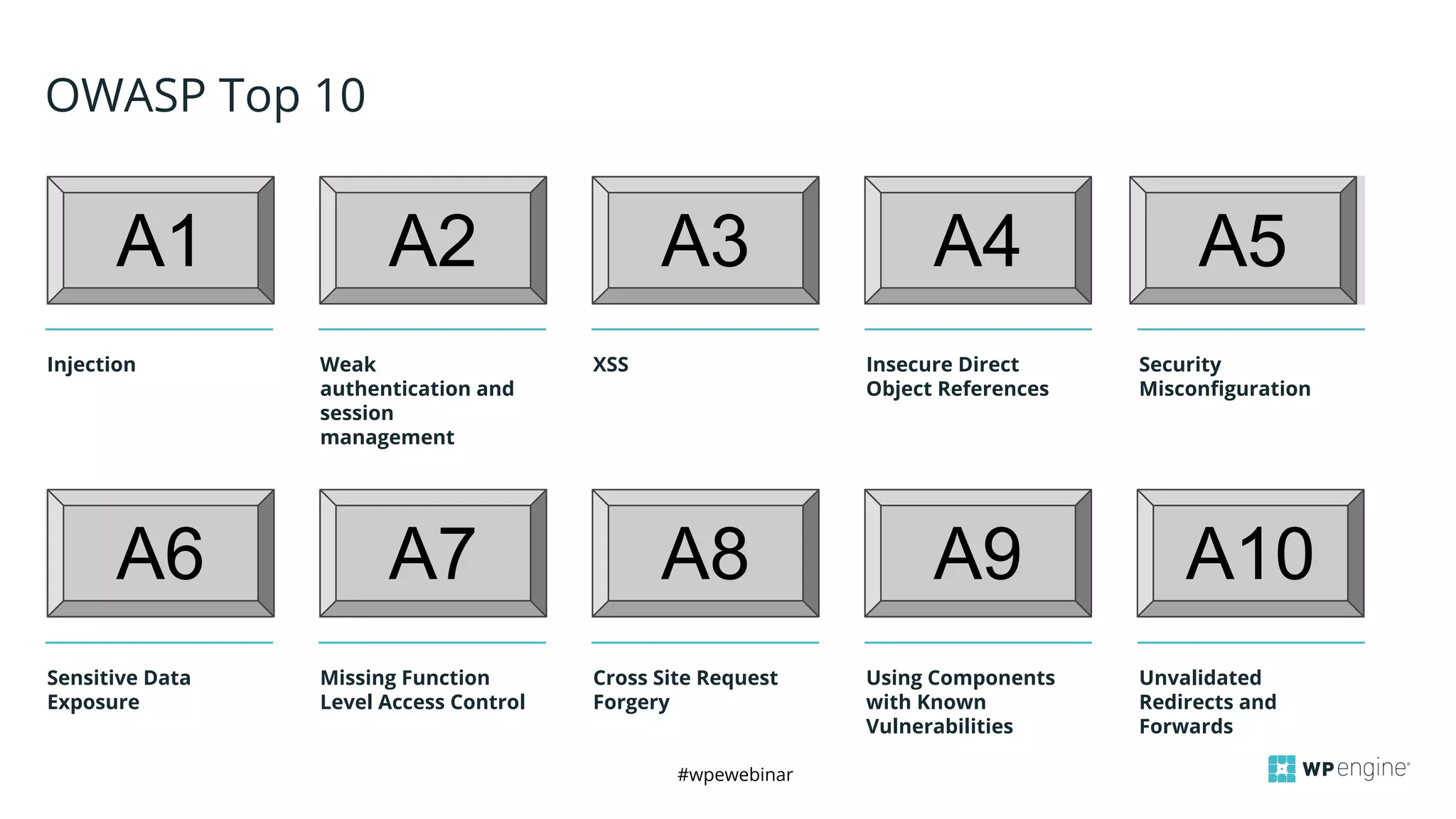
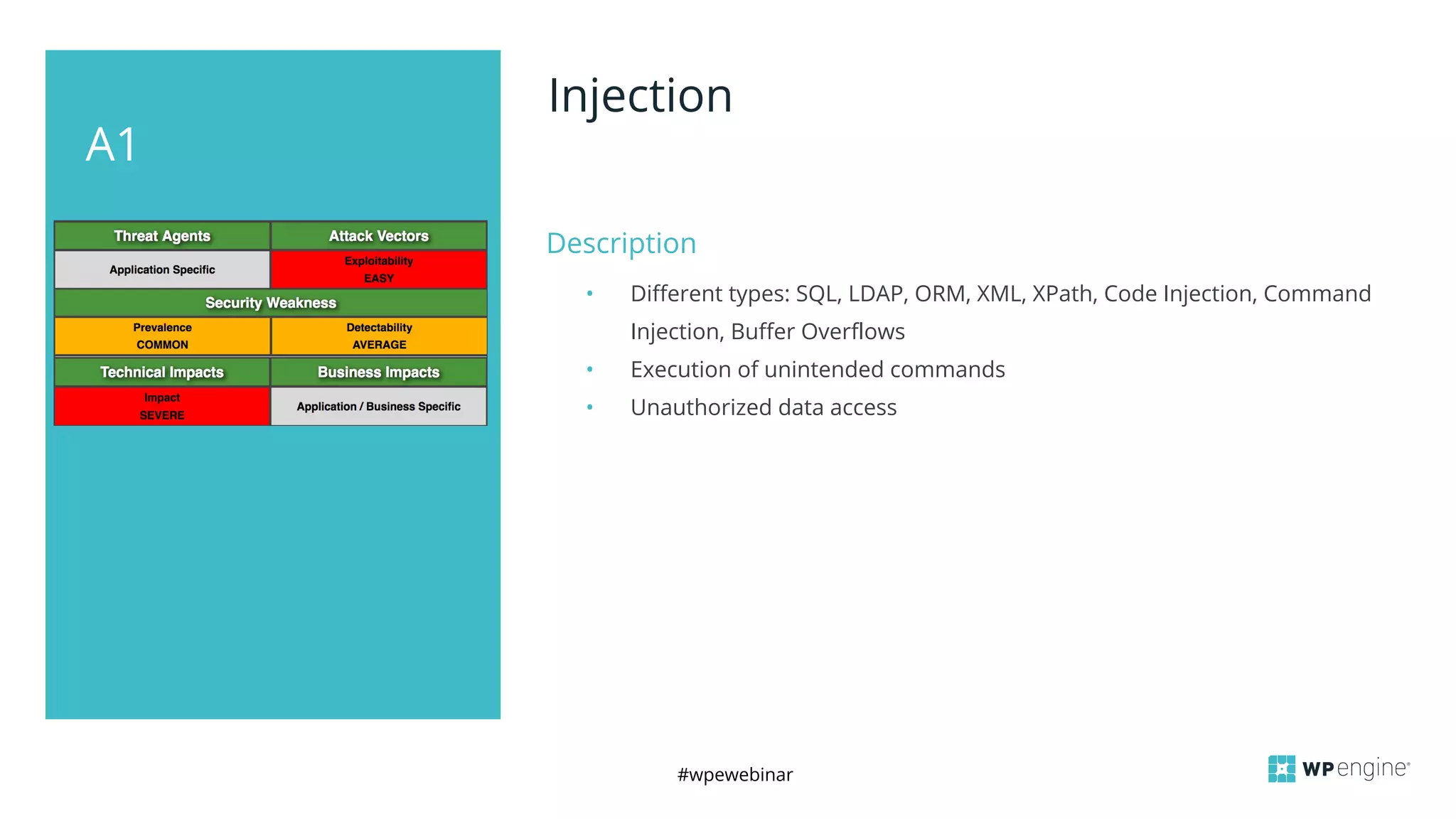
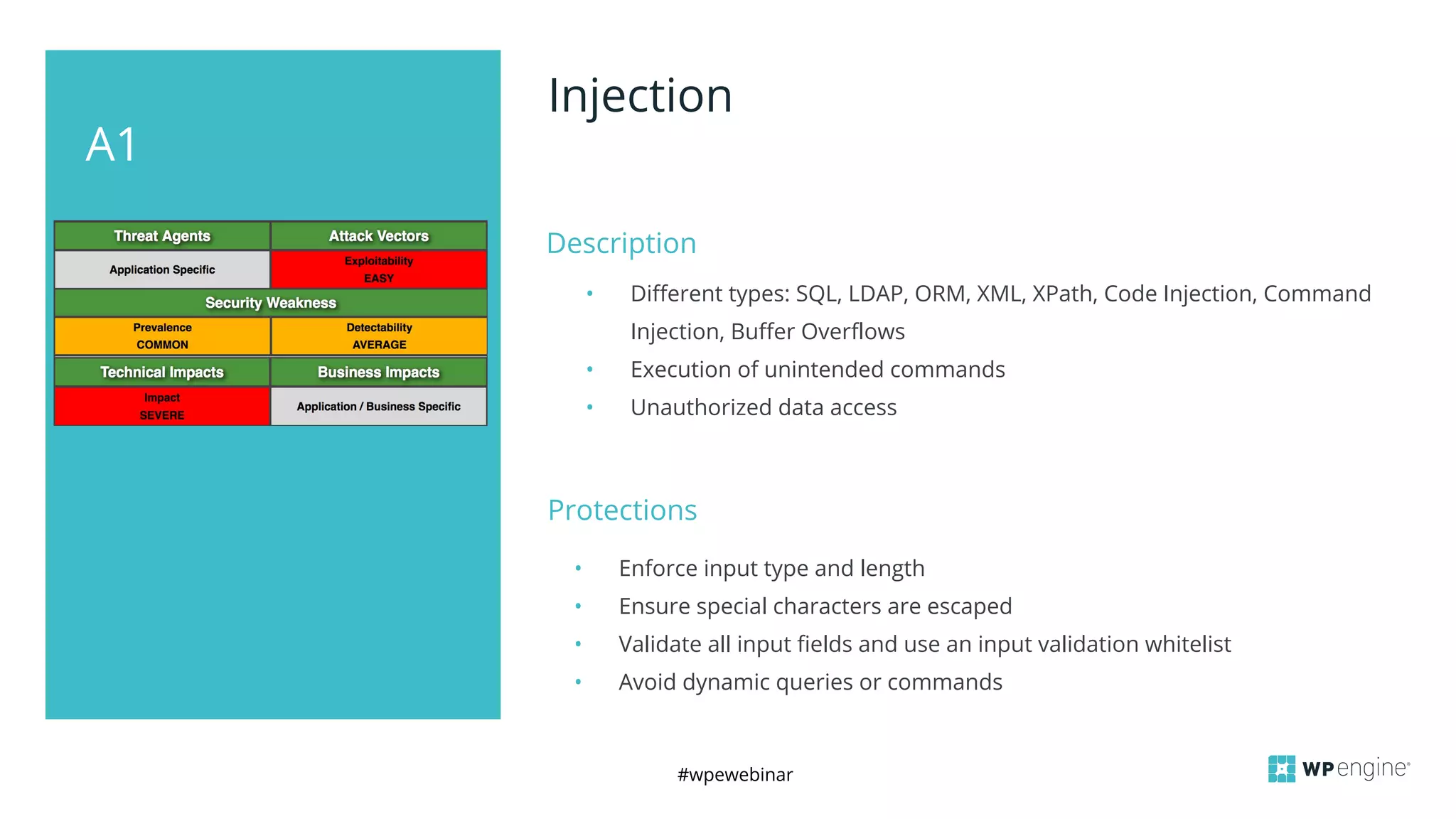
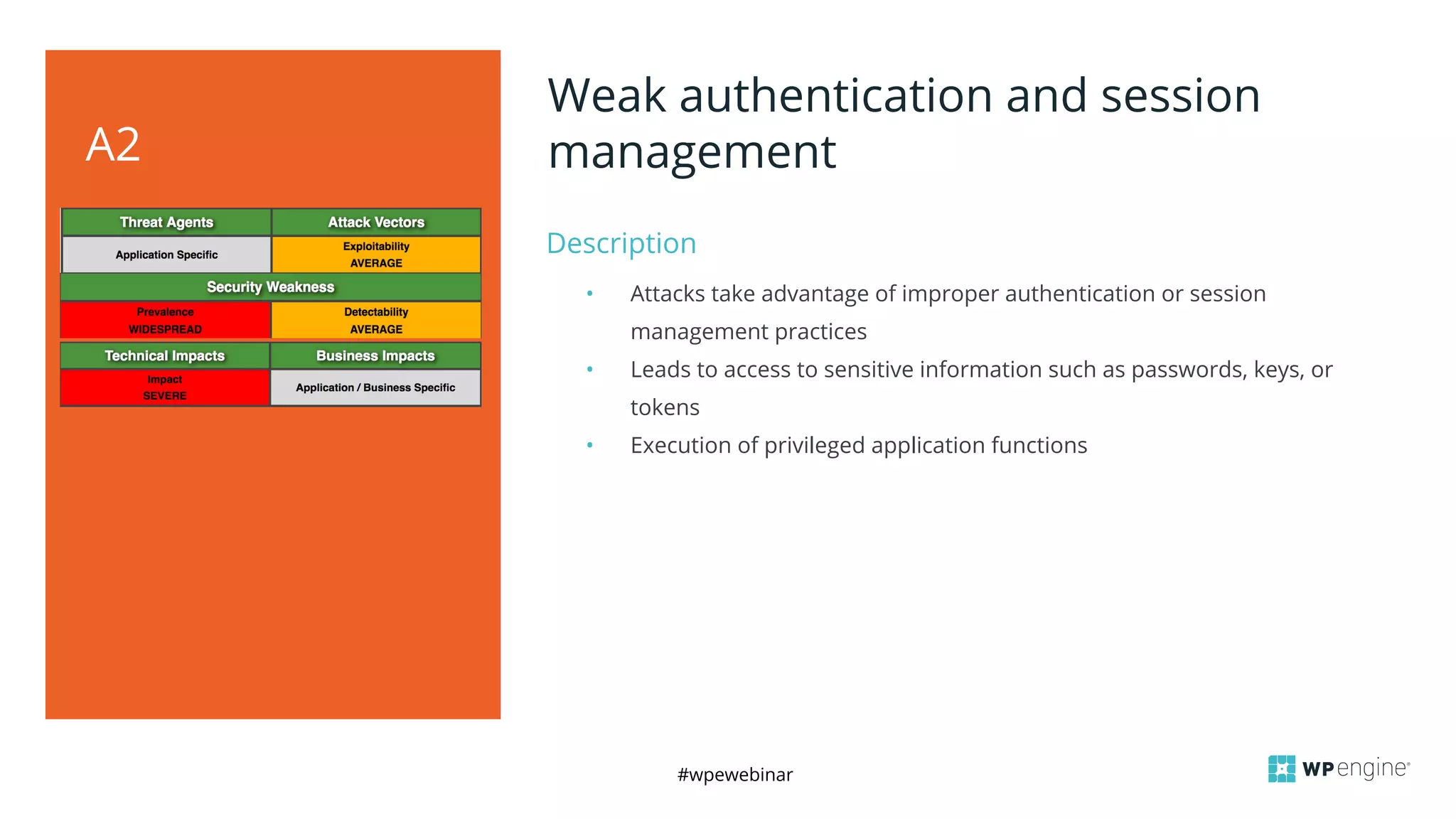
