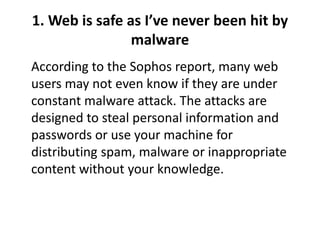
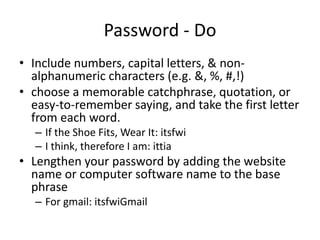
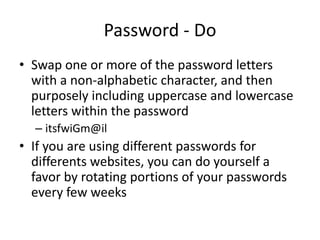
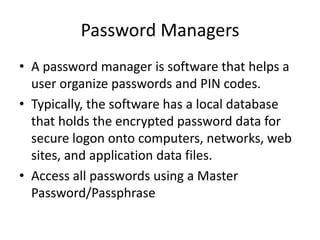
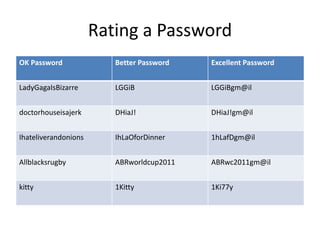
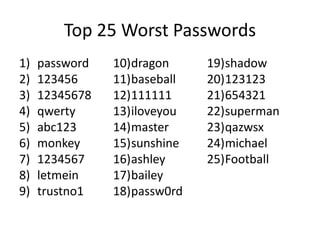
This document discusses various topics relating to computer and internet security. It defines common cyber threats like viruses, malware, spyware and provides tips on using antivirus software, firewalls, and strong passwords to enhance security. Specific myths about internet safety are debunked, such as thinking certain browsers are more secure or that only downloads can infect a device. Overall, the document stresses the importance of maintaining updated software, using caution online, and employing security measures like unique, complex passwords to help protect devices and information.