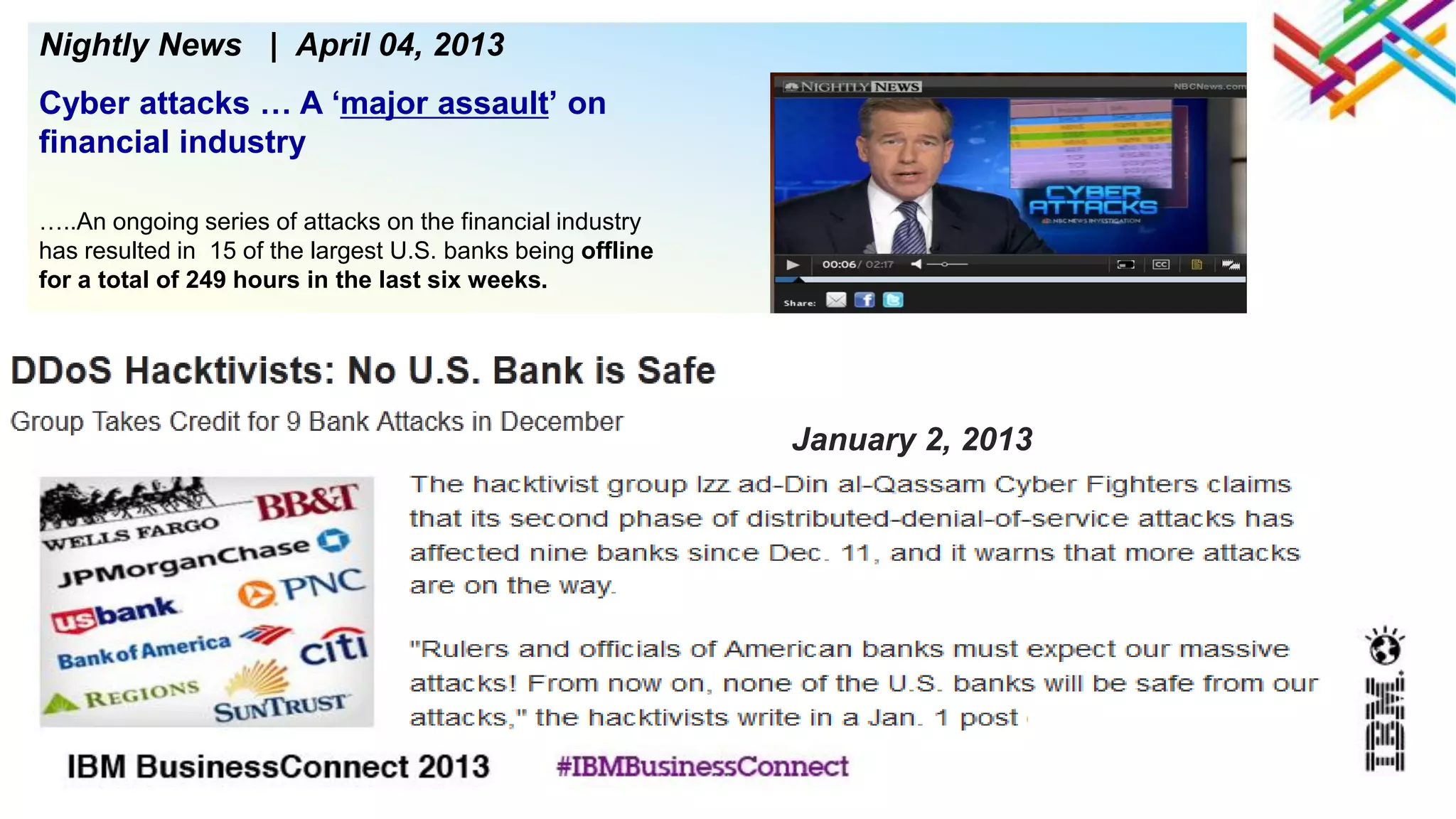
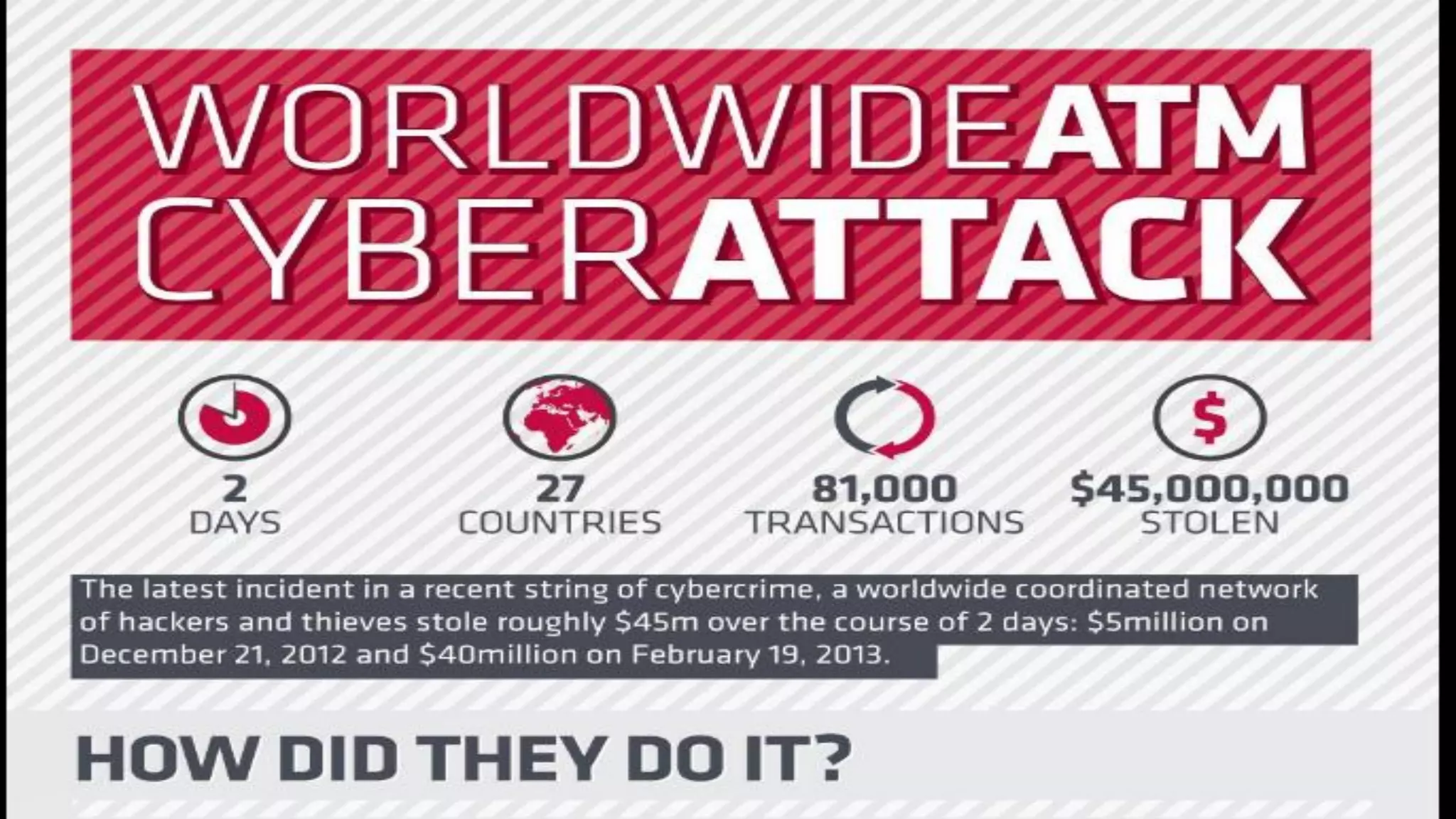
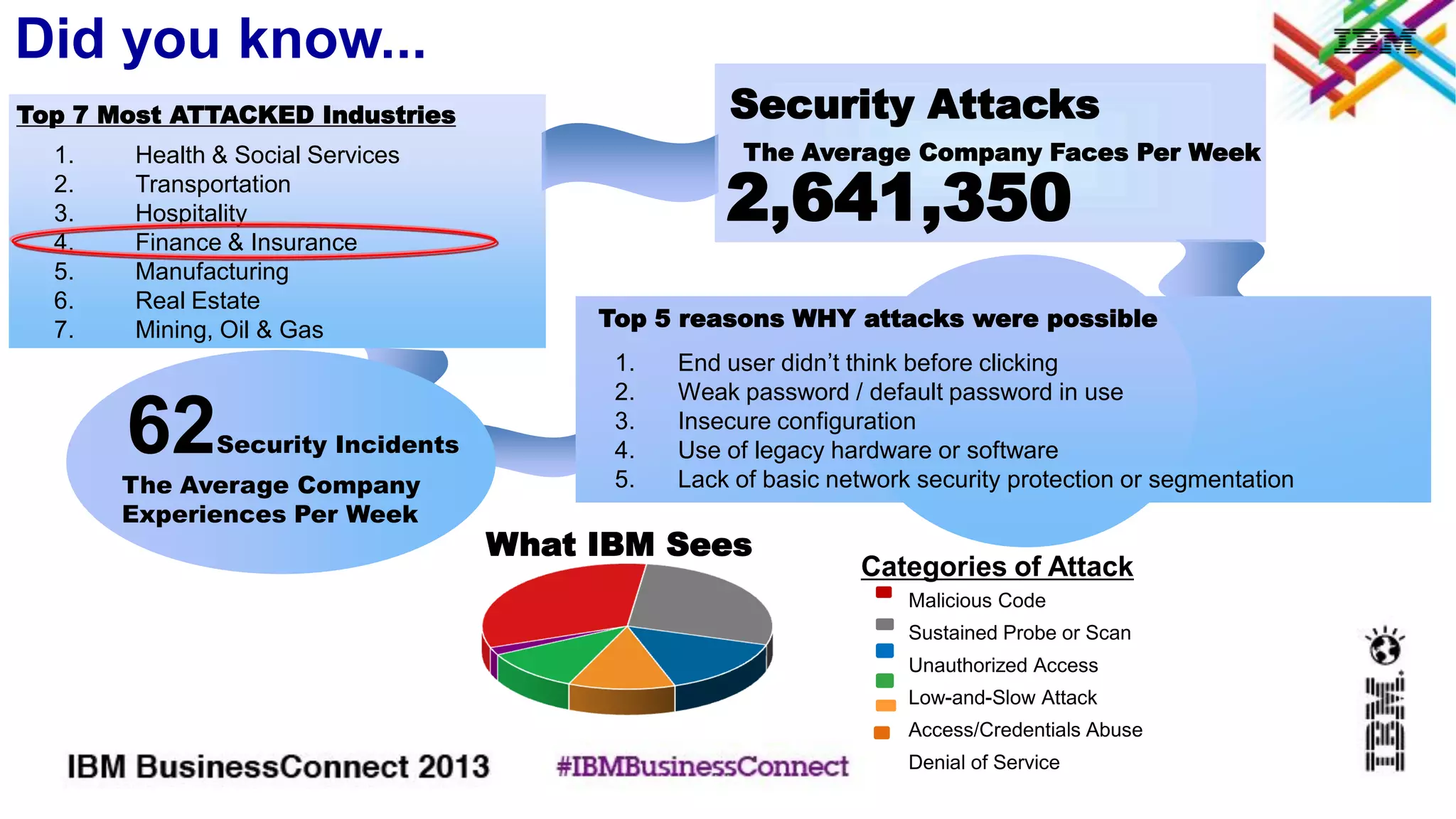
