Risk management processes
•
2 likes•1,042 views
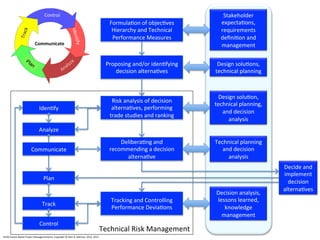
When we hear that a proposed process, tool, method or any ideas is all about "risk management," check to see if it covers these areas. If not, the suggestion is not really about risk management.
Report
Share
Report
Share
Download to read offline
Recommended
Roles of business analyst

This documents shows that who is Business Analyst and what are the roles of BA
Failure Mode Effects & Criticality Analysis 2-Day Workshop by Tetrahedron

The Failure Mode Effects and Criticality Analysis is a reliability evaluation/design technique which examines the potential failure modes within a system and its equipment, in order to determine the effects on equipment and system performance.
Model Driven Prototyping

Shows a model-driven approach for building prototypes focused on domain models.
Presented at the Vancouver Island Java User Group in September 2009.
Business Aanalysis Resume/Interview preparation 

In this Business Analysis Training session, you will learn, resume and Interview preparation. Topics covered in this session are:
• Resume Preparation and Interview
• What is behavioral interviewing?
• Why Does the BA Interviewer Ask Behavioral Interview Questions?
• STAR technique
• Resume workshop
To learn more about this course, visit this link: https://www.mindsmapped.com/courses/business-analysis/foundation-level-business-analyst-training/
Recommended
Roles of business analyst

This documents shows that who is Business Analyst and what are the roles of BA
Failure Mode Effects & Criticality Analysis 2-Day Workshop by Tetrahedron

The Failure Mode Effects and Criticality Analysis is a reliability evaluation/design technique which examines the potential failure modes within a system and its equipment, in order to determine the effects on equipment and system performance.
Model Driven Prototyping

Shows a model-driven approach for building prototypes focused on domain models.
Presented at the Vancouver Island Java User Group in September 2009.
Business Aanalysis Resume/Interview preparation 

In this Business Analysis Training session, you will learn, resume and Interview preparation. Topics covered in this session are:
• Resume Preparation and Interview
• What is behavioral interviewing?
• Why Does the BA Interviewer Ask Behavioral Interview Questions?
• STAR technique
• Resume workshop
To learn more about this course, visit this link: https://www.mindsmapped.com/courses/business-analysis/foundation-level-business-analyst-training/
Inversion of Control

The Impedance Mismatch in Integrated Engineering Design Systems is an issue in the Integration of commercial off the shelf (COTS) components.
This issue is a member of the Impedance Mismatch
problems found when commercial off the shelf
components are assembled into systems.
This mismatch occurs when event, control sequence,
or data semantics of two or more participating application
domains are mismatched.
During the system integration process the impedance
mismatch must be addressed through some means,
either through an integration layer which hides the
mismatch or through an integrating service, such as
CORBA, which facilitates the impedance adaptation
between the applications.
Pedir lo mismo de diferentes maneras

Una pequeña reflexión sobre diferentes maneras de evitar que los perros manchen la calle con sus necesidades. Nos encontramos desde avisos procedentes de las autoridades, tanto apelando a la ley como premiando actitudes positivas, hasta carteles hechos por particulares.
Avoid software project horror stories - check the reality value of the estima...

Avoid software project horror stories - check the reality value of the estima...Harold van Heeringen
Many large software projects turn into software horror stories, resulting in newspaper headlines and even political issues. Often, the project costs and schedule were estimated unrealistically optimistic, using immature estimation techniques. A relatively simple way to avoid many problems is to perform a reality check on the estimate. This presentation was given on the conference of the International Cost Estimating and Analysis Association (ICEAA2014), June 2014 (Denver, USA)Customer Intelligence & Social Media

Introduction to Amplified Analytics methodology and implementation
Architectured Centered Design