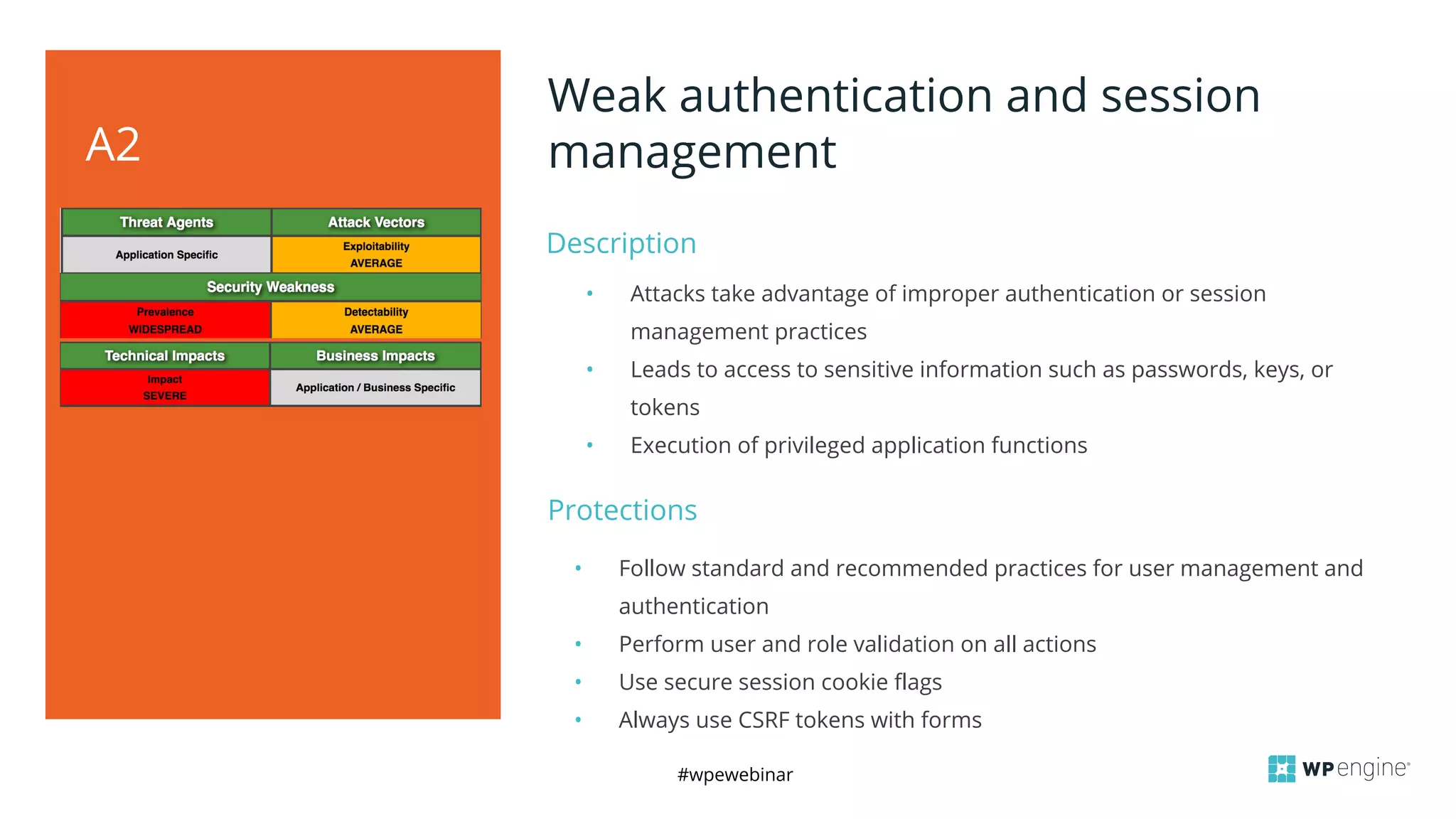
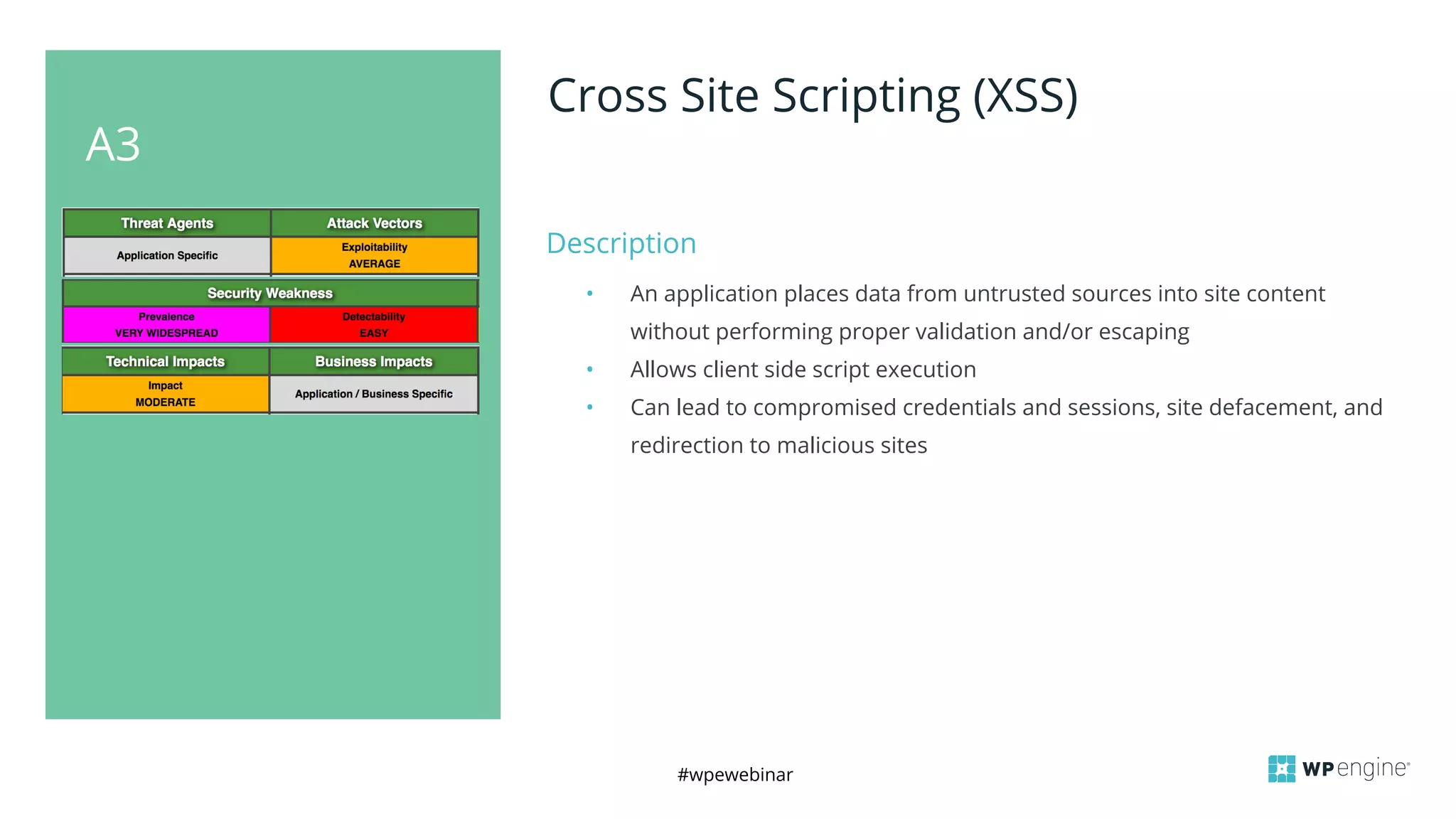
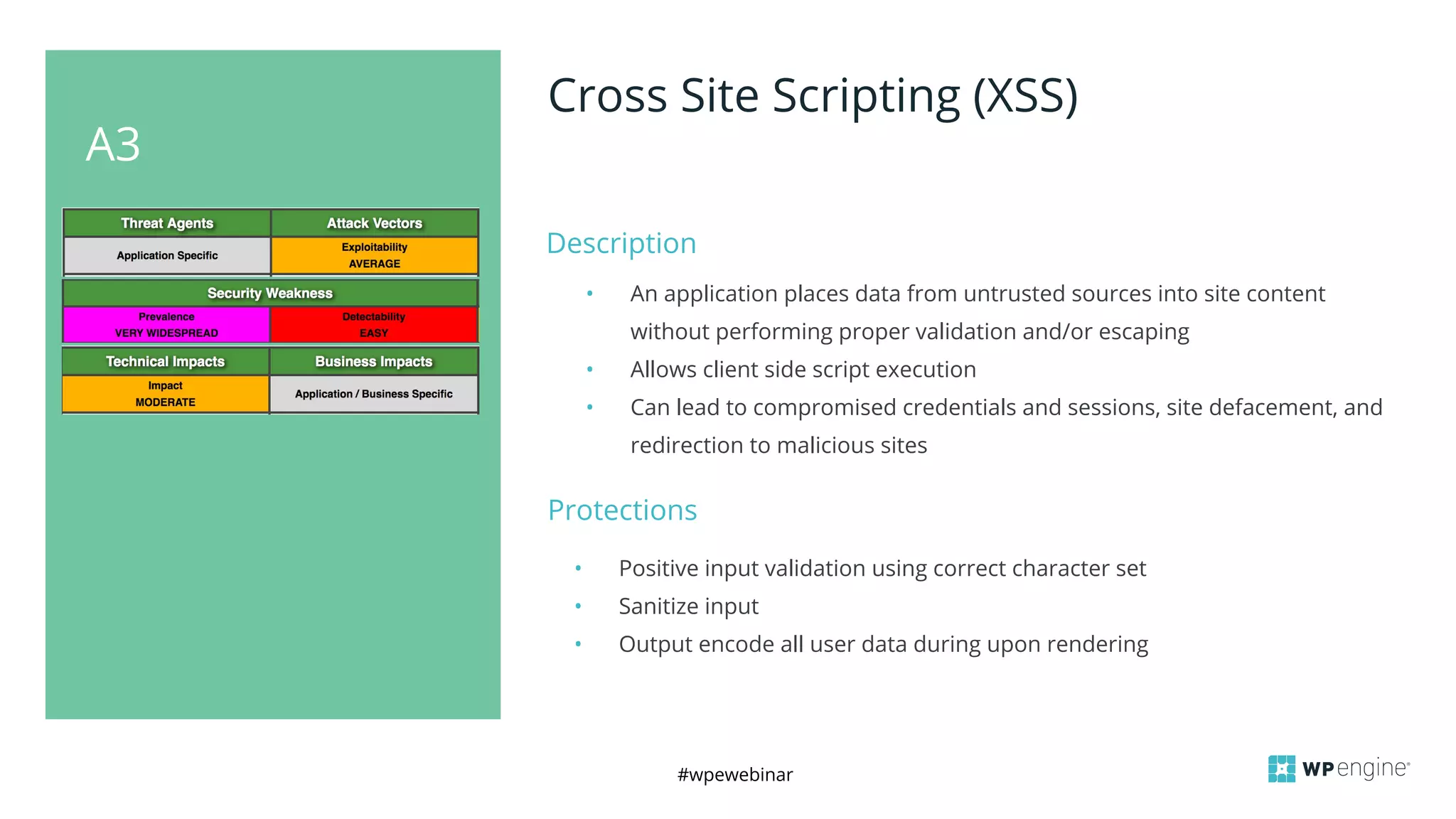
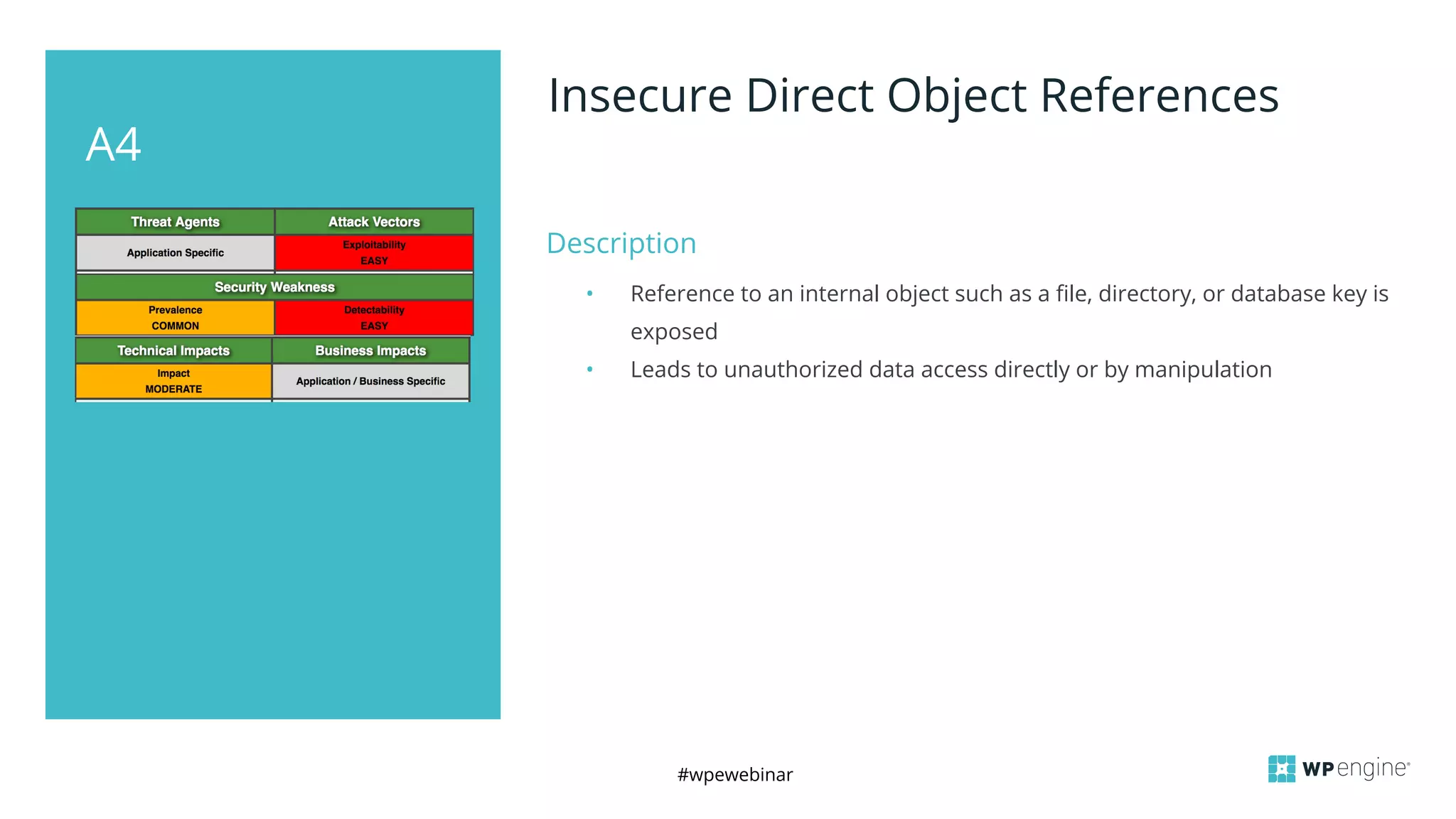
