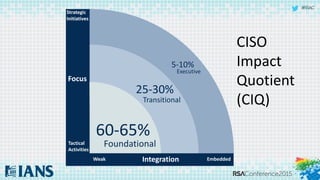
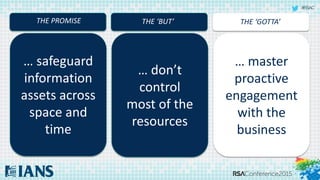
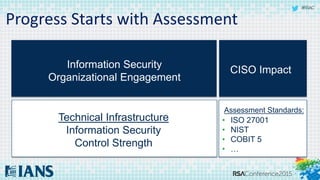
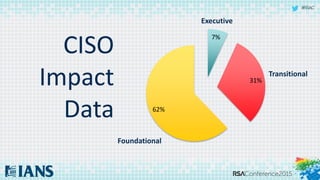
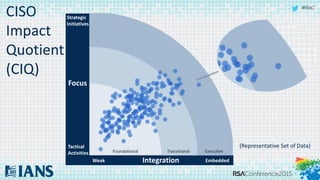
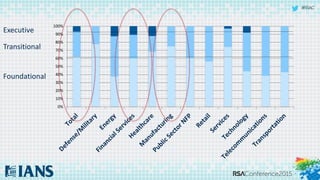
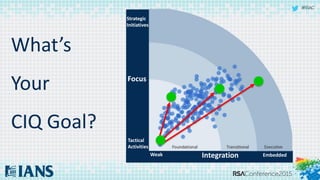
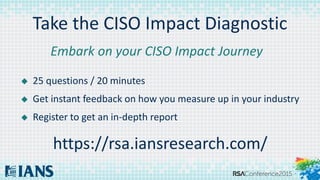
The document discusses the 'CISO Impact Quotient' (CIQ) and outlines seven key factors that influence a Chief Information Security Officer's impact within an organization. These factors include gaining command of facts, involving business leaders in risk ownership, embedding security into processes, and communicating security's value. The document highlights the importance of strategic alignment between information security and business objectives to enhance overall organizational resilience.