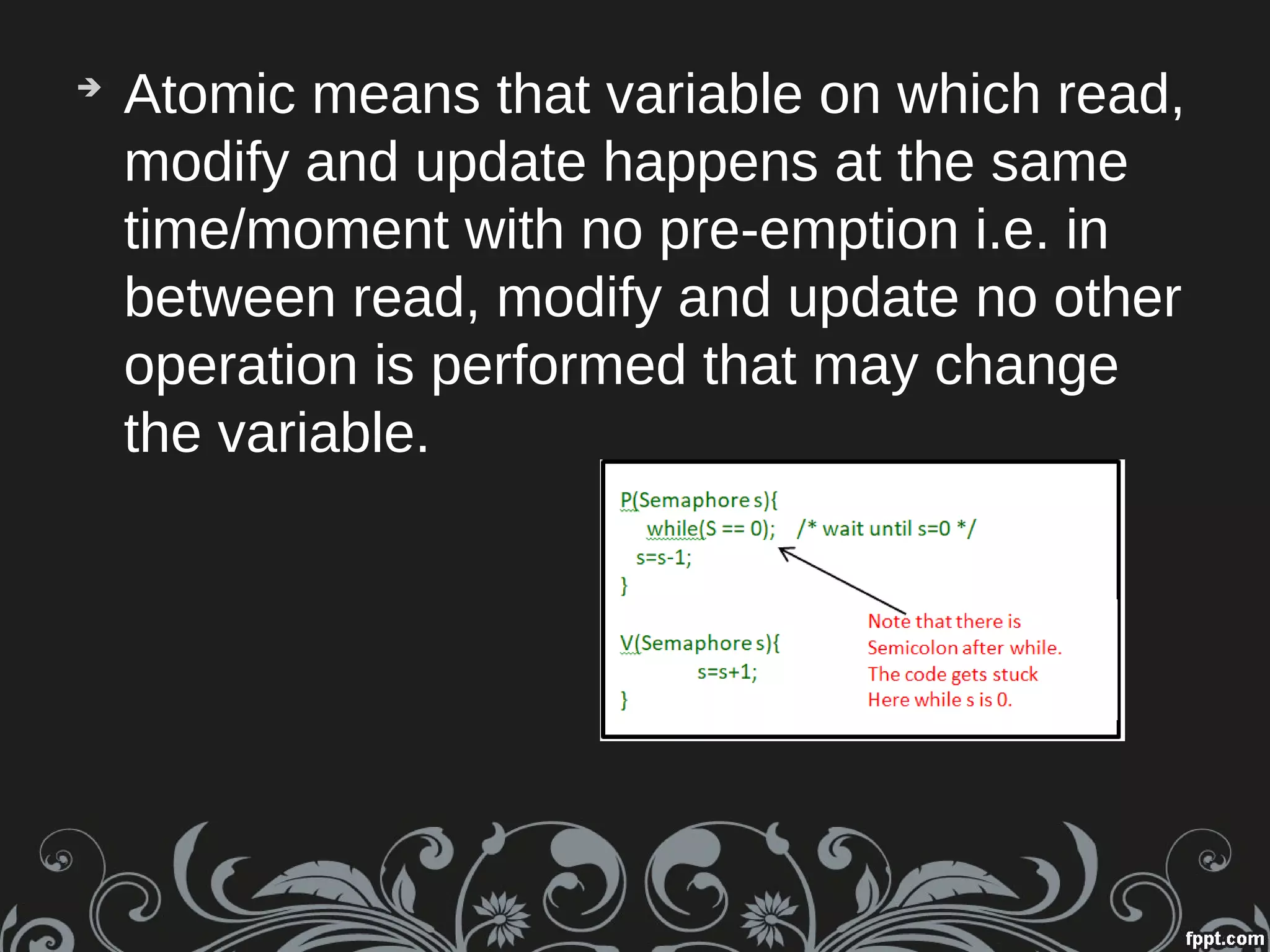
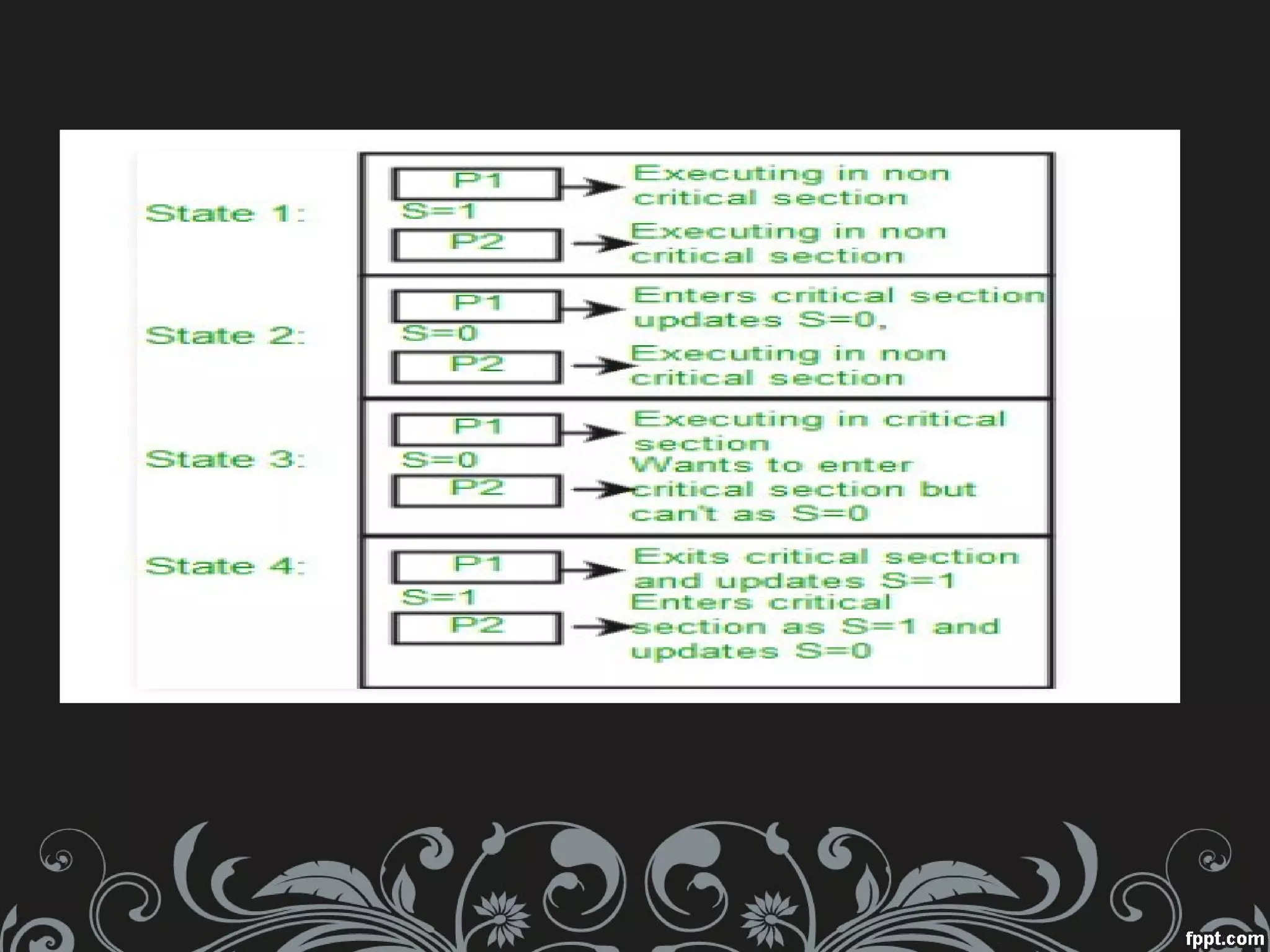
Semaphores are variables that allow processes and threads to synchronize access to shared resources. There are two main types: binary semaphores, which allow mutually exclusive access to a resource, and counting semaphores, which allow access to a limited number of identical resources. Semaphores use two atomic operations - P() to decrement the semaphore and wait if it is not positive, and V() to increment the semaphore and wake a waiting thread. This allows processes to synchronize access to critical sections and resources in a multiprocessing environment.


![Operations SupportedOperations Supported
Only Two Atomic operations
➔
P(sem) : Waits for semaphore to become
positive, then decrement it by 1 .
➔
V(sem) : [Signal] Increments semaphore
by 1 and wakes up a waiting thread at P(),
if any.](https://image.slidesharecdn.com/os-201025084719/75/Semaphores-4-2048.jpg)