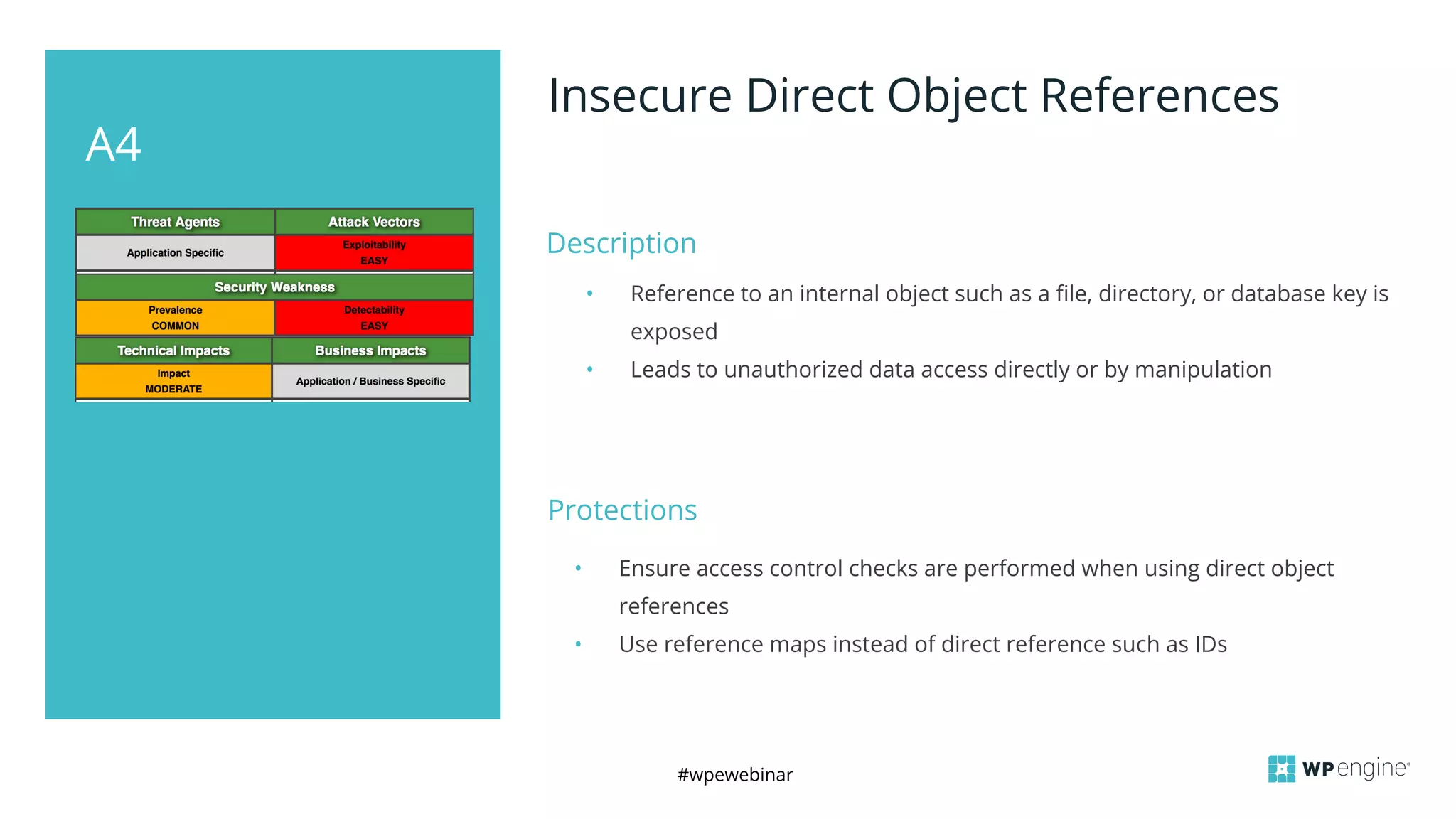
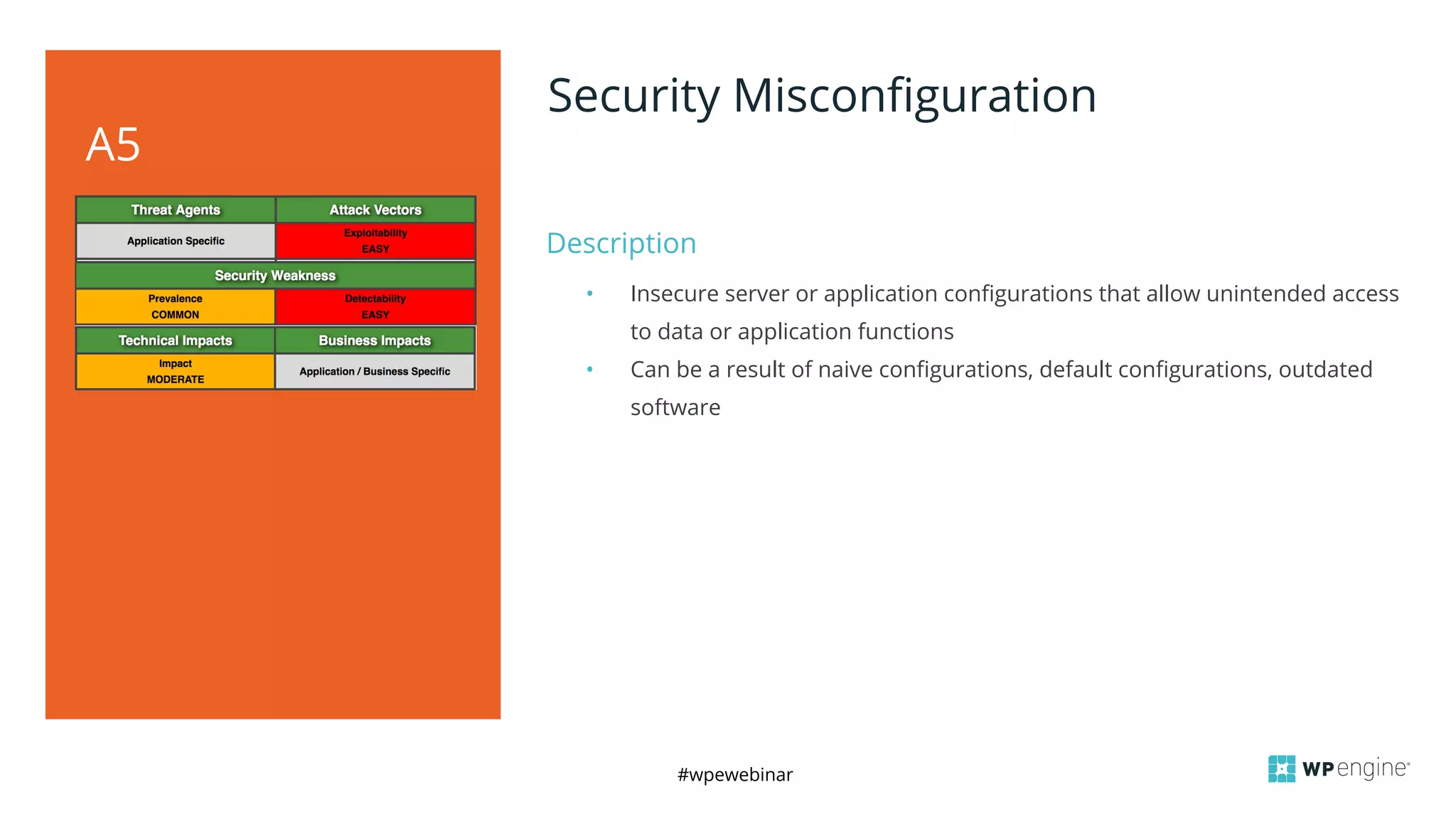
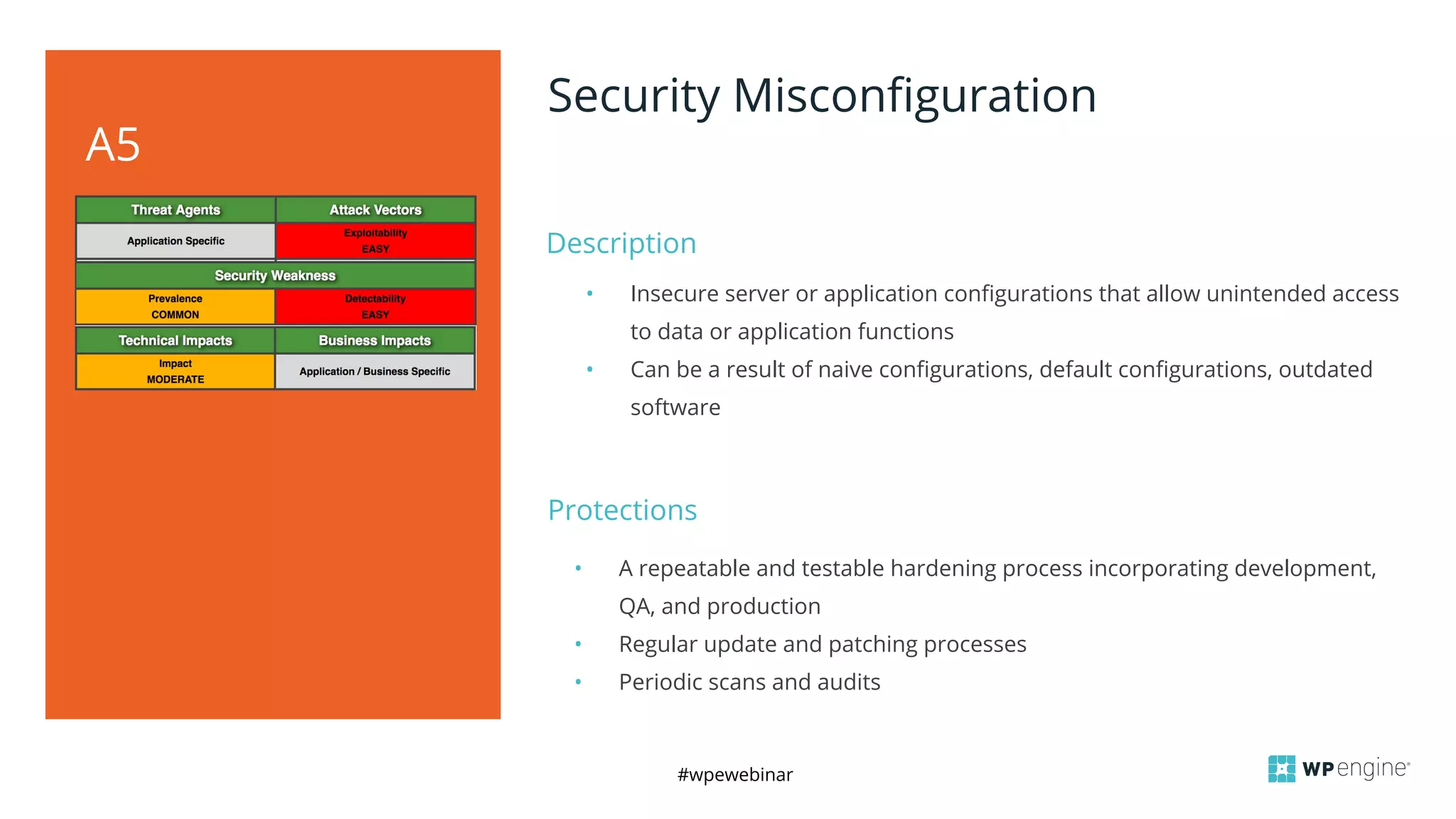
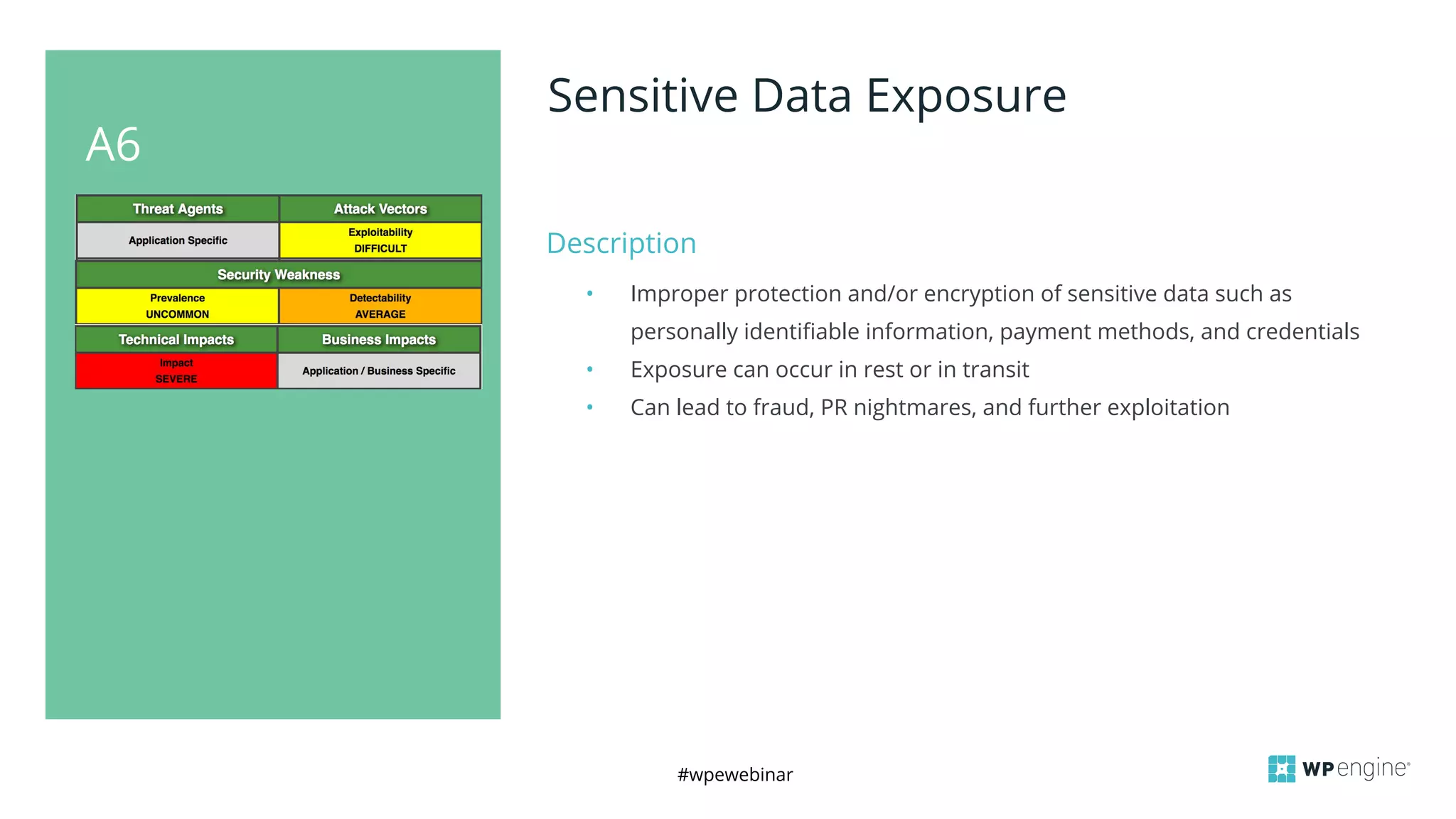
