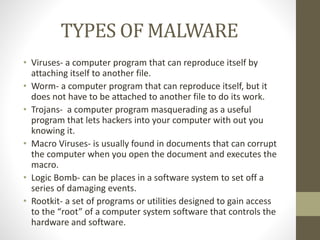
This document discusses social engineers, malware, and how to protect against cyber crime. It defines social engineers as con artists who trick users into giving up valuable information. Malware is described as damaging computer programs that install without consent, and includes viruses, worms, Trojans, and other types. The document outlines how malware can spread through email attachments, infected websites, storage devices, and networks. It emphasizes the importance of computer security through authentication, encryption, antivirus software, and policies to protect home and business networks and devices.