The use of an architecture–centered development process for delivering information technology began with the introduction of client / server based systems. Early client/server and legacy mainframe applications did not provide the architectural flexibility needed to meet the changing business requirements of the modern manufacturing organization. With the introduction of Object Oriented systems, the need for an architecture–centered process became a critical success factor. Object reuse, layered system components, data abstraction,
web based user interfaces, CORBA, and rapid development and deployment processes all provide economic
incentives for object technologies. However, adopting the latest object oriented technology, without an adequate understanding of how this technology fits a specific architecture, risks the creation of an instant legacy
system.
A possible cure 2014 may9

We have lots data. Let’s use it create more credible estimates to help tame the growth beast. In spite the estimating community’s efforts to provide credible estimates, government programs still seem to deliver less than promised, cost more than planned, and take longer than needed. When estimates are consistently biased low:
- Decisions of choice are distorted
- Cost growth causes more growth as programs are stretched out to fund portfolios with fixed budgets
- Taxpayers become more cynical and negative about government
- The estimating community’s credibility is seriously questioned
Cure for cost and schedule growth

Delivering programs with less capability than promised, while exceeding the cost and planned durations, distorts decision making, contributes to increasing cost growth to other programs, undermines the Federal government’s credibility with taxpayers and contributes to the public’s negative support for these programs.
Many reasons have been hypothesized and documented for cost and schedule growth. The authors review some of these reasons, and propose that government and contractors use the historical variability of the past programs to establish cost and schedule estimates at the outset and periodically update these estimates with up-to-date risks, to increase the probability of program success. For this to happen, the authors recommend changes to estimating, acquisition and contracting processes.
Fix you some bad estimation habits

Slides as given for the Feb. 12, 2014 talk at Bay Area Software Testers.
(btw, I failed to give credit for the "Stand Back!" t-shirt image, it was from the XKCD T-shirt here: http://store-xkcd-com.myshopify.com/products/try-science)
Also forgot reference to the paper on Fibonacci numbers in planning poker affecting estimates: http://simula.no/publications/Simula.simula.1282/simula_pdf_file
UX for Lean Startups Sep 15

Materials from "UX for Lean Startups" at Cross Campus, September 15, 2012.
UPDATE Sep 16 - added video URLs to slides.
More Related Content
Viewers also liked
Inversion of Control

The Impedance Mismatch in Integrated Engineering Design Systems is an issue in the Integration of commercial off the shelf (COTS) components.
This issue is a member of the Impedance Mismatch
problems found when commercial off the shelf
components are assembled into systems.
This mismatch occurs when event, control sequence,
or data semantics of two or more participating application
domains are mismatched.
During the system integration process the impedance
mismatch must be addressed through some means,
either through an integration layer which hides the
mismatch or through an integrating service, such as
CORBA, which facilitates the impedance adaptation
between the applications.
Pedir lo mismo de diferentes maneras

Una pequeña reflexión sobre diferentes maneras de evitar que los perros manchen la calle con sus necesidades. Nos encontramos desde avisos procedentes de las autoridades, tanto apelando a la ley como premiando actitudes positivas, hasta carteles hechos por particulares.
Avoid software project horror stories - check the reality value of the estima...

Avoid software project horror stories - check the reality value of the estima...Harold van Heeringen
Many large software projects turn into software horror stories, resulting in newspaper headlines and even political issues. Often, the project costs and schedule were estimated unrealistically optimistic, using immature estimation techniques. A relatively simple way to avoid many problems is to perform a reality check on the estimate. This presentation was given on the conference of the International Cost Estimating and Analysis Association (ICEAA2014), June 2014 (Denver, USA)Customer Intelligence & Social Media

Introduction to Amplified Analytics methodology and implementation
Architectured Centered Design

The use of an architecture–centered development process for delivering information technology began with the introduction of client / server based systems. Early client/server and legacy mainframe applications did not provide the architectural flexibility needed to meet the changing business requirements of the modern manufacturing organization. With the introduction of Object Oriented systems, the need for an architecture–centered process became a critical success factor. Object reuse, layered system components, data abstraction,
web based user interfaces, CORBA, and rapid development and deployment processes all provide economic
incentives for object technologies. However, adopting the latest object oriented technology, without an adequate understanding of how this technology fits a specific architecture, risks the creation of an instant legacy
system.
A possible cure 2014 may9

