Embed presentation
Downloaded 21 times
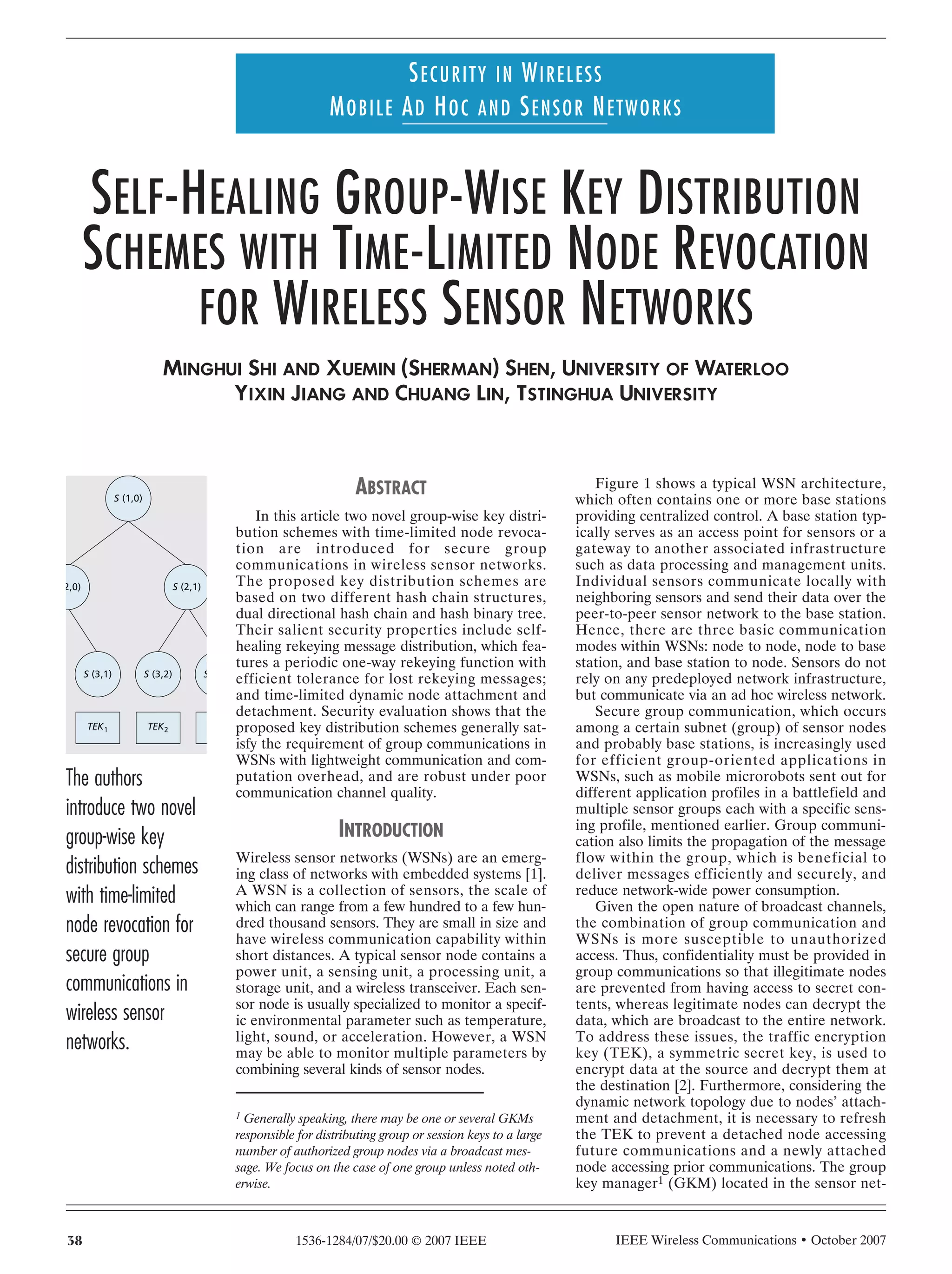









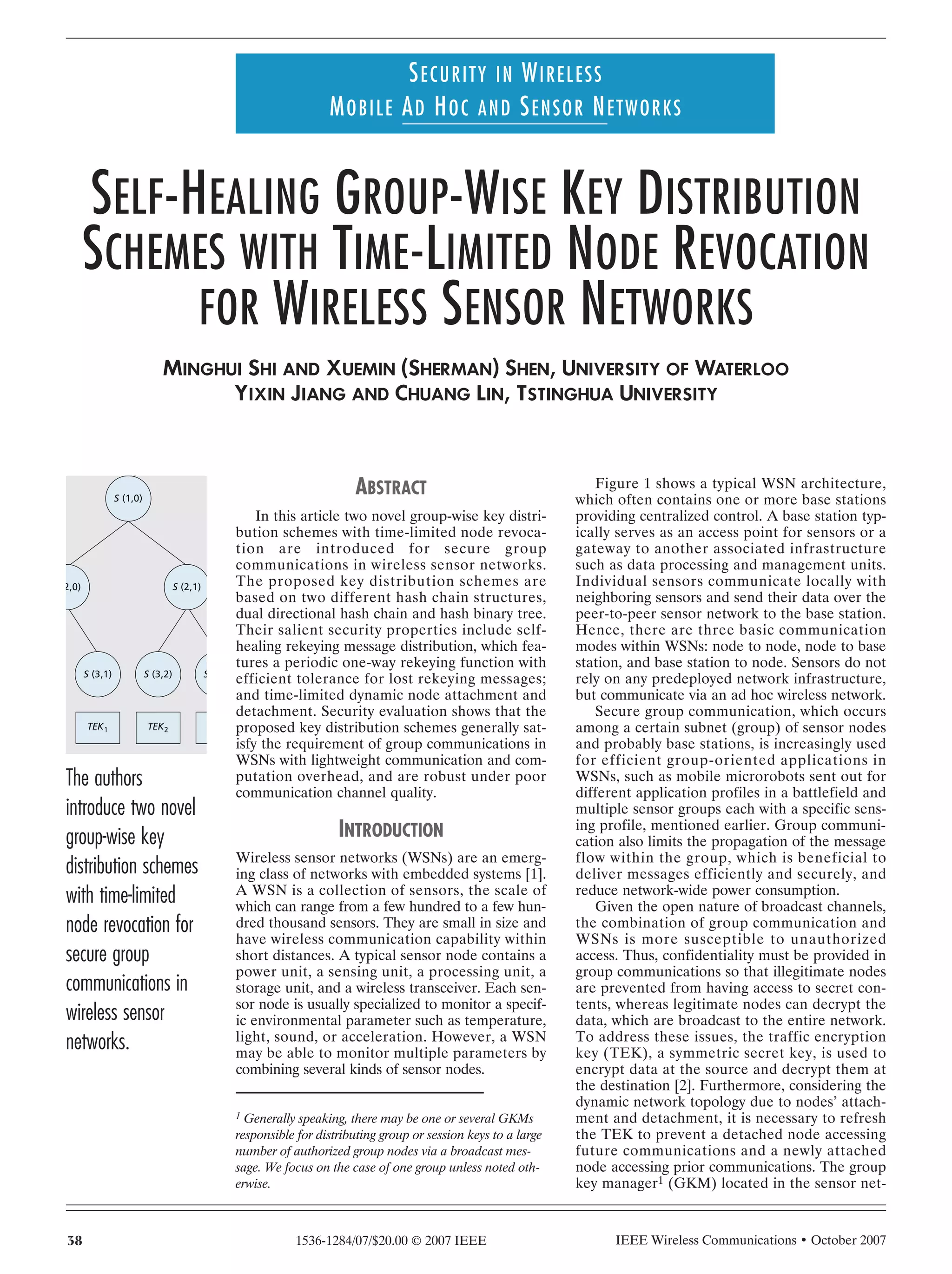
The document summarizes two novel group-wise key distribution schemes for secure group communications in wireless sensor networks that are based on dual directional hash chains (DDHC) and hash binary trees (HBT). The schemes offer self-healing rekeying message distribution with efficient tolerance for lost messages. They also feature time-limited dynamic node attachment and detachment. Security evaluation shows the schemes satisfy requirements for group communications in WSNs with lightweight overhead.