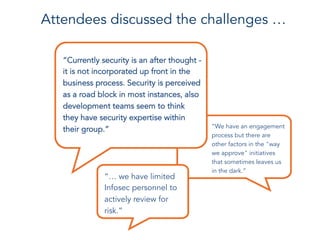
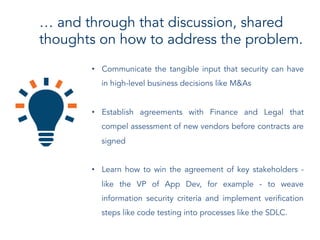
Connector Events are small group discussions organized by IANS that bring together senior information security professionals to discuss challenges and solutions. The discussions provide a forum for peer-to-peer conversations around common issues. Attendees can gain different perspectives and new ideas to help solve problems in their own organizations. One recent event discussed how to better embed information security into key business processes like software development and vendor selection, as research found most CISOs are still in the early stages of integration. Attendees shared challenges like limited security resources to review everything and potential solutions such as communicating security's business impact and establishing agreements to assess vendors before contracts.