We have lots data. Let’s use it create more credible estimates to help tame the growth beast. In spite the estimating community’s efforts to provide credible estimates, government programs still seem to deliver less than promised, cost more than planned, and take longer than needed. When estimates are consistently biased low:
- Decisions of choice are distorted
- Cost growth causes more growth as programs are stretched out to fund portfolios with fixed budgets
- Taxpayers become more cynical and negative about government
- The estimating community’s credibility is seriously questioned
Cure for cost and schedule growth

Delivering programs with less capability than promised, while exceeding the cost and planned durations, distorts decision making, contributes to increasing cost growth to other programs, undermines the Federal government’s credibility with taxpayers and contributes to the public’s negative support for these programs.
Many reasons have been hypothesized and documented for cost and schedule growth. The authors review some of these reasons, and propose that government and contractors use the historical variability of the past programs to establish cost and schedule estimates at the outset and periodically update these estimates with up-to-date risks, to increase the probability of program success. For this to happen, the authors recommend changes to estimating, acquisition and contracting processes.
Fix you some bad estimation habits

Slides as given for the Feb. 12, 2014 talk at Bay Area Software Testers.
(btw, I failed to give credit for the "Stand Back!" t-shirt image, it was from the XKCD T-shirt here: http://store-xkcd-com.myshopify.com/products/try-science)
Also forgot reference to the paper on Fibonacci numbers in planning poker affecting estimates: http://simula.no/publications/Simula.simula.1282/simula_pdf_file
UX for Lean Startups Sep 15

Materials from "UX for Lean Startups" at Cross Campus, September 15, 2012.
UPDATE Sep 16 - added video URLs to slides.
Viewers also liked (20)
Avoid software project horror stories - check the reality value of the estima...

Avoid software project horror stories - check the reality value of the estima...
Immutable Principles Of Project Management (V7 Final Cmu)

Immutable Principles Of Project Management (V7 Final Cmu)
Establishing the performance measurement baseline (pmi fort worth)(v4)

Establishing the performance measurement baseline (pmi fort worth)(v4)
Similar to Risk management processes
Decision-Centric Dashboards with DMN at Two Fortune 200 Financial Companies

Decision-Centric Dashboards with DMN at Two Fortune 200 Financial CompaniesDecision Management Solutions
The new Decision Model and Notation (DMN) standard has been used to gather requirements for and to design Enterprise IT Management dashboards at two Fortune 200 Financial Corporations. These dashboards are used to manage 100+ projects being released every 2 weeks into production across hundreds of critical applications ranging from mainframe, client-server, web and mobile applications.
Presentation from BBC2014Nicolas Schobinger | Business Transformation Academy - Post Merger Integratio...

This presentation was given to the European Business Transformation Conference, an event of the Business Transformation Academy (www.bta-online.com). The overall topic of the event was “Post-Merger Integration”, which is one of the main triggers for business transformation.
The case study presented is the one of SAP's own integration of acquired BusinessObjects. The presenter was leading the worldwide PMO for the Day 1 PMI phase.
Enterprise Assets Management PowerPoint Presentation Slides 

Every organization needs to adapt to the ever-changing business environment. Sensing this need, we have come up with these content-ready change management PowerPoint presentation slides. These change management PPT templates will help you deal with any kind of an organizational change. Be it with people, goals or processes. The business solutions incorporated here will help you identify the organizational structure, create vision for change, implement strategies, identify resistance and risk, manage cost of change, get feedback and evaluation, and much more. With the help of various change management tools and techniques illustrated in this presentation design, you can achieve the desired business outcomes. This business transition PowerPoint design also covers certain related topics such as change model, transformation strategy, change readiness, change control, project management and business process. By implementing the change control methods mentioned in the presentation, you will be able to have a smooth transition in an organization. So, without waiting much, download our extensively researched change management framework presentation. With our Change Management Presentation slides, understand the need for change and plan to go through it without any hassles.
Managing Design 2010