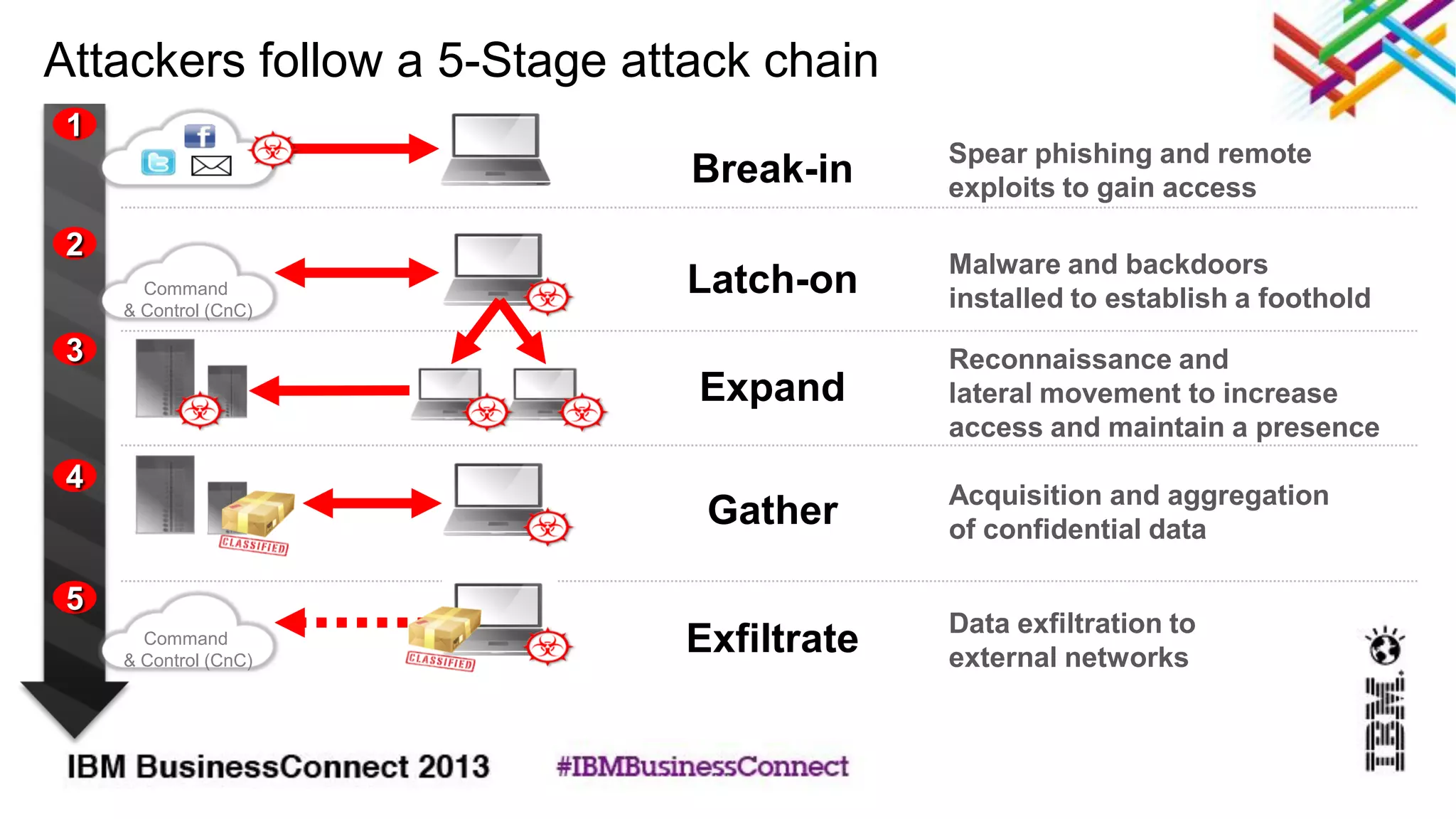
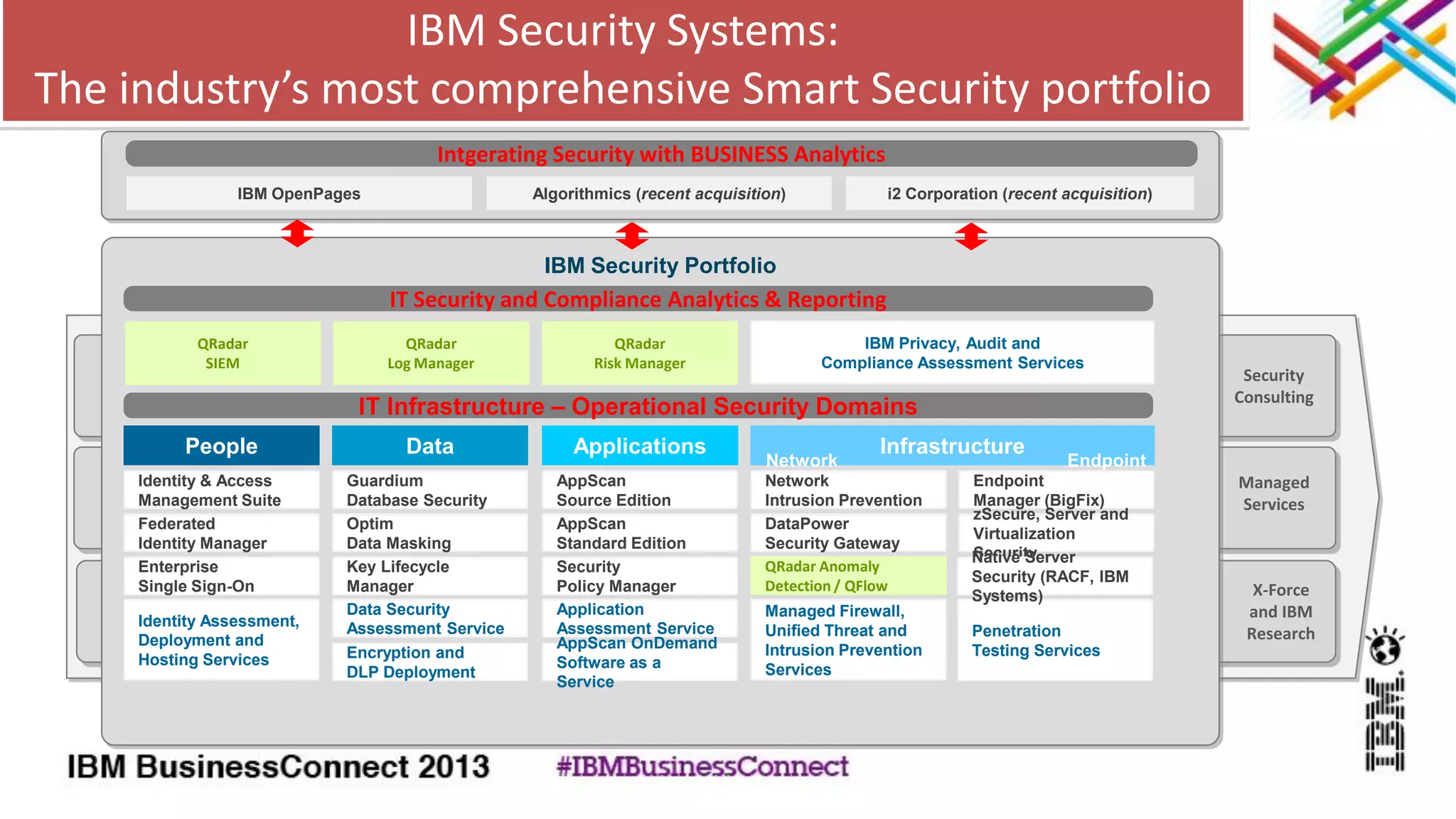
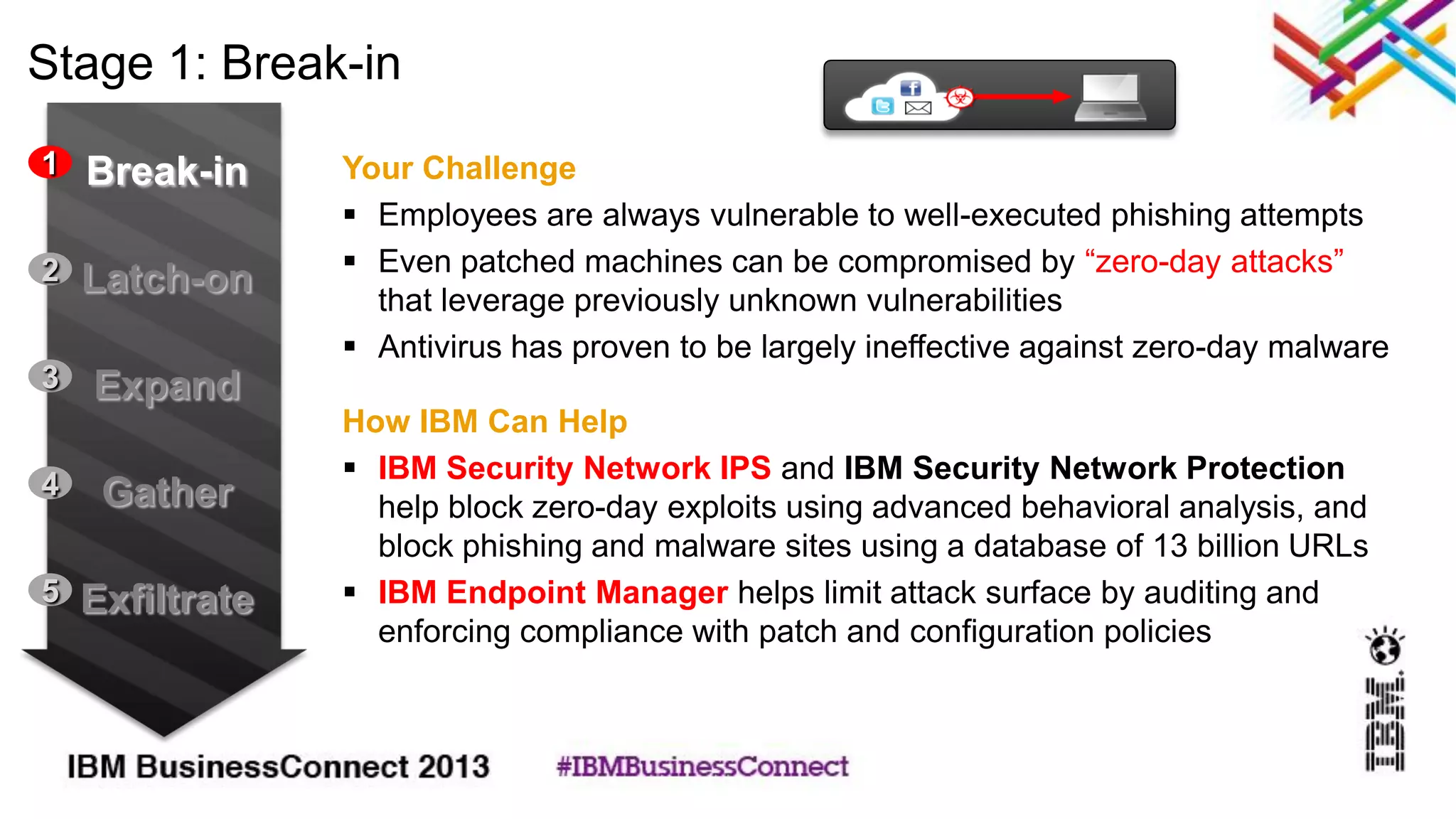
The document discusses defending against cyber threats with IBM security solutions. It describes IBM security solutions that address each stage of a typical 5-stage cyber attack process: 1) breaking in, 2) latching on, 3) expanding access, 4) gathering data, and 5) exfiltrating data. For each stage, it outlines challenges companies face and how IBM solutions such as QRadar, Endpoint Manager, Network IPS, and others can help address those challenges.