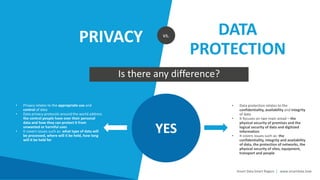
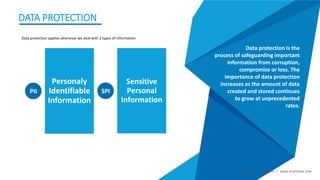
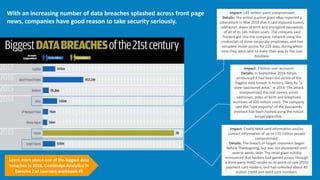
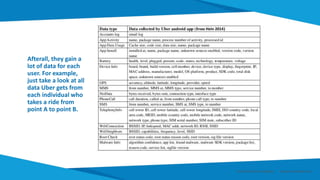
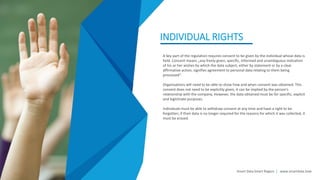
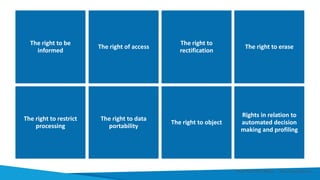
The document provides an overview of ethics, legislation, and privacy issues related to big data. It discusses the necessity of regulating big data and the differences between privacy and data protection. It also provides details on the General Data Protection Regulation (GDPR), including its goals, requirements for companies, and individual rights it aims to protect.