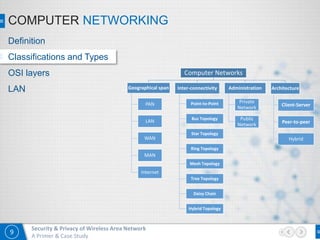
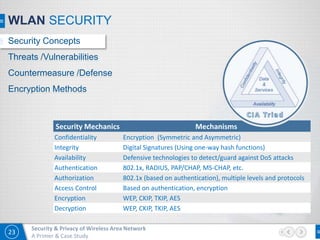
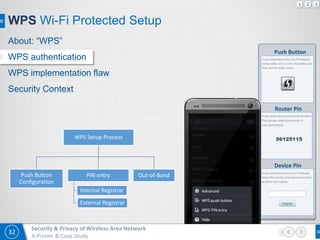
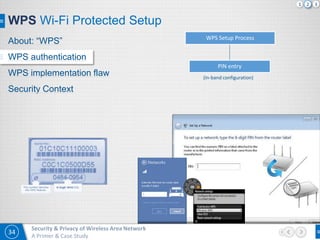
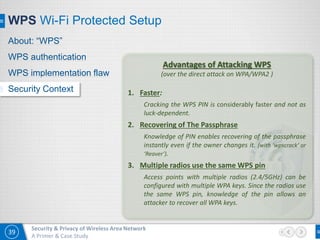
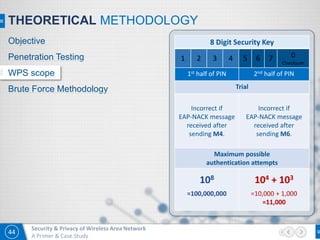
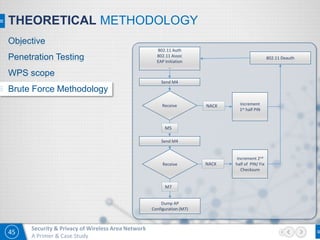
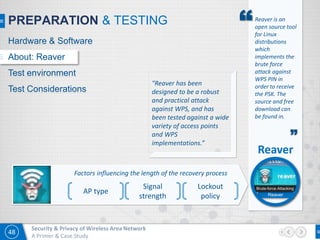
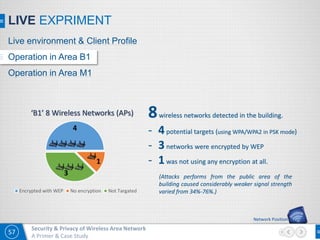
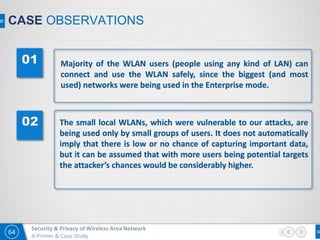
The document presented by Mohammad Mahmud Kabir focuses on security and privacy issues within wireless local area networks (WLAN), providing a theoretical overview and a practical penetration testing case study. It details WLAN security threats, countermeasures, and specifically addresses vulnerabilities within the Wi-Fi Protected Setup (WPS). The objective is to educate on ethical hacking and penetration testing methodologies while emphasizing the importance of security measures in wireless networks.
![A Primer & Case Study
Presented By Mohammad Mahmud KabirPresented By Mohammad Mahmud Kabir
Security & Privacy in
Wireless Local Area Network
[ Prepared As the Presentation on Term Paper Prepared for BIM PGDCS Course 2015 ]](https://image.slidesharecdn.com/bim-pgdcs-term-paper-on-security-privacy-in-wlan-ver-181-160215175734/75/Security-Privacy-in-WLAN-A-Primer-and-Case-Study-1-2048.jpg)