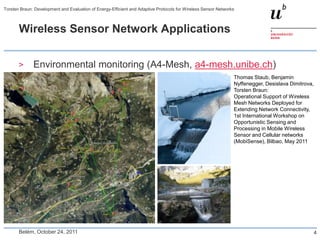
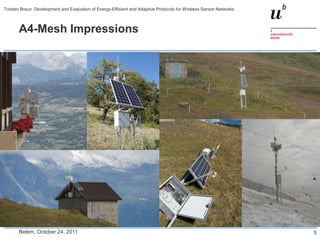
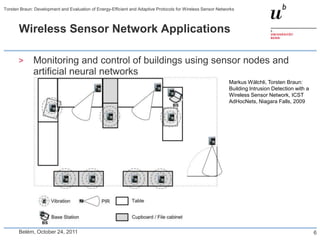
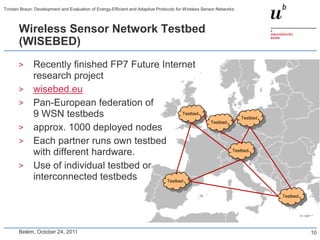
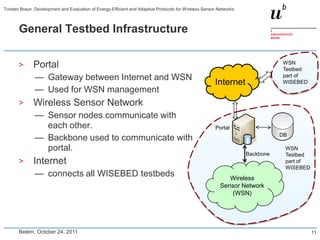
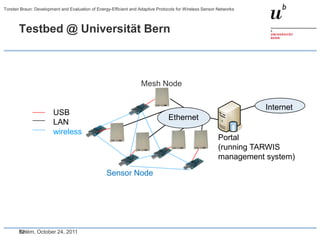
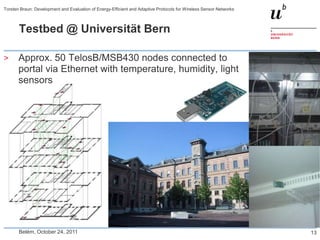
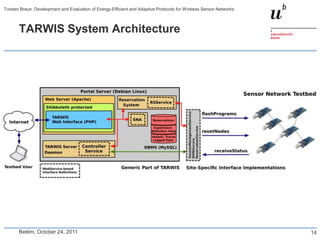
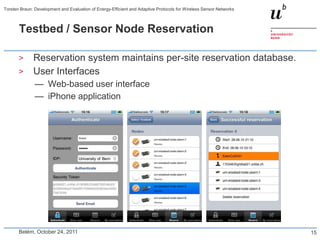
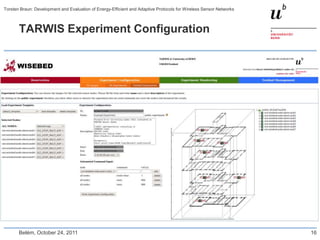
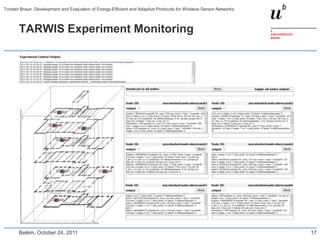
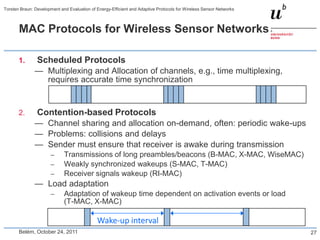
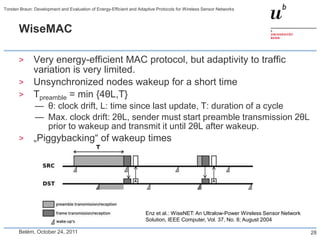
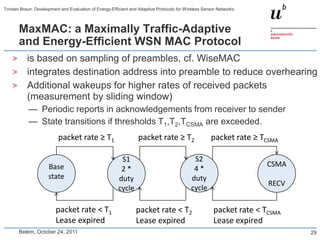
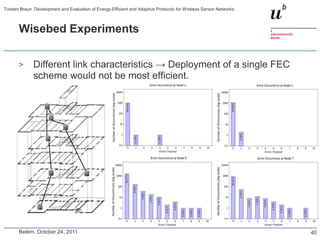
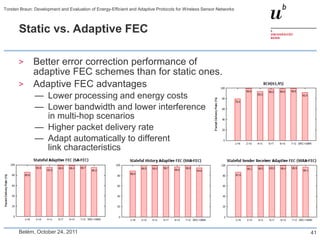
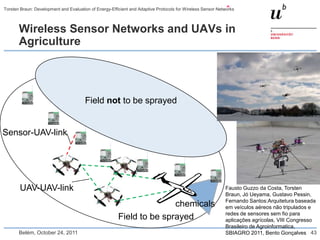
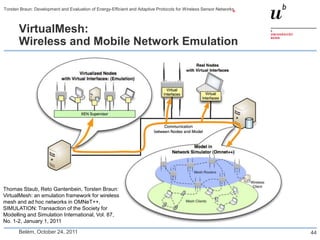
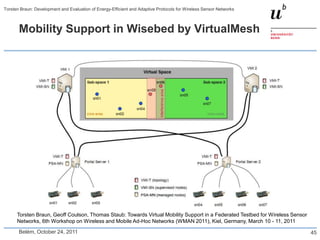
Torsten Braun presented on developing and evaluating energy-efficient and adaptive protocols for wireless sensor networks. He discussed wireless sensor network applications like environmental and building monitoring. Key application requirements include energy efficiency, low delays, reliability, and adaptivity. He described designing, implementing, and evaluating WSN protocols through simulations and experiments on a wireless sensor network testbed called WISEBED, which is a pan-European federation of over 1000 sensor nodes across 9 testbeds. The testbed infrastructure includes sensor nodes, backbones to connect to a portal, and a portal that acts as a gateway between the internet and the wireless sensor network.