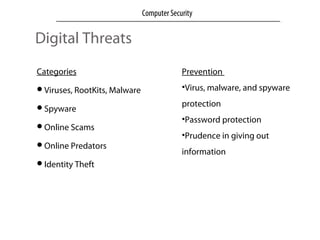
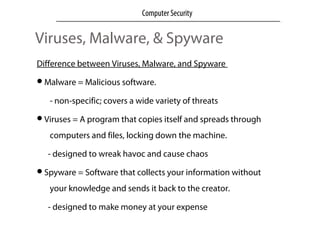
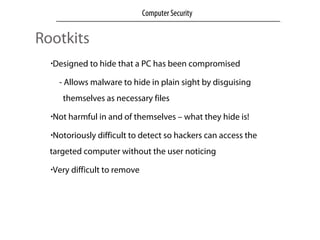
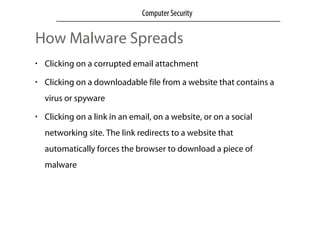
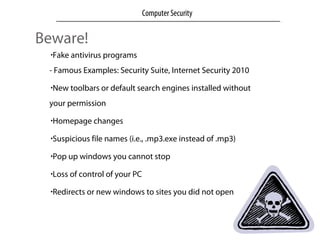
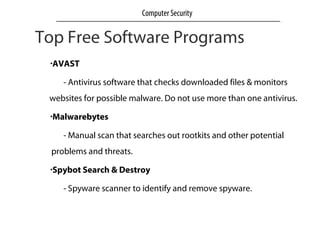
This document discusses computer security, privacy, and safety in the digital world. It describes common digital threats like viruses, malware, spyware, online scams, and identity theft. It provides information on computer security and privacy measures people can take, such as using antivirus software, strong passwords, and privacy settings on social networks. The document recommends keeping systems updated, using caution when downloading files or clicking links, and knowing how to identify and remove malware and spyware.