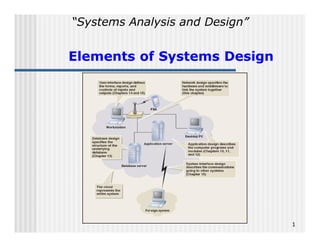
Elements of systems design
- 1. Systems Analysis and Design Elements of Systems Design 1
- 2. Topics n n n n n n n n n n n Elements of Design Inputs for System Design Design and Integrate the Network Design the Application Architecture Design the User Interfaces Design the System Interfaces Prototype for Design Details Deployment Environment Software Application Functions Internet and Web-Based Application WebArchitecture Middleware 2
- 3. Elements of Design n Design is process of describing, organizing, and structuring system components at architectural design level and detailed design level Focused on preparing for construction Like developing blueprints n Three questions What components require systems design? What are inputs to and outputs of design process? How is systems design done? 3
- 5. Inputs for System Design n Design Converts functional models from analysis into models that represent the solution Focused on technical issues Requires less user involvement than analysis n Design may use structured or OO approaches Database can be relational, OO, or hybrid User interface issues 5
- 8. SDLC Phases with Design Phase Activities 8
- 9. Design Phase Activities and Key Questions 9
- 10. Design and Integrate the Network n Network specialists establish network based on strategic plan n Project team typically integrates system into existing network n Technical requirements have to do with communication via networks n Technical issues handled by network specialists Reliability, security, throughput, synchronization 10
- 11. Design the Application Architecture and Software n Specify how system use cases are carried out n Described during system analysis as logical models of system activities n After design alternative is selected, detailed computer processing is designed as physical models n Approach varies depending on development and deployment environments 11
- 12. Design the User Interfaces n User interface quality is critical aspect of system n Design of user interface defines how user interacts with system GUI windows, dialog boxes, mouse interaction Sound, video, voice commands n To user of system, user interface is the system n User interface specialists interface designers, usability consultants, human factors engineers 12
- 13. Design the System Interfaces n System interfaces enable systems to share and exchange information Internal organization systems Interfaces with systems outside organization New system interfaces with package application that organization has purchased and installed n n System interfaces can be complex Organization needs very specialized technical skills to work on these interfaces 13
- 14. Design and Integrate the Database n n n n System analysis data model used to create physical database model Collection of traditional computer files, relational databases, and/or object-oriented databases Technical requirements, such as response times, determine database performance needs Design work might involve Performance tuning Integration between new and existing databases 14
- 15. Prototype for Design Details n n Continue to create and evaluate prototypes during design phase Prototypes confirm design choices Database Network architecture Controls Programming environment n Rapid application development (RAD) design prototypes evolve into finished system 15
- 16. Design and Integrate the System Controls n n Final design activity to ensure system has adequate safeguards (system controls) to protect organizational assets Controls are needed for all other design activities User interface limit access to authorized users System interface protect from other systems Application architecture record transactions Database protect from software/hardware failure Network design protect communications 16
- 17. Network Design n n n n Integrate network needs of new system into existing network infrastructure Describe processing activity and network connectivity at each system location Describe communications protocols and middleware that connects layers Ensure that network capacity is sufficient Data size per access type and average Peak number of access per minute or hour 17
- 18. Computer Networks n n n n n Set of transmission lines, specialized hardware, and communication protocols Enables communication among different users and computer systems Local area network (LAN) less than one kilometer long connects computers within single building Wide area network (WAN) over one kilometer long implies much greater, global, distances Router directs information within network 18
- 19. A Possible Network Configuration for RMO 19
- 20. The Internet, Intranets, and Extranets Internet global collection of networks that use TCP/IP networking protocols n Intranets n Private networks using same TCP/IP protocols as the Internet Limited to internal users n Extranets Intranets that have been extended outside the organization 20
- 21. Network Diagram for RMO Customer Support System 21
- 22. Deployment Environment n Deployment environment definition bridges analysis and design Hardware System software Networking Common deployment environments in which system will operate n Related design patterns and architectures for application software 22 n
- 23. Application Architecture n Complex hardware/networks require more complex software architectures n There are commonly used approaches (patterns) for application architecture Client/server architecture Three-layer client/server architecture Web services architecture Internet and Web-based application architecture 23
- 24. Software Application Functions n n n n n Presentation logic (i.e. HCI) Application logic (i.e. the processing of business rules processing) Data access logic (i.e. the processing required to access data database queries in SQL) Data storage (i.e. data files) There are several alternatives for the processing environment: Centralized systems Distributed computing 24
- 25. Centralized systems Prior to the early 1970 s there was only one technological environment the mainframe computer system at a central location The only options focused around kinds of input/output (e.g., keypunch, key-to-tape, or interactive input using video display terminal) and whether input/output devices would be placed in remote locations Although they are no longer the preferred platform for deploying ISs, they are still widely used as a subsystem of a larger, sometimes distributed information system or for large-scale batch processing applications (e.g., banking, insurance, government, etc.) where: Some input transactions don t need to be processed in real time On-line data-entry personnel can be centrally located Large numbers of periodic outputs are produced by the system There are three types of centralized systems: single, clustered and multicomputer architectures 25