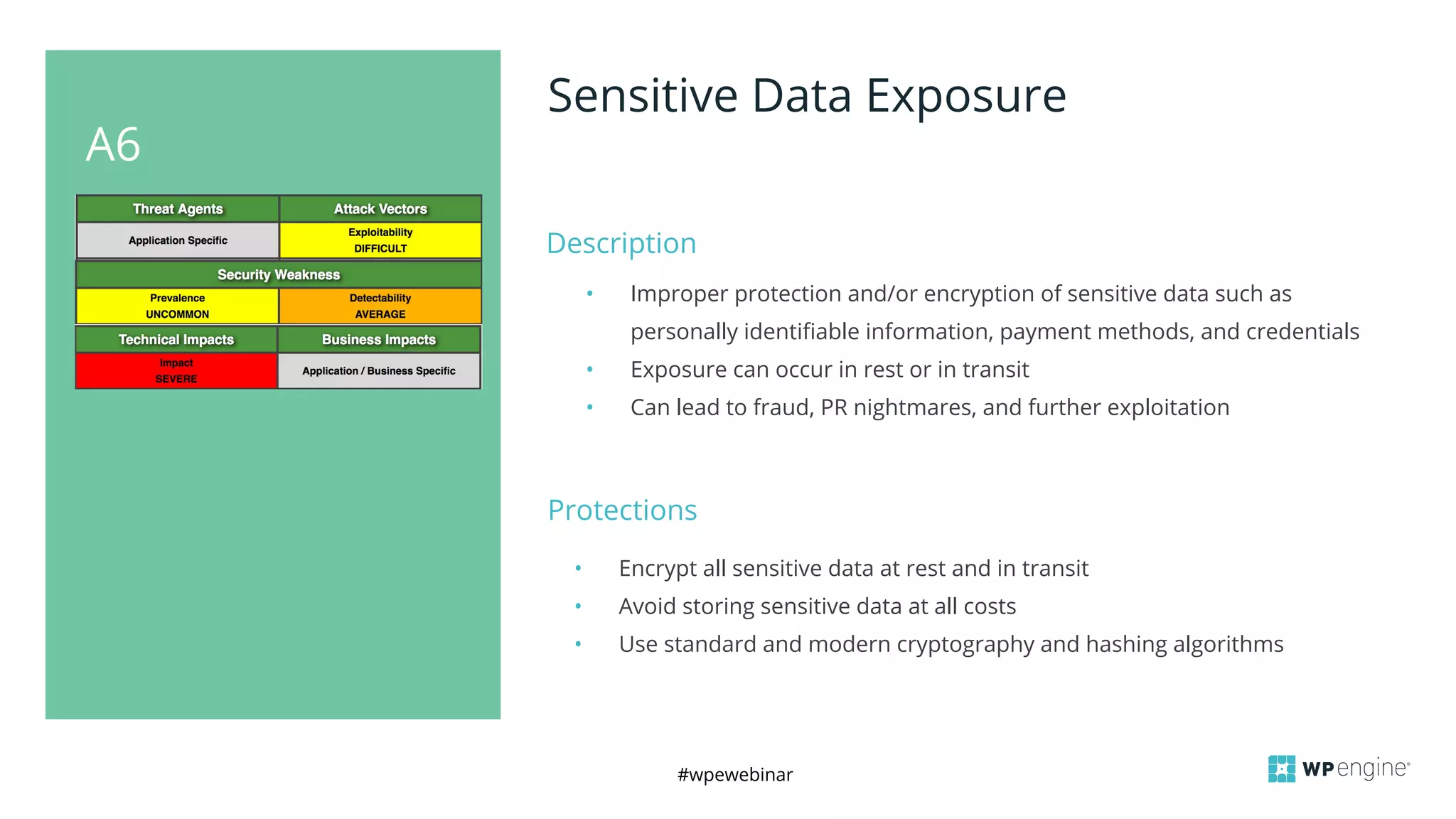
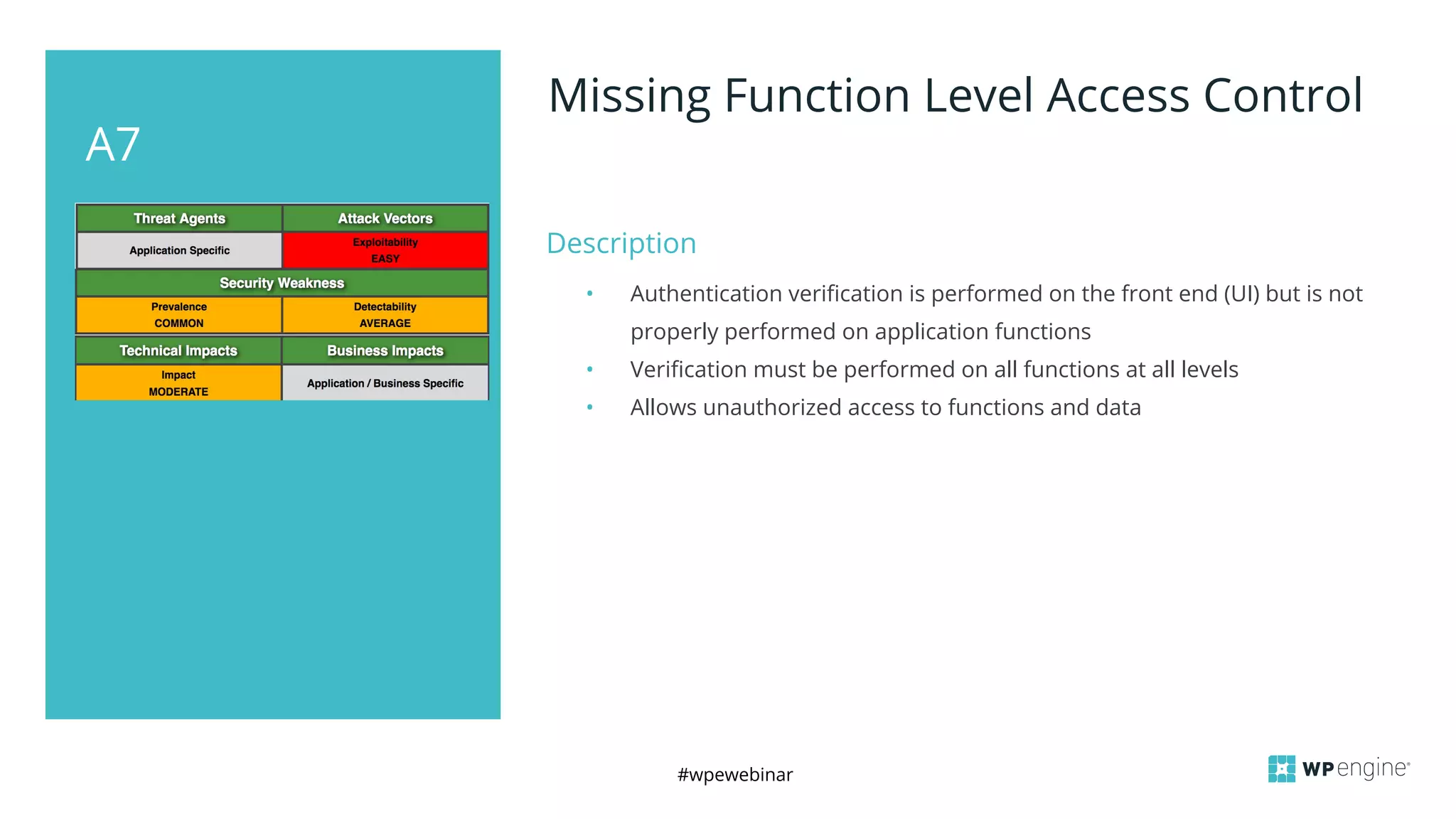
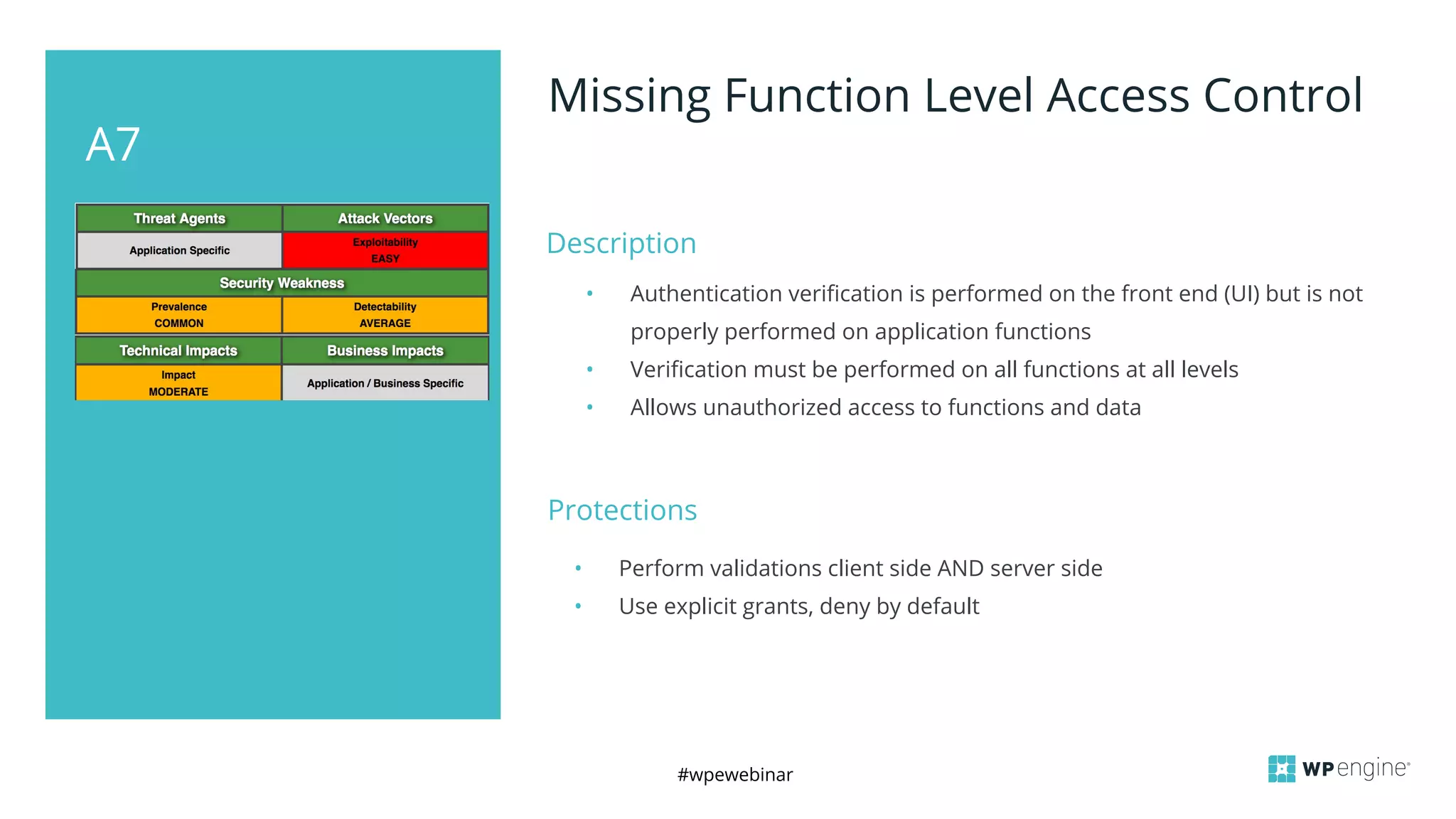
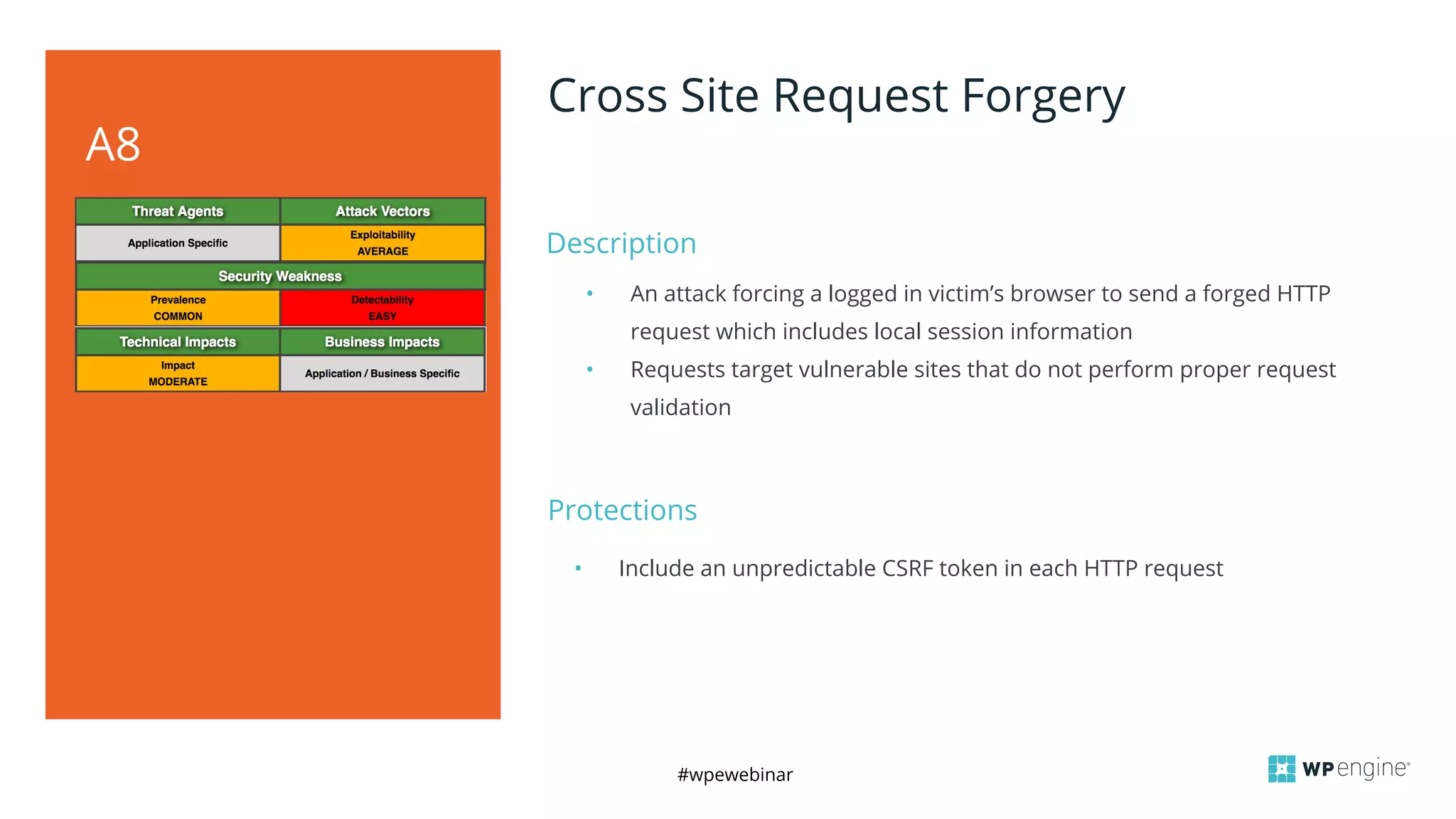
