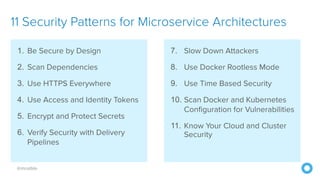
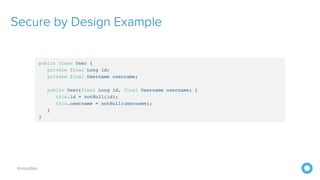
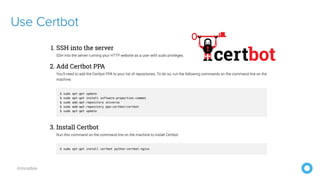
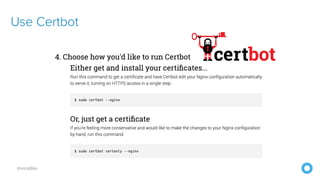
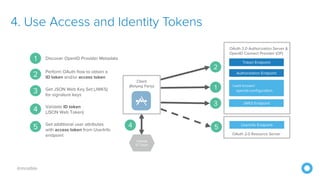
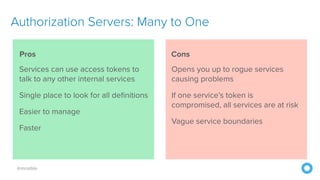
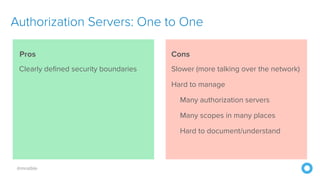
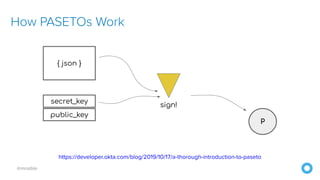
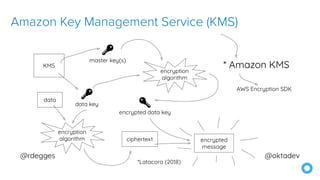
The document discusses security patterns for microservice architectures, highlighting eleven essential practices for enhancing security. These include being secure by design, using HTTPS everywhere, scanning dependencies, and employing access and identity tokens. The author emphasizes the importance of implementing these security patterns to protect against vulnerabilities in microservices.