- 26. Single Computer Architecture Places all information system resources on a single computer system and its directly attached peripheral devices Users interact with the system via simple input/output devices directly connected to the computer Requires all users be located near the computer All 4 software application functions are realized on a mainframe computer (server host) server-based architecture Advantage: Simplicity of maintenance: relatively easy to design, build and operate Disadvantage: The capacity limits make single computer impractical or unusable for large ISs: cannot provide all the required processing, data storage, and data retrieval tasks. However, many systems require more computing power than one single machine can provide (a clustered or multicomputer architecture is required) 26
- 27. SingleSingle-Computer, Clustered, and Multicomputer Architectures 27
- 29. Clustered Architecture Clustered architecture is a group (or cluster) of computers of the same type that have the same operating environment and share resources Computers from the same manufacturer and model family are networked together Application programs may be executed on any machine in the cluster without modification due to similar hardware and operating systems Cluster acts like a single large computer system (program movement and access to resources on other machines occur quickly and efficiently due to rapid and direct communication at the operating system level) Often one computer may act as entry point and the others function as slave computers 29
- 30. Multicomputer Architecture Multicomputer architecture is a group of dissimilar computers that are linked together but the hardware and operating systems are not required to be a similar as in the clustered architecture Hardware and software differences do not allow movement of application programs between computers (instead, resources are exclusively assigned to each computer system) System still functions like one single large computer Can have central computer and slave computers Main computer may execute programs and hold database The front-end computer may handle all communication lines with other computers or simple terminals Notes on Centralized Systems Clustered architectures may be cost efficient and provide greater total capacity if similar operating system and hardware are used Multicomputer architectures are good when the centralized system can be decomposed into relatively independent subsystems (each possibly with its own operating system and/or hardware platform) 30
- 31. Distributed Architecture n Distributes system across several computers and locations distributed computing n Relies on communication networks for geographic connectivity n Client/server architecture dominant model for distributed computing 31
- 32. Client/Server Architecture The dominant architectural model for distributing information resources Two-tire architecture divides the information system processes into two classes: Server: manages system resources and provides access to those resources and services to other computers on the network Client computer: uses communication interface to requests services from other computers on the network Computer software that implements communication protocols on the network is called middleware n Advantage deployment flexibility Location, scalability, maintainability n Disadvantage complexity Performance, security, and reliability 32
- 33. Interaction Among Multiple Clients and a Single Server 33
- 37. ThreeThree-Layer Client/Server Architecture The data layer is a layer on a client-server configuration that manages stored data implemented as one or more databases The business logic layer contains the programs that implement the rules and procedures of business processing (or program logic of the application) The view layer contains the user interface and other components to access the system (accepts user input, and formats and displays processing results) n n This approach is called tree-layer architecture The IS divided into three layer is relatively easy to distribute and replicate across a network (interactions among the layers are always have a form of either request or response) It makes the layer relatively independent of one another, thus they can be placed on different computer systems with network connections and middleware serving 37
- 39. ThreeThree-Layer Architecture Software Application Functions 39
- 40. N-Layer Client/Server Architecture When processing requirements or data resources are complex, threelayer architecture can be expanded into a larger number of layers (nlayer or n-tiered architecture) Next slide shows an example in which the data layer is split into two separate layers: the combined database server and servers that control the individual databases (marketing, production, accounting). The business logic layer interacts with a combined database server that provides a unified view of the data stored in several different databases. The responses from the individual database servers are then combined to create a single response to send to the business logic layer. 40
- 43. Internet and Web-Based WebApplication Architecture Web is complex example of client/server architecture n Can use Web protocols and browsers as application interfaces n Benefits n Accessibility Low-cost communication Widely implemented standards 43
- 44. Negative Aspects of Internet Application Delivery n Breaches of security n Fluctuating reliability of network throughput n Throughput can be limited n Volatile, changing standards 44
- 45. Web Services Architecture A client/server architecture n Packages software functionality into server processes ( services ) n Makes services available to applications via Web protocols n Web services are available to internal and external applications n Developers can assemble an application using existing Web services 45
- 47. Middleware n Aspect of distributed computing n Connects parts of an application and enables requests and data to pass between them n Transaction process monitors, object request brokers (ORBs), Web services directories n Designers reply on standard frameworks and protocols incorporated into middleware 47