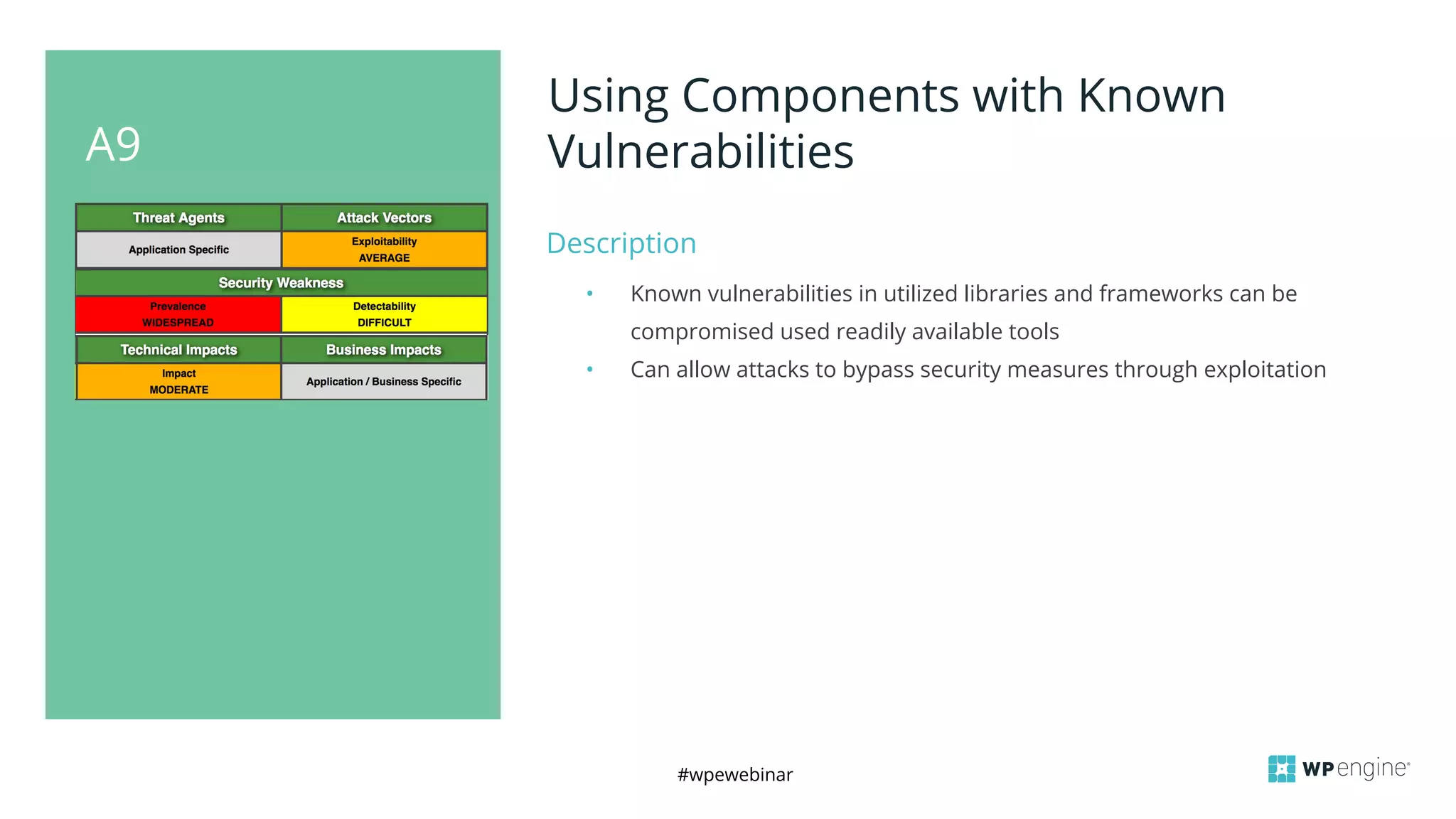
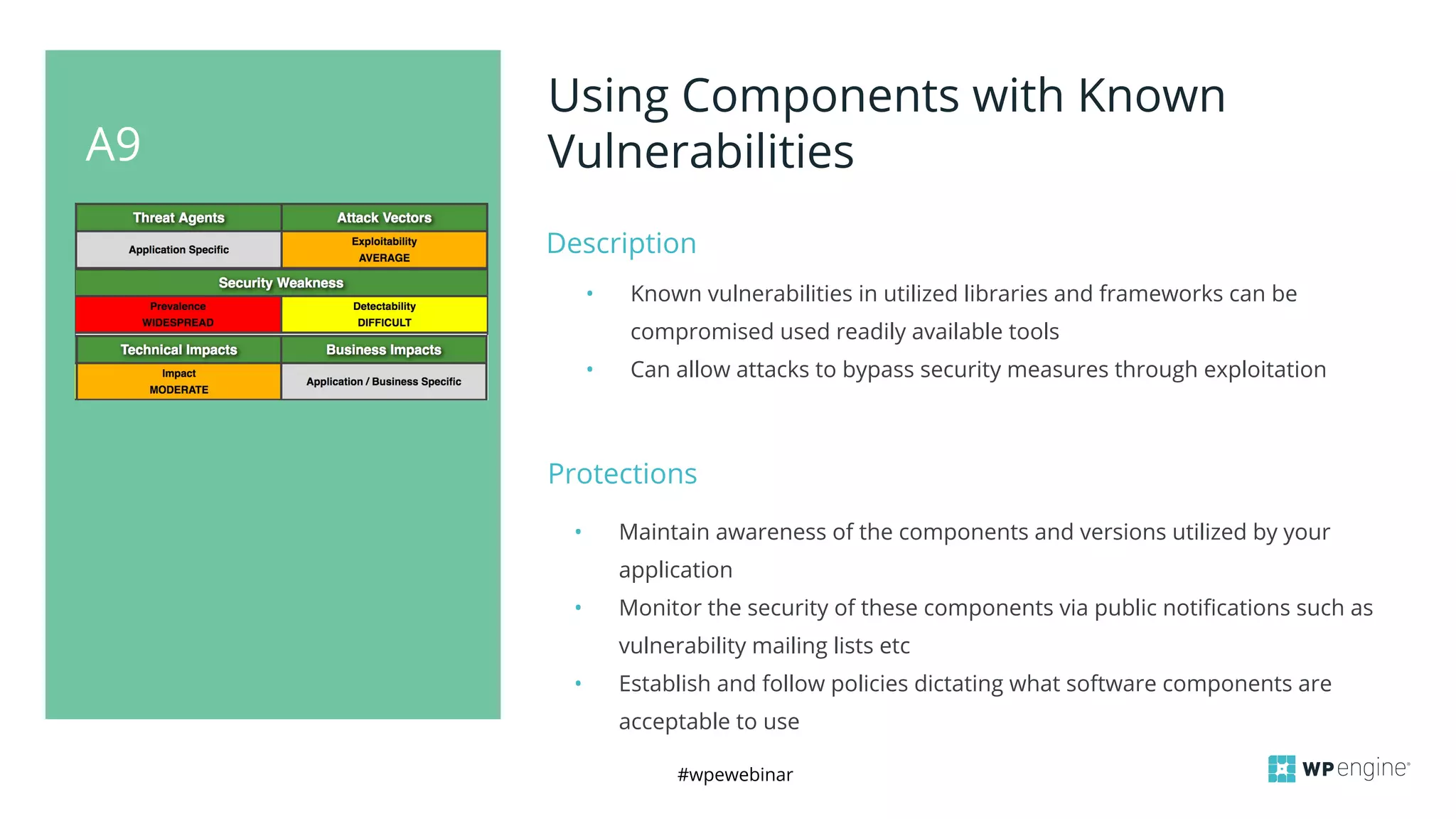
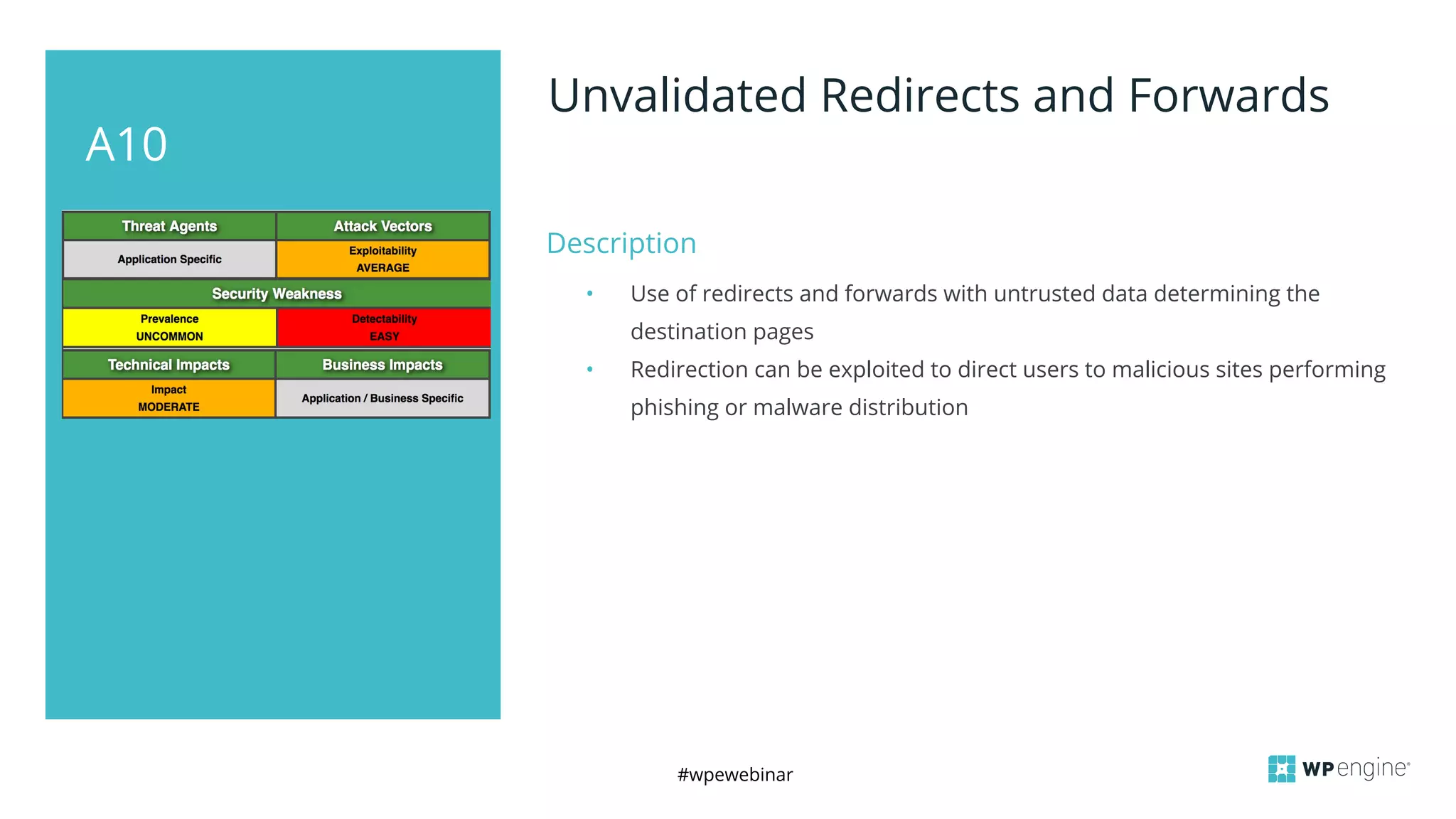
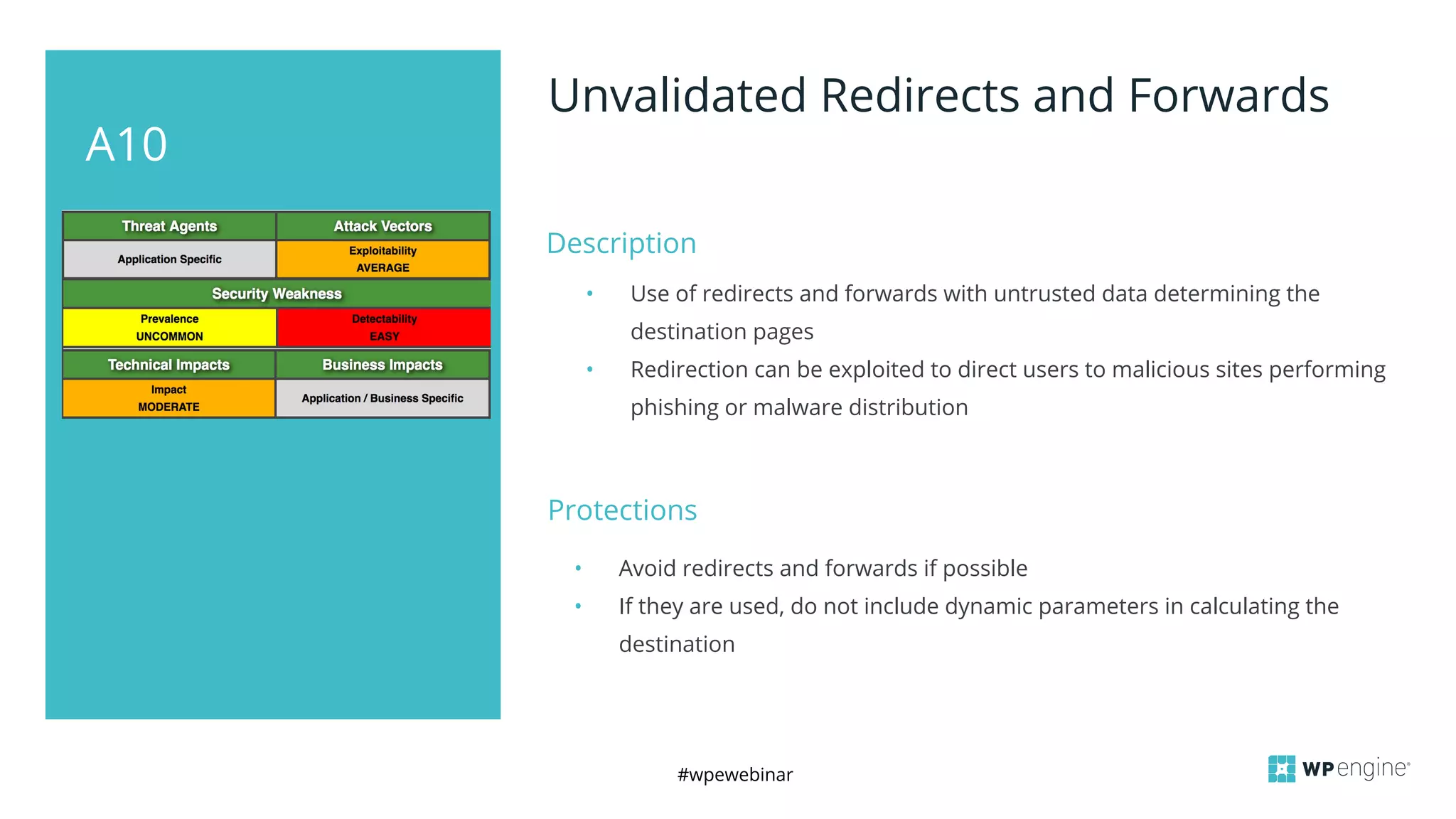