Design Management is becoming increasingly recognised as critical to the success of complex construction projects. However, the role of the Design Manager is poorly defined and Design Management is a discipline without robust terms of reference.
This presentation reviews the need for Design Management and the day to day challenges facing Design Managers. It concludes by setting out Adept Management’s Design Management Framework which provides clarity and structure to this emerging profession.
Six Sigma Quality and IT Governance

Six Sigma Quality and IT Governance share many process and can produce synergistic results when combined.
Lean dqm reporting

Webinar slides delivered in conjunction with DataQualityPro.com.
We present key aspects of applying a lean approach to Data Quality Management using the latest Data Mining & Profiling tools. Includes a practical demonstration of applying these techniques to Financial Regulatory and compliance reporting.
Sept 2008 Presentation Quality & Project Management

Presentation by Andy Willums - September 2008 ASQ Section meeting
6.18.2013 - 2013 - Prj & Port Mgmt SftDev - Portfolio Management - For the ...

Webcast Series: Project and Portfolio Management Software Development
Title: 2013 - Prj & Port Mgmt SftDev - Portfolio Management - For the Manager - Making Good Decisions
Date: 6-18-2013
Presenter: Chris Wolters
Developing an Acquisition Centre of Excellence for Effective Sourcing and Sup...

Acquisition skills are necessary to support move from in-sourcing to outsourcing of projects, solutions and services. Effective and appropriate sourcing allows organisations react quickly while reducing costs, ensuring repeatability and improving returns on sourcing activities. Acquisition includes sourcing of suppliers, defining services, awarding contracts to supplier agreements, managing the delivery of contracted services, Getting good at acquisition is a very worthwhile investment for any organisation. Acquisitions skills are essential for implementing sourcing strategy effectively. It ensures consistent and cost-effective outcomes from sourcing activities. Use CMMI for Acquisition maturity model structure to develop an acquisition capability programme. This provides a structured approach with a set of activities and tasks.
Similar to Risk management processes (20)
Decision-Centric Dashboards with DMN at Two Fortune 200 Financial Companies

Decision-Centric Dashboards with DMN at Two Fortune 200 Financial Companies
Nicolas Schobinger | Business Transformation Academy - Post Merger Integratio...

Nicolas Schobinger | Business Transformation Academy - Post Merger Integratio...
Enterprise Assets Management PowerPoint Presentation Slides 

Enterprise Assets Management PowerPoint Presentation Slides
Sept 2008 Presentation Quality & Project Management

Sept 2008 Presentation Quality & Project Management
6.18.2013 - 2013 - Prj & Port Mgmt SftDev - Portfolio Management - For the ...

6.18.2013 - 2013 - Prj & Port Mgmt SftDev - Portfolio Management - For the ...
Developing an Acquisition Centre of Excellence for Effective Sourcing and Sup...

Developing an Acquisition Centre of Excellence for Effective Sourcing and Sup...
More from Glen Alleman
Managing risk with deliverables planning

Without metrics, you're just another guy with an opinion - Stephan Leeschka, Hewlett Packard
A Gentle Introduction to the IMP/IMS

Planning projects usually starts with tasks and milestones. The planner gathers this information from the participants – customers, engineers, subject matter experts. This information is usually arranged in the form of activities and milestones. PMBOK defines “project time management” in this manner. The activities are then sequenced according to the projects needs and mandatory dependencies.
Increasing the Probability of Project Success

Risk Management is essential for development and production programs. Information about key cost, performance and schedule attributes are often uncertain or unknown until late in the program.
Risk issues that can be identified early in the program, which may potentially impact the program, termed Known Unknowns, can be alleviated with good risk management. -- Effective Risk Management 2nd Edition, Page 1, Edmund Conrow, American Institute of Aeronautics and Astronautics, 2003
Process Flow and Narrative for Agile+PPM

Providing actionable information to the Decision Maker using Earned Value Management integrated with Agile Software Development performed in Rally
Practices of risk management

With the Principles of Risk Management in place, we now need Practices and Processes
Principles of Risk Management

Cost and schedule growth for complex projects is created when unrealistic technical performance expectations, unrealistic cost and schedule estimates, inadequate risk assessments, unanticipated technical issues, and poorly performed and ineffective risk management, contribute to project technical and programmatic shortfalls
Deliverables Based Planning, PMBOK® and 5 Immutable Principles of Project Suc...

