
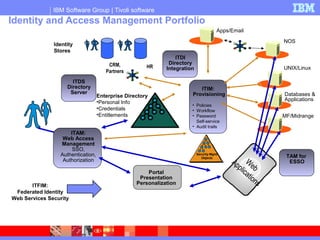
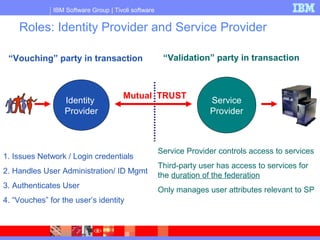
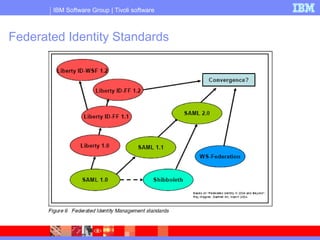
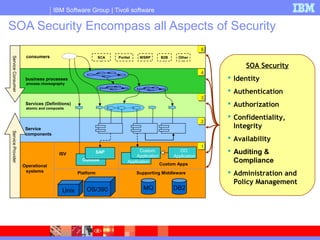
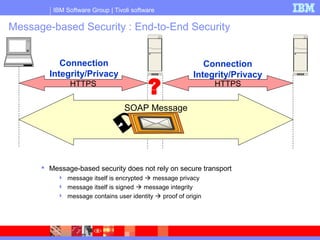
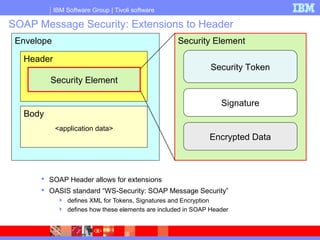
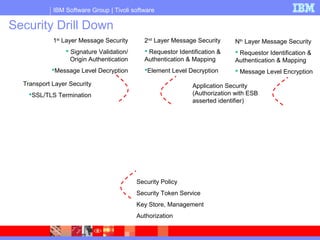
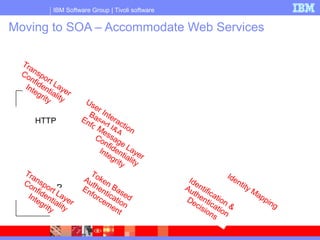
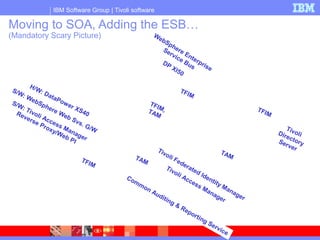
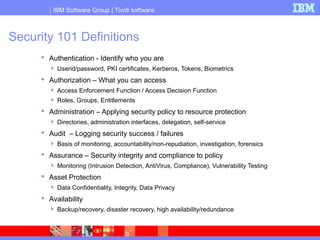
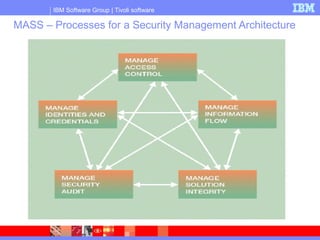
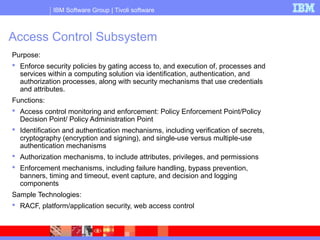
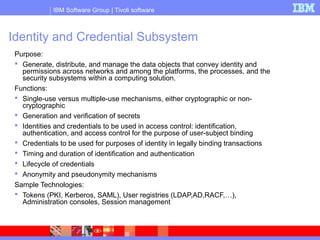
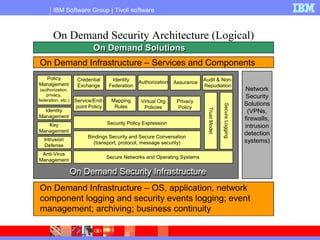
This document discusses security considerations for service-oriented architectures (SOA) and on-demand environments. It describes several subsystems that are important for a comprehensive security management architecture (MASS), including access control, identity and credential management, information flow control, security auditing, and solution integrity. Technologies that can be used to implement each subsystem are also outlined, such as directories, firewalls, encryption, and systems management solutions. The document stresses that security requires an integrated approach across all of these areas.