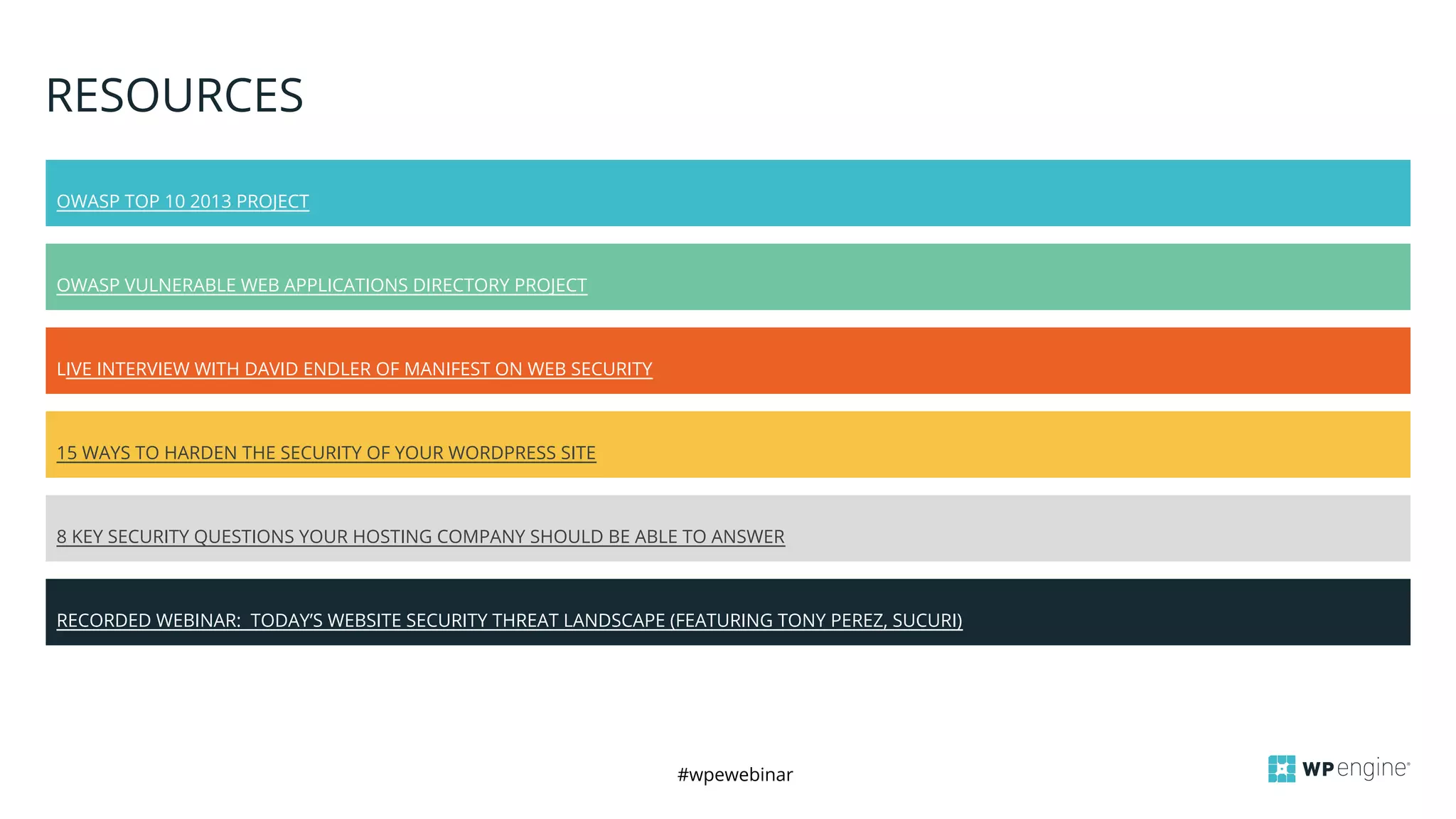
The document is a summary of a webinar about OWASP and its top ten vulnerabilities that affect website security, detailing each vulnerability along with its descriptions and protections. It covers topics like injection attacks, weak authentication, cross-site scripting, and others, providing advice on mitigation strategies. The presentation also includes a Q&A section and mentions the availability of slides and recordings post-webinar.