The planning to produce the needed deliverables, on or before the need date, and at or below the planned cost starts with this framework
From Principles to Strategies for Systems Engineering

From Principles to Strategies How to apply Principles, Practices, and Processes of Systems Engineering to solve complex technical, operational,
and organizational problems
NAVAIR Integrated Master Schedule Guide guide

The Integrated Master Schedule contains the networked, detailed tasks necessary to ensure successful program execution.
Building a Credible Performance Measurement Baseline

Establishing a credible Performance Measurement Baseline, with a risk adjusted Integrated Master Plan and Integrated Master Schedule, starts with the WBS and connects Technical Measures of progress to Earned Value
Integrated master plan methodology (v2)

This report described the methodology for the developing an Integrated Master Plan (IMP)
IMP / IMS Step by Step

Building the Integrated Master Plan (IMP) and Integrated Master Schedule (IMS) from Proposal to Successful Execution
DHS - Using functions points to estimate agile development programs (v2)

Determining the size of system functionality and measuring the performance of project teams is the basis of successful projects
Making the impossible possible

Applying Heliotropic Abundance for creating Program and Project Management Processes to Increase the Probability of Success
Heliotropic Abundance

The key to project success is connecting Leadership Behaviours with Project Management Principles, Processes, and Practices
Capabilities based planning

Capabilities‒Based Planning the capabilities needed to accomplish a mission or fulfill a business strategy
Only when capabilities are defined can we start with requirements elicitation
Process Flow and Narrative for Agile

Starting with the development of a Rough Order of Magnitude (ROM) estimate of work and duration, creating the Product Roadmap and Release Plan, the Product and Sprint Backlogs, executing and statusing the Sprint, and informing the Earned Value Management Systems, using Physical Percent Complete of progress to plan.
Building the Performance Measurement Baseline

The Performance Measurement Baseline (PMB) is a time–phased plan for accomplishing work, against which contract performance is measured.
Program Management Office Lean Software Development and Six Sigma

Successfully combining a PMO, Agile, and Lean / 6 starts with understanding what benefit each paradigm brings to the table. Architecting a solution for the enterprise requires assembling a “Systems” with processes, people, and principles – all sharing the goal of business improvement.
Policy and Procedure Rollout

This resource document describes the Program Governance Road map for product development, deployment, and sustainment of products and services in compliance with CMS guidance, ITIL IT management, CMMI best practices, and other guidance to assure high quality software is deployed for sustained operational success in mission critical domains.
More from Glen Alleman (20)
Deliverables Based Planning, PMBOK® and 5 Immutable Principles of Project Suc...

Deliverables Based Planning, PMBOK® and 5 Immutable Principles of Project Suc...
From Principles to Strategies for Systems Engineering

From Principles to Strategies for Systems Engineering
Building a Credible Performance Measurement Baseline

Building a Credible Performance Measurement Baseline
DHS - Using functions points to estimate agile development programs (v2)

DHS - Using functions points to estimate agile development programs (v2)
Program Management Office Lean Software Development and Six Sigma

Program Management Office Lean Software Development and Six Sigma
Recently uploaded
Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI

