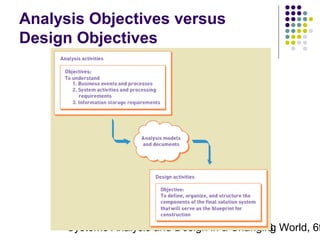
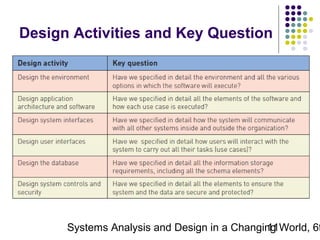
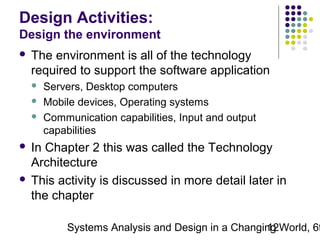
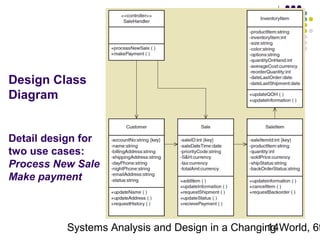
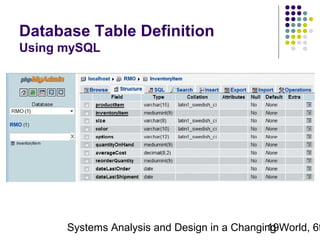
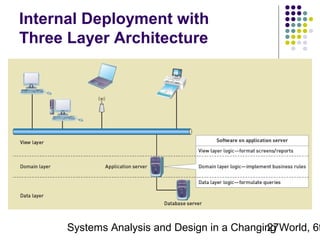
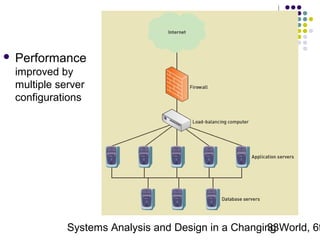
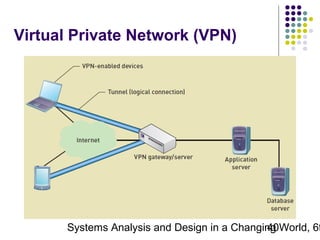
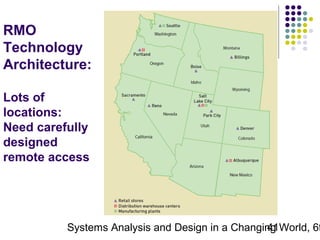
This chapter discusses systems design and the major design activities involved in systems development. It outlines the difference between systems analysis and systems design, and describes the key design activities which include designing the environment, application architecture, user interfaces, system interfaces, database, and security controls. The chapter also covers designing for internal deployment on a local network as well as external deployment over the internet, and various hosting alternatives for internet deployment.