Enchancing adoption of Open Source Libraries. A case study on Albumentations.AIVladimir Iglovikov, Ph.D.
Presented by Vladimir Iglovikov:
- https://www.linkedin.com/in/iglovikov/
- https://x.com/viglovikov
- https://www.instagram.com/ternaus/
This presentation delves into the journey of Albumentations.ai, a highly successful open-source library for data augmentation.
Created out of a necessity for superior performance in Kaggle competitions, Albumentations has grown to become a widely used tool among data scientists and machine learning practitioners.
This case study covers various aspects, including:
People: The contributors and community that have supported Albumentations.
Metrics: The success indicators such as downloads, daily active users, GitHub stars, and financial contributions.
Challenges: The hurdles in monetizing open-source projects and measuring user engagement.
Development Practices: Best practices for creating, maintaining, and scaling open-source libraries, including code hygiene, CI/CD, and fast iteration.
Community Building: Strategies for making adoption easy, iterating quickly, and fostering a vibrant, engaged community.
Marketing: Both online and offline marketing tactics, focusing on real, impactful interactions and collaborations.
Mental Health: Maintaining balance and not feeling pressured by user demands.
Key insights include the importance of automation, making the adoption process seamless, and leveraging offline interactions for marketing. The presentation also emphasizes the need for continuous small improvements and building a friendly, inclusive community that contributes to the project's growth.
Vladimir Iglovikov brings his extensive experience as a Kaggle Grandmaster, ex-Staff ML Engineer at Lyft, sharing valuable lessons and practical advice for anyone looking to enhance the adoption of their open-source projects.
Explore more about Albumentations and join the community at:
GitHub: https://github.com/albumentations-team/albumentations
Website: https://albumentations.ai/
LinkedIn: https://www.linkedin.com/company/100504475
Twitter: https://x.com/albumentationsMicrosoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
Large Language Model (LLM) and it’s Geospatial Applications

Large Language Model (LLM) and it’s Geospatial Applications.
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Artificial Intelligence for XMLDevelopment

In the rapidly evolving landscape of technologies, XML continues to play a vital role in structuring, storing, and transporting data across diverse systems. The recent advancements in artificial intelligence (AI) present new methodologies for enhancing XML development workflows, introducing efficiency, automation, and intelligent capabilities. This presentation will outline the scope and perspective of utilizing AI in XML development. The potential benefits and the possible pitfalls will be highlighted, providing a balanced view of the subject.
We will explore the capabilities of AI in understanding XML markup languages and autonomously creating structured XML content. Additionally, we will examine the capacity of AI to enrich plain text with appropriate XML markup. Practical examples and methodological guidelines will be provided to elucidate how AI can be effectively prompted to interpret and generate accurate XML markup.
Further emphasis will be placed on the role of AI in developing XSLT, or schemas such as XSD and Schematron. We will address the techniques and strategies adopted to create prompts for generating code, explaining code, or refactoring the code, and the results achieved.
The discussion will extend to how AI can be used to transform XML content. In particular, the focus will be on the use of AI XPath extension functions in XSLT, Schematron, Schematron Quick Fixes, or for XML content refactoring.
The presentation aims to deliver a comprehensive overview of AI usage in XML development, providing attendees with the necessary knowledge to make informed decisions. Whether you’re at the early stages of adopting AI or considering integrating it in advanced XML development, this presentation will cover all levels of expertise.
By highlighting the potential advantages and challenges of integrating AI with XML development tools and languages, the presentation seeks to inspire thoughtful conversation around the future of XML development. We’ll not only delve into the technical aspects of AI-powered XML development but also discuss practical implications and possible future directions.
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

Leonard Jayamohan, Partner & Generative AI Lead, Deloitte
This keynote will reveal how Deloitte leverages Neo4j’s graph power for groundbreaking digital twin solutions, achieving a staggering 100x performance boost. Discover the essential role knowledge graphs play in successful generative AI implementations. Plus, get an exclusive look at an innovative Neo4j + Generative AI solution Deloitte is developing in-house.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

ここ3000字までしか入らないけどタイトルの方がたくさん文字入ると思います。
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
Recently uploaded (20)
Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI

Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI
Large Language Model (LLM) and it’s Geospatial Applications

Large Language Model (LLM) and it’s Geospatial Applications
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
Risk management processes
- 1. Formula9on of objec9ves Hierarchy and Technical Performance Measures Proposing and/or iden9fying decision alterna9ves Design solu9ons, technical planning Risk analysis of decision alterna9ves, performing trade studies and ranking Design solu9on, technical planning, and decision analysis Delibera9ng and recommending a decision alterna9ve Iden9fy Stakeholder expecta9ons, requirements defini9on and management Technical planning and decision analysis Analyze Communicate Plan Tracking and Controlling Performance Devia9ons Track Control Technical Risk Management Performance-‐Based Project Management(sm), Copyright © Glen B. Alleman, 2012, 2013 Decision analysis, lessons learned, knowledge management Decide and implement decision